2an initial value <strong>of</strong> CW min and may exponentially increaseup to a maximum <strong>of</strong> CW max . Then, a node that is readyto transmit randomly selects a back<strong>of</strong>f value CW bf from (0,CW ] using a uniform distribution. The node will keep sensingthe channel. If the channel is busy, the back<strong>of</strong>f value is frozenuntil the channel becomes idle. Otherwise, it is decremented byone at every (idle) time slot. When the back<strong>of</strong>f value reaches“0”, the node starts its transmission. If the transmission fails,the current contention window upper-bound CW is doubledunless it has reached the maximum CW max . Then anotherback<strong>of</strong>f procedure is repeated with the updated contentionwindow.III. PROBLEM STATEMENT AND MOTIVATIONThe motivation <strong>of</strong> this work is to exploit user diversity inrandom access wireless networks. This motivation stems froma few observed problems as described below.A. Impact <strong>of</strong> Access on Network PerformanceThe access mechanism in a wireless network with userdiversity has significant impact on the network performanceand channel utilization. Let us examine a network with a basestation and two client nodes: A and B. Suppose A has poorchannel conditions supporting a bit rate <strong>of</strong> R l and B has goodchannel conditions supporting a bit rate <strong>of</strong> R h . In one extremecase where only A has the access to the channel, the networkthroughput is A’s bit rate R l assuming no packet failure. Inthe other extreme case where only B uses the channel, thenetwork throughput is B’s bit rate R h . Otherwise, if A and Bshare the channel, the network throughput will be some valuebetween R l and R h . Namely, R h and R l are respectively theupper and lower bounds <strong>of</strong> the network throughput. Therefore,to improve the network throughput and channel utilization, Bshould be favored for accessing the channel, which is referredas opportunistic access.B. Equal Probability Access in CSMA/CAFrom the brief review <strong>of</strong> CSMA/CA in Section II, regardless<strong>of</strong> the channel conditions, all nodes probabilisticallyhave equal opportunities to access the channel because theyuniformly select the back<strong>of</strong>f value from the same initialcontention windows. In a two-node network with CSMA/CA,a node A with poor channel condition may beat the node Bwith good channel condition because both nodes have equalprobability in channel access. However, intuitively and fromthe discussion in the last section (Section III-A), it is morebeneficial to allow B to transmit under these conditions fortwo reasons. First, B would use the wireless channel moreefficiently because it takes less time in transmitting the sameamount <strong>of</strong> data at a higher bit rate than A. This opportunismcan lead to higher utilization, efficiency, and throughput <strong>of</strong>the overall network. Second, because <strong>of</strong> the inherent temporalvariations <strong>of</strong> the wireless channel, B with presently goodchannel conditions may not keep as good when it wins thechannel later.C. Opportunistic Transmission vs. Opportunistic AccessUnlike opportunistic access that exploits user diversity inwireless networks, opportunistic transmission takes advantage<strong>of</strong> time diversity due to the temporal dynamic characteristics<strong>of</strong> the wireless channel. In opportunistic transmission, after anode wins the contention, it tries to transmit aggressively whileits channel remains good because the condition may degradelater. In CSMA/CA, a node only transmits one frame when itwins the channel while in opportunistic transmission schemessuch as OAR [1] and MOAR [3], more than one frame may betransmitted when a node wins access. The number <strong>of</strong> framesto be transmitted is determined by the channel conditions. InOAR and MOAR, the number <strong>of</strong> frames transmitted after anode wins the contention is calculated as the ratio <strong>of</strong> currentbit rate over the basic rate. For example, if the current bit rate<strong>of</strong> a node is 11 Mbps and the basic rate is 2 Mbps, then theratio should be ⌊11/2⌋ = 5, so the node will transmits fivepackets before the channel is released for contention.Each communication cycle in the random access wirelessnetworks can actually be considered as two phases: access(contention) followed by transmission. From the above discussion,opportunistic transmission focuses on the transmissionphase but not the access phase. Although opportunistic transmissionimproves the network performance by exploiting timediversity, it does not guarantee the node with the best channelcondition has the best chance to win the channel. However,the node with the best channel conditions deserves the chanceto use the channel because its channel may degrade later. Toimprove the utilization <strong>of</strong> scarce wireless resources, we aremotivated to design opportunistic access algorithms that grantthe channel in probability to the node that has the best channelcondition, namely that is most likely to generate the largestinstantaneous network throughput.With the observations discussed above, to improve networkefficiency and channel utilization, we are motivated to designdistributed opportunistic access algorithms that probabilisticallyfavor the users with best channel conditions in winningthe channel contention.IV. DESIGN OF OPPORTUNISTIC RANDOM ACCESSTo achieve opportunistic random access, we proposethree algorithms based on the contention mechanism in theCSMA/CA. Two <strong>of</strong> these algorithms target at calculatingthe contention window for each node based on its instantaneouschannel conditions. The third algorithm proposes toselect a back<strong>of</strong>f value from the contention window with anormal distribution, rather than a uniform distribution as inthe CSMA/CA. In addition, opportunistic access inherentlytends to starve nodes with poor channel conditions. Thissection elaborates on these algorithms and how to address thestarvation problem with temporal fairness.A. Contention Window Based Opportunistic AccessTwo algorithms achieve opportunistic random access bydetermining contention windows based on channel conditions.
