Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
Xcon2005_Profiling_Malware_and_Rootkits_from_Ke..
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
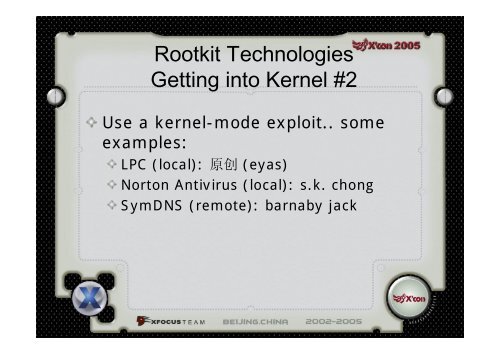
Rootkit TechnologiesGetting into <strong>Ke</strong>rnel #2Use a kernel-mode exploit.. someexamples:LPC (local): 原 创 (eyas)Norton Antivirus (local): s.k. chongSymDNS (remote): barnaby jack