Persistent Asynchronous and Fileless Backdoor
us-15-Graeber-Abusing-Windows-Management-Instrumentation-WMI-To-Build-A-Persistent Asynchronous-And-Fileless-Backdoor
us-15-Graeber-Abusing-Windows-Management-Instrumentation-WMI-To-Build-A-Persistent Asynchronous-And-Fileless-Backdoor
- No tags were found...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
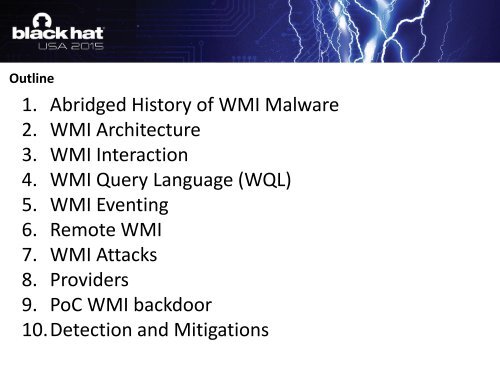
Outline1. Abridged History of WMI Malware2. WMI Architecture3. WMI Interaction4. WMI Query Language (WQL)5. WMI Eventing6. Remote WMI7. WMI Attacks8. Providers9. PoC WMI backdoor10.Detection <strong>and</strong> Mitigations