Government Security News August Digital Edition
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
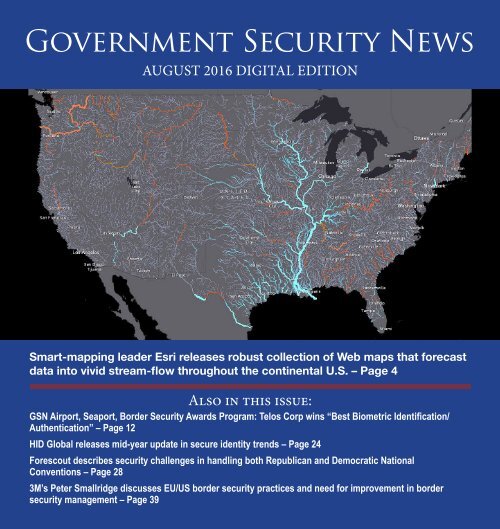
<strong>Government</strong> <strong>Security</strong> <strong>News</strong><br />
AUGUST 2016 DIGITAL EDITION<br />
Smart-mapping leader Esri releases robust collection of Web maps that forecast<br />
data into vivid stream-flow throughout the continental U.S. – Page 4<br />
Also in this issue:<br />
GSN Airport, Seaport, Border <strong>Security</strong> Awards Program: Telos Corp wins “Best Biometric Identification/<br />
Authentication” – Page 12<br />
HID Global releases mid-year update in secure identity trends – Page 24<br />
Forescout describes security challenges in handling both Republican and Democratic National<br />
Conventions – Page 28<br />
3M’s Peter Smallridge discusses EU/US border security practices and need for improvement in border<br />
security management – Page 39
GSN <strong>August</strong> 2016 <strong>Digital</strong><br />
NEWS<br />
4<br />
5<br />
7<br />
10<br />
12<br />
14<br />
15<br />
18<br />
20<br />
22<br />
24<br />
28<br />
Smart-mapping leader Esri releases robust<br />
collection of Web maps that forecast data into<br />
vivid stream-flow throughout the continental U.S.<br />
IntraLogic Solutions to announce first ever<br />
National Common Operating Picture (COP) platform for first<br />
responders allowing immediate 9-1-1 notification<br />
Senators Grassley/Leahy, press federal investigators on breach of<br />
Democratic National Committee<br />
Cypherpath, Quali partnership provides portable containerized<br />
infrastructures that support virtual sand boxes and cyber ranges<br />
GSN Airport, Seaport, Border <strong>Security</strong> Awards Program: Telos Corp<br />
wins “Best Biometric Identification/Authentication”<br />
Cellebrite introduces UFED Touch2 platform for<br />
standalone mobile Forensic solutions<br />
Controp’s airborne EO/IR Surveillance<br />
Camera payload protects Olympic games<br />
ECN acquires MIR3, extends SaaS-based unified critical<br />
communications platform to enterprise clients<br />
Climate Change – This is what it’s going to look<br />
like! A dispatch from Baton Rouge from<br />
George Lane, GSN Columnist<br />
Convy on Net-Centric <strong>Security</strong> – Securing the Internet of Things<br />
HID Global releases mid-year update on top trends for secure identity<br />
Forescout describes security challenges of handling both Republication<br />
and Democratic National Conventions<br />
2
<strong>Edition</strong> Table of Contents<br />
FEATURES<br />
SPECIAL REPORT: Border <strong>Security</strong>/Immigration<br />
30<br />
31<br />
32<br />
Why the Department of Homeland <strong>Security</strong> should<br />
also end private prison contracts<br />
Donald Trump’s shortsighted immigration plans<br />
won’t secure the homeland<br />
<strong>Government</strong> sued for withholding records on<br />
immigration raids<br />
33<br />
35<br />
36<br />
37<br />
Court order release of graphic photos of Arizona<br />
Border Patrol detection facilities<br />
3M’s new ALPR software extends reach,<br />
delivers real-time actionable intelligence<br />
DevMynd obtains strategic investment<br />
from Motorola Solutions<br />
Albuquerque police fight violence with<br />
intelligence-led policing<br />
SPECIAL REPORT: Access Control/Biometric ID<br />
39<br />
3M’s Peter Smallridge discusses EU/US border<br />
security practices and need for improvement in<br />
border security management<br />
41<br />
LBsecure promotes best-of-class granular<br />
and layered security solutions for its clients<br />
within SAP<br />
3
New Esri Maps NOAA’s National Model forecast<br />
data into vivid pictures of U.S. river flows<br />
REDLANDS, CA—<strong>August</strong> 25, 2016<br />
—Smart-mapping leader Esri today<br />
released a beautiful, robust new<br />
collection of Web maps that forecast<br />
NOAA stream-flow data throughout<br />
the continental U.S.<br />
Esri’s multiscale visualization<br />
of the National Water<br />
Model enables forecast water<br />
flows in real time at high<br />
resolution. The maps weave<br />
together NOAA’s recently released<br />
water model data and<br />
Esri ArcGIS functionality to<br />
provide interactive views of current<br />
and future water-system behaviors.<br />
Esri maps the flow of water along<br />
2.7 million stream segments in the<br />
U.S. river network. These data-rich<br />
maps improve NOAA’s ability to<br />
meet the needs of emergency responders,<br />
reservoir operators, ecosystem<br />
professionals, and floodplain<br />
managers by providing detailed information<br />
that can anticipate flood<br />
and drought conditions. National<br />
Weather Service data populates the<br />
interactive maps with hourly updates<br />
and forecasts up to 10 days.<br />
“In collaboration with our academic<br />
partners, the Esri team supported<br />
the development process<br />
leading up to the launch of the National<br />
Water Model,” said Edward<br />
Clark, director of geointelligence at<br />
NOAA. “We share a common vision<br />
for the value that high-resolution<br />
water prediction brings to the nation.”<br />
Esri’s new maps enable users to<br />
access large amounts of complex<br />
data quickly and easily. Although<br />
10-day, mid-range forecasts contain<br />
more than 200 million records and<br />
short-term forecasts require hourly<br />
data refresh, Esri maps automatically<br />
integrate and synthesize NOAA<br />
data so that users have the real-time<br />
information they need at the click of<br />
a button.<br />
“These attractive, accessible maps<br />
are part of our commitment to improve<br />
water awareness—a commitment<br />
we made at the White House<br />
Water Summit earlier this year,” said<br />
Esri President Jack Dangermond.<br />
“ArcGIS provides a visually engaging<br />
way to communicate complex<br />
scientific information simply so that<br />
4<br />
anyone can understand it.”<br />
Esri plans to continue its investment<br />
in water prediction and analysis<br />
by releasing an open-source<br />
toolkit later this year that will enable<br />
ArcGIS users to analyze<br />
data and create custom maps<br />
from water model records.<br />
About Esri<br />
Since 1969, Esri has been<br />
giving customers around the<br />
world the power to think<br />
and plan geographically. The<br />
market leader in GIS technology,<br />
Esri software is used in more than<br />
300,000 organizations worldwide<br />
including each of the 200 largest<br />
cities in the United States, most<br />
national governments, more than<br />
two-thirds of Fortune 500 companies,<br />
and more than 7,000 colleges<br />
and universities. Esri applications,<br />
running on more than one million<br />
desktops and thousands of Web<br />
and enterprise servers, provide the<br />
backbone for the world’s mapping<br />
and spatial analysis. Esri is the only<br />
vendor that provides complete<br />
technical solutions for desktop, mobile,<br />
server, and Internet platforms.<br />
Visit us at esri.com/news.
IntraLogic Solutions to announce first ever National<br />
Common Operating Picture (COP) platform for first<br />
responders allowing immediate 9-1-1 notification<br />
As recently reported by <strong>Government</strong><br />
<strong>Security</strong> <strong>News</strong>, Intralogic Solutions,<br />
Inc. a leading global school security,<br />
and government developer and integrator,<br />
and Rave Mobile Safety, a<br />
respected creator of innovative public<br />
safety and communication software<br />
have announced a partnership<br />
to develop an integrated service offering<br />
that will benefit both schools<br />
and first responders during crisis<br />
situations, including ones involving<br />
active shooters.<br />
According to the partners, the new<br />
solution combines Rave’s Panic Button<br />
application and 9-1-1 data delivery<br />
capabilities with robust video<br />
surveillance, interactive rich digital<br />
floor plans, One Button Lockdown<br />
and access control technology. The<br />
combined solution will allow<br />
first responders full access<br />
to critical information<br />
about a situation from any<br />
location, including while<br />
en route via a secure, mobile<br />
broadband connection.<br />
In an <strong>August</strong> 10 interview<br />
with Intralogic CEO Lee<br />
Mandel, GSN learned that the integrated<br />
technologies offer a unique<br />
Lee Mandel,<br />
Intralogic CEO<br />
technological breakthrough experience<br />
that no other company is presently<br />
offering. Rather than the traditional<br />
9-1-1 process to call police,<br />
the new, integrated technology<br />
can send critical information<br />
within milliseconds<br />
to a 9-1-1 call center.<br />
“When someone hits the<br />
panic button in a school,<br />
the 9-1-1 center is immediately<br />
activated giving<br />
operators full command<br />
and control to help find the shooter<br />
while the first responders are still in<br />
5<br />
View the video<br />
transit. They can then remotely open<br />
the doors and guide the responders<br />
to exactly where the shooter is,” said<br />
Mandel. “No one else on a national<br />
level is offering this comprehensive<br />
solution. Additionally the panic button<br />
can initiate a lockdown which<br />
will, locks all the doors automatically,<br />
flash strobe lights, send text<br />
messages to parents, teachers, and<br />
students, and take over all computer<br />
screens while playing a pre-recorded<br />
message over the P.A. system.”<br />
Mandel indicated that the technology<br />
is a first of its kind agnos-
tic platform that allows integration<br />
from any manufacturer. IntraLogic<br />
considers this an advanced PSIM<br />
solutions.<br />
Mandel and his company have<br />
been getting a lot of attention from<br />
major companies in the field who<br />
understand that clients have never<br />
been able to customize in this manner,<br />
“with one common operating<br />
picture.”<br />
Founded by Mandel in 2004, IntraLogic<br />
focused mainly on software<br />
development in its early years,<br />
working for a lot of businesses on<br />
Long Island, NY and other nearby<br />
states. The turning point, said Mandel,<br />
was when the company got on<br />
its first government contract which<br />
enables any government agency to<br />
purchase products from pre-bid,<br />
published lists. Currently, the company<br />
serves over 160 School Districts<br />
nationally including 49 of<br />
the 57 districts in Nassau County,<br />
30 in Suffolk County and over 80<br />
throughout Upstate New York, New<br />
Jersey, Connecticut, Florida, and<br />
across the United States.<br />
IntraLogic’s overall list of clients<br />
include schools, townships, municipalities,<br />
as well as a contract with the<br />
MTA Long Island Railroad, which<br />
buys its Cameras, Fire Alarms, Burglar<br />
Alarms and Command Centers.<br />
On the private side, the company<br />
works with some very well<br />
known National Retail chains with<br />
hundreds of locations throughout<br />
the U.S. and overseas.<br />
As impressive as these entrepreneurial<br />
accomplishments may<br />
seem, Mandel made it clear to GSN<br />
that another major breakthrough is<br />
going to be announced in early September,<br />
although he is not at liberty<br />
to announce who this major client is<br />
– except to assure us that the pending<br />
client is a very significant organization.<br />
“We’ve been working with our clients<br />
as an integrator, manufacturer,<br />
and software developer. Our goal is<br />
to offer a one stop shop for our clients<br />
and partners.”<br />
“With our new Common Operating<br />
Picture we can now take all<br />
school districts, malls, schools, hospitals,<br />
municipalities, villages and<br />
other critical assets and tie them to<br />
a centralized platform. We can go<br />
to any government agency around<br />
the world and create this without<br />
replacing their existing technology.<br />
It’s the first of its kind agnostic<br />
platform that allows us to integrate<br />
technology from any manufacturer.”<br />
Along with many readers, GSN is<br />
eager to learn more about this exciting<br />
new platform, and how it will<br />
enhance technology and security<br />
around the globe!<br />
6
Senators Grassley, Leahy press federal investigators on<br />
breach of Democratic National Committee<br />
VIA ELECTRONIC TRANSMISSION<br />
The Honorable Loretta Lynch<br />
Attorney General<br />
U.S. Department of Justice<br />
950 Pennsylvania Avenue, NW<br />
Washington, DC 20530<br />
The Honorable James B. Comey, Jr.<br />
Director<br />
Federal Bureau of Investigation<br />
935 Pennsylvania Avenue, NW<br />
Washington, DC 20535<br />
Dear Attorney General Lynch and<br />
Director Comey:<br />
We are writing in regard to the recent<br />
cyberattacks on American political<br />
organizations. Yesterday the<br />
FBI confirmed that it is investigating<br />
the recent hack of the Democratic<br />
National Committee (DNC). We are<br />
writing to request more specific information<br />
about the efforts that the<br />
National Cyber Investigative Joint<br />
Task Force (NCIJTF) and other elements<br />
of the FBI and Justice Department<br />
are undertaking in order<br />
to counter these types of attacks and<br />
bring the perpetrators to justice.<br />
On June 14, 2016, the Washington<br />
Post reported that Russian government<br />
hackers had successfully penetrated<br />
the computer network of the<br />
Democratic National Committee,<br />
gaining access to DNC databases<br />
and email. [1] According to the article,<br />
DNC officials noticed unusual<br />
network activity and hired Crowd-<br />
Strike, a cybersecurity firm, to investigate.<br />
The firm identified two<br />
separate groups of hackers who had<br />
penetrated the DNC network, both<br />
of which it determined were working<br />
for the Russian government. Immediately<br />
after the Washington Post<br />
report, a purported hacker calling<br />
himself “Guccifer 2.0” claimed responsibility<br />
for the hack, and further<br />
claimed to be a lone Romanian<br />
hacker. [2] The Russian government<br />
also denied its involvement. [3] However,<br />
evidence appears to undermine<br />
the Romanian hacker’s claim of responsibility<br />
and instead suggests<br />
the Russian government’s involvement.<br />
[4] The hackers subsequently<br />
publicly released what appears to be<br />
the DNC’s opposition research on<br />
Donald Trump in June. [5] Last week,<br />
WikiLeaks released roughly 20,000<br />
of the hacked DNC emails that the<br />
hackers had provided to it. [6]<br />
It is not unusual for a nation’s intelligence<br />
services to obtain sensitive<br />
information from other nations’<br />
political entities. Not only<br />
has James Clapper, the Director of<br />
7<br />
Senator Grassley<br />
Senator Leahy<br />
National Intelligence, stated that the<br />
government has indications of cyberattacks<br />
on the 2016 presidential<br />
campaigns, the government has also<br />
reported that foreign hackers targeted<br />
the networks of the Romney<br />
and Obama campaigns in 2012, and<br />
that Chinese hackers compromised<br />
the networks of the Obama and Mc-<br />
Cain campaigns in 2008. [7]<br />
However, when a foreign intelligence<br />
service not only spies on<br />
American political organizations,<br />
which is bad enough, but then selectively<br />
publishes the obtained<br />
information in what appear to be<br />
attempts to affect our democratic<br />
process, it is substantially more troubling.<br />
The integrity of the democratic<br />
process is essential to the social<br />
contract on which our republic is<br />
formed. If foreign intelligence agencies<br />
are attempting to undermine
that process, the U.S. government<br />
should treat such efforts even more<br />
seriously than standard espionage.<br />
These types of cyberattacks are significant<br />
and pernicious crimes. Our<br />
government must do all that it can<br />
to stop such attacks and to seek justice<br />
for the attacks that have already<br />
occurred.<br />
We were pleased to see that the<br />
FBI has stated that it is investigating<br />
this situation. We are writing to<br />
request more information on this<br />
cyberattack in particular and more<br />
information in general on how the<br />
Justice Department, FBI, and NCI-<br />
JTF attempt to prevent and punish<br />
these types of cyberattacks. Accordingly,<br />
please respond to the following<br />
by <strong>August</strong> 9, 2016:<br />
1. When did the Department of Justice,<br />
FBI, and NCIJTF first learn<br />
of the DNC hack? Was the government<br />
aware of the intrusion<br />
prior to the media reporting it?<br />
2. Has the FBI deployed its Cyber<br />
Action Team to determine who<br />
hacked the DNC?<br />
3. Has the FBI determined whether<br />
the Russian government, or any<br />
other foreign government, was<br />
involved in the hack?<br />
4. In general, what actions, if any, do<br />
the Justice Department, FBI, and<br />
NCIJTF take to prevent cyberattacks<br />
on non-governmental political<br />
organizations in the U.S.,<br />
such as campaigns and political<br />
parties? Does the government<br />
consult or otherwise communicate<br />
with the organizations to<br />
inform them of potential threats,<br />
relay best practices, or inform<br />
them of detected cyber intrusions?<br />
5. Does the Justice Department believe<br />
that existing statutes provide<br />
an adequate basis for addressing<br />
hacking crimes of this nature, in<br />
which foreign governments hack<br />
seemingly in order to affect our<br />
electoral processes?<br />
In addition to the questions listed<br />
above, we also request that the Justice<br />
Department, FBI, and/or NCI-<br />
JTF arrange a briefing on these issues<br />
for Committee staff by <strong>August</strong><br />
16, 2016. If possible, we also request<br />
that the briefing include a staff tour<br />
of NCIJTF’s facilities. Thank you<br />
for your attention to this important<br />
matter. If you have any questions,<br />
please contact Patrick Davis of the<br />
Committee Staff at (202) 224-5225<br />
or [redacted].<br />
Sincerely,<br />
Charles E. Grassley<br />
Chairman<br />
Senate Committee on the Judiciary<br />
Patrick Leahy<br />
Ranking Member<br />
Senate Committee on the Judiciary<br />
8<br />
cc: The Honorable Donald Freese<br />
Director National Cyber<br />
Investigative Joint Task Force<br />
cc: The Honorable John P. Carlin<br />
Assistant Attorney General<br />
National <strong>Security</strong> Division<br />
Department of Justice<br />
cc: The Honorable James C. Trainor, Jr.<br />
Assistant Director<br />
Cyber Division<br />
Federal Bureau of Investigation<br />
[1] Ellen Nakashima, Russian <strong>Government</strong> Hackers<br />
Penetrated DNC, Stole Opposition Research On<br />
Trump,The Washington Post, June 14, 2016.<br />
[2] Lorenzo Franceschi-Bicchierai, ‘Guccifer 2.0’ Is<br />
Likely A Russian <strong>Government</strong> Attempt To Cover Up<br />
Their Own Hack, Motherboard, June 16, 2016.<br />
[3] Andrew Roth, Russia Denies DNC Hack And Says<br />
Maybe Someone ‘Forgot The Password,’ The Washington<br />
Post, June 15, 2016.<br />
[4] E.g., Dmitri Alperovitch, Bears In The Midst:<br />
Intrusion Into The Democratic National Committee,<br />
CrowdStrike, June 15, 2016; Lorenzo Franceshi-<br />
Bicchierai, We Spoke to DNC Hacker ‘Guccifer 2.0,’<br />
Motherboard, June 21, 2016; Eli Lake, Cybersecurity<br />
Experts Say Russia Hacked The Democrats, Bloomberg,<br />
July 25, 2016; Thomas Rid, All Signs Point To<br />
Russia Being Behind The DNC Hack, Motherboard,<br />
July 25, 2016; Evan Perez, Russians Suspected Of<br />
Hacking Democratic National Committee Emails,<br />
CNN, July 25, 2016.<br />
[5] Caitlin Yilek, Stolen DNC Files On Trump Leaked,<br />
The Hill, June 15, 2016.<br />
[6] Andrea Peterson, Wikileaks Post Nearly 20,000<br />
Hacked DNC Emails Online, The Washington Post,<br />
July 22, 2016.<br />
[7] Ellen Nakashima, National Intelligence Director:<br />
Hackers Have Targeted 2016 Presidential Campaigns,<br />
The Washington Post, May 18, 2016.
