- Page 5 and 6:
Chapter 2: Code Vulnerabilities due
- Page 7 and 8:
Enforcing Data Integrity in the App
- Page 9 and 10:
About the AuthorAlex Kuznetsov has
- Page 11 and 12:
IntroductionResilient T-SQL code is
- Page 13 and 14:
IntroductionCh. 02: Code Vulnerabil
- Page 15 and 16:
IntroductionSpecific examples demon
- Page 17:
IntroductionWhat this book does not
- Page 21 and 22:
Chapter 1: Basic Defensive Database
- Page 24 and 25:
Chapter 1: Basic Defensive Database
- Page 26 and 27:
Chapter 1: Basic Defensive Database
- Page 28 and 29:
Chapter 1: Basic Defensive Database
- Page 30 and 31:
Chapter 1: Basic Defensive Database
- Page 32 and 33:
Chapter 1: Basic Defensive Database
- Page 34 and 35:
Chapter 1: Basic Defensive Database
- Page 36 and 37:
Chapter 1: Basic Defensive Database
- Page 38 and 39:
Chapter 1: Basic Defensive Database
- Page 40 and 41:
Chapter 1: Basic Defensive Database
- Page 42 and 43:
Chapter 1: Basic Defensive Database
- Page 44 and 45:
Chapter 1: Basic Defensive Database
- Page 46 and 47:
Chapter 1: Basic Defensive Database
- Page 48 and 49:
Chapter 1: Basic Defensive Database
- Page 50 and 51:
Chapter 1: Basic Defensive Database
- Page 52 and 53:
Chapter 1: Basic Defensive Database
- Page 54 and 55:
Chapter 1: Basic Defensive Database
- Page 57 and 58:
Chapter 2: Code Vulnerabilitiesdue
- Page 59 and 60:
Chapter 2: Code Vulnerabilities due
- Page 61 and 62:
Chapter 2: Code Vulnerabilities due
- Page 63 and 64:
Chapter 2: Code Vulnerabilities due
- Page 65 and 66:
Chapter 2: Code Vulnerabilities due
- Page 67 and 68:
Chapter 2: Code Vulnerabilities due
- Page 69 and 70:
Chapter 2: Code Vulnerabilities due
- Page 71 and 72:
Chapter 2: Code Vulnerabilities due
- Page 73 and 74:
Chapter 2: Code Vulnerabilities due
- Page 75:
Chapter 2: Code Vulnerabilities due
- Page 78 and 79: Chapter 3: Surviving Changes to Dat
- Page 80 and 81: Chapter 3: Surviving Changes to Dat
- Page 82 and 83: Chapter 3: Surviving Changes to Dat
- Page 84 and 85: Chapter 3: Surviving Changes to Dat
- Page 86 and 87: Chapter 3: Surviving Changes to Dat
- Page 88 and 89: Chapter 3: Surviving Changes to Dat
- Page 90 and 91: Chapter 3: Surviving Changes to Dat
- Page 92 and 93: Chapter 3: Surviving Changes to Dat
- Page 94 and 95: Chapter 3: Surviving Changes to Dat
- Page 96 and 97: Chapter 3: Surviving Changes to Dat
- Page 98 and 99: Chapter 3: Surviving Changes to Dat
- Page 100 and 101: Chapter 3: Surviving Changes to Dat
- Page 102 and 103: Chapter 3: Surviving Changes to Dat
- Page 104 and 105: 104
- Page 106: Chapter 4: When Upgrading Breaks Co
- Page 109 and 110: Chapter 4: When Upgrading Breaks Co
- Page 111 and 112: Chapter 4: When Upgrading Breaks Co
- Page 113 and 114: Chapter 4: When Upgrading Breaks Co
- Page 115 and 116: Chapter 4: When Upgrading Breaks Co
- Page 117 and 118: Chapter 4: When Upgrading Breaks Co
- Page 119 and 120: Chapter 4: When Upgrading Breaks Co
- Page 121 and 122: Chapter 4: When Upgrading Breaks Co
- Page 123 and 124: Chapter 4: When Upgrading Breaks Co
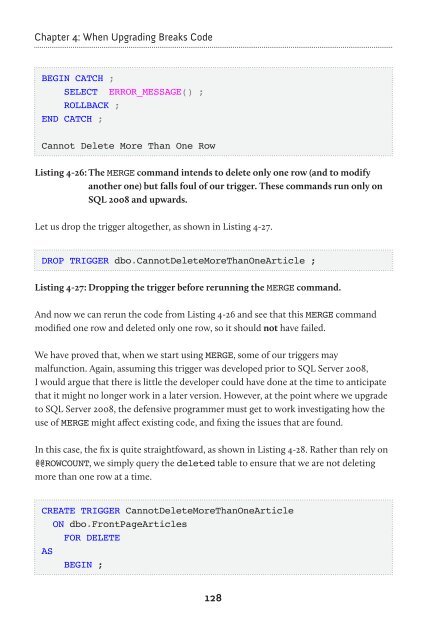
- Page 125 and 126: Chapter 4: When Upgrading Breaks Co
- Page 127: Chapter 4: When Upgrading Breaks Co
- Page 131 and 132: Chapter 5: Reusing T-SQL CodeOften,
- Page 133 and 134: Chapter 5: Reusing T-SQL CodeUNION
- Page 135 and 136: Chapter 5: Reusing T-SQL CodeALTER
- Page 137 and 138: Chapter 5: Reusing T-SQL CodeHow Re
- Page 139 and 140: Chapter 5: Reusing T-SQL Code( SELE
- Page 141 and 142: Chapter 5: Reusing T-SQL CodeOver t
- Page 143 and 144: Chapter 5: Reusing T-SQL Code( Amou
- Page 145 and 146: Chapter 5: Reusing T-SQL CodeAs per
- Page 147 and 148: Chapter 5: Reusing T-SQL CodeScalar
- Page 149 and 150: Chapter 5: Reusing T-SQL CodeCREATE
- Page 151 and 152: Chapter 5: Reusing T-SQL Code……
- Page 153 and 154: Chapter 5: Reusing T-SQL CodeCREATE
