GSN_Oct_YUMPU
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
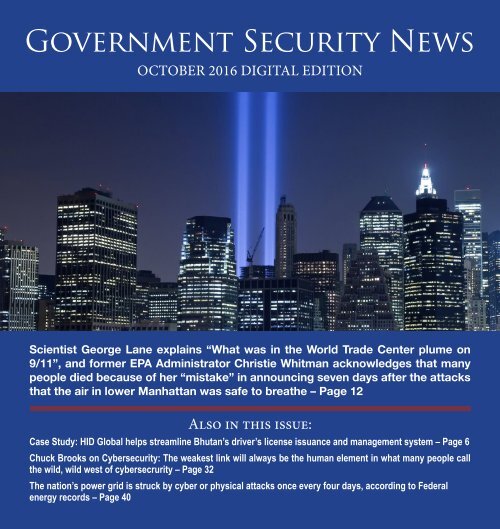
Government Security News<br />
OCTOBER 2016 DIGITAL EDITION<br />
Scientist George Lane explains “What was in the World Trade Center plume on<br />
9/11”, and former EPA Administrator Christie Whitman acknowledges that many<br />
people died because of her “mistake” in announcing seven days after the attacks<br />
that the air in lower Manhattan was safe to breathe – Page 12<br />
Also in this issue:<br />
Case Study: HID Global helps streamline Bhutan’s driver’s license issuance and management system – Page 6<br />
Chuck Brooks on Cybersecurity: The weakest link will always be the human element in what many people call<br />
the wild, wild west of cybersecrurity – Page 32<br />
The nation’s power grid is struck by cyber or physical attacks once every four days, according to Federal<br />
energy records – Page 40
NEWS<br />
<strong>GSN</strong> <strong>Oct</strong>ober 2016 Digital<br />
12<br />
4<br />
5<br />
6<br />
15<br />
16<br />
19<br />
20<br />
24<br />
25<br />
26<br />
27<br />
What was in the World Trade Center chemical plume at<br />
Ground Zero on 9/11<br />
Salient CRGT awarded $22.6M contract from DHS<br />
to improve border technologies<br />
GTT releases most advanced TSP solution to date:<br />
modular, expandable Opticom CVP<br />
HID Global helps streamline Bhutan’s driver license issuance<br />
and management system<br />
Canon U.S.A. and National Crime Prevention Council collaborate<br />
to raise awareness of theft and safety concerns<br />
The Technology War: Advantages of Network-Centric<br />
approach to modern warfare<br />
International sports competition in Brazil catapults<br />
to Gold Standard of ID Management with<br />
Quantum Secure<br />
The 2015 ISIS Attacks on Paris: Assessment and Lessons Learned<br />
Handheld Narcotics Analyzer can now detect lethal W-18 opioid drug<br />
FLIR announces identiFINDER R100 personal radiation detector<br />
with integrated Bluetooth smart technology<br />
Cambridge Pixel enhances radar tracking software<br />
to support small target detection<br />
Vecna attainst DoD DIACAP Security Accreditation<br />
and ATO for patient self-service solution<br />
2
Edition Table of Contents<br />
28<br />
29<br />
30<br />
Even the Government’s own advisory committee wants<br />
to end family detention<br />
How the Vice Presidential candidates responded to<br />
immigration issues at the debate<br />
Class action lawsuit challenging failure of CBP to respond to<br />
Freedom of Information requests is dismissed following settlement<br />
FEATURES<br />
SPECIAL REPORT ON INTERNATIONAL THREAT/CYBER INTELLIGENCE<br />
32<br />
36<br />
37<br />
38<br />
Chuck Brooks on Cybersecurity: The weakest link will<br />
always be the human element<br />
Arrest of ex-NSA contractor shows federal<br />
cybersecurity still faces a serious insider threat<br />
Intelligent Automation Inc discusses cyber attacks<br />
and tools of analysis and mitigation<br />
Convy on Net-Centric Security:<br />
The future of identity management is<br />
on the tips of your fingers<br />
SPECIAL REPORT ON OIL/GAS/ELECTRIC GRID SECURITY<br />
40<br />
42<br />
44<br />
The nation’s power grid is struck by cyber or physical attacks once every four<br />
days, according to federal energy records<br />
Quanergy acquires OTUS People Tracker Software<br />
from Raytheon BBN Technologies to strengthen its<br />
position as complete LiDar solution provider<br />
Infrared NCR launches national critical infrastructure<br />
security and resilience month awareness campaign<br />
3
Salient CRGT awarded $22.6M contract from Department<br />
of Homeland Security to improve border technologies<br />
FAIRFAX, VA – <strong>Oct</strong>ober 12, 2016<br />
- Salient CRGT, Inc., a leading provider<br />
of worldwide training development<br />
and delivery, Agile software<br />
development, data analytics, mobility,<br />
cyber security, and infrastructure<br />
solutions, today announced a<br />
prime contract award from<br />