Cypherpath, Quali partnership provides portable<br />
containerized infrastructures that support virtual<br />
sandboxes and cyber ranges<br />
SANTA CLARA, CA, Aug. 23, 2016<br />
– Quali, the leading Cloud Sandbox<br />
software platform for DevOps<br />
automation, and Cypherpath, the<br />
leader in on-demand containerized<br />
infrastructure solutions, today<br />
announced the integration of<br />
the Cypherpath Virtual Container<br />
Platform (VCP) with the Quali<br />
CloudShell solution. Through this<br />
partnership, joint customers are<br />
using on-demand containerized<br />
infrastructures to create and manage<br />
cyber ranges and private cloud<br />
sandboxes. Through full infrastructure<br />
and IT environment virtualization,<br />
customers are saving millions<br />
of dollars in costs associated with<br />
creating, delivering and managing<br />
the full stack of physical compute,<br />
network and storage resources in<br />
highly secure containers.<br />
A cyber range, or cloud sandbox,<br />
gives enterprises the ability to rapidly<br />
reconfigure IT environments<br />
for use by individuals and teams<br />
to conduct offensive and defensive<br />
cyber-mission rehearsal training,<br />
tool-specific training, software<br />
evaluation, and configuration testing.<br />
Most organizations lack the<br />
budget and manpower resources<br />
required to deploy large scale, nonproduction<br />
cyber environments<br />
using existing enterprise tools and<br />
many solutions available to them<br />
do not include the ability to rapidly<br />
change, add, modify and control the<br />
environments.<br />
By leveraging the partnership,<br />
value added reseller (VAR) TSI was<br />
able to provide ManTech International<br />
Corporation the technology<br />
needed to give DISA a fully virtualized<br />
lab infrastructure, complete<br />
with integrated virtual sandboxing<br />
and cyber range capabilities. With<br />
this full stack, DISA is able to use<br />
the lab to develop, test and run infrastructure<br />
in private clouds or<br />
bare-metal servers without requiring<br />
the agency to adopt proprietary<br />
tools, saving both time and money.<br />
10<br />
“DISA is responsible for supporting<br />
a critical element of our national<br />
defense strategy, which is the sharing<br />
of information between joint<br />
warfighters, national leaders, and<br />
other mission and coalition partners,”<br />
said Ernest McCaleb, Man-<br />
Tech technical director and DISA<br />
Cyber <strong>Security</strong> Range chief architect.<br />
“This fast, simple and cost effective<br />
solution provides us with the<br />
ability to fulfill our mission without<br />
sacrificing performance or security,<br />
and deliver the Multiprotocol Label<br />
Switching stack at a fraction of the<br />
cost.”<br />
Through this partnership, joint<br />
customers can:<br />
• Use on-demand infrastructure<br />
to support private cloud sandboxes<br />
in mission ready cyber ranges<br />
• Define, deploy and manage fully<br />
containerized IT infrastructure ondemand<br />
while providing the agility<br />
to share and collaborate between<br />
nodes, networks, bare-metal servers<br />
and private clouds<br />
• Significantly reduce investment<br />
in new physical data center resources<br />
and technologies by virtualizing<br />
More on page 42
New generation.<br />
New possibilities.<br />
Secure your site with the new F3 Series Fence<br />
Controllers, the latest in perimeter protection.<br />
Find out more at security.gallagher.com/latest-releases<br />
security.gallagher.com<br />
security.gallagher.com
Winners’ Portraits: GSN 2016 Airport, Seaport, Border <strong>Security</strong> Awa<br />
Telos Corporation:<br />
2016 Winner, Best Biometric<br />
Identification/Authentication Solution<br />
By Chuck Brooks, 2016 Lead Judge<br />
It was an honor to judge the recent<br />
GSN 2016 Airport, Seaport, Border<br />
<strong>Security</strong> Awards Program and<br />
review a wide array of exceptional<br />
security technology submissions.<br />
I’m very pleased to be discussing<br />
the Telos winning entry with Renate<br />
Neely, Marketing Director of Telos<br />
Corporation, and Dawn E. Lucini,<br />
Director of Aviation <strong>Security</strong>, Telos<br />
Identity Management Solutions.<br />
I have been aware of the important<br />
work of Telos Corporation dating<br />
back to the years when I covered<br />
national security issues working<br />
for the late Senator Arlen Specter<br />
on The Hill. As the digital world<br />
has involved operationally over the<br />
past decade, so has the vulnerability<br />
of maintaining security for people,<br />
systems and information.<br />
Brooks: In the defense, homeland,<br />
and intel communities Telos is<br />
highly regarded for the generic category<br />
of “secure communications”<br />
and we know that your solution is<br />
advanced, efficient and certainly<br />
has the confidence of some of the<br />
most important government agencies<br />
in the security arena. Can you<br />
elaborate on your background in<br />
government and some of the communications<br />
areas, including mobility,<br />
where Telos has contributed<br />
solutions?<br />
Renate Neely: Thank you, Chuck,<br />
for your kind words about Telos<br />
Corporation. We do indeed have a<br />
long history of supporting federal<br />
government clients with solutions<br />
for secure communications, as well<br />
as cyber security, secure mobility,<br />
and identity management. But if I<br />
may, I’d like to focus our remarks<br />
today not on Telos Corporation,<br />
but on Telos Identity Management<br />
Solutions LLC (Telos ID). It is this<br />
subsidiary rather than the parent<br />
Telos Corporation that is the star<br />
of the GSN 2016 Airport, Seaport,<br />
Border <strong>Security</strong> award for the Best<br />
Biometric Identification or Authentication<br />
Solution.<br />
Telos ID’s original claim to fame<br />
12<br />
Renate Neely,<br />
Marketing Director<br />
Dawn E. Lucini,<br />
Director of<br />
Aviation <strong>Security</strong><br />
is its long history of supporting the<br />
Defense Manpower Data Center’s<br />
(DMDC) Common Access Card<br />
(CAC) program to provide DoD<br />
personnel with identity-based access<br />
to secure resources, including<br />
communications systems, as well as<br />
physical access to secure areas. This<br />
has been the springboard for innovative<br />
developments in the areas<br />
of identity vetting and continuous<br />
threat assessment.<br />
Brooks: We are living in an era of<br />
large and widespread information<br />
security breaches. Everyone is vulnerable<br />
and networks, including<br />
those of government agencies (i.e.<br />
OPM) are immune to cyber-attacks.<br />
Risk management has become an<br />
operational requirement for executive<br />
management. What does Telos<br />
do in the area of risk assessments
ds Program<br />
for networks both in the federal and<br />
commercial spaces?<br />
Renate Neely: Telos Corporation<br />
protects government and commercial<br />
enterprises with solutions and<br />
services for the full cyber security<br />
lifecycle. Our offerings include independent<br />
counsel for information<br />
security requirements, cyber security<br />
consulting services, and enterprise<br />
solutions for IT risk management<br />
and continuous compliance.<br />
But again, let’s focus on Telos ID,<br />
which addresses the operational<br />
requirements of risk management<br />
as well, focusing primarily on the<br />
insider threat. An example is the<br />
company’s IDVetting service, which<br />
provides governments, schools,<br />
medical professionals, and commercial<br />
organizations with a complete<br />
fingerprint background checking<br />
solution. These customers use<br />
IDVetting services to submit biographic<br />
and biometric information<br />
from employees, candidates, and<br />
contractors to the FBI for criminal<br />
history records checks, helping to<br />
secure their business environment,<br />
reduce risk and cost, and comply<br />
with federal, state, and local laws regarding<br />
required checks for specific<br />
industries and roles.<br />
Brooks: The recent terrorist attacks<br />
against airport targets demonstrate<br />
the need for enhanced security measures,<br />
including screening of airport<br />
staff, and background checks and<br />
badging operations. The trend is for<br />
better authentication and biometric<br />
layering to mitigate threats. Can you<br />
take this opportunity to highlight<br />
the current application and futures<br />
uses of Telos ID for transportation<br />
security?<br />
Can you provide more detail about<br />
your award winning Telos ID Designated<br />
Aviation Channeling service<br />
(DAC)? What are the engineering<br />
and performance differentiators for<br />
the aviation industry? Can you also<br />
list Telos ID current applications<br />
and some of your key customers as<br />
well as future offerings?<br />
Dawn Lucini: Airports, airlines, and<br />
related services are required to vet<br />
the security backgrounds of job applicants<br />
and employees who have<br />
access to secure areas. Telos ID is<br />
one of only three organizations authorized<br />
by the TSA to be a designated<br />
aviation channeler (DAC),<br />
meaning it is certified to collect and<br />
send fingerprints and enrollment information<br />
to TSA for security threat<br />
assessments and criminal history<br />
record checks. Telos ID’s DAC service<br />
was the first of these third party<br />
channeling services to be approved<br />
13<br />
for operation by the TSA, and has<br />
continued to win the vast majority<br />
of DAC business since its inception.<br />
Telos ID DAC is a modular, Webbased<br />
offering that lets airports and<br />
air carriers select which services<br />
they need. The solution can be customized<br />
to specific business processes<br />
and provide custom reporting<br />
and information exports. The<br />
Telos ID DAC platform can integrate<br />
with other workforce systems<br />
to meet additional badging, physical<br />
security and personnel administrative<br />
needs. Telos ID tailors the secure<br />
Web portal, allowing security<br />
and badging offices to perform multiple<br />
functions on one platform.<br />
Telos ID DAC is deployed at more<br />
than 50 airports and airlines across<br />
the U.S. – including BWI Thurgood<br />
Marshall and DFW Dallas/Fort<br />
Worth. Here is the full list of current<br />
clients: https://www.telos.com/<br />
identity-management/aviationchanneling/customers/<br />
Vetting the backgrounds of airport<br />
and related personnel is essential to<br />
understanding and mitigating the<br />
risk of bad actors gaining access to<br />
secure areas. But doing this vetting<br />
on a periodic basis may allow something<br />
to slip through the cracks, a<br />
piece of information that just might<br />
help avoid disaster. To that end, the<br />
More on page 42
Cellebrite introduces UFED Touch2 platform<br />
for standalone mobile forensic solutions<br />
PETAH TIKVA, ISRAEL, July 19,<br />
2016 – Cellebrite, a leader in digital<br />
forensic extraction, decoding and<br />
analysis solutions, today unveiled<br />
UFED Touch2, the latest addition<br />
to the company’s industry-leading<br />
UFED Series family of mobile forensic<br />
solutions. With enhanced speed,<br />
usability, and portability, UFED<br />
Touch2 is a comprehensive mobile<br />
forensic solution that allows law enforcement,<br />
military, and intelligence<br />
agencies to extract evidentiary data<br />
in a forensically sound manner. The<br />
Touch2 can extract mobile device<br />
content up to three times faster than<br />
the UFED Touch, enabling investigators<br />
and examiners to accelerate<br />
investigations.<br />
“Many of our customers prefer a<br />
purpose-built device for extracting<br />
and viewing digital evidence regardless<br />
of location,” said Yossi Carmil,<br />
Global Co-CEO, Cellebrite. “The<br />
UFED Touch2 delivers the performance,<br />
reliability and usability required<br />
to allow customers to meet<br />
their mission in the lab or field,<br />
while simplifying the procurement<br />
process by eliminating the need to<br />
buy separate hardware.”<br />
With its intuitive GUI and easyto-use<br />
touch screen, UFED Touch2<br />
enables physical, file system and<br />
logical extractions of data and passwords,<br />
including deleted data, from<br />
the widest range of mobile devices.<br />
