CYBER SECURITY INCIDENT MANAGEMENT GUIDE
Cyber-Security-Incident-Management-Guide-2015
Cyber-Security-Incident-Management-Guide-2015
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
01 PREPARING FOR A <strong>CYBER</strong> <strong>SECURITY</strong> <strong>INCIDENT</strong> 9<br />
II.<br />
CONTENT OF A <strong>CYBER</strong> <strong>SECURITY</strong><br />
<strong>INCIDENT</strong> RESPONSE PLAN<br />
KNOW WHAT TO<br />
PROTECT<br />
IDENTIFY YOUR ASSETS AND<br />
POTENTIAL THREATS<br />
When hit by an incident the first questions<br />
that will arise are: which assets are at risk?<br />
And which of those assets are vital for your<br />
business’s activity? You will have to decide<br />
which assets need your attention first in<br />
order to remain in business and keep the<br />
damage to your business as low as possible.<br />
That’s why it is crucial to identify, document<br />
and categorise your organisation’s ‘vitals’:<br />
the assets your organisation depends on<br />
to conduct its core activities. This will help<br />
you identify where to apply which protective<br />
measures and to take quick and justified<br />
decisions during the incident management<br />
process.<br />
1.<br />
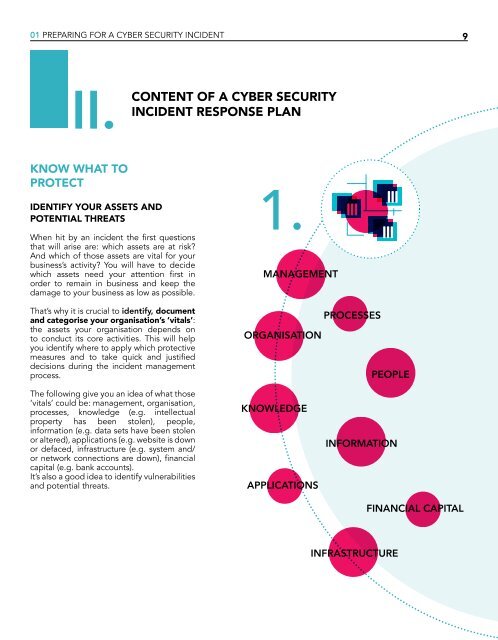
<strong>MANAGEMENT</strong><br />
PROCESSES<br />
ORGANISATION<br />
PEOPLE<br />
The following give you an idea of what those<br />
‘vitals’ could be: management, organisation,<br />
processes, knowledge (e.g. intellectual<br />
property has been stolen), people,<br />
information (e.g. data sets have been stolen<br />
or altered), applications (e.g. website is down<br />
or defaced, infrastructure (e.g. system and/<br />
or network connections are down), financial<br />
capital (e.g. bank accounts).<br />
It’s also a good idea to identify vulnerabilities<br />
and potential threats.<br />
KNOWLEDGE<br />
APPLICATIONS<br />
INFORMATION<br />
FINANCIAL CAPITAL<br />
INFRASTRUCTURE