SECURITY BASICS
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Copyright © 2004 by Course Technology. All rights reserved.This publication is protected by federal copyright law. No part of this publication<br />
may be reproduced without prior permission in writing from Course Technology. Some of the product names and company names have been<br />
used for identification purposes only and may be trademarks or registered trademarks of their respective manufactures and sellers.<br />
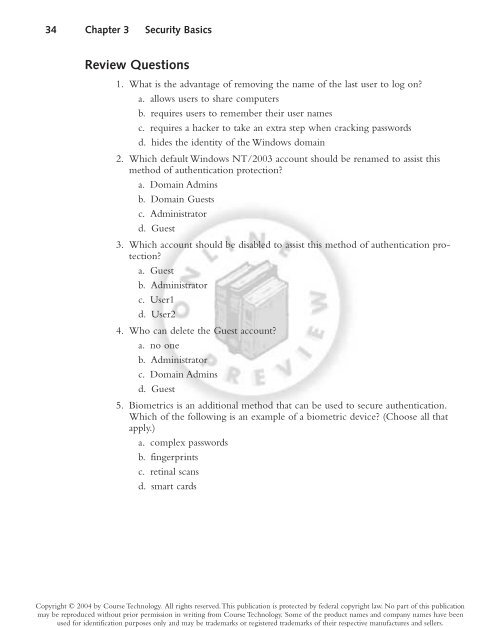
34 Chapter 3 Security Basics<br />
Review Questions<br />
1. What is the advantage of removing the name of the last user to log on?<br />
a. allows users to share computers<br />
b. requires users to remember their user names<br />
c. requires a hacker to take an extra step when cracking passwords<br />
d. hides the identity of the Windows domain<br />
2. Which default Windows NT/2003 account should be renamed to assist this<br />
method of authentication protection?<br />
a. Domain Admins<br />
b. Domain Guests<br />
c. Administrator<br />
d. Guest<br />
3. Which account should be disabled to assist this method of authentication protection?<br />
a. Guest<br />
b. Administrator<br />
c. User1<br />
d. User2<br />
4. Who can delete the Guest account?<br />
a. no one<br />
b. Administrator<br />
c. Domain Admins<br />
d. Guest<br />
5. Biometrics is an additional method that can be used to secure authentication.<br />
Which of the following is an example of a biometric device? (Choose all that<br />
apply.)<br />
a. complex passwords<br />
b. fingerprints<br />
c. retinal scans<br />
d. smart cards