Usability and Security
Usability and Security - Vurore
Usability and Security - Vurore
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
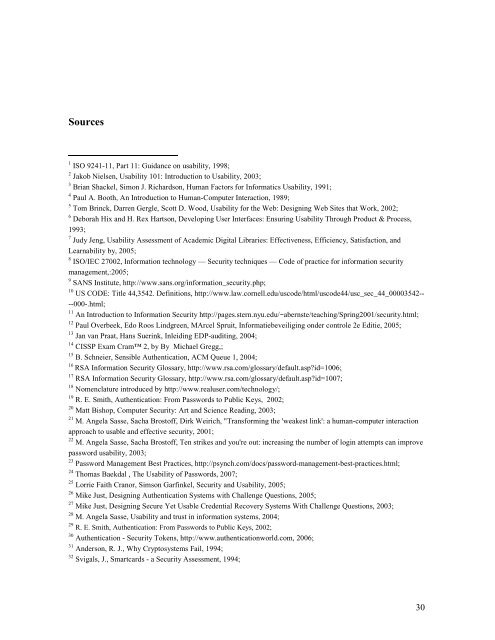
Sources1 ISO 9241-11, Part 11: Guidance on usability, 1998;2 Jakob Nielsen, <strong>Usability</strong> 101: Introduction to <strong>Usability</strong>, 2003;3 Brian Shackel, Simon J. Richardson, Human Factors for Informatics <strong>Usability</strong>, 1991;4 Paul A. Booth, An Introduction to Human-Computer Interaction, 1989;5 Tom Brinck, Darren Gergle, Scott D. Wood, <strong>Usability</strong> for the Web: Designing Web Sites that Work, 2002;6 Deborah Hix <strong>and</strong> H. Rex Hartson, Developing User Interfaces: Ensuring <strong>Usability</strong> Through Product & Process,1993;7 Judy Jeng, <strong>Usability</strong> Assessment of Academic Digital Libraries: Effectiveness, Efficiency, Satisfaction, <strong>and</strong>Learnability by, 2005;8 ISO/IEC 27002, Information technology — <strong>Security</strong> techniques — Code of practice for information securitymanagement,:2005;9 SANS Institute, http://www.sans.org/information_security.php;10 US CODE: Title 44,3542. Definitions, http://www.law.cornell.edu/uscode/html/uscode44/usc_sec_44_00003542----000-.html;11 An Introduction to Information <strong>Security</strong> http://pages.stern.nyu.edu/~abernste/teaching/Spring2001/security.html;12 Paul Overbeek, Edo Roos Lindgreen, MArcel Spruit, Informatiebeveiliging onder controle 2e Editie, 2005;13 Jan van Praat, Hans Suerink, Inleiding EDP-auditing, 2004;14 CISSP Exam Cram 2, by By Michael Gregg,;15 B. Schneier, Sensible Authentication, ACM Queue 1, 2004;16RSA Information <strong>Security</strong> Glossary, http://www.rsa.com/glossary/default.asp?id=1006;17 RSA Information <strong>Security</strong> Glossary, http://www.rsa.com/glossary/default.asp?id=1007;18 Nomenclature introduced by http://www.realuser.com/technology/;19 R. E. Smith, Authentication: From Passwords to Public Keys, 2002;20 Matt Bishop, Computer <strong>Security</strong>: Art <strong>and</strong> Science Reading, 2003;21 M. Angela Sasse, Sacha Brostoff, Dirk Weirich, "Transforming the 'weakest link': a human-computer interactionapproach to usable <strong>and</strong> effective security, 2001;22 M. Angela Sasse, Sacha Brostoff, Ten strikes <strong>and</strong> you're out: increasing the number of login attempts can improvepassword usability, 2003;23 Password Management Best Practices, http://psynch.com/docs/password-management-best-practices.html;24 Thomas Baekdal , The <strong>Usability</strong> of Passwords, 2007;25 Lorrie Faith Cranor, Simson Garfinkel, <strong>Security</strong> <strong>and</strong> <strong>Usability</strong>, 2005;26 Mike Just, Designing Authentication Systems with Challenge Questions, 2005;27 Mike Just, Designing Secure Yet Usable Credential Recovery Systems With Challenge Questions, 2003;28 M. Angela Sasse, <strong>Usability</strong> <strong>and</strong> trust in information systems, 2004;29 R. E. Smith, Authentication: From Passwords to Public Keys, 2002;30 Authentication - <strong>Security</strong> Tokens, http://www.authenticationworld.com, 2006;31 Anderson, R. J., Why Cryptosystems Fail, 1994;32 Svigals, J., Smartcards - a <strong>Security</strong> Assessment, 1994;30