Chapter 11 Intrusion Detection System
Chapter 11 Intrusion Detection System
Chapter 11 Intrusion Detection System
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
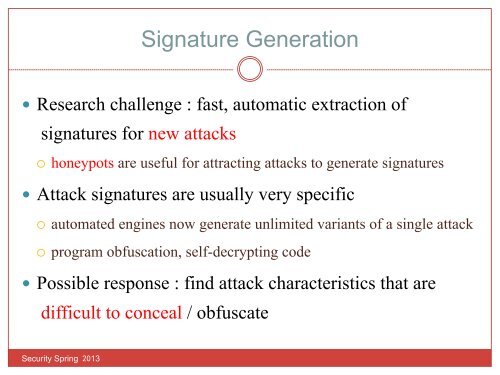
Signature Generation Research challenge : fast, automatic extraction ofsignatures for new attacks¡ honeypots are useful for attracting attacks to generate signatures Attack signatures are usually very specific¡ automated engines now generate unlimited variants of a single attack¡ program obfuscation, self-decrypting code Possible response : find attack characteristics that aredifficult to conceal / obfuscateSecurity Spring 2013