UFED Touch2 is available in both<br />
standard and ruggedized editions,<br />
running Logical or Ultimate (logical,<br />
file system and physical extraction)<br />
configurations and comes with<br />
a suite of supporting software applications,<br />
peripherals and accessories.<br />
UFED Touch2 delivers a range<br />
of enhanced capabilities designed<br />
to increase performance, usability,<br />
and portability. Key performance<br />
enhancements designed to reduce<br />
14<br />
extraction time include:<br />
• 5x faster CPU than the UFED<br />
Touch<br />
• DDR3 memory<br />
• Large and fast hard drive<br />
(SSD 128GB)<br />
• USB 3.1 phase 1 axillaries<br />
(Up to 5Mbps)<br />
In addition, the UFED Touch2 includes<br />
a number of features that<br />
simplify usage and increase flexibility:<br />
• High-resolution (1024),<br />
capacitive multi-touch display<br />
with intuitive GUI<br />
• Built-in multi-SIM Reader<br />
• Mini Display Port<br />
• Customized Windows 10<br />
Finally, the Touch2 delivers new capabilities<br />
to allow for improved portability:<br />
• WiFi b\g\n\ac (up to 350 Mbps)<br />
• All-inclusive field-ready<br />
operational kit – smaller, lighter<br />
connector tips, and external<br />
hard drive<br />
• Long-lasting battery<br />
Cellebrite will continue to support<br />
its customers using UFED Touch.<br />
Any future announcement regarding<br />
the end of support for the Touch<br />
platform will be made 18 months in
advance to allow users to effectively<br />
plan for the transition. Customers<br />
that purchased a UFED Touch in<br />
2016 will receive attractive offers to<br />
trade in their device for a Touch2.<br />
Customers that purchased a UFED<br />
Touch after June 15, 2016 will be<br />
able to trade in their device for a<br />
UFED Touch2 at no cost.<br />
About Cellebrite<br />
Every day around the world digital<br />
data is impacting investigations.<br />
Making it intelligent and actionable<br />
is what Cellebrite does best. A pioneer<br />
of mobile data forensics since<br />
1999 with a passion for technology<br />
innovation, Cellebrite is uniquely<br />
positioned to address the rapidly<br />
evolving needs of its diverse customer<br />
base to access, unify and defend<br />
digital evidence of all kinds.<br />
Together, our powerful UFED solutions<br />
deliver the only complete, endto-end<br />
<strong>Digital</strong> Forensics Platform<br />
on the market. Our track record<br />
remains unchallenged. Our results?<br />
Proven and well documented. With<br />
more than 40,000 UFED licenses<br />
deployed globally in 100 countries,<br />
we allow law enforcement, intelligence<br />
services, border patrols, special<br />
forces, military and the private<br />
sector to achieve their missions<br />
quickly and effectively.<br />
Cellebrite is a wholly-owned subsidiary<br />
of the Sun Corporation, a<br />
listed Japanese company (6736/JQ)<br />
Controp’s airborne EO/IR<br />
Surveillance Camera payload<br />
protects Rio Olympic games<br />
15<br />
HOD HASHARON, ISRAEL, 17<br />
<strong>August</strong> 2016 – CONTROP Precision<br />
Technologies Ltd. – a company<br />
specializing in the field of electrooptics<br />
(EO) and<br />
infrared (IR)<br />
cameras for defense<br />
and homeland<br />
security solutions<br />
– is proud<br />
to announce the<br />
use of CON-<br />
TROP’s SHAPO<br />
Airborne<br />
EO/IR surveillance<br />
payload for<br />
the protection<br />
of 2016 Summer<br />
Olympics in Rio<br />
de Janeiro, Brazil.<br />
The SHAPO<br />
is installed on<br />
board the ADB-<br />
150 Aerostat that supports the Brazilian<br />
Air Force security mission<br />
and is deployed above the Olympics<br />
area.<br />
The ADB-150 aerostat carrying<br />
CONTROP’s SHAPO EO/IR surveillance<br />
payload was launched <strong>August</strong><br />
9th, 2016, by Airship do Brasil,<br />
a company of Bertolini’s Holdings,<br />
in cooperation with the Brazilian<br />
Air Force, in order to provide 24/7<br />
surveillance,<br />
monitoring and<br />
public security<br />
of the Olympics<br />
area.<br />
Prior to the<br />
start of the Rio<br />
Olympics 2016,<br />
the system was<br />
deployed as part<br />
of a surveillance<br />
operation with<br />
Air Force University<br />
(UNIFA)<br />
security systems<br />
at Afonsos Air<br />
Force Base in Rio<br />
de Janeiro for the<br />
protection of the<br />
training center for athletes competing<br />
in the current Olympics events.<br />
The CONTROP SHAPO is a gyrostabilized<br />
3-gimbal camera payload,<br />
which was designed for surveillance<br />
and observation on a variety of airborne<br />
platforms including aerostats,
helicopters, fixed wing aircraft and<br />
unmanned air vehicles. The compact<br />
SHAPO camera payload includes<br />
a high sensitivity color Day<br />
Camera and a Thermal Imaging<br />
Camera with a Continuous Optical<br />
Zoom Lens.<br />
The SHAPO<br />
can also include<br />
an optional<br />
Laser<br />
Range Finder<br />
and/or<br />
Laser Pointer<br />
as well as<br />
an optional<br />
Mission<br />
Management<br />
Moving<br />
Map<br />
System.<br />
M a r i t i m e<br />
and Land versions<br />
of the SHA-<br />
PO, for installation<br />
on patrol boats, vessels<br />
and observation vehicles, are available<br />
as well.<br />
The SHAPO is used worldwide<br />
for a variety of long-range surveillance<br />
and observation applications<br />
including Law Enforcement, Search<br />
& Rescue, Homeland <strong>Security</strong> and<br />
Defense. CONTROP’s airborne<br />
payloads are installed on a variety<br />
of airships and aerostats worldwide,<br />
in order to provide public security<br />
and safety.<br />
About CONTROP<br />
Precision Technologies Ltd.<br />
CONTROP specializes in the development<br />
and production of Electro-Optical<br />
and Precision Motion<br />
Control Systems.<br />
The company’s<br />
specialists have<br />
over 35 years of<br />
experience in<br />
EO / IR products<br />
for Surveillance,<br />
Defense and<br />
Homeland <strong>Security</strong>.<br />
CONTROP’s<br />
main product<br />
lines include: Automatic<br />
passive<br />
Intruder Detection<br />
Systems for<br />
airport perimeter<br />
surveillance, coastal<br />
surveillance, port and<br />
harbor security, border<br />
surveillance, the security of sensitive<br />
sites and ground troop security;<br />
High performance Stabilized<br />
Observation Payloads used for day<br />
and night surveillance on board<br />
UAVs, small UAVs and aerostats/<br />
balloons, helicopters, light aircraft,<br />
maritime patrol boats and ground<br />
vehicles; Thermal Imaging Cameras<br />
with high performance continuous<br />
Zoom Lens and state-of-the-art<br />
image enhancement features, and<br />
more. CONTROP’s products are in<br />
16<br />
daily operational use in many of the<br />
most critical surveillance, homeland<br />
security and defense programs<br />
worldwide.<br />
For more information on CONTROP,<br />
please visit the company’s website:<br />
www.controp.com<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly <strong>Digital</strong> <strong>Edition</strong><br />
Airport/Seaport <strong>News</strong>letter<br />
Daily Insider <strong>News</strong>letter<br />
GSN Media Kit<br />
CLICK HERE
GSN’s 2016 Homeland <strong>Security</strong> Awards Program<br />
Now Accepting Entries at:<br />
www.gsnmagazine.com/hsa2016/welcome<br />
The 2016 <strong>Government</strong> <strong>Security</strong> <strong>News</strong> Awards Program, featuring<br />
many new categories in Cybersecurity, Physical <strong>Security</strong>, <strong>Government</strong><br />
Agency Innovations and Mobile Technologies will open for entries on<br />
<strong>August</strong> 24 and will close for entries on November 15.<br />
In good news for Winners and Finalists, GSN will be reinstating its<br />
annual Homeland <strong>Security</strong> Awards Dinner in Washington, DC in<br />
the first week of December, in a venue to be announced. Longtime<br />
participants in the GSN awards programs will recall that previous<br />
GSN Awards Dinners have featured top government, military leaders<br />
and respected television commentators such as 4-Star General<br />
Barry McCaffrey (Ret); Fran Townsend, Homeland <strong>Security</strong> Advisor to<br />
George W. Bush, James Kallstrom, Assistant Director of the FBI and<br />
Admiral Thad Allen (Ret), Commandant of the U.S. Coast Guard<br />
who came out of retirement twice to serve his county, first in<br />
Hurricane Katrina and later in the BP Oil Spill.<br />
The cost of an entry for vendors is $300 per entry, but there is no<br />
charge for government agencies or departments. All Winners<br />
and Finalists receive Awards Emblems, and all Winners receive a<br />
handsome, gold-trimmed plaque describing their winning entries.<br />
All Winners and Finalists will also be invited to participate in the 2016<br />
<strong>Digital</strong> Yearbook of Awards Winners.<br />
To see photo gallery of previous Awards Dinners:<br />
https://www.flickr.com/photos/44536438@N06/<br />
For information on the Awards Dinner or Sponsorships,<br />
Contact Adrian Courtenay, Managing Partner, at<br />
acourtenay@gsnmagazine.com, (Mobile) 917-696-5782
ECN acquires MIR3, extends SaaS-based<br />
unified critical communications platform to<br />
enterprise clients<br />
ORMOND BEACH, FL, Aug. 1,<br />
2016 /PR<strong>News</strong>wire/ – Emergency<br />
Communications Network (ECN)<br />
has acquired MIR3, a global Software<br />
as a Service (SaaS) provider of<br />
intelligent communications to business<br />
and government clients. The<br />
combination of ECN’s critical communications<br />
platform and MIR3’s<br />
growing enterprise platform brings<br />
together two highly complementary<br />
companies, creating an organization<br />
uniquely qualified to meet the<br />
fast growing demand for software<br />
communications solutions. Financial<br />
terms of the transaction were<br />
not disclosed.<br />
MIR3 provides its clients with<br />
advanced, reliable, and flexible<br />
software solutions that facilitate<br />
multi-channel communication and<br />
collaboration at scale, with use cases<br />
designed to address the growing<br />
complexity of the messaging landscape<br />
and ever increasing challenges<br />
faced by enterprises today. Clients<br />
depend on MIR3’s software for daily<br />
business operations, including crisis<br />
management, IT service management,<br />
corporate communications,<br />
customer relations, supply chain<br />
management, and event management.<br />
MIR3’s clients include leading<br />
organizations in the government, financial<br />
services, technology, healthcare,<br />
energy, and consumer product<br />
segments.<br />
“The acquisition of MIR3 accelerates<br />
ECN’s vision to be a leader<br />
in the unified critical communications<br />
space serving a broad range of<br />
clients and applications.<br />
This transaction creates<br />
an opportunity for ECN<br />
to greatly scale our footprint<br />
in the adjacent enterprise<br />
market, as well<br />
as introduce ECN’s Cloud<br />
Platform as a Service<br />
(CPaaS) offering, which<br />
can enable enterprises to<br />
enrich software applications<br />
with multi-channel and realtime<br />
communication functions. We<br />
are excited to welcome MIR3’s clients<br />
and partners to the ECN family,<br />
and we look forward to continuing<br />
to enhance the MIR3 products,”<br />
said David DiGiacomo, President<br />
and CEO of ECN.<br />
18<br />
David DiGiacomo,<br />
President and CEO<br />
As a result of this transaction,<br />
Amir Moussavian is stepping down<br />
from his positions as CEO and<br />
Chairman in order to pursue new<br />
opportunities. “I am thrilled to have<br />
played a role in the success of MIR3,<br />
and could not be more proud of my<br />
colleagues, as their hard work has<br />
allowed us to maintain the position<br />
as a leader in the industry. With the<br />
additional resources of ECN, MIR3<br />
will continue to provide<br />
the exceptional level of<br />
service its Intelligent Notification<br />
and TelAlert<br />
clients have grown to expect,”<br />
said Mr. Moussavian.<br />
Ann Pickren, President<br />
of MIR3 said, “Joining<br />
forces with ECN establishes<br />
an industry leader<br />
in the unified critical communications<br />
market, paving the way for<br />
continued innovation and development<br />
to address critical business<br />
needs. We are excited for this opportunity<br />
and will continue to provide<br />
our clients with unparalleled<br />
service.”
