presentation departments reproduced
Spring 2004 - Air and Space Power Journal - Air Force Link
Spring 2004 - Air and Space Power Journal - Air Force Link
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
80 AIR & SPACE POWER JOURNAL SPRING 2004<br />
Air Force ground, air, cyber, and space systems.<br />
Broad areas of investment in science and technology<br />
include upper-level information fusion,<br />
communications, EBO, collaboration environments,<br />
distributed-information infrastructures,<br />
modeling and simulation, intelligent agents,<br />
information assurance, information management,<br />
and intelligent information systems and<br />
databases. Successful outcomes from these<br />
areas provide affordable capability options required<br />
for Air Force information dominance<br />
and air and space superiority. To provide these<br />
capabilities, the AFRL/IF has three major<br />
thrusts—Global Awareness, Dynamic Planning<br />
and Execution, and the Global Information<br />
Enterprise—that receive support from seven<br />
technology-focus areas: information exploitation,<br />
information fusion and understanding,<br />
information management, advanced computing<br />
architectures, cyber operations, air and<br />
space connectivity, and C2.<br />
Information Exploitation<br />
Given the growing threat of global terrorism,<br />
the potential use and exploitation of readily<br />
available information technology by our adversaries<br />
make it imperative that the United States<br />
continue to invest in technologies for the protection<br />
and authentication of digital information<br />
systems for the military and homeland defense.<br />
Toward that end, the AFRL/IF conducts<br />
advanced research and development in the<br />
field of digital data-embedding technology.<br />
The directorate’s work in such areas as information<br />
hiding, steganography, watermarking,<br />
steganalysis, and digital data forensics will<br />
greatly enhance war fighters’ ability to exploit<br />
enemy systems while providing greater security<br />
to ensure that an adversary does not have access<br />
to US and allied systems.<br />
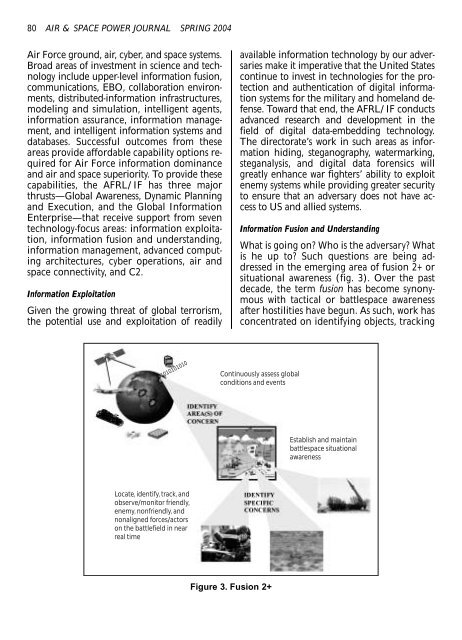
Information Fusion and Understanding<br />
What is going on? Who is the adversary? What<br />
is he up to? Such questions are being addressed<br />
in the emerging area of fusion 2+ or<br />
situational awareness (fig. 3). Over the past<br />
decade, the term fusion has become synonymous<br />
with tactical or battlespace awareness<br />
after hostilities have begun. As such, work has<br />
concentrated on identifying objects, tracking<br />
01010101010<br />
Continuously assess global<br />
conditions and events<br />
Establish and maintain<br />
battlespace situational<br />
awareness<br />
Locate, identify, track, and<br />
observe/monitor friendly,<br />
enemy, nonfriendly, and<br />
nonaligned forces/actors<br />
on the battlefield in near<br />
real time<br />
Figure 3. Fusion 2+