- Page 155 and 156: Chapter 5: Reusing T-SQL CodeSuppos
- Page 157 and 158: Chapter 5: Reusing T-SQL Code'Hobar
- Page 159 and 160: Chapter 5: Reusing T-SQL CodeUNION
- Page 161 and 162: Chapter 5: Reusing T-SQL Code• be
- Page 163 and 164: Chapter 6: Common Problemswith Data
- Page 165 and 166: Chapter 6: Common Problems with Dat
- Page 167 and 168: Chapter 6: Common Problems with Dat
- Page 169 and 170: Chapter 6: Common Problems with Dat
- Page 171 and 172: Chapter 6: Common Problems with Dat
- Page 173 and 174: Chapter 6: Common Problems with Dat
- Page 175 and 176: Chapter 6: Common Problems with Dat
- Page 177 and 178: Chapter 6: Common Problems with Dat
- Page 179 and 180:
Chapter 6: Common Problems with Dat
- Page 181 and 182:
Chapter 6: Common Problems with Dat
- Page 183 and 184:
Chapter 6: Common Problems with Dat
- Page 185 and 186:
Chapter 6: Common Problems with Dat
- Page 187 and 188:
Chapter 6: Common Problems with Dat
- Page 189 and 190:
Chapter 6: Common Problems with Dat
- Page 191 and 192:
Chapter 6: Common Problems with Dat
- Page 193 and 194:
Chapter 6: Common Problems with Dat
- Page 195 and 196:
Chapter 6: Common Problems with Dat
- Page 197 and 198:
Chapter 6: Common Problems with Dat
- Page 199 and 200:
Chapter 6: Common Problems with Dat
- Page 201 and 202:
Chapter 6: Common Problems with Dat
- Page 203:
Chapter 6: Common Problems with Dat
- Page 206 and 207:
Chapter 6: Common Problems with Dat
- Page 208 and 209:
Chapter 6: Common Problems with Dat
- Page 210 and 211:
Chapter 7: Advanced Use of Constrai
- Page 212 and 213:
Chapter 7: Advanced Use of Constrai
- Page 214 and 215:
Chapter 7: Advanced Use of Constrai
- Page 216 and 217:
Chapter 7: Advanced Use of Constrai
- Page 218 and 219:
Chapter 7: Advanced Use of Constrai
- Page 220 and 221:
Chapter 7: Advanced Use of Constrai
- Page 222 and 223:
Chapter 7: Advanced Use of Constrai
- Page 224 and 225:
Chapter 7: Advanced Use of Constrai
- Page 226 and 227:
Chapter 7: Advanced Use of Constrai
- Page 228 and 229:
Chapter 7: Advanced Use of Constrai
- Page 230 and 231:
Chapter 7: Advanced Use of Constrai
- Page 232 and 233:
Chapter 7: Advanced Use of Constrai
- Page 234 and 235:
Chapter 7: Advanced Use of Constrai
- Page 236 and 237:
Chapter 7: Advanced Use of Constrai
- Page 238 and 239:
Chapter 7: Advanced Use of Constrai
- Page 240 and 241:
Chapter 7: Advanced Use of Constrai
- Page 242 and 243:
Chapter 7: Advanced Use of Constrai
- Page 244 and 245:
Chapter 7: Advanced Use of Constrai
- Page 246 and 247:
Chapter 7: Advanced Use of Constrai
- Page 248 and 249:
Chapter 7: Advanced Use of Constrai
- Page 250 and 251:
Chapter 7: Advanced Use of Constrai
- Page 252 and 253:
Chapter 7: Advanced Use of Constrai
- Page 254 and 255:
Chapter 7: Advanced Use of Constrai
- Page 256 and 257:
Chapter 8: Defensive Error Handling
- Page 258 and 259:
Chapter 8: Defensive Error Handling
- Page 260 and 261:
Chapter 8: Defensive Error Handling
- Page 262 and 263:
Chapter 8: Defensive Error Handling
- Page 264 and 265:
Chapter 8: Defensive Error Handling
- Page 266 and 267:
Chapter 8: Defensive Error Handling
- Page 268 and 269:
Chapter 8: Defensive Error Handling
- Page 270 and 271:
Chapter 8: Defensive Error Handling
- Page 272 and 273:
Chapter 8: Defensive Error Handling
- Page 274 and 275:
Chapter 8: Defensive Error Handling
- Page 276 and 277:
Chapter 8: Defensive Error Handling
- Page 278 and 279:
Chapter 8: Defensive Error Handling
- Page 280 and 281:
Chapter 8: Defensive Error Handling
- Page 282 and 283:
Chapter 8: Defensive Error Handling
- Page 284 and 285:
Chapter 8: Defensive Error Handling
- Page 286 and 287:
Chapter 8: Defensive Error Handling
- Page 288 and 289:
Chapter 8: Defensive Error Handling
- Page 290 and 291:
Chapter 8: Defensive Error Handling
- Page 292:
About Red GateYou know those annoyi