the Department of Homeland<br />
Security (DHS) Science<br />
and Technology<br />
Directorate (S&T), to<br />
provide development,<br />
integration and evaluation<br />
in support of Borders<br />
& Maritime Research, Integration<br />
and Transition Environments<br />
(BorderRITE). This five-year<br />
effort is valued at approximately<br />
$22.6 million.<br />
The objective of BorderRITE is<br />
to provide two environments that<br />
seamlessly work together to help<br />
secure the Nation’s borders. Salient<br />
CRGT fills the gap between vendor<br />
testing and pilot programs by<br />
development systems and creating<br />
environments to evaluate emerging<br />
technologies and transition them<br />
into operational use. The company<br />
will build and maintain these environments<br />
and help S&T identify<br />
new technologies.<br />
Created by Congress in 2003 with<br />
the formation of the Department of<br />
Homeland Security, S&T is DHS’s<br />
primary research and development<br />
(R&D) arm. S&T manages science<br />
and technology research, from development<br />
through transition, for<br />
the department’s operational<br />
components and the nation’s<br />
first responders.<br />
S&T’s mission is to deliver<br />
effective and innovative<br />
insight, methods<br />
and solutions for<br />
the critical needs of the<br />
Homeland Security Enterprise.<br />
“Our partnership with DHS Science<br />
and Technology Directorate<br />
aligns with our company focus on<br />
innovation,” says Brad Antle, CEO<br />
of Salient CRGT. “Our Innovation<br />
Centers focus on identifying and<br />
testing new technologies to improve<br />
our customers’ efficiency and<br />
threat posture. This effort picks up<br />
where manufacturers’ and vendors’<br />
product testing ends. Evaluating<br />
technologies in a real-world environment<br />
will inform DHS S&T’s<br />
decision making about significant<br />
technology investments and save<br />
the agency time and money.”<br />
4<br />
This award was through Salient<br />
Federal Solutions, Inc., a wholly<br />
owned subsidiary of Salient CRGT.<br />
About Salient CRGT<br />
Salient CRGT provides Agile software<br />
development, data analytics,<br />
mobility, cyber security and infrastructure<br />
solutions. We support<br />
these core capabilities with full lifecycle<br />
IT services and training—to<br />
help our customers meet critical<br />
goals for pivotal missions. We are<br />
purpose built for IT transformation<br />
supporting federal civilian, defense,<br />
homeland, and intelligence agencies,<br />
as well as Fortune 1000 companies.<br />
We use the most innovative<br />
talent delivery model in the industry,<br />
scientifically providing exactly<br />
the right people for the customers’<br />
most pressing requirements. Salient<br />
CRGT has earned a record of success<br />
with integration and operations<br />
of large‐scale, high‐volume solutions.<br />
On September 15, 2015, Salient<br />
and CRGT announced closing<br />
of the merger transactions – visit<br />
newsroom. For additional information<br />
on Salient and CRGT, visit<br />
www.salientcrgt.com
GTT releases most advanced TSP solution to date:<br />
modular, expandable Opticom CVP<br />
ST. PAUL, MN – <strong>Oct</strong>ober 11, 2016<br />
– Global Traffic Technologies announced<br />
today the availability of Opticom<br />
CVP, the company’s next-generation<br />
transit optimization solution.<br />
The Opticom CVP is built with<br />
the same powerful and precise algorithms<br />
used in Opticom hardwarecentric,<br />
GPS-enabled solutions. The<br />
new platform provides softwarebased<br />
Transit Signal Priority (TSP),<br />
schedule adherence, headway management<br />
and other advanced capabilities,<br />
helping to ensure transit vehicles<br />
adhere to their published timetables.<br />
With GTT’s most advanced solution<br />
to date, agencies have the potential to<br />
increase rider satisfaction while dramatically<br />
reducing operating costs.<br />
The platform also adds cloud-based<br />
