Download - Cloud Security Alliance
Download - Cloud Security Alliance
Download - Cloud Security Alliance
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
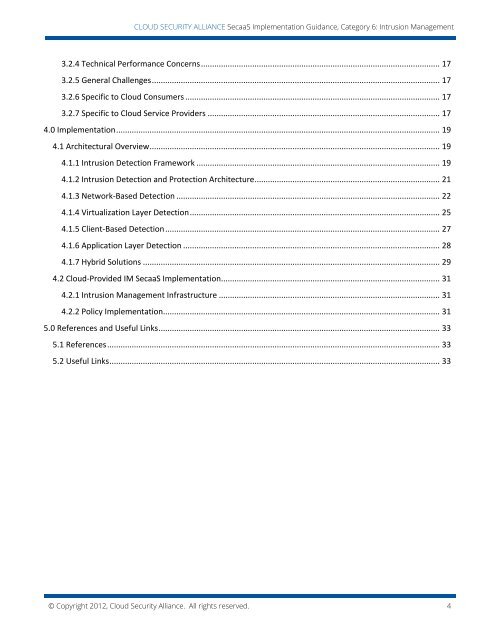
CLOUD SECURITY ALLIANCE SecaaS Implementation Guidance, Category 6: Intrusion Management3.2.4 Technical Performance Concerns........................................................................................................... 173.2.5 General Challenges................................................................................................................................. 173.2.6 Specific to <strong>Cloud</strong> Consumers .................................................................................................................. 173.2.7 Specific to <strong>Cloud</strong> Service Providers ........................................................................................................ 174.0 Implementation................................................................................................................................................. 194.1 Architectural Overview.................................................................................................................................. 194.1.1 Intrusion Detection Framework ............................................................................................................. 194.1.2 Intrusion Detection and Protection Architecture................................................................................... 214.1.3 Network-Based Detection ...................................................................................................................... 224.1.4 Virtualization Layer Detection................................................................................................................ 254.1.5 Client-Based Detection........................................................................................................................... 274.1.6 Application Layer Detection ................................................................................................................... 284.1.7 Hybrid Solutions ..................................................................................................................................... 294.2 <strong>Cloud</strong>-Provided IM SecaaS Implementation.................................................................................................. 314.2.1 Intrusion Management Infrastructure ................................................................................................... 314.2.2 Policy Implementation............................................................................................................................ 315.0 References and Useful Links.............................................................................................................................. 335.1 References..................................................................................................................................................... 335.2 Useful Links.................................................................................................................................................... 33© Copyright 2012, <strong>Cloud</strong> <strong>Security</strong> <strong>Alliance</strong>. All rights reserved. 4