ECN is a portfolio company of<br />
Veritas Capital, a private equity<br />
firm active in the communications<br />
space. Veritas Capital is committed<br />
to supporting ECN in building a fast<br />
growing, global leader in intelligent<br />
communications and CPaaS markets.<br />
About ECN<br />
ECN is a leading national provider<br />
in the SaaS-based unified critical<br />
communications market. ECN<br />
has pioneered high-speed notification<br />
services capable of reaching<br />
millions of people in minutes<br />
through its CodeRED solution<br />
for government clients and has applied<br />
its mission critical capabilities<br />
to commercial, healthcare and<br />
other end markets. The company’s<br />
cloud-based software communications<br />
platform provides seamless<br />
and easy-to-deploy solutions for<br />
the exchange of critical information<br />
among organizations, their people,<br />
devices and external entities with<br />
use cases designed to save lives, enhance<br />
revenue and reduce costs. In<br />
addition, ECN will empower clients<br />
to embed solutions directly into existing<br />
software applications to offer<br />
a richer suite of communications.<br />
ECN is based in Ormond Beach, FL<br />
with additional offices in Minneapolis,<br />
MN. More information can<br />
be found on the company’s website at<br />
www.ecnetwork.com.<br />
About MIR3<br />
MIR3 provides intelligent notification<br />
and response software for business<br />
operations. It offers Intelligent<br />
Notification, a critical notification<br />
solution for business continuity<br />
and disaster recovery, as well as for<br />
various business operations, such<br />
as information technology alerting,<br />
business continuity, or emergency<br />
notification. In addition, it offers<br />
TelAlert, a two-way notification<br />
system that helps users to simplify<br />
the administration of their network<br />
management, help desk, and financial<br />
processing systems by automatically<br />
launching alerts to personnel.<br />
The company deploys its solution in<br />
SaaS, on-premise, and hybrid formats.<br />
MIR3 is based in San Diego,<br />
CA with additional offices in London,<br />
UK, and Dubai, UAE. More information<br />
can be found on the company’s<br />
website at www.mir3.com.<br />
About Veritas Capital<br />
Veritas Capital is a leading private<br />
equity firm that invests in companies<br />
that provide critical products<br />
and services, primarily technology<br />
or technology-enabled solutions,<br />
to government and commercial<br />
clients worldwide including those<br />
operating in aerospace & defense,<br />
healthcare, technology, national security,<br />
communications, energy and<br />
education. Veritas Capital seeks to<br />
create value by strategically transforming<br />
the companies in which it<br />
invests through organic and inorganic<br />
means. For more information<br />
on Veritas Capital and its current<br />
and past investments, visit www.veritascapital.com.<br />
19<br />
SOURCE Emergency Communications Network<br />
(ECN)
Climate Change – This is what it’s going to look like!<br />
A dispatch from Baton Rouge from George Lane,<br />
GSN Columnist<br />
Thu, 2016-08-18 03:00 AM<br />
My son was evacuated Saturday<br />
night by boat in Lafayette, Louisiana.<br />
The National Weather Service<br />
(NWS) said this was a one in 500<br />
years flood; however, there have<br />
been 8 one in 500 year floods in this<br />
year alone, including one in Louisiana<br />
in March. This is what climate<br />
change will look in Louisiana. Here<br />
is why the disastrous flooding occurred;<br />
1.) “Inland Tropical Depression”:<br />
Flooding in Louisiana was fueled<br />
by a system somewhat similar to an<br />
inland tropical depression. Parts of<br />
Louisiana saw more rain than some<br />
U.S. cities have seen in the last few<br />
years combined. Deep, tropical<br />
moisture in combination with low<br />
pressure near the earth’s surface and<br />
aloft were the main ingredients that<br />
fueled the serious flooding in Louisiana.<br />
Simultaneously the Jet stream<br />
dipped into North Louisiana, providing<br />
a blocking force that kept the<br />
tropical storm over South Louisiana.<br />
On Friday morning, NOAA’s<br />
Weather Prediction Center said:<br />
“The best description of this system<br />
is that of an inland sheared tropical<br />
20<br />
depression.”<br />
The rainfall it<br />
produced was<br />
very similar<br />
to what one<br />
would expect<br />
from a<br />
George Lane<br />
slow-moving tropical depression or<br />
storm since rainfall potential is related<br />
to the forward speed of those<br />
types of systems. A weather forecast<br />
discussion from the National<br />
Weather Service in New Orleans<br />
Friday morning said that the moisture<br />
content in the atmosphere was<br />
higher than what has been observed<br />
there during some tropical cyclones.<br />
It was an all-time record for the area.<br />
When that much moisture is<br />
available in the atmosphere, thunderstorms<br />
can produce excessive<br />
rainfall of several inches in a single<br />
hour, leading to astronomical totals<br />
over time. While no one likely forecast<br />
24+ inches of rain in southeast<br />
Louisiana, this is the type of thing<br />
that can happen on a very localized<br />
scale in situations like this one.<br />
2.) River Records Shattered by 4 to<br />
6+ Feet: At least 8 river gauges have<br />
set new record highs in southeast
Louisiana, exceeding the previous<br />
record by several feet in some cases.<br />
The most extreme of those was<br />
in Magnolia, Louisiana, where the<br />
Amite River crested at 58.56 feet.<br />
This topped the old record at that<br />
location by more than six feet set on<br />
April 23, 1977. The Amite River in<br />
Denham Springs hit 4.7 feet above<br />
its previous record set in 1983 on<br />
Sunday morning. Records there<br />
date back to at least 1921, making<br />
this an impressive feat. These areas<br />
were already saturated with rain,<br />
and could not absorb water, allowing<br />
water to accumulate.<br />
3.) More Rain Fell Than Los Angeles<br />
Has Seen in More Than 3 Years:<br />
Since the start of 2012, Los Angeles<br />
has seen a total of 29.18 inches<br />
of rain. In just a few days, Watson,<br />
Louisiana, picked up two inches<br />
more than that amount with 31.39<br />
inches of rain during the event.<br />
4.) Second 24+ Inch Rain Event<br />
in Louisiana This Year: This is the<br />
second time in a matter of months<br />
that Louisiana has seen more than<br />
24 inches of rain from a single event.<br />
Almost 27 inches of rain fell southsoutheast<br />
of Monroe, Louisiana, on<br />
March 8-11, 2016. The official airport<br />
reporting station in Monroe<br />
picked up 20.66 inches of rain. Record<br />
flooding was observed on five<br />
river gauges in parts of the state,<br />
also topping the previous records by<br />
several feet.<br />
The potential for heavy rain and<br />
flooding will continue the next few<br />
days as the tropical moisture expands<br />
northward from the Gulf<br />
Coast and interacts with a stalled<br />
frontal boundary. Additional locally<br />
heavy rain will impact parts<br />
of the Gulf Coast, including southeast<br />
Texas and Louisiana, though<br />
amounts will not be nearly as heavy<br />
as seen the last few days. FYI.<br />
George Lane, a resident of Baton<br />
Rouge, Louisiana, has 25 years of<br />
experience in the development of<br />
chemical security systems, conducting<br />
research as a NASA Fellow at the<br />
Stennis Space Center and as a NASA<br />
Fellow. Lane was air quality SME for<br />
the University of California at Berkeley<br />
Center for Catastrophe Risk Management<br />
during the BP Oil Spill. He<br />
is currently Chemical <strong>Security</strong> SME<br />
for the Naval Post Graduate School<br />
Maritime Interdiction in the Center<br />
for Network Innovation and Experimentation.<br />
21<br />
Sign-up for<br />
Free GSN<br />
<strong>Digital</strong> <strong>Edition</strong>s<br />
and<br />
Email <strong>News</strong>letters<br />
Free subscription to your selection of<br />
GSN digital editions and daily/weekly<br />
email newsletters. Add new selections<br />
or opt-out of any selections at any<br />
time.<br />
Monthly <strong>Digital</strong> <strong>Edition</strong><br />
Airport/Seaport <strong>News</strong>letter<br />
Daily Insider <strong>News</strong>letter<br />
GSN Media Kit<br />
CLICK HERE<br />
The <strong>News</strong> Leader in<br />
Physical, IT and<br />
Homeland <strong>Security</strong><br />
www.gsnmagazine.com
Convy on Net-Centric <strong>Security</strong><br />
Securing the Internet of Things<br />
By John Convy, Convy Associates, Washington, DC<br />
Most people in technology know<br />
that the Internet of Things (IoT) is<br />
the vast network of physical objects<br />
and devices, vehicles, and buildings<br />
that have been embedded with<br />
electronics, software sensors, and<br />
network connectivity. This enables<br />
them to collect, exchange, and share<br />
data with each other and with big,<br />
analytic tools. It’s the<br />
digital offspring of<br />
the Internet, and it is<br />
growing up quickly.<br />
Connectivity is a<br />
fundamental part of<br />
our world, making<br />
our stuff “smarter.”<br />
In fact, its growth has been exponential.<br />
According to Markets and<br />
Marketing, Investments made in<br />
the Internet of Things are expected<br />
to increase from $6.89 billion per<br />
year in 2015 to $28 billion in 2020.<br />
Things we use every day – lighting,<br />
cars, healthcare, parking meters,<br />
and even our home appliances have<br />
become smarter and more connected.<br />
At a recent <strong>Security</strong> Industry Association<br />
Conference, I asked three<br />
prominent thought leaders to address<br />
the emerging questions concerning<br />
the Internet of Things and<br />
its vulnerability to attack.<br />
Chris Cressy, who leads Federal<br />
IoT Solutions at Cisco, emphasized<br />
the expanding value of the IoT. “IoT<br />
is transforming businesses and business<br />
processes, in the public sector.<br />
Integration and interoperability<br />
are fundamental needs that IoT<br />
“Customers should seek out vendors that<br />
are designing network security into their<br />
products, and are based on well-recognized<br />
standards, such as the NIST certification.”<br />
22<br />
can address. Integration increases<br />
operational efficiency. Traditional<br />
approaches to system security are<br />
called air gap – keeping systems isolated<br />
– but that does not work with<br />
IoT. You have to connect systems to<br />
get value. When you connect them,<br />
you do introduce vulnerability, but<br />
you can do continuous real-time<br />
monitoring of those systems.<br />
Cressy also outlined some key<br />
components for IoT system architecture<br />
for security. “At the bottom<br />
layer is basic IT security, essentially<br />
network segmentation with firewalls,<br />
VPNs,<br />
and VLANs.<br />
The second<br />
element is encryption, and lastly, we<br />
implement more advanced capabilities,<br />
such as real-time monitoring<br />
and real-time threat detection. Just<br />
as IoT is a phased implementation,<br />
so is IoT security.”<br />
Jeff Hill, an Enterprise<br />
Solutions<br />
Specialist at Spectra<br />
Logic, provided insight<br />
on another consequence<br />
of so much<br />
connectivity – the<br />
need for secure data<br />
storage. “The IoT is driving massive<br />
video growth because of automation<br />
and monitoring, and that video<br />
requires secured storage. Storage is<br />
becoming a much larger piece of<br />
the overall infrastructure because of<br />
the tools that we are able to leverage<br />
with storage, such as analytics.<br />
We are expecting that by 2019, 3.4<br />
Zeta Bytes of data will be transmitted<br />
over networks in an entire year,<br />
and security is one area where we<br />
are seeing tremendous growth,” he<br />
said.<br />
Hill believes that the best way to
store data is with hybrid clouds,<br />
which offer more flexibility in security<br />
and ownership in a concept he<br />
calls, “genetic diversity.” The other<br />
types of clouds are private clouds in<br />
which you own the hardware and<br />
control the security with a high-security<br />
protocol – and public clouds,<br />
which are extremely efficient for accessing<br />
information, but provide no<br />
benefits of ownership.<br />
“When considering best practices<br />
for IoT data, it’s important to<br />
plan infrastructure with a growth<br />
mindset. Genetic diversity represents<br />
scalable technology and tiered<br />
storage. A great example would be<br />
Facebook, because of the volume of<br />
their data – millions of videos and<br />
photos. They’ve found that it’s important<br />
not just to have it on local<br />
storage that can be accessed quickly,<br />
but they’ve diversified the tiers of<br />
storage and the kinds of storage they<br />
have, to ensure against all types of<br />
threats.”<br />
Hill also explained that enterpriseclass<br />
storage solutions are becoming<br />
increasingly more affordable, which<br />
makes securing data in the government<br />
sector much more cost-effective<br />
than not.<br />
Matt Bretoi, VP of <strong>Security</strong> Sales<br />
at Flir Systems, weighed in on how<br />
the convergence of cyber security,<br />
network security, and physical security<br />
are creating new challenges.<br />
“<strong>Security</strong> manufacturers have a dichotomous<br />
responsibility to protect<br />
the network from the security system<br />
and anything that migrates into<br />
it, and to protect the security system<br />
from the network,” he suggested.<br />
So what can manufacturers do to<br />
help customers protect their assets?<br />
“Customers should seek out vendors<br />
that are designing network security<br />
into their products, and are<br />
based on well-recognized standards,<br />
such as the NIST certification. This<br />
is a cyber security framework that<br />
ensures that any sensitive information<br />
such as user data is encrypted,<br />
and that users are able to identify<br />
third-party components. This reduces<br />
known vulnerabilities. All<br />
communications between the edge<br />
devices, such as cameras or access<br />
control card readers, should include<br />
proper encryption, such as Transport<br />
Layered <strong>Security</strong>. Minimally,<br />
SSL encryption should be used,”<br />
Bretoi said.<br />
Bretoi also explained that combining<br />
this strategy with robust<br />
authentication, such as two-factor<br />
authentication, creates a very powerful<br />
one-two punch. It is notable<br />
that NIST certification covers security<br />
audits for the equipment and<br />
penetration testing. He believes this<br />
is critical, and that collaboration<br />
and communication are essential<br />
when integrating physical and cyber<br />
23<br />
security.<br />
“Implementing these tools should<br />
be part of a system’s coding DNA,<br />
as a manufacturer’s first line of defense.<br />
The second front is deployment.<br />
It’s imperative that integration<br />
technicians – those people actually<br />
installing the system – understand<br />
cybersecurity, and employ best<br />
practices in implementation and<br />
maintenance,” Bretoi added. “End<br />
users should avail themselves of all<br />
training tools provided to them, so<br />
that vulnerabilities can be quickly<br />
identified and mitigated.”<br />
The opinions of these three experts<br />
were eye opening, and validated<br />
that the Internet of Things is fostering<br />
significant changes. It is not<br />
only transforming the way we live<br />
and work, but it is transforming the<br />
way we think about and implement<br />
strong security measures.<br />
John Convy and Convy Associates<br />
provide strategic alliance, A&E consultant,<br />
technology ecosystem, and<br />
lead generation programs to monetize<br />
relationships and accelerate demand<br />
for leading security industry<br />
manufacturers. John is the Founder<br />
and Managing Director of the Open<br />
Standards <strong>Security</strong> Alliance and the<br />
IP <strong>Security</strong> Academy, and a speaker<br />
at many global industry events.<br />
Email: John@ConvyAssociates.com
HID Global provides mid-year update on top<br />
trends for secure identity<br />
<strong>News</strong> Highlights:<br />
• Mobility and a better user experience<br />
continue to be the market’s<br />
top focus areas for the year.<br />
• Adding wearables to the device<br />
ecosystem has elevated awareness<br />
around the use of trusted digital<br />
identities across increasingly connected<br />
environments.<br />
• The need for privacy protection,<br />
improved mobile security, and<br />
trust in all transactions has intensified<br />
with growing interaction<br />
between the identities of things<br />
and people.<br />
AUSTIN, TX, July 14, 2016 – HID<br />
Global®, a worldwide leader in secure<br />
identity solutions, today released a<br />
mid-year update to its top 2016 security<br />
trends, based on customer insights<br />
into key market developments<br />
across enterprise, healthcare, banking<br />
and government markets. In the<br />
first six months of the year, the company<br />
noted continued forward movement<br />
in market adoption of mobile<br />
solutions and interest in the Internet<br />
of Things, as customers place more<br />
value on seamless environments that<br />
require trusted digital identities with<br />
heightened security and privacy protection.<br />
“Customers are increasingly investing<br />
in solutions that give them the<br />
flexibility to incorporate new and<br />
better capabilities that deliver a more<br />
satisfying connected experience for<br />
their users,” said Stefan Widing, HID<br />
Global President and CEO. “As we<br />
move through the middle of the year,<br />
we are experiencing a dramatic increase<br />
in customer demand for mobility,<br />
a better user experience, and<br />
connected environments. We have<br />
also forged new partnerships with<br />
major industry players who have the<br />
same vision to create an extraordinary<br />
user experience and we look forward<br />
to unveiling more about these<br />
partnerships as deployments progress<br />
throughout the year.”<br />
Following are HID Global’s midyear<br />
updates to the trends that the<br />
company forecasted in January:<br />
Trend #1: “Mobilizing” security will<br />
make it more pervasive and personalized:<br />
a new, more secure identity<br />
lifestyle will be built around the convenience<br />
of ever-present mobile devices.<br />
Computer and network logon,<br />
driver licenses and other applications<br />
will more seamlessly join physical<br />
security functions on phones, tablets<br />
24<br />
and laptops. Wearables will be the<br />
next step, and phones will also work<br />
with RFID tags to add security and<br />
trust to the IoT for proof-of-presence<br />
applications.<br />
Mid-year update: Demand for mobile<br />
solutions continues to grow, along with<br />
an increasing focus on security issues.<br />
Multiple studies revealed fears about<br />
mobile security, countered by growing<br />
demand in for the benefits of online<br />
and mobile functionality. The definition<br />
of mobility is also expanding to<br />
encompass the broader idea of “on-thego”<br />
convenience and efficiency, where<br />
smartphones can be used as both a credential<br />
and a general-purpose reader<br />
for new use cases. In a recent deployment<br />
at the CityPoint building in London,<br />
security guards are able use their<br />
smartphones as NFC readers; with a<br />
tap of their phone to RFID tags, guards<br />
can check keys in and out and prove<br />
presence at shift checkpoints.<br />
Trend #2: <strong>Security</strong> will move to a<br />
much greater focus on the user experience:<br />
This will help close the gap<br />
between planning and compliance,<br />
while ensuring that security adapts<br />
to rather than defines end-user habits<br />
and lifestyles. Old ways of authenti-<br />
More on page 26
cating will be replaced by more satisfying<br />
alternatives.<br />
Mid-year update: Customers continue<br />
to want an easier, more trustworthy<br />
way to use digital identities to access<br />
on-the-go services and applications.<br />
Studies repeatedly highlighted the importance<br />
of the user experience -- the<br />
Frost & Sullivan Asia Pacific study<br />
ranked it among the top two most important<br />
drivers for deploying mobile<br />
access control over the next three years.<br />
Biometrics continued to emerge as an<br />
effective solution for bringing<br />
together security and convenience<br />
together -- this approach<br />
is now used at four of<br />
Brazil’s top five financial institutions<br />
to simplify an estimated<br />
two billion trusted ATM<br />
transactions annually.<br />
Trend #3: Secure, connected<br />
identities will fuel safety and innovation<br />
in how we work, shop and play:<br />
The industry will enter its next new<br />
chapter of connected identities, employing<br />
multi-layered security strategies<br />
that also include biometrics in<br />
order to bind these identities to their<br />
legitimate owners.<br />
Mid-year update: An explosion<br />
of trusted digital identities began ushering<br />
in new innovation opportunities<br />
during the first half of the year. This<br />
trend is being fueled by a growing interest<br />
in wearables and use of sensors<br />
for IoT-based solutions aimed at new<br />
use cases for employee productivity, asset<br />
tracking, energy management and<br />
employee safety. These developments<br />
serve as critical points of unification<br />
for trusted identities that make digital<br />
interactions more personal, contextual<br />
and valuable, and will pave the way<br />
for innovations like building occupant<br />
apps for the smart facility that enhance<br />
the user experience. During 2016, financial<br />
institutions made some of<br />
the most visible advances on the trust<br />
front, adopting a multi-layered approach<br />
to addressing potential mobile<br />
banking challenges at both the front<br />
end (consumer devices) and the back<br />
end (banking systems that recognize<br />
and facilitate legitimate user requests<br />
through mobile devices).<br />
Trend #4: There will be more attention<br />
on privacy in an increasingly connected<br />
and mobile-first world: Identity<br />
will expand beyond people and<br />
their personal identity to the identity<br />
of objects and their authenticity, accentuating<br />
the need to protect personal<br />
information across increasingly<br />
26<br />
interconnected devices, services and<br />
applications.<br />
Mid-year update: Gartner forecasts<br />
that 5.5 million new “things” are getting<br />
connected every day in 2016, increasing<br />
the need for embedded security<br />
and privacy technology across the<br />
payments, transportation, industrial,<br />
consumer and healthcare markets.<br />
In the earlier CityPoint example, this<br />
“<strong>Security</strong> of Things” goal is achieved<br />
by adding trust to RFID tags and to<br />
their interactions with mobile devices.<br />
Biometrics also continues to<br />
play a pivotal role in privacy<br />
protection for an increasingly<br />
connected world, and solutions<br />
became available in early 2016<br />
that include intelligent encryption-enabled<br />
and tamper-resistant<br />
fingerprint devices to more<br />
effectively address these challenges.<br />
Trend #5: <strong>Security</strong> policies and best<br />
practices will become as important<br />
as technology advances: The industry<br />
will sharpen its focus on not only<br />
what to deploy, but how – from the<br />
first U.S. mobile driver licenses to<br />
unified credential management systems<br />
that enable organizations to<br />
more holistically address both facility<br />
and information security. Rather<br />
than focus exclusively on preventing<br />
breaches, the industry will also adopt<br />
best practices for controlling what<br />
More on page 43
FROM OUT Of THE BOX<br />
to STATE OF THE ART.<br />
ID CARD PRINTING INNOVATION.<br />
HID Global is leading the industry with the most robust portfolio of secure ID issuance<br />
solutions in the world. Our FARGO® line of printers and encoders provide governments,<br />
financial institutions and businesses of all sizes fast, efficient and reliable solutions that<br />
are as secure as they are affordable.<br />
You’ll call it innovation on demand. We call it, “your security connected.”<br />
YOUR SECURITY. CONNECTED | Visit us at hidglobal.com/printers<br />
© 2016 HID Global Corporation/ASSA ABLOY AB. All rights reserved. HID, HID Global, the HID Blue Brick logo, and the Chain Design are trademarks<br />
or registered trademarks of HID Global or its licensor(s)/supplier(s) in the US and other countries and may not be used without permission.
