4.0
1IZ1TDd
1IZ1TDd
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
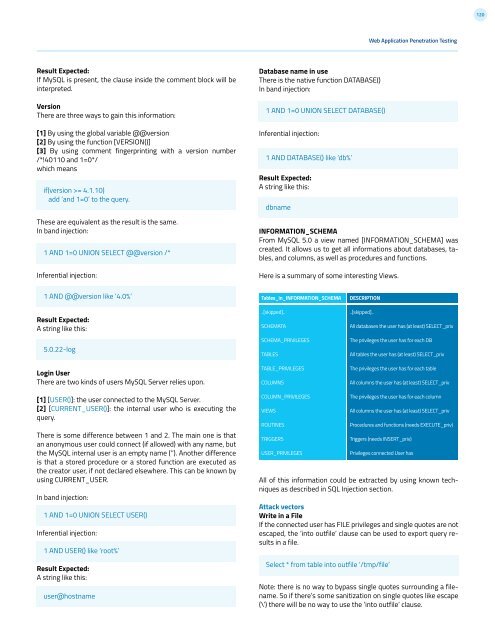
120Web Application Penetration TestingResult Expected:If MySQL is present, the clause inside the comment block will beinterpreted.VersionThere are three ways to gain this information:[1] By using the global variable @@version[2] By using the function [VERSION()][3] By using comment fingerprinting with a version number/*!40110 and 1=0*/which meansif(version >= 4.1.10)add ‘and 1=0’ to the query.These are equivalent as the result is the same.In band injection:1 AND 1=0 UNION SELECT @@version /*Inferential injection:Database name in useThere is the native function DATABASE()In band injection:1 AND 1=0 UNION SELECT DATABASE()Inferential injection:1 AND DATABASE() like ‘db%’Result Expected:A string like this:dbnameINFORMATION_SCHEMAFrom MySQL 5.0 a view named [INFORMATION_SCHEMA] wascreated. It allows us to get all informations about databases, tables,and columns, as well as procedures and functions.Here is a summary of some interesting Views.1 AND @@version like ‘<strong>4.0</strong>%’Result Expected:A string like this:5.0.22-logLogin UserThere are two kinds of users MySQL Server relies upon.Tables_in_INFORMATION_SCHEMA..[skipped]..SCHEMATASCHEMA_PRIVILEGESTABLESTABLE_PRIVILEGESCOLUMNSDESCRIPTION..[skipped]..All databases the user has (at least) SELECT_privThe privileges the user has for each DBAll tables the user has (at least) SELECT_privThe privileges the user has for each tableAll columns the user has (at least) SELECT_priv[1] [USER()]: the user connected to the MySQL Server.[2] [CURRENT_USER()]: the internal user who is executing thequery.There is some difference between 1 and 2. The main one is thatan anonymous user could connect (if allowed) with any name, butthe MySQL internal user is an empty name (‘’). Another differenceis that a stored procedure or a stored function are executed asthe creator user, if not declared elsewhere. This can be known byusing CURRENT_USER.In band injection:1 AND 1=0 UNION SELECT USER()Inferential injection:1 AND USER() like ‘root%’Result Expected:A string like this:user@hostnameCOLUMN_PRIVILEGESVIEWSROUTINESTRIGGERSUSER_PRIVILEGESThe privileges the user has for each columnAll columns the user has (at least) SELECT_privProcedures and functions (needs EXECUTE_priv)Triggers (needs INSERT_priv)Privileges connected User hasAll of this information could be extracted by using known techniquesas described in SQL Injection section.Attack vectorsWrite in a FileIf the connected user has FILE privileges and single quotes are notescaped, the ‘into outfile’ clause can be used to export query resultsin a file.Select * from table into outfile ‘/tmp/file’Note: there is no way to bypass single quotes surrounding a filename.So if there’s some sanitization on single quotes like escape(\’) there will be no way to use the ‘into outfile’ clause.