analytics for more control and insights.<br />
GTT’s president Doug Roberts said<br />
“the new Opticom CVP is a softwarecentric<br />
platform that, combined with<br />
new service and delivery options, is<br />
designed to offer agencies maximum<br />
flexibility with their implementation.<br />
“The solution significantly reduces<br />
implementation time,” Roberts said.<br />
“This allows agencies to increase efficiency<br />
and improve rider satisfaction<br />
faster than conventional solutions.”<br />
The CVP - like other transit solutions<br />
from GTT - provides a compelling<br />
and quick return on investment<br />
for transit agencies by reducing fuel<br />
and labour costs. Opticom TSP solutions<br />
can even have the potential to<br />
reduce fleet requirements.<br />
“The Opticom Connected Vehicle<br />
Platform is designed to empower<br />
transit agencies,” Roberts said.<br />
“Combining GTT’s industry-leading<br />
Opticom TSP with built-in active<br />
schedule and headway management<br />
capabilities, the CVP helps keep transit<br />
services on time and performing<br />
optimally in order to minimize travel<br />
times, increase predictability and improve<br />
on-time metrics.”<br />
In addition to the software-based<br />
TSP, schedule and headway applications,<br />
the Opticom CVP allows transit<br />
managers to monitor and maintain<br />
system performance from a central<br />
location with cloud-based analytics<br />
and reporting. Transit managers can<br />
monitor such key metrics as on-time<br />
performance, and dwell time and<br />
travel time by vehicle or route. Users<br />
can also assess and maintain system<br />
performance and provide updates to<br />
the system from anywhere with Internet<br />
access using Opticom Centralized<br />
Management Software (CMS).<br />
The Opticom CVP is built to expand<br />
as an agency’s needs grow. The<br />
CVP offers multiple interface options<br />
and allows additional applications to<br />
5<br />
be added as needed.<br />
In cities that are already equipped<br />
with Opticom for emergency vehicle<br />
preemption, Opticom CVP can be<br />
easily integrated to include service to<br />
their transit fleets. Opticom CVP is<br />
designed to support all variations of<br />
Opticom TSP, including distributed<br />
variants that use infrared and/or GPS<br />
intersection infrastructure, centralized<br />
architectures, and radio or cellbased<br />
communications, including<br />
DSRC.<br />
The Opticom CVP solution is available<br />
now from authorized GTT dealers.<br />
For more information contact<br />
GTT Sales Support via phone at +1<br />
800-258-4610 select Option 1, email<br />
sales@gtt.com, or visit www.gtt.com/<br />
cvp.<br />
About Global Traffic<br />
Technologies, LLC<br />
GTT, formed in 2007 from 3M’s pioneering<br />
Intelligent Transportation<br />
Systems business, is the manufacturer<br />
of Opticom priority control systems<br />
and CanogaT traffic-sensing systems.<br />
These systems have provided safe and<br />
More on page 46
CASE STUDIES<br />
HID Global helps streamline Bhutan’s driver<br />
license issuance and management system<br />
Road Safety and Transport Authority,<br />
Thimphu, Bhutan<br />
The Road Safety and Transport<br />
Authority of Bhutan (RSTA), the<br />
government agency responsible<br />
for printing and issuing driver’s licenses<br />
sought a more secure and<br />
durable card issuance solution for<br />
the country’s growing population<br />
of road users. Formerly known as<br />
Surface and Transport Authority<br />
(STA), the agency was established<br />
in 1977 and works to provide safe,<br />
reliable and cost-effective transportation<br />
alternatives that support the<br />
socio-economic development of<br />
Bhutan. Among its myriad of private<br />
and commercial motor vehicle<br />
functions, it is responsible for all vehicle<br />
registration and driver license<br />
issuance throughout the country.<br />
The RSTA currently employs approximately<br />
170 civil servants in its<br />