Forescout describes security challenges<br />
of handling both Republican and Democratic<br />
National Conventions<br />
By Katherine Gronberg,<br />
VP <strong>Government</strong> Affairs<br />
Inside RNC/DNC Convention<br />
Networks - Cybersecurity Challenges<br />
ForeScout had the honor of providing<br />
information security support<br />
for the Republican National Convention<br />
(RNC) and the Democratic<br />
National Convention (DNC). These<br />
were challenging environments<br />
as the networks were created and<br />
configured in a short time-span,<br />
they were more “IP-enabled” than<br />
any conventions in history and, of<br />
course, they were extremely high<br />
profile. But the lessons learned in<br />
Cleveland and Philadelphia are relevant<br />
to almost any complex network,<br />
including large commercial<br />
and government networks. It helped<br />
us to think about the conventions’<br />
networks in terms of buckets.<br />
Segmentation, Segmentation,<br />
Segmentation…<br />
Probably the biggest challenge in securing<br />
events like the conventions is<br />
that there are SO MANY ad hoc networks<br />
being created all the time. It’s<br />
an unavoidable requirement for the<br />
event to be successful. This happens<br />
in the commercial and government<br />
worlds too, although to a lesser extent.<br />
You have to divide your network<br />
up in to three high-level buckets.<br />
We called them The Wild West,<br />
Mission Control, and The Vault. If<br />
at all possible, these networks need<br />
to be completely isolated from each<br />
other. The key to success in the convention<br />
environments was to focus<br />
on controlling access to the most<br />
sensitive networks, while still ensuring<br />
that the less sensitive networks<br />
remained operational.<br />
The Wild West<br />
These days, people attending events<br />
like the conventions expect access to<br />
reliable free WiFi. Public access to<br />
WiFi enhances their experience and<br />
makes for a more successful and<br />
impactful event. However, “Secure<br />
free WiFi” is an oxymoron. When<br />
people connect to a public WiFi<br />
network, their traffic is often visible<br />
to other people on the network and<br />
they run a greater risk of having their<br />
device infected with malware. There<br />
are steps that can be taken to make<br />
users more secure, such as requiring<br />
WPA2 encryption and attempting<br />
to isolate users from each other, but<br />
28<br />
these efforts<br />
are only partially<br />
effective<br />
at best. In an<br />
environment<br />
like this, user<br />
education is<br />
necessary:<br />
instructing Katherine Gronberg<br />
users as to<br />
which network is the “Official” free<br />
WiFi network, and also advising users<br />
to not conduct sensitive business<br />
on public WiFi without establishing<br />
a VPN tunnel first. Above all else,<br />
the public free WiFi should NEVER<br />
have a connection back to Mission<br />
Control or The Vault. We developed<br />
specific policies that looked for<br />
cross-bucket communication and<br />
remediated any discovered anomalies.<br />
Mission Control<br />
Mission Control is the network for<br />
“official” business. These networks<br />
often include things like staff systems,<br />
kiosks, point-of-sale devices,<br />
VOIP phones, cameras, and many<br />
other mission-critical functions. In<br />
such a dynamic and transient network<br />
environment characterized by
so many wired and wireless<br />
network access points,<br />
unauthorized network access<br />
should be expected<br />
and planned for. Controlling<br />
access as much as possible<br />
by using passwords<br />
and other authentication<br />
protocols is critical. But<br />
the real key is continuous<br />
monitoring of the networks to<br />
look for unwanted behaviors (devices<br />
scanning your network, transmitting<br />
large amounts of data, or<br />
changing their profiles unexpectedly).<br />
Establishing a baseline of<br />
a known good state BEFORE the<br />
event begins is critical to identifying<br />
something that’s not supposed to be<br />
there. For all of the devices found,<br />
policies must be written that stipulate<br />
how a device must be handled<br />
depending on how it behaves. We<br />
started this process early on for the<br />
conventions and continually refined<br />
our baseline throughout the events.<br />
In addition to establishing a baseline,<br />
penetration testing, or “pentesting,”<br />
is highly encouraged. This<br />
will allow you to anticipate the<br />
methods that attackers may use to<br />
gain access to your network. Reconfiguring<br />
the network can mitigate<br />
some attacks. Others can be<br />
caught through Continuous Monitoring<br />
policies, but you first need to<br />
know what to look for. This is where<br />
a skilled pen tester comes in very<br />
handy. ForeScout did not pen test<br />
the conventions ourselves, however,<br />
we worked extensively with trusted<br />
White Hat resources to develop policies<br />
to catch malicious behavior that<br />
can indicate network intrusions.<br />
The Vault<br />
29<br />
The best advice for securing the<br />
most sensitive assets in an organization<br />
is: “Don’t connect it to the Internet!”<br />
If, for some reason, Internet<br />
connectivity is required, give these<br />
systems their own dedicated and<br />
highly monitored internet connection.<br />
Something as important as a<br />
teleprompter should be completely<br />
disconnected. A broadcast system<br />
is another example of something<br />
that deserves an isolated internet<br />
connection. If the only thing that is<br />
ever present on that connection is a<br />
broadcast system, network anomalies<br />
should be easy to detect. Leading<br />
up to the conventions, there was<br />
a lot of speculation around the potential<br />
hacking of teleprompters or<br />
broadcast systems, but in actuality,<br />
they were never connected to the<br />
convention networks. Physical security<br />
is also used to protect<br />
these assets – in this case,<br />
physical security was provided<br />
by Secret Service agents<br />
manning doors backstage. At<br />
a corporate datacenter, physical<br />
security is provided by<br />
things like guards and retinal<br />
scanners. At the end of the<br />
day, for your most critical assets,<br />
disconnect them from the network<br />
and rely on robust physical<br />
security.<br />
Katherine Gronberg is Vice President<br />
for <strong>Government</strong> Affairs at ForeScout<br />
Technologies. Prior to joining ForeScout,<br />
she was a professor at Georgetown<br />
University, teaching classes in<br />
cybersecurity and business-government<br />
relations. Katherine also founded<br />
and ran her own consulting firm,<br />
Gronberg Consulting, L.L.C., which<br />
represented top U.S. technology firms<br />
on their government relations strategies.<br />
Prior to this, Katherine worked<br />
for Morhard & Associates, L.L.C.<br />
Katherine began her Washington career<br />
in 2000 as a staff member on the<br />
Senate Appropriations Committee<br />
handling annual appropriations for<br />
a range of federal agencies. Katherine<br />
holds a Bachelor’s degree from Yale<br />
University, an MBA from the University<br />
of Virginia’s Darden School of<br />
Business, and is a former Fulbright<br />
Scholar.
Border <strong>Security</strong>/Immigration<br />
Why the Department of Homeland <strong>Security</strong><br />
should also end private prison contracts<br />
By Walter Ewing,<br />
American Immigration Coucil<br />
For two years, women and children<br />
from Honduras, El Salvador,<br />
and Guatemala have been fleeing to<br />
the United States to escape the extreme<br />
violence of gangs which control<br />
large swaths of territory within<br />
their home countries. And for two<br />
years the Obama Administration<br />
has responded to this humanitarian<br />
crisis by locking up the women<br />
and children seeking protection<br />
and then deporting them back to<br />
the countries where their lives may<br />
be in danger. In defiance of its obligations<br />
under international law,<br />
the Administration is<br />
Photo: Neil Conway<br />
trying to deter future Central<br />
American asylum<br />
seekers by coming down<br />
hard on current Central<br />
American asylum seekers.<br />
During that first “surge”<br />
of refugees two years ago, the<br />
Administration knew exactly what<br />
it needed to get a handle on the crisis:<br />
a bigger and better prison for<br />
women and children. And so, according<br />
to the Washington Post, the<br />
Administration handed a $1 billion,<br />
four-year contract to Corrections<br />
Corporation of America (CCA) to<br />
build a “massive detention facility<br />
for women and children seeking<br />
asylum.” In the sweetest of sweetheart<br />
deals, CCA “gets the money<br />
regardless of how many people are<br />
detained at the facility.”<br />
The facility in question<br />
is the South Texas Family<br />
Residential Center in Dilley,<br />
Texas. According to the<br />
Post:<br />
“In 2015, the first full year<br />
in which the South Texas<br />
Family Residential Center<br />
was operating, CCA—which<br />
operates 74 facilities—made<br />
30<br />
14 percent of its revenue<br />
from that one center<br />
while recording record<br />
profit. CCA declined to<br />
specify the costs of operating<br />
the center.”<br />
The Administration’s heavyhanded<br />
approach to the social turmoil<br />
currently engulfing Honduras,<br />
El Salvador, and Guatemala may<br />
mean big money for private contractors,<br />
but it’s not going to be an<br />
effective deterrent to women who<br />
are running for their lives or the<br />
lives of their children. If you or your<br />
child face murder, rape, or forced<br />
induction into a gang if you stay, as<br />
opposed to a slim chance of asylum<br />
if you head to the United States,<br />
then common sense dictates you<br />
head to the United States.<br />
Moreover, even looked at from a<br />
purely financial standpoint, CCA<br />
isn’t running a very cost-effective<br />
prison. The Post writes that:<br />
“When 2,400 people are detained,<br />
the government spends<br />
what amounts to $285 per day, per<br />
person, according to a Post calculation.<br />
When the facility is half-full,<br />
More on page 43
Donald Trump’s shortsighted immigration plans<br />
won’t secure the homeland<br />
By Walter Ewing<br />
As any serious national security expert<br />
will tell you, trying to find a potential<br />
terrorist by treating all immigrants<br />
or Muslims as security risks<br />
is far too vague to be effective. Accurate<br />
intelligence and effective information-sharing<br />
across agencies<br />
is the key to national security—not<br />
profiling. Yet in a bombastic <strong>August</strong><br />
15 speech, Republican presidential<br />
nominee Donald Trump offered up<br />
blatantly bigoted and utterly pointless<br />
proposals on national security<br />
including ideas like instituting an<br />
“ideological screening test” and “extreme<br />
vetting” to determine which<br />
would-be immigrants to the United<br />
States (especially Muslims) harbor<br />
“any hostile attitude towards our<br />
country or its principles.”<br />
Leaving aside Trump’s nativist<br />
histrionics, it would be a serious<br />
mistake to embrace policies that<br />
conflate immigration enforcement<br />
and counter-terrorism efforts, implying<br />
that immigration enforcement<br />
is a way to catch terrorists. In<br />
reality, immigration enforcement is<br />
not designed to catch terrorists; it is<br />
meant to catch people who violate<br />
immigration laws. Immigration-enforcement<br />
mechanisms might snare<br />
a terrorist if supplied with specific<br />
intelligence gleaned from counterterrorist<br />
operations, but immigration<br />
enforcement by itself is very<br />
unlikely to stumble upon and actually<br />
identify a terrorist. Without the<br />
right information in the right hands,<br />
even the most efficiently constructed<br />
immigration-enforcement and<br />
border-control mechanisms are not<br />
going to catch a terrorist.<br />
This is precisely why the 9/11<br />
Commission did not recommend<br />
that we adopt ethnic or religious<br />
profiling to help prevent another<br />
terrorist attack in the United States.<br />
Identifying threats actually depends<br />
on the development of “actionable<br />
intelligence” which identifies<br />
a specific threat, and then sharing<br />
that information with immigration<br />
and border-enforcement personnel.<br />
31<br />
Photo: Gage Skidmore<br />
This approach is a little more subtle<br />
than profiling millions of people,<br />
which actually undermines intelligence<br />
gathering by alienating ethnic<br />
and religious communities and the<br />
countries from which they come. A<br />
group of people who feel themselves<br />
to be under government attack is<br />
not likely to share information with<br />
(and report tips to) the same government<br />
which is attacking them.<br />
Nor are the governments of their<br />
home countries as likely to partner<br />
with the United States in counterterrorism<br />
operations.<br />
In evaluating the typically outlandish<br />
ideas thrown around by<br />
Trump, we should never forget that,<br />
shortly after 9/11, the federal government<br />
created the National <strong>Security</strong><br />
Entry-Exit Registration System<br />
(NSEERS). Under NSEERS, 83,000<br />
men from Muslim and Arab coun-<br />
More on page 44
Border <strong>Security</strong>/Immigration<br />
<strong>Government</strong> sued for withholding records<br />
on immigration raids<br />
By Tory Johnson<br />
The Department of<br />
Homeland <strong>Security</strong><br />
(DHS) is continuing<br />
to defend the controversial<br />
“Operation<br />
Border Guardian”<br />
program that<br />
took more than 100 Central American<br />
women and children from their<br />
homes in two days of immigration<br />
raids last January. According to a lawsuit<br />
filed this week by the Southern<br />
Poverty Law Center (SPLC) and the<br />
law firm Alston & Bird, the government<br />
has failed to release records related<br />
to the program under the Freedom<br />
of Information Act (FOIA).<br />
The complaint argues that DHS<br />
and its component agency Immigration<br />
and Customs Enforcement (ICE)<br />
violated public records law by failing<br />
to substantively respond to a January<br />
7 FOIA request seeking information<br />
related to the raids DHS conducted<br />
January 2 and January 3 in North<br />
Carolina, Georgia, and Texas. They<br />
are seeking records and information<br />
about how and why ICE went after<br />
the 121 individuals swept up in the<br />
raids.<br />
The widely-publicized round-ups<br />
raised concerns about constitutional<br />
and due process violations.<br />
146 members<br />
of Congress<br />
and more than 150<br />
organizations condemned<br />
the government’s<br />
actions,<br />
and local governments<br />
voiced their<br />
concerns about the damage to trust<br />
between communities and law enforcement.<br />
Lisa Graybill, SPLC deputy legal<br />
director, said that “there are serious<br />
questions about whether ICE agents’<br />
conduct during these raids violated<br />
the Constitution. We cannot allow<br />
ICE, the nation’s largest law enforcement<br />
