Chapter 11 Intrusion Detection System
Chapter 11 Intrusion Detection System
Chapter 11 Intrusion Detection System
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
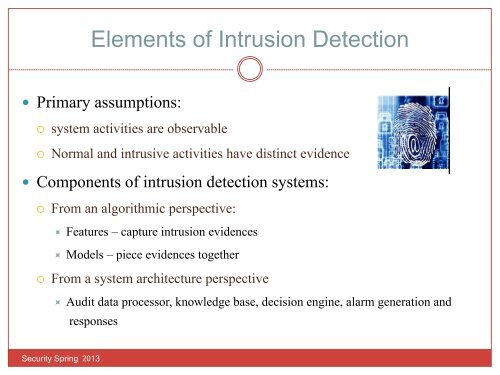
Elements of <strong>Intrusion</strong> <strong>Detection</strong>ents of <strong>Intrusion</strong> <strong>Detection</strong>ary assumptions: Primary assumptions:stem activities are observable¡ system activities are observableormal and intrusive activities have distinct¡ Normal and intrusive activities have distinct evidenceidence Components of intrusion detection systems:ponents of intrusion detection systems:¡ From an algorithmic perspective:om an algorithmic perspective:÷ Features – capture intrusion evidencesFeatures ÷ Models - capture – piece evidences intrusion together evidencesModels - piece evidences together¡ From a system architecture perspectiveom a system architecture perspective:÷ Audit data processor, knowledge base, decision engine, alarm generation andresponsesAudit data processor, knowledge base, decisionengine, alarm generation and responsesSecurity Spring 2013