regional and local offices across the<br />
country.<br />
Challenges<br />
In recent years, Bhutan has undergone<br />
significant economic development<br />
and modernization leading<br />
to an increase in a<br />
number of drivers<br />
unable to manage<br />
the high demand<br />
in the issuance of<br />
driver’s licenses, the<br />
existing printing<br />
process was inefficient<br />
and lacked<br />
a streamlined approach<br />
for replacing<br />
printer consumables<br />
needed in order to<br />
meet the demands<br />
of new driver requirements.<br />
Dependent on a system<br />
that required different vendors for<br />
its consumables such as cards and<br />
overlaminates, the RSTA needed<br />
a more efficient printing solution<br />
from a single source that would enable<br />
them to issue a high-volume of<br />
ID cards.<br />
“We needed a more efficient printing<br />
solution without compromising<br />
security, durability and image quality,”<br />
said Tshering Nidup, ICT Officer<br />
at the Road Safety and Transport<br />
Authority.“Before implementing<br />
HID Global’s ID card issuance solution,<br />
we had to work with mul-<br />
6<br />
“The printers were plugged in and they were just ready to go. They<br />
were also incredibly intuitive to use, and we have had no problem<br />
with them through the entire year.”<br />
– Tshering Nidup<br />
ICT Officer, Road Safety and Transport<br />
Authority of Bhutan (RSTA)<br />
tiple vendors to get all the components<br />
needed in order to carry out<br />
the printing of driver’s licenses, but<br />
there were times when it was difficult<br />
to ensure each vendor would<br />
deliver the needed consumable on<br />
time. If any of them had to delay<br />
their delivery to a particular site, we<br />
had to stop printing at that location<br />
creating a large backlog for us.”<br />
Since the driver’s licenses are also<br />
used as citizen identification, it is<br />
critical for the ID card to be highly<br />
secure, resistant to cloning and<br />
counterfeiting. Previously, the li-<br />
More on page 10
HID Global Helps Streamline<br />
Bhutan’s Driver License Issuance<br />
and Management System<br />
Continued from page 6<br />
censes lacked the security features<br />
that prevented them from being<br />
tampered with resulting in an underground<br />
market of fake IDs that<br />
presented a problem for law enforcement.<br />
In addition, the old licenses were<br />
very susceptible to wear and tear<br />
fading after a few years, leaving behind<br />
IDs with only faint images of<br />
personal information that were illegible,<br />
and difficult to be recognized.<br />
Solutions<br />
After RSTA selected Ugen Trading<br />
House (UTH), the local authorized<br />
dealer of HID Global solutions in<br />
Bhutan, the RSTA selected HID<br />
Global’s FARGO® HDP5000 high<br />
definition printers/encoders and<br />
Thinley Dorji, Motor Vehicle Inspector at<br />
RSTA, is one of the officers responsible for the<br />
issuance of drivers’ licenses in Bhutan.<br />
deployed the new system in its offices<br />
last year to manage the driver’s<br />
license issuance process. The RSTA<br />
chose HID Global because it was<br />
looking for a trusted partner who<br />
could provide not only highly secure<br />
products that adhere to international<br />
standards, but also professional<br />
and thorough aftersales<br />
services and support.<br />
The HDP5000 printers/encoders<br />
enabled RSTA to gain access to<br />
state-of-the-art, high-definition and<br />
efficient card printing at a lower total<br />
cost of ownership than the previously<br />
deployed solution.<br />
“Gaining greater efficiency with<br />
the new printers, we had no problems<br />
operating and issuing ID cards<br />
across all of our driver’s license distribution<br />
locations,” said Nidup.<br />
Additionally, the HDP5000 ID<br />
printer and encoder produces crisp,<br />
high-definition images by leveraging<br />
the retransfer print technology.<br />
By printing a reverse image on an<br />