agency, to avoid accountability<br />
and violate federal law by withholding<br />
these records.”<br />
The complaint alleges, for example,<br />
that ICE agents conducting the enforcement<br />
operations used deceptive<br />
tactics to enter homes. In some cases,<br />
according to the complaint:<br />
“ICE agents… stat[ed] that they<br />
were police officers looking for a<br />
criminal suspect and show[ed] residents<br />
a photo of an African-American<br />
man. In other instances, ICE<br />
agents allegedly stated that they were<br />
only taking the immigrants into custody<br />
for a short time to examine the<br />
32<br />
women’s electronic ankle shackles.”<br />
Moreover, “when asked for copies<br />
of warrants or orders to enter a home,<br />
ICE agents ignored the requests,<br />
threatened residents, or ordered them<br />
to ‘be quiet,’” according to the complaint.<br />
The families targeted by the raids<br />
actually had conditional permission<br />
to be in the United States. According<br />
to SPLC, they “had complied with orders<br />
of supervision provided by ICE,<br />
which permitted them to remain in<br />
the United States subject to certain<br />
conditions.” Yet the women and children<br />
were detained and most were<br />
subsequently deported. Only 12 families<br />
had their deportations halted,<br />
with the help of attorneys from the<br />
Dilley Pro Bono Project.<br />
ICE refuses to comment on pending<br />
litigation. The agency has 20 days<br />
and a 10-day extension to decide and<br />
notify SPLC whether or not it will<br />
comply with the request.<br />
Hopefully the government will act<br />
within that timeframe to release these<br />
important documents. As the complaint<br />
states, the public has a right to<br />
this information and the government<br />
a responsibility to be accountable for<br />
its actions.<br />
Photo: Julio Cesar
Court orders release of graphic photos of<br />
Arizona Border Patrol detention facilities<br />
WASHINGTON D.C. <strong>August</strong> 18,<br />
2016 - Today, groups made public<br />
damning evidence, including expert<br />
testimony and video stills illustrating<br />
the deplorable and unconstitutional<br />
conditions detained individuals<br />
are subjected to in Border<br />
Patrol custody in<br />
the agency’s Tucson<br />
Sector. The<br />
court rejected Border<br />
Patrol’s effort<br />
to conceal evidence<br />
of inhumane and<br />
abusive detention<br />
practices from the<br />
public. Accepting<br />
the position of the<br />
Plaintiffs and the<br />
Arizona Republic,<br />
which intervened to<br />
argue for the release<br />
of the materials, the<br />
court recognized that access to court<br />
proceedings and to basic information<br />
about governmental practices<br />
are fundamental First Amendment<br />
rights.<br />
The video stills and expert testimony<br />
released today reveal that Border<br />
Patrol holds individuals—among<br />
them traumatized asylum seekers<br />
and mothers with infants and small<br />
children—for days at a time in cold,<br />
overcrowded, and dirty cells that are<br />
designed to detain people for only<br />
a few hours. Graphic photographs<br />
show detainees packed head-to-foot<br />
Tucson facility: men wrapped in Mylar sheets on concrete floors and benches near<br />
trash & toilets<br />
in filthy, overcrowded rooms. One<br />
image captures a mother changing<br />
an infant’s diaper on a trash-strewn<br />
concrete floor.<br />
Also among the unsealed documents<br />
is testimony from an expert<br />
for the Plaintiffs who wrote that,<br />
in his 35 years of experience work-<br />
33<br />
ing in correctional facilities, he had<br />
“never been in one that treats those<br />
confined in a manner that the CBP<br />
treats detainees.”<br />
Among other conclusions about<br />
the poor treatment of individuals<br />
detained in Border Patrol facilities,<br />
he said that “[t]he<br />
absence of medical<br />
screening upon<br />
arrival is unthinkable,”<br />
and that he<br />
had never before<br />
witnessed an attempt<br />
to “cram” so<br />
many people into so<br />
little space, without<br />
beds and bedding.<br />
He concluded, “[t]<br />
he CBP [is] housing<br />
people in conditions<br />
that are unnecessarily<br />
harsh, dangerous<br />
and contrary to accepted industry<br />
practices and standards.”<br />
“Every step the <strong>Government</strong> has<br />
taken in response to this lawsuit has<br />
been designed to delay this suit and<br />
hide the conditions present at these<br />
facilities,” said Louise Stoupe of<br />
Morrison & Foerster. “The Govern-
Border <strong>Security</strong>/Immigration<br />
ment should be using the resources<br />
they are wasting in court to provide<br />
basic human necessities to those in<br />
its custody.”<br />
“Migrants detained in the Tucson<br />
sector have long suffered horrific<br />
conditions,” said Dan Pochoda,<br />
senior counsel for the ACLU of<br />
Arizona. “It is unconscionable that<br />
the federal government continues<br />
to detain people including infants<br />
in this manner. The Border Patrol<br />
continues to operate in violation of<br />
U.S. and international law as well<br />
as its own standards without being<br />
held accountable for these egregious<br />
abuses.”<br />
“These photos show the harm<br />
people suffer in these facilities, from<br />
having to sleep on the floor for days<br />
to needing to huddle together just to<br />
stay warm,” said Travis Silva, attorney<br />
with the Lawyers’ Committee<br />
for Civil Rights of the San Francisco<br />
Bay Area. “These conditions should<br />
not exist in a facility operated by the<br />
United States government.”<br />
“The images unsealed by the court<br />
leave no room to debate the fact<br />
that thousands of immigrants are<br />
subjected to inhumane and unconstitutional<br />
conditions by the Border<br />
Patrol,” said Nora Preciado, staff attorney<br />
with the National Immigration<br />
Law Center. “We urgently need<br />
meaningful and lasting reforms that<br />
put an end to these abuses, hold the<br />
agency accountable, and ensure that<br />
people are treated with dignity.”<br />
“Mothers should not be forced to<br />
change their babies’ diapers on cold<br />
concrete floors or warm them with<br />
flimsy aluminum sheets. Border<br />
Patrol’s treatment of men, women<br />
and children in its custody is simply<br />
inexcusable,” said Mary Kenney,<br />
senior staff attorney for the American<br />
Immigration Council. “We are<br />
seeking immediate relief from the<br />
deplorable detention conditions in<br />
CBP holding facilities for the thousands<br />
of individuals who are or will<br />
be held there while this case progresses.”<br />
In December, attorneys representing<br />
the Plaintiff class of detained<br />
immigrants sought a preliminary<br />
injunction to stop Border Patrol’s<br />
unconstitutional detention practices<br />
while the case is being litigated. The<br />
injunction is based on compelling<br />
evidence of inhumane conditions<br />
in Tucson facilities—much of which<br />
was disclosed after the Court sanctioned<br />
Border Patrol for destroying<br />
video recordings from these facilities<br />
and failing to turn over other<br />
relevant documentation.<br />
Jane Doe, et al. v. Johnson, et al.<br />
was filed in the U.S. District Court<br />
for the District of Arizona. Attorneys<br />
on the case include Harold J.<br />
34<br />
McElhinny, Colette Reiner Mayer,<br />
Louise C. Stoupe, Kevin M. Coles,<br />
Pieter S. de Ganon, and Elizabeth<br />
Balassone of Morrison & Foerster<br />
LLP; Nora Preciado, Linton Joaquin,<br />
and Karen C. Tumlin of the<br />
National Immigration Law Center;<br />
Mary Kenney, and Melissa Crow of<br />
the American Immigration Council;<br />
Travis Silva of the Lawyers’<br />
Committee for Civil Rights of the<br />
San Francisco Bay Area; and Kathy<br />
Brody, Brenda Muñoz Furnish, and<br />
Dan Pochoda of ACLU of Arizona.<br />
For additional links see:<br />
• Challenging Unconstitutions<br />
Conditions in CBP Short Term<br />
Detention Facilities (Litigation<br />
Page)<br />
• Photo Exhibits of CBP Short-<br />
Term Detention Conditions<br />
• Declaration by Joe Goldenson,<br />
M.D., Medical Conditions Expert<br />
• Declaration by Eldon Vail,<br />
Prison Conditions Expert<br />
• Declaration by Robert W. Powitz,<br />
Sanitation Expert<br />
• Detained Beyond the Limit:<br />
Prolonged Confinement by U.S.<br />
Customs and Border Protection<br />
along the Southwest Border (Special<br />
Report, <strong>August</strong> 2016)
3M’s new ALPR software extends reach, delivers<br />
real-time actionable intelligence<br />
ST. PAUL‚ Minn. – (<strong>August</strong> 4‚ 2016)<br />
– In order to create and maintain<br />
safe communities, law enforcement<br />
agencies are increasingly relying on<br />
technology. A new tool for officers<br />
is now available; 3M is proud to introduce<br />
3M Plate Alert Analytical<br />
ALPR Software, a next-generation<br />
ALPR software which uses data fusion<br />
analytics and proactive alerts to<br />
provide more answers and the confidence<br />
to act.<br />
Designed to be fast, powerful and<br />
intuitive, 3M Plate Alert Software<br />
allows officers to take action, faster.<br />
Collaborating with Human Factors<br />
Scientists to ensure the software<br />
can be learned quickly and used<br />
efficiently, Plate Alert Software features<br />
the latest user-centered design<br />
methods to optimize interfaces and<br />
usability. This makes it easier to set<br />
up, search, get alerts and find leads.<br />
3M also partnered with law enforcement<br />
agencies to offer the most<br />
in-demand features. The result is an<br />
ALPR software that is powerful and<br />
easy to use, so officers spend less<br />
time clicking and more time following<br />
up on leads.<br />
Going beyond typical ALPR<br />
software, which notifies users<br />
when a plate read matches a watch<br />
list, 3M’s Plate Alert Software features<br />
pattern management alerts.<br />
Designed to proactively provide<br />
relevant information and actionable<br />
insights in near real-time, pattern<br />
alerts ensure almost all of the work<br />
is done before an officer even looks<br />
at the data. Notifications are sent<br />
when the system detects activity<br />
matching a pre-defined pattern that<br />
may suggest illicit activity.<br />
“Plate Alert Software uncovers<br />
relevant connections and provides<br />
a clear view of how seemingly unrelated<br />
people, places, things and<br />
events are connected, and how they<br />
impact each other,” said Seth Stores,<br />
global business manager at 3M. “By<br />
providing a more complete, informative<br />
and accurate picture, officers<br />
35<br />
can spot patterns faster and take<br />
action to keep their communities<br />
safe.”<br />
3M Plate Alert Analytical ALPR<br />
Software is the first ALPR software<br />
powered by data fusion analytics.<br />
Plate Alert Software can compile<br />
ALPR data with data from various<br />
sources, such as 911 calls, pawn<br />
data, police reports, motor vehicle<br />
data and more. It can then almost<br />
instantly find connections between<br />
data points to deliver solid, meaningful<br />
leads. By linking and simultaneously<br />
evaluating numerous common<br />
characteristics across multiple<br />
data sources, Plate Alert Software<br />
can uncover unexpected relationships<br />
and associations. This means<br />
law enforcements agencies can get<br />
new answers and leads from their<br />
data. Using sophisticated secondorder<br />
analysis, data fusion analytics<br />
deliver more actionable intelligence<br />
than conventional ALPR software,<br />
which rely on first-order analysis.<br />
Plate Alert Software also has increased<br />
data privacy measures.<br />
Mandatory controls ensure data is<br />
only accessed for legitimate purposes<br />
by customer chosen individu-<br />
More on page 44
DevMynd obtains strategic investment from<br />
Motorola Solutions<br />
CHICAGO, IL, Aug. 18, 2016 –<br />
DevMynd, a leading-edge digital<br />
innovation consulting firm, announced<br />
today that it received<br />
Series A funding from Motorola<br />
Solutions Venture Capital.<br />
JC Grubbs, CEO, DevMynd,<br />
said the investment opens new<br />
collaborative opportunities that<br />
include the wave of innovation occurring<br />
in public safety and commercial<br />
communications.<br />
“We couldn’t be happier to be working<br />
with a partner that has such a rich<br />
tradition of solving problems that<br />
have a meaningful impact on people<br />
in critical situations,” Grubbs said.<br />
“Those are the types of challenges<br />
that we like to work on at DevMynd<br />
– things that really give us purpose.<br />
“Our experience in human-centered<br />
user research, user experience<br />
and service design will help Motorola<br />
Solutions and its customers develop<br />
products and apps that solve nextgeneration<br />
challenges,” he added.<br />
“And, we’re excited about opportunities<br />
to apply software engineering<br />
expertise to mobile, web and device<br />
needs that will result in robust, enterprise-grade<br />
solutions.”<br />
Paul Steinberg, chief technology officer,<br />
Motorola Solutions, said, “Both<br />
of our organizations look forward to<br />
working together on several fronts.<br />
DevMynd is an excellent example of<br />
our support of and collaboration with<br />
the entrepreneurial community in<br />
Chicago.<br />
“The adoption of broadband technology<br />
is driving innovation in public<br />
safety and commercial communications,”<br />
he added. “We know that<br />
tailored software and services will<br />
be required to deliver solutions and<br />
capabilities to our customers. We’re<br />
pursuing technological advances<br />
such as interoperable mobile applications<br />
for mission-critical communications<br />
and collaboration, enhanced<br />
situational awareness, real-time rich<br />
messaging, data analytics, and artificial<br />
intelligence. All of these are on<br />
the immediate horizon and we are<br />
looking for DevMynd to help us get<br />
these capabilities to our customers.”<br />
The strategic investment will allow<br />
DevMynd to expand its team,<br />
add new capabilities and enter new<br />
markets. It also will support access<br />
to strong strategy, design and custom<br />
software development services for<br />
Motorola Solutions and its customers.<br />
36<br />
About DevMynd<br />
DevMynd is an innovation firm in<br />
Chicago and San Francisco with<br />
practice areas in digital strategy,<br />
human-centered design, UI/UX,<br />
and custom mobile and web application<br />
development. The firm’s<br />
mission is to help its clients use<br />
technology to solve meaningful<br />
problems that have a profound<br />
impact on life, society and business.<br />
They serve clients ranging from startups<br />
to Fortune 100 firms that are investing<br />
in design, digital transformation<br />
and innovation. Learn more at<br />
https://www.devmynd.com.<br />
About Motorola Solutions<br />
Motorola Solutions (NYSE: MSI) creates<br />
innovative, mission-critical communication<br />
solutions and services<br />
that help public safety and commercial<br />
customers build safer cities and<br />
thriving communities. For ongoing<br />
news, http://www.motorolasolutions.<br />
com/newsroom or subscribe to a news<br />
feed.
Albuquerque police fight violence with<br />
intelligence-led policing<br />
The state of New Mexico has long<br />
held the dubious honor of high placement<br />
on the FBI National Crime Data<br />
Report. In 2014, the state was ranked<br />
the #2 most dangerous state in the<br />
Union. The city of Albuquerque has<br />
suffered a particularly high rate of<br />
violent crimes, with the number of<br />
murders in the city almost doubling<br />
between 2009-2013.<br />
Among the problems contributing<br />
to the high crime rate in Albuquerque<br />
is a proliferation of gangs. The<br />
Stop Albuquerque Gangs Task Force<br />
maintains an online list of known<br />
violent groups in the city. At the time<br />
of this writing, more than 100 gangs<br />
were listed on the website. The Albuquerque<br />
Police Department (APD)<br />
is not one of exceptional size, and<br />
has historically struggled to provide<br />
enough officers to effectively combat<br />
the problem.<br />
The APD is not the first and will not<br />
be the last police department to face<br />
this dilemma. Criminals have become<br />
more numerous, craftier, and are<br />
quick to take advantage of new technologies.<br />
Reactive police action, the<br />
traditional model of law enforcement<br />
in which police respond to crimes as<br />
they happen, has been steadily losing<br />
ground in the war against crime.<br />
Instead, more and more police departments,<br />
the APD included, are<br />
turning to a new paradigm known as<br />
intelligence-led policing. The core of<br />
this law enforcement model is “Work<br />
smarter, not harder.” In an intelligence-led<br />
police department, officers<br />
collect and analyze data using a variety<br />
of technologies and techniques.<br />
The data is used to decide where police<br />
resources should be committed to<br />
have the greatest effect. Intelligence<br />
officers are tasked with identifying<br />
repeat offenders and high risk areas,<br />
so that a department’s limited human<br />
resources can be utilized most efficiently.<br />
Intelligence-led<br />
policing is a revelation<br />
within the law<br />
enforcement community.<br />
In a study<br />
conducted by the<br />
non-profit Police<br />
Executive Research<br />
Forum (PERF), 54%<br />
of responding agencies<br />
reported that<br />
37<br />
they planned to increase the use of<br />
the practice within the near future.<br />
According to Wikipedia, intelligenceled<br />
policing has also found widespread<br />
adoption in Canada, Mexico,<br />
the UK, and New Zealand.<br />
A subset of intelligence-led policing<br />
is the burgeoning field of predictive<br />
policing. Intelligence officers within a<br />
department use collected data to construct<br />
heat maps and other models in<br />
an effort to predict where crimes are<br />
likely to occur, days or even weeks before<br />
they do.<br />
The heat map incorporates a vast<br />
amount of data about criminal activity<br />
over an area, allowing officers to<br />
visually identify the locations where<br />
crimes most densely concentrated.<br />
This technique allows “boots on the<br />
ground” to be sent where they can<br />
have the greatest positive effect, without<br />
wasting time patrolling quiet,<br />
low-risk areas. By patrolling the most<br />
crime-dense areas of Albuquerque,<br />
the APD is able to benefit the entire<br />
city by targeting the root causes of<br />
criminal activity.<br />
In Albuquerque, predictive policing<br />
requires the high volume collection of<br />
data about gang members and other<br />
likely criminal elements. The APD<br />
has successfully leveraged technology<br />
to accomplish this task in several<br />
ways.<br />
In 2013, the APD opened the Re-
al-Time Crime Center (RTCC). The<br />
RTCC is a locus of crime prevention<br />
technology, staffed with trained operators<br />
who monitor a network of static<br />
cameras around the city that today<br />
exceeds 1,000 units. RTCC personnel<br />
also monitor pawn shops for stolen<br />
goods and distribute a daily newscast<br />
to APD officers. They are largely responsible<br />
for the creation of the heat<br />
maps APD higher-ups use to intelligently<br />
assign police. The RTCC has<br />
proven effective, and is the recipient<br />
of an award from the International<br />
Association of Law Enforcement<br />
Planners.<br />
In its efforts to further develop the<br />
effectiveness of the RTCC and the<br />
APD as a whole, in 2014 the City of Albuquerque<br />
decided to invest in more<br />
advanced technology for its network<br />
of surveillance cameras. The selection<br />
criteria for the cameras prioritized<br />
flexibility and return on investment,<br />
meaning the cameras would have to<br />
cover more ground than the comparatively<br />
basic static-mounted cameras<br />
that comprised the original network.<br />
The new cameras would also necessarily<br />
be compatible with the existing<br />
systems at the RTCC, with a minimum<br />
of equipment retooling, software<br />
redevelopment, and operator<br />
retraining. After evaluating and testing<br />
camera solutions from a number<br />
of manufacturers across the United<br />
States, the APD settled on the Mobile<br />
Surveillance Unit (MSU) from<br />
ECAMSECURE.<br />
The MSU is essentially a freestanding<br />
camera tower. Each unit is portable<br />
enough to be towed by police<br />
vehicles, and can power and support<br />
a number of cameras with varying<br />
configurations. ECAMSECURE custom-designed<br />
and constructed several<br />
MSUs that incorporated a variety<br />
of pan / tilt / zoom (PTZ) cameras<br />
and fixed-angle HD cameras with a<br />
speaker feature to alert crowds to disperse.<br />
The portable nature of the MSUs<br />
has made them a perfect fit for Albuquerque’s<br />
push towards intelligenceled<br />
policing. The APD can now assign<br />
MSUs to heavy crime areas just as it<br />
does human officers. The imposing<br />
structures, bristling with cameras,<br />
have proven an effective deterrent for<br />
crime.<br />
By moving the MSUs from location<br />
to location, the APD keep criminals<br />
guessing as to whether or not they<br />
are under surveillance. The cameras<br />
have proven a boon for law-abiding<br />
citizens. <strong>News</strong> coverage reports that<br />
residents often feel safer and more<br />
protected with the cameras present.<br />
After moving an MSU out of a neighborhood,<br />
the APD typically fields requests<br />
and petitions for the cameras<br />
to return.<br />
Since the MSUs are a custombuilt<br />
solution tailored to each client,<br />
ECAMSECURE was able to ensure<br />
that they would be seamlessly compatible<br />
with the existing equipment<br />
and software at the RTCC. By sourcing<br />
compatible hardware and modifying<br />
software where needed, the<br />
MSU deployed in Albuquerque can<br />
be accessed by RTCC operators using<br />
largely the same interface and software<br />
they have already used for years.<br />
38<br />
ECAMSECURE technicians accompanied<br />
the initial deployment of<br />
MSUs to Albuquerque to train RTCC<br />
operators in their use, and support<br />
personnel have remained on-call to<br />
the APD 24/7. The APD leadership<br />
has praised ECAMSECURE for its<br />
dedication to service and support,<br />
especially the fast response time and<br />
willingness to resolve any issue, problem,<br />
or concern.<br />
The Mobile Surveillance Units have<br />
proven to be an excellent fit for the<br />
APD, and an order for additional<br />
units is already underway. ECAMSE-<br />
CURE is making several design upgrades<br />
and improvements for the next<br />
shipment of MSUs. The new units will<br />
include license plate capture, as well<br />
as other refinements. The existing run<br />
already deployed in Albuquerque will<br />
also be upgraded to match the new<br />
units.<br />
The crime rate in Albuquerque is<br />
today still high, but dropping through<br />
the efforts of the APD, the RTCC, and<br />
ECAMSECURE. Using the MSUs, the<br />
RTCC is able to alert APD officers of<br />
crimes in progress, as well as in suspicious<br />
activity or congregations that<br />
may erupt into violence. Using the<br />
two-way audio features, RTCC operators<br />
can even resolve some situations<br />
on their own, by broadcasting to<br />
would-be criminals that the police are<br />
on their way.<br />
The partnership is expected to continue,<br />
helping the APD leverage the<br />
latest technologies to safeguard the<br />
law-abiding residents of the city.
Access Control/Biometric ID<br />
Peter Smallridge, 3M Traffic Safety and <strong>Security</strong> Manager,<br />
discusses E.U. border security management, trends, new<br />
3M products and similarity to U.S. practices<br />
By Adrian Courtenay<br />
In a wide-ranging discussion that<br />
covered successful border security<br />
initiatives, new directions and<br />
needs for improvement in border<br />
security management in the European<br />
Union, including comparisons<br />
with U.S. practices, Peter Smallridge<br />
outlined the pros and cons of<br />
passport readers, biometrics, facial<br />
recognition, passwords with<br />
chips on them, automated border<br />
control, kiosks, mobile transport<br />
and the treatment of refugees.<br />
By necessity, the discussion also<br />
focused on the many ways to enter<br />
a country, from airports and<br />
seaports to automobiles, trains and<br />
private planes – not to mention the<br />
question of what happens to people<br />
after they have arrived in a country.<br />
“Many companies around the<br />
world are talking about exit,” said<br />
Smallridge. “They come in, we don’t<br />
know if they went home. Is he or she<br />
still here? We have no information<br />
whatsoever. That’s the big concern.<br />
In an ideal world, you want reporting<br />
of people coming in through any<br />
mobile transport – and recording of<br />
the exit. This is a megatrend.”<br />
“Across the world, border agencies<br />
are trying to get smarter,” he<br />
pointed out. “We focus on airports<br />
and mainly on people arriving<br />
through the airport. But in the E.U.<br />
we’ve found in some cities that only<br />
50% of the people enter via airports.<br />
Many cross land borders to go to<br />
work each day. Some come through<br />
seaports, some through civil airports.<br />
And you can leave by different<br />
routes or border agencies.”<br />
In response to security incidents<br />
or terrorism, Smallridge pointed<br />
out, a second reality in border security,<br />
that governments can be<br />
pressed for cash. <strong>Government</strong>s<br />
think this is where they can save<br />
some money. And unfortunately<br />
39<br />
this happens at the same time they<br />
want to replicate their installations<br />
into different locations.<br />
The solution that is taking place<br />
is that there is a big move toward<br />
Automated Border Control (ABC).<br />
It could be kiosks, gates or barriers<br />
– sometimes called – gates.<br />
Sometimes these are for everybody,<br />
sometimes they’re for people who<br />
register, as in the Global Entry<br />
System. This is about processing<br />
people in a self-service way. “It’s<br />
the least we can do with resident<br />
nationals or people from friendly<br />
countries who probably are not a<br />
risk – if you can get them to use<br />
the machines. Depending on the<br />
situation, some numbers of officers<br />
may have to be deployed in some<br />
venues.”<br />
But deploying officers can also<br />
create a major challenge – a technical<br />
one, because an officer from<br />
one post who then goes to another<br />
post to operate a different type of<br />
machinery may not know how to<br />
do it. This can be problematic, for<br />
instance, if the officer has to handle<br />
a finger print reader that he is not
Access Control/Biometric ID<br />
familiar with and neither is the traveler,<br />
it can call delays.<br />
There are lots of technical issues<br />
like these that 3M is considering,<br />
said Smallridge. “For example, if<br />
there’s a chip on the passport and it<br />
takes several seconds to open, and<br />
the user is used to seeing chips in<br />
a supermarket, he or she may need<br />
help in order to be processed. Our<br />
objective here is to make the systems<br />
easier to use, more intuitive, so<br />
that we can use them without having<br />
to think.”<br />
Automated Border Control is also<br />
being considered in the E.U. for sea<br />
borders. People arriving by ship<br />
may be coming off a car and may<br />
come to a barrier system where they<br />
are processed by password and fingerprint.<br />
Or they may have to get<br />
out of the vehicle, go into a building,<br />
or you drive next to a barrier of<br />
some sort.<br />
In the case of trains, an officer<br />
may have to walk through a with<br />
some kind of mobile device processing<br />
people as they go through. But<br />
often, because the train is going to<br />
arrive soon at the next station, and<br />
people are going to get off, there are<br />
more complications.<br />
Alongside all of that, there is the<br />
subject of biometrics. Typically, finger<br />
prints have been the most accurate<br />
and reliable system. They can<br />
also benefit law enforcement agencies,<br />
when they catch criminals or<br />
when they find evidence left behind,<br />
since the law enforcement officers<br />
do not typically have Iris processing.<br />
Finger prints have been the<br />
main biometric used for authentication.<br />
But that is changing, says<br />
Smallridge. “In order to process<br />
these people properly and to avoid<br />
queues, agencies are looking to use<br />
more than one type if biometric,<br />
because it takes too long to find<br />
the fingerprint. Thus we’re going<br />
to have to more than one biometric,<br />
because it takes too long to find<br />
the fingerprint. Thus many agencies<br />
around the world are now talking<br />
about ‘face and finger.’ If I select two<br />
of them on the way in, I can use anyone<br />
of them on the way out. It might<br />
be easier to face the people without<br />
stopping them.”<br />
The need for two means of processing<br />
has also created interest in<br />
iris usage, when neither face or finger<br />
are a good idea, such as where<br />
40<br />
it’s difficult to lean across a vehicle<br />
where someone is sitting next to the<br />
window, to finger print somebody,<br />
or when it is too dark to see their<br />
faces It also may be too dark to see<br />
their faces.<br />
Summing up on the logistical<br />
challenges, if you tighten up on the<br />
system, how do you avoid lines? If<br />
you’re going to the U.S., you don’t<br />
want to wait two hours to be processed.<br />
That’s why there’s so much<br />
effort being put into effect to make<br />
things smarter, and that’s why prebooking<br />
is getting more uses. When<br />
you book American Airlines, for example,<br />
they ask you for your passport<br />
during the booking process,<br />
and the information is supplied to<br />
the country of arrival, which will<br />
either use it to interview you when<br />
you arrive or possibly tell the airport<br />
not to board you.<br />
“We’re going to see more of these<br />
types of systems,” says Smallridge.<br />
“When I come to the United States,<br />
I get an ESTA, which is a kind of<br />
visa. The U.K. is a visa waiver country,<br />
where you buy a twelve month<br />
visa that costs something like $15.<br />
The ESTA determines validity of the<br />
entry to the country. In some countries,<br />
you have to go to the airport,<br />
where you provide ten fingerprints<br />
and probably will be asked a few<br />
More on page 44
LBsecure promotes best-of-class granular<br />
and layered security solutions for its clients<br />
within SAP<br />
LBsecure is partnered with realtime,<br />
a unique “Control and Monitoring”<br />
security software for SAP,<br />
called bioLock. Designed by former<br />
SAP engineers, bioLock allows you<br />
to secure your SAP enterprise from<br />
the inside-out, with granular and<br />
layered solutions, including unique<br />
identification and natively embedded<br />
SAP security software.<br />
With successful installations<br />
around the world, bioLock’s software<br />
and biometric re-authentication<br />
protocols can easily be installed<br />
through a port natively embedded<br />
within your SAP ERP. Also providing<br />
flexibility and integration with<br />
many different biometric partners.<br />
bioLock can distinguish between<br />
legitimate users and imposters in<br />
real time and instantly alert risk<br />
management and senior administrators<br />
by secure email notification.<br />
bioLock is easy to install and does<br />
not require any outside monitoring<br />
or the expense of MSSP support.<br />
It also eliminates any need for 3rd<br />
party security monitors to have access<br />
to your privileged information.<br />
SAP normally relies<br />
on simple single<br />
sign-on procedures or<br />
“password only” protection<br />
to gain access.<br />
Unfortunately stolen or shared administrative<br />
passwords allow intruders<br />
to roam freely once inside<br />
the system. Insider fraud can be a<br />
major risk factor for this very reason.<br />
Now SAP administrators can easily<br />
make dramatic security improvements<br />
by implementing rigorous reauthentication<br />
protection at layered<br />
and granular levels. Customizing<br />
user-specific biometric checkpoints<br />
dictated by the organization and the<br />
governing body and not an outside<br />
security provider.<br />
Enhancing your present SAP<br />
security solution with bioLock’s<br />
unique identity management solution.<br />
Providing positive re-authentication<br />
and indisputable realtime<br />
audit trails. In addition to providing<br />
the best defense against fraud, bioLock<br />
ensures compliance with various<br />
government regulations, which<br />
41<br />
rely on log-in activities within SAP,<br />
i.e. ITAR, HIPAA, Sarbanes Oxley,<br />
GRC, etc.<br />
We invite you to explore and evaluate<br />
how bioLock can further protect<br />
your SAP initiative from unwanted<br />
intrusion, as it has done for<br />
many businesses around the world<br />
from finance, supply chain, pharmaceutical<br />
and many many more.<br />
Case Studies are available for Supply<br />
Chain, Banking Fraud, Procure<br />
to Pay, Payroll Fraud, Retail/POS,<br />
Employee Self-service, Workflow<br />
Approvals, Perimeter <strong>Security</strong>,<br />
HIPAA Compliance, Public Sector<br />
Fraud.
