Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
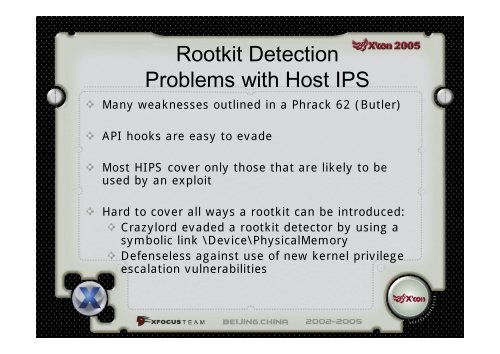
Rootkit DetectionProblems with Host IPSMany weaknesses outlined in a Phrack 62 (Butler)API hooks are easy to evadeMost HIPS cover only those that are likely to beused by an exploitHard to cover all ways a rootkit can be introduced:Crazylord evaded a rootkit detector by using asymbolic link \Device\PhysicalMemoryDefenseless against use of new kernel privilegeescalation vulnerabilities