intermediate film, then transferring<br />
the film to the card surface, the<br />
HDP5000 outputs greater image<br />
quality that is long-lasting and more<br />
resistant to wear and tear compared<br />
to those printed directly on the<br />
cards.<br />
The new driver’s licenses also features<br />
a multitude of security features,<br />
supported by the HDP5000<br />
printers. The RTSA achieved this<br />
by utilizing the dual-sided printing<br />
10<br />
feature. By installing the dual lamination<br />
module it enabled them to<br />
quickly and efficiently laminate the<br />
cards on both sides, without flipping,<br />
in one pass.<br />
Benefits<br />
For easy identification, the new<br />
driver’s licenses are issued in three<br />
different colors – white for private<br />
cars, blue for commercial vehicles<br />
such as buses, and green for taxis.<br />
The improved quality of the cards<br />
have received positive feedback by<br />
the citizens of Bhutan, as it provides<br />
a more secure, durable and updated<br />
look. “We now have a lot fewer requests<br />
for replacement cards compared<br />
to last year lessening our work<br />
load and resulting in an added benefit<br />
in annual waste savings,” added<br />
Nidup.<br />
With the new HID Global solution<br />
deployed, the RSTA of Bhutan can<br />
now procure all printer consumables<br />
from a single source for a more efficient<br />
and streamlined resupplying<br />
process. The high throughput rate of<br />
the HDP5000 printers also contributes<br />
to improved efficiency. In the<br />
first few weeks of deployment, the<br />
RSTA cleared its backlog of driver’s<br />
licenses requests. As a result, the department<br />
also reduced its wait times<br />
for the issuance of new and replacement<br />
licenses.<br />
Law enforcement agencies also<br />
More on page 46
<strong>GSN</strong>’s 2016 Homeland Security Awards Program<br />
Now Accepting Entries at:<br />
www.gsnmagazine.com/hsa2016/welcome<br />
The 2016 Government Security News Awards Program, featuring<br />
many new categories in Cybersecurity, Physical Security, Government<br />
Agency Innovations and Mobile Technologies will open for entries on<br />
August 24 and will close for entries on November 15.<br />
In good news for Winners and Finalists, <strong>GSN</strong> will be reinstating its<br />
annual Homeland Security Awards Dinner in Washington, DC in<br />
the first week of December, in a venue to be announced. Longtime<br />
participants in the <strong>GSN</strong> awards programs will recall that previous<br />
<strong>GSN</strong> Awards Dinners have featured top government, military leaders<br />
and respected television commentators such as 4-Star General<br />
Barry McCaffrey (Ret); Fran Townsend, Homeland Security Advisor to<br />
George W. Bush, James Kallstrom, Assistant Director of the FBI and<br />
Admiral Thad Allen (Ret), Commandant of the U.S. Coast Guard<br />
who came out of retirement twice to serve his county, first in<br />
Hurricane Katrina and later in the BP Oil Spill.<br />
The cost of an entry for vendors is $300 per entry, but there is no<br />
charge for government agencies or departments. All Winners<br />
and Finalists receive Awards Emblems, and all Winners receive a<br />
handsome, gold-trimmed plaque describing their winning entries.<br />
All Winners and Finalists will also be invited to participate in the 2016<br />
Digital Yearbook of Awards Winners.<br />
To see photo gallery of previous Awards Dinners:<br />
https://www.flickr.com/photos/44536438@N06/<br />
For information on the Awards Dinner or Sponsorships,<br />
Contact Adrian Courtenay, Managing Partner, at<br />
acourtenay@gsnmagazine.com, (Mobile) 917-696-5782
What was in the World Trade Center chemical<br />
plume created at Ground Zero on “9/11”?<br />
By George Lane,<br />
Emergency Response Technology<br />
Fifteen years later, what exactly residents<br />
and rescue workers were exposed<br />
to remains at least a partial<br />
mystery. The smell cannot be forgotten.<br />
Any smoky mix of burning plastic<br />