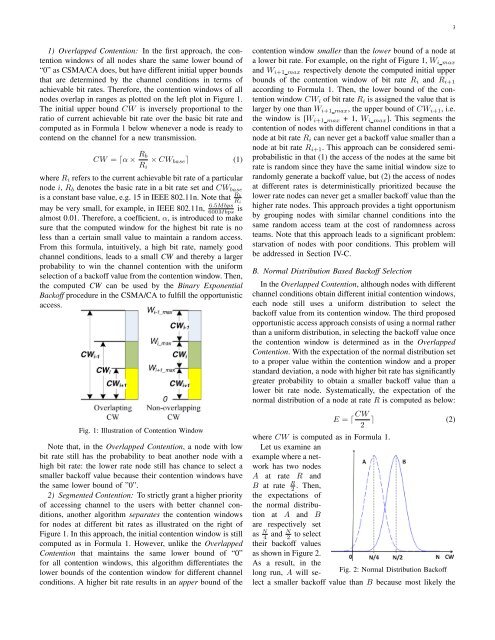
31) Overlapped Contention: In the first approach, the contentionwindows <strong>of</strong> all nodes share the same lower bound <strong>of</strong>“0” as CSMA/CA does, but have different initial upper boundsthat are determined by the channel conditions in terms <strong>of</strong>achievable bit rates. Therefore, the contention windows <strong>of</strong> allnodes overlap in ranges as plotted on the left plot in Figure 1.The initial upper bound CW is inversely proportional to theratio <strong>of</strong> current achievable bit rate over the basic bit rate andcomputed as in Formula 1 below whenever a node is ready tocontend on the channel for a new transmission.CW = ⌈α × R bR i× CW base ⌉ (1)where R i refers to the current achievable bit rate <strong>of</strong> a particularnode i, R b denotes the basic rate in a bit rate set and CW baseis a constant base value, e.g. 15 in IEEE 802.11n. Note that R bR i6.5Mbps600Mbps ismay be very small, for example, in IEEE 802.11n,almost 0.01. Therefore, a coefficient, α, is introduced to makesure that the computed window for the highest bit rate is noless than a certain small value to maintain a random access.From this formula, intuitively, a high bit rate, namely goodchannel conditions, leads to a small CW and thereby a largerprobability to win the channel contention with the uniformselection <strong>of</strong> a back<strong>of</strong>f value from the contention window. Then,the computed CW can be used by the Binary ExponentialBack<strong>of</strong>f procedure in the CSMA/CA to fulfill the opportunisticaccess.Fig. 1: Illustration <strong>of</strong> Contention WindowNote that, in the Overlapped Contention, a node with lowbit rate still has the probability to beat another node with ahigh bit rate: the lower rate node still has chance to select asmaller back<strong>of</strong>f value because their contention windows havethe same lower bound <strong>of</strong> ”0”.2) Segmented Contention: To strictly grant a higher priority<strong>of</strong> accessing channel to the users with better channel conditions,another algorithm separates the contention windowsfor nodes at different bit rates as illustrated on the right <strong>of</strong>Figure 1. In this approach, the initial contention window is stillcomputed as in Formula 1. However, unlike the OverlappedContention that maintains the same lower bound <strong>of</strong> “0”for all contention windows, this algorithm differentiates thelower bounds <strong>of</strong> the contention window for different channelconditions. A higher bit rate results in an upper bound <strong>of</strong> thecontention window smaller than the lower bound <strong>of</strong> a node ata lower bit rate. For example, on the right <strong>of</strong> Figure 1, W i maxand W i+1 max respectively denote the computed initial upperbounds <strong>of</strong> the contention window <strong>of</strong> bit rate R i and R i+1according to Formula 1. Then, the lower bound <strong>of</strong> the contentionwindow CW i <strong>of</strong> bit rate R i is assigned the value that islarger by one than W i+1 max , the upper bound <strong>of</strong> CW i+1 , i.e.the window is [W i+1 max + 1, W i max ]. This segments thecontention <strong>of</strong> nodes with different channel conditions in that anode at bit rate R i can never get a back<strong>of</strong>f value smaller than anode at bit rate R i+1 . This approach can be considered semiprobabilisticin that (1) the access <strong>of</strong> the nodes at the same bitrate is random since they have the same initial window size torandomly generate a back<strong>of</strong>f value, but (2) the access <strong>of</strong> nodesat different rates is deterministically prioritized because thelower rate nodes can never get a smaller back<strong>of</strong>f value than thehigher rate nodes. This approach provides a tight opportunismby grouping nodes with similar channel conditions into thesame random access team at the cost <strong>of</strong> randomness acrossteams. Note that this approach leads to a significant problem:starvation <strong>of</strong> nodes with poor conditions. This problem willbe addressed in Section IV-C.B. Normal Distribution Based Back<strong>of</strong>f SelectionIn the Overlapped Contention, although nodes with differentchannel conditions obtain different initial contention windows,each node still uses a uniform distribution to select theback<strong>of</strong>f value from its contention window. The third proposedopportunistic access approach consists <strong>of</strong> using a normal ratherthan a uniform distribution, in selecting the back<strong>of</strong>f value oncethe contention window is determined as in the OverlappedContention. With the expectation <strong>of</strong> the normal distribution setto a proper value within the contention window and a properstandard deviation, a node with higher bit rate has significantlygreater probability to obtain a smaller back<strong>of</strong>f value than alower bit rate node. Systematically, the expectation <strong>of</strong> thenormal distribution <strong>of</strong> a node at rate R is computed as below:E = ⌈ CW 2 ⌉ (2)where CW is computed as in Formula 1.Let us examine anexample where a networkhas two nodesA at rate R andB at rate R 2 . Then,the expectations <strong>of</strong>the normal distributionat A and Bare respectively setas N 4 and N 2to selecttheir back<strong>of</strong>f valuesas shown in Figure 2.As a result, in thelong run, A will selecta smaller back<strong>of</strong>f value than B because most likelyFig. 2: Normal Distribution Back<strong>of</strong>fthe