Cypherpath, Quali partnership<br />
provides portable containerized<br />
infrastructures<br />
Continued from page 10<br />
their underlying IT infrastructure<br />
“Public and private sector organizations<br />
need agility and security<br />
to compete, which is forcing them<br />
to look for solutions that bypass all<br />
of the roadblocks caused by legacy<br />
infrastructure,” said Danial Faizullabhoy,<br />
president and CEO, Cypherpath.<br />
“Through this partnership, our<br />
joint customers have access to innovative<br />
on-demand solutions that<br />
provide IT infrastructures to support<br />
testing, training, and experimenting<br />
in sandboxes and cyber ranges at<br />
scale.”<br />
“The modern enterprise needs to<br />
be extremely vigilant and responsive<br />
to sophisticated security threats. Cyber<br />
ranges are a great tool to simulate<br />
real-world attack scenarios in a controlled<br />
environment and strengthen<br />
the security posture”, said Lior<br />
Koriat, CEO, Quali. “Quali cloud<br />
sandboxes help organizations build<br />
cyber ranges and other portable ondemand<br />
environments in a cost effective<br />
manner to model, orchestrate<br />
and test advanced threats. We’re excited<br />
to partner with Cypherpath to<br />
offer this solution to our defense and<br />
enterprise customers.”<br />
About Quali<br />
Quali is the leading provider of<br />
Cloud Sandboxes for automating<br />
the DevOps lifecycle. Quali gives innovators<br />
control over their world by<br />
enabling them to create personalized<br />
replicas of the most complex production<br />
environments. The Cloud providers,<br />
Telcos, Technology vendors<br />
and Enterprises including the Global<br />
100 depend on Quali to help them<br />
deliver their products and services to<br />
market faster and with better quality.<br />
Learn more at: http://www.quali.com<br />
About Cypherpath<br />
Enterprises rely on Cypherpath to<br />
create, deliver and manage containerized<br />
on-demand infrastructure at<br />
the lowest possible cost while providing<br />
container security and simplified<br />
control of the entire stack.<br />
Cypherpath’s industry-leading enterprise<br />
software platform encapsulates<br />
virtualized compute, network,<br />
and storage resources into software<br />
containers running on commodity<br />
hardware. Learn more at http://www.<br />
cypherpath.com<br />
About TSI<br />
TSI is a systems integrator and value<br />
added reseller focusing on providing<br />
innovative automation, orchestration,<br />
test, and virtualization solutions<br />
for network centric environments.<br />
TSI has been Quali’s Partner<br />
and Service Provider since 2010 integrating<br />
tools like those from Cypherpath.<br />
For information go to our<br />
website www.tsieda.com or email at<br />
sales@tsieda.com.<br />
42<br />
Telos Corporation: 2016 Winner,<br />
Best Biometric Identification/<br />
Authentication Solution<br />
Continued from page 13<br />
FBI and TSA have engaged Telos<br />
ID on a pilot basis to be part of the<br />
continuous-vetting/always-on FBI<br />
Rap Back Program. As continuous<br />
monitoring and assessment are to<br />
IT security, so continuous vetting<br />
is to the insider threat. To know<br />
in real time that a previously vetted<br />
employee’s criminal record has<br />
changed, for example, offers another<br />
critical tool for securing our<br />
airports.<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly <strong>Digital</strong> <strong>Edition</strong><br />
Airport/Seaport <strong>News</strong>letter<br />
Daily Insider <strong>News</strong>letter<br />
GSN Media Kit<br />
CLICK HERE
HID Global provides mid-year<br />
update on top trends<br />
Continued from page 26<br />
happens afterwards, so stolen identities<br />
are useless to thieves.<br />
Mid-year update: Through mid-year,<br />
the world moved closer to deploying<br />
driver licenses on mobile phones, while<br />
two key policy issues emerged through<br />
mid-year: protecting privacy by using<br />
a smartphone’s Bluetooth connection<br />
so users needn’t physically relinquish<br />
their smartphones to officers and officials,<br />
and ensuring citizens can control<br />
what data is made available to others.<br />
Beyond citizen ID, general security<br />
best practices and policies remain important<br />
for virtually any organization,<br />
and demand grew for HID Global services<br />
that help customers deploy innovative<br />
solutions to meet compliance,<br />
security and risk management needs,<br />
while enabling new, value-added capabilities.<br />
HID Global’s Seos® credential technology<br />
continues to help drive these<br />
trends, enabling organizations to<br />
confidently incorporate mobile solutions<br />
and empower their users with<br />
new applications and capabilities.<br />
For more HID Global news, visit<br />
our Media Center, read our Industry<br />
Blog, subscribe to our RSS Feed,<br />
watch our videos and follow us on<br />
Facebook, LinkedIn and Twitter. To<br />
read about HID Global’s mobility initiative,<br />
click here.<br />
About HID Global<br />
HID Global is the trusted source for<br />
innovative products, services, solutions,<br />
and know-how related to the<br />
creation, management, and use of<br />
secure identities for millions of customers<br />
around the world. The company’s<br />
served markets include physical<br />
and logical access control, including<br />
strong authentication and credential<br />
management; card printing and personalization;<br />
visitor management systems;<br />
highly secure government and<br />
citizen ID; and identification RFID<br />
technologies used in animal ID and<br />
industry and logistics applications.<br />
The company’s primary brands include<br />
ActivID®, EasyLobby®, FAR-<br />
GO®, IdenTrust®, LaserCard®, Lumidigm®,<br />
Quantum Secure, and HID®.<br />
Headquartered in Austin, Texas, HID<br />
Global has over 2,700 employees<br />
worldwide and operates international<br />
offices that support more than 100<br />
countries. HID Global® is an ASSA<br />
ABLOY Group brand.<br />
For more information, visit http://<br />
www.hidglobal.com.<br />
43<br />
Why the Department of Homeland<br />
<strong>Security</strong> should also end private<br />
prison contracts<br />
Continued from page 30<br />
as it has been in recent months, the<br />
government would spend $570. On<br />
some days when the facility is nearly<br />
empty, as it was for a period in<br />
January, the government would be<br />
paying multiples more.”<br />
Why would the government give<br />
a handout like this to a private company?<br />
Perhaps it stems from the fact<br />
that CCA “has on its payroll a slew<br />
of former senior government officials,”<br />
who are—presumably—very<br />
well connected. Regardless of how<br />
CCA procured such a bargain, the<br />
real bottom line is that a civilized<br />
nation does not put asylum seekers<br />
behind bars and then try as hard as<br />
possible to deport them back to the<br />
deadly situations they are fleeing.<br />
The Department of Homeland<br />
<strong>Security</strong> (DHS), which bears the<br />
responsibility for immigration detention,<br />
would be wise to follow<br />
the lead the Department of Justice,<br />
which just announced it is no longer<br />
going to use private prisons.
Donald Trump’s shortsighted<br />
immigration plans won’t secure the<br />
homeland<br />
Continued from page 31<br />
tries stepped forward<br />
and registered with<br />
the federal government,<br />
resulting in<br />
13,000 deportations.<br />
However, no one who registered under<br />
NSEERS was ever charged with<br />
a crime related to terrorism. The<br />
“special registration” requirement<br />
ended in December 2003, while<br />
NSEERS as a whole was scrapped in<br />
April 2011. What Trump is proposing<br />
is NSEERS on a massive scale.<br />
It is important to keep in mind<br />
that “security” is about more than<br />
just keeping out those who would<br />
threaten our national security. It<br />
is also about creating and maintaining<br />
a vibrant economy and dynamic<br />
society that attract people<br />
from around the world. It is about<br />
establishing our global credibility<br />
as a society in which the rule of law<br />
and fundamental human rights are<br />
highly valued and respected. And it<br />
is about not undermining U.S. relationships<br />
with the allies needed to<br />
effectively combat international terrorists.<br />
If we move too far away from<br />
these goals, building a locked-down<br />
nation in which fear runs rampant<br />
and productivity and creativity are<br />
starved, then what exactly are we attempting<br />
to “secure”?<br />
3M’s new ALPR software extends<br />
reach, delivers real-time actionable<br />
intelligence<br />
Continued from page 35<br />
als, and audit reports provide a full<br />
view of system activity to identify<br />
any potential misuse of sensitive or<br />
private data.<br />
“From parking lots and highways<br />
to ports and borders, we are<br />
committed to protecting law enforcement<br />
officials and their communities,”<br />
said Stores. “Plate Alert<br />
Software is the newest innovation to<br />
support those who take the oath to<br />
protect and serve.”<br />
About 3M<br />
At 3M, we apply science in collaborative<br />
ways to improve lives daily.<br />
With $30 billion in sales, our 90,000<br />
employees connect with customers<br />
all around the world. Learn more<br />
about 3M’s creative solutions to the<br />
world’s problems at www.3M.com or<br />
on Twitter @3M or @3M<strong>News</strong>room.<br />
3M and 3M Science. Applied to Life. are<br />
trademarks of 3M Company. Used under<br />
license in Canada.<br />
44<br />
Peter Smallridge, 3M Traffic Safety<br />
and <strong>Security</strong> Manager, discusses<br />
E.U. border security<br />
Continued from page 40<br />
questions.<br />
Another major trend is Interoperability<br />
of Systems. In the U.S. there<br />
are different fingerprint systems<br />
which are called “AFIS” systems.<br />
These are fingerprint identify systems.<br />
Some are for border, a second<br />
group is for dealing with criminals,<br />
and the third group is use by the<br />
military. This system is not available<br />
in Europe, since a big objective<br />
in Europe is to separate systems so<br />
that citizens’ private affairs cannot<br />
be misused by politicians.<br />
Smallbridge adds that “The terrorist<br />
incidents in the last few months<br />
have proved the weakness of that<br />
concept”.<br />
He concludes the interview with a<br />
number of observations of the U.S.<br />
differences in practices from those<br />
of the European Union, and lists a<br />
number of objectives and initiatives<br />
that 3M is working with, pointing
out that 3M is one of the big three in<br />
this area – 3M, BEC and Morpho/<br />
Safron. As a company generating<br />
upwards of $30-billion in revenues,<br />
3M definitely has the wherewithal<br />
to research and produce topnotch<br />
solutions and take a long view.<br />
In the U.S., identification systems<br />
are operated by Customs and Border<br />
Protection, and with the purchase<br />
some years ago of Cogent Systems,<br />
the CBP biometric matching<br />
system contains about 200 million<br />
people in its database; the criminal<br />
database is handled by the FBI and<br />
the military databases are handled<br />
by the Department of Defense.<br />
3M is working now on Mission<br />
Critical systems, the AFIS system<br />
and is modernizing capabilities for<br />
multiple biometric matching. 3M<br />
has also been working on facial<br />
recognition, voice recognition, mobile<br />
readers for such applications<br />
as walking through trains or entire<br />
cities, and further document reader<br />
improvement to enable processing<br />
of people who don’t speak English.<br />
“Learning our customers’ problems<br />
is the best way to solve the<br />
problems,” says Smallbridge. “It’s<br />
the kind of things we worry about.<br />
Can we see it? How? Do we need to<br />
acquire? That would be our scope.<br />
We’re a big company with many divisions.<br />
We share information inhouse<br />
with other divisions. Usability<br />
is very important to us.<br />
Sign-up for Free<br />
GSN <strong>Digital</strong> <strong>Edition</strong>s<br />
and Email <strong>News</strong>letters<br />
Free subscription to your selection of GSN digital editions<br />
and daily/weekly email newsletters. Add new selections or<br />
opt-out of any selections at any time.<br />
GSN Airport, Seaport, Rail, Border <strong>Security</strong> Weekly<br />
GSN Daily Insider <strong>News</strong>letter (5 Days Weekly)<br />
GSN Monthly <strong>Digital</strong> <strong>Edition</strong><br />
GSN Media Kit<br />
CLICK HERE<br />
The <strong>News</strong> Leader in Physical, IT and Homeland <strong>Security</strong><br />
www.gsnmagazine.com<br />
45
The <strong>News</strong> Leader in Physical, IT and Homeland <strong>Security</strong><br />
CEO/Editorial Director<br />
Adrian Courtenay<br />
917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Editor<br />
Steve Bittenbender<br />
502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Senior Writer<br />
Karen Ferrick-Roman<br />
412-671-1456<br />
karenferrickroman@gmail.com<br />
Columnist<br />
Shawn Campbell<br />
Campbell on Crypto<br />
shawn.campbell@safenetat.com<br />
Columnist<br />
George Lane<br />
Hazmat Science & Public Policy<br />
georgelane@hotmail.com<br />
Contributing Author<br />
Lloyd McCoy Jr<br />
Immix Group<br />
Contributing Author<br />
Walter Ewing<br />
Contributing Author<br />
Wendy Feliz<br />
Contributing Author<br />
Joshua Breisblatt<br />
Contributing Author<br />
J. Michael Barrett<br />
Contributing Author<br />
Christopher Millar<br />
Gatekeeper <strong>Security</strong><br />
Art Director<br />
Gerry O’Hara, OHDesign3<br />
gerry@ohd3.com<br />
203-249-0626<br />
Production Manager<br />
Brenden Hitt<br />
Brenden.hitt@gsnmagazine.com<br />
Direct: 203-216-7798<br />
COMING ATTRACTIONS<br />
September<br />
Tech Focus<br />
School Safety/Mobile<br />
Surveillance Solutions<br />
Market Sector Focus<br />
Maritime/Coastal/<br />
Port <strong>Security</strong><br />
October<br />
Tech Focus<br />
International Threats/<br />
Cyber Intelligence<br />
Market Sector Focus<br />
Oil/Gas/Electricity<br />
Grid <strong>Security</strong><br />
November<br />
Tech Focus<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Market Sector Focus<br />
Mass Notification/<br />
Disaster Response<br />
46
GSN’s 2016 Homeland <strong>Security</strong> Awards Program<br />
Now Accepting Entries at:<br />
www.gsnmagazine.com/hsa2016/welcome<br />
The 2016 <strong>Government</strong> <strong>Security</strong> <strong>News</strong> Awards Program, featuring<br />
many new categories in Cybersecurity, Physical <strong>Security</strong>, <strong>Government</strong><br />
Agency Innovations and Mobile Technologies will open for entries on<br />
<strong>August</strong> 24 and will close for entries on November 15.<br />
In good news for Winners and Finalists, GSN will be reinstating its<br />
annual Homeland <strong>Security</strong> Awards Dinner in Washington, DC in<br />
the first week of December, in a venue to be announced. Longtime<br />
participants in the GSN awards programs will recall that previous<br />
GSN Awards Dinners have featured top government, military leaders<br />
and respected television commentators such as 4-Star General<br />
Barry McCaffrey (Ret); Fran Townsend, Homeland <strong>Security</strong> Advisor to<br />
George W. Bush, James Kallstrom, Assistant Director of the FBI and<br />
Admiral Thad Allen (Ret), Commandant of the U.S. Coast Guard<br />
who came out of retirement twice to serve his county, first in<br />
Hurricane Katrina and later in the BP Oil Spill.<br />
The cost of an entry for vendors is $300 per entry, but there is no<br />
charge for government agencies or departments. All Winners<br />
and Finalists receive Awards Emblems, and all Winners receive a<br />
handsome, gold-trimmed plaque describing their winning entries.<br />
All Winners and Finalists will also be invited to participate in the 2016<br />
<strong>Digital</strong> Yearbook of Awards Winners.<br />
To see photo gallery of previous Awards Dinners:<br />
https://www.flickr.com/photos/44536438@N06/<br />
For information on the Awards Dinner or Sponsorships,<br />
Contact Adrian Courtenay, Managing Partner, at<br />
acourtenay@gsnmagazine.com, (Mobile) 917-696-5782