can instantly bring back memories<br />
for locals of the aftermath of the collapse<br />
of the two towers of the World<br />
Trade Center on September 11,<br />
2001. 91,000 liters of jet fuel and the<br />
10,000,000 tons of building materials<br />
and contents burning at temperatures<br />
above 1,000 degrees Celsius extended<br />
from lower Manhattan across the East<br />
River into Brooklyn and beyond to<br />
the sea.<br />
The terrorist attacks on the World<br />
Trade Center on September 11, 2001,<br />
exposed thousands of Fire Department<br />
of New York City (FDNY) rescue<br />
workers to dust, leading to substantial<br />
declines in lung function in<br />
the first year. So what exactly was in<br />
that smoke and dust?<br />
The real answer to that question will<br />
never be known as few direct measurements<br />
were taken of the plume<br />
that followed the disintegration of<br />
the two towers into a blizzard of dust,<br />
though air samples were collected in<br />
subsequent weeks and months. Regardless,<br />
the then administrator of the<br />
U.S. Environmental Protection Agency<br />
and former governor of New Jersey<br />
Christie Whitman said on September<br />
13, 2001, “EPA is greatly relieved to<br />
have learned that there appears to be<br />
no significant levels of asbestos dust in<br />
the air in New York City.” She added:<br />
“We will continue to monitor closely.”<br />
And five days later, she announced: “I<br />
am glad to reassure the people of New<br />
York and Washington, D.C., that their<br />
air is safe to breath [sic].” 1<br />
Knowing what was in the dust suggests<br />
what may have caused the ailment<br />
dubbed “World Trade Center<br />
or WTC Cough” by the New England<br />
Journal of Medicine, which doctors at<br />
Mount Sinai Medical Center in New<br />
York estimate afflicted nearly half of<br />
those who worked at the site.<br />
Ultimately, the EPA determined<br />
that the air around “Ground Zero”<br />
was harmless, despite the agency’s<br />
findings concerning levels of asbestos<br />
and dioxin, at least to civilians living<br />
and working in the vicinity, if not the<br />
rescue workers. “Except for inhalation<br />
exposures that may have occurred on<br />
9/11 and a few days afterwards, the<br />
ambient air concentration data suggest<br />
that persons in the general population<br />
were unlikely to suffer short-term or<br />
long-term adverse health effects caused<br />
12<br />
by inhalation exposures,” EPA scientists<br />
wrote in their analysis published<br />
in 2007. 2<br />
“It was such a horrific event,” says<br />
environmental scientist Paul Lioy of<br />
the Environmental and Occupational<br />
Health Sciences Institute in New<br />
Jersey, who was contacted by both<br />
the federal government and the Port<br />
Authority of New York and New Jersey<br />
to collect samples of the pulverized<br />
remains of the Twin Towers in<br />
the days following the attack. “What<br />
was the contribution of the gases [from<br />
combustion]?”<br />
The terrorist attack on the World<br />
Trade Center on September 11, 2001,<br />
now known as “9/11”, and its consequent<br />
collapse killed 2,751 persons,<br />
including 343 rescue workers employed<br />
by the Fire Department of<br />
New York City (FDNY) and exposed<br />
thousands of persons to a dense, persistent<br />
dust cloud of pulverized building<br />
materials and chemical by-products<br />
of combustion or pyrolysis. 3<br />
The FDNY rescue workers who responded<br />
to the World Trade Center<br />
site during the collapse or the subsequent<br />
10-month rescue-and-recovery<br />
operations had substantial loss in pulmonary<br />
function during the first year<br />
after the event, more than 12 times<br />
the annual age-associated rate. The
largest decline was observed among<br />
workers who arrived at the site on<br />
the morning of “9/11”, and there were<br />
larger declines among firefighters<br />
than among emergency medical services<br />
workers. 4<br />
Among non-FDNY rescue workers,<br />
