BATTLE OF SKM AND IUM
1MHMIxh
1MHMIxh
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
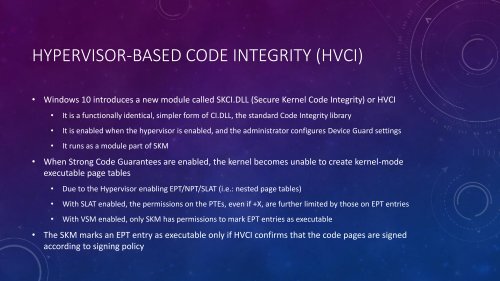
HYPERVISOR-BASED CODE INTEGRITY (HVCI)<br />
• Windows 10 introduces a new module called SKCI.DLL (Secure Kernel Code Integrity) or HVCI<br />
• It is a functionally identical, simpler form of CI.DLL, the standard Code Integrity library<br />
• It is enabled when the hypervisor is enabled, and the administrator configures Device Guard settings<br />
• It runs as a module part of <strong>SKM</strong><br />
• When Strong Code Guarantees are enabled, the kernel becomes unable to create kernel-mode<br />
executable page tables<br />
• Due to the Hypervisor enabling EPT/NPT/SLAT (i.e.: nested page tables)<br />
• With SLAT enabled, the permissions on the PTEs, even if +X, are further limited by those on EPT entries<br />
• With VSM enabled, only <strong>SKM</strong> has permissions to mark EPT entries as executable<br />
• The <strong>SKM</strong> marks an EPT entry as executable only if HVCI confirms that the code pages are signed<br />
according to signing policy