volunteers, and residents of lower<br />
Manhattan who were exposed to<br />
World Trade Center dust, abnormal<br />
results on spirometry, a common office<br />
test used to assess how well your<br />
lungs work by measuring how much<br />
air you inhale, how much you exhale<br />
and how quickly you exhale,<br />
were common and persisted during a<br />
3-year follow-up. However, health records<br />
were not available before “9/11”<br />
to determine the extent of new versus<br />
preexisting abnormalities. 5<br />
During the “9/11” attack on the<br />
WTCs, urban chemical warfare was<br />
introduced to America. Thousands<br />
were hospitalized with a “pulmonary<br />
edema”, an indicator of what became<br />
known as the “WTC Cough”. 6<br />
“FEV1”,” forced expiratory volume” in<br />
1 second, is the volume exhaled during<br />
the first second of a forced expiratory<br />
maneuver started from the level<br />
of total lung capacity. FEV1 was used<br />
to assess airway obstruction, bronchoconstriction,<br />
or bronchodilatation.<br />
7,8<br />
“Ground Zero” smoldered until<br />
December 19, releasing fumes that<br />
researchers collected in air samples.<br />
The debris pile acted like a chemical<br />
factory. It cooked together the components<br />
of the buildings and their<br />
contents, including enormous numbers<br />
of computers, and gave off gases<br />
of toxic metals, acids and organics.<br />
The “WTC Cough” was named by<br />
Dr. David Prezant, medical director<br />
of the New York City Fire Department,<br />
in a September 12, 2002, study<br />
in the New England Journal of Medicine.<br />
He and his colleagues reported<br />
that firefighters who had worked at<br />
the World Trade Center site within<br />
the first three days of September<br />
11 were most likely to display these<br />
symptoms, no doubt from massive<br />
exposure to a variety of toxic chemicals.<br />
Those who required at least four<br />
consecutive weeks of medical leave as<br />
a result of the sickness were diagnosed<br />
with “World Trade Center Cough”.<br />
A 2005 study of 2,812 residents living<br />
near the World Trade Center published<br />
in the Journal Environmen-<br />
13<br />
tal Health Perspectives found that<br />
coughing, wheezing, chest tightness<br />
and shortness of breath were reported<br />
in three to six times greater numbers<br />
among people living within one<br />
mile of the World Trade Center site<br />
than among those who lived more<br />
than five miles away. More recent<br />
studies of patients who have sought<br />
treatment for September 11-related<br />
respiratory illness suggest that years<br />
later, they still have a greater risk for<br />
abnormal lung function.<br />
But it is hard to know what the real<br />
numbers are. Unlike firefighters, who<br />
receive care through the New York<br />
City Fire Department and whose<br />
health status before and after September<br />
11 has been well-documented, the<br />
health of residents and local workers<br />
hasn’t been well-tracked.<br />
The “James L. Zadroga 9/11 Health<br />
& Compensation Act”, signed into law<br />
by President Obama in early 2011,<br />
establishes the “World Trade Center<br />
(WTC) Health Program”. It ensures<br />
that those affected by “9/11” continue<br />
to receive monitoring and treatment<br />
services for “9/11”-related health<br />
problems through at least 2015. The<br />
“WTC Health Program” consists of a<br />
Responder Program (for rescue and<br />
recovery workers, including more<br />
than 15,000 New York City firefighters)<br />
and a Survivor Program (for those<br />
who lived, worked or went to school<br />
in lower Manhattan on “9/11”). Services<br />
also are available for responders<br />
to the Pentagon and Shanksville,
Pennsylvania sites also attacked by<br />
9/11 terrorists. People eligible can receive<br />
services, no matter where they<br />
live now in the U.S. The director of<br />
the National Institute for Occupational<br />
Safety and Health (NIOSH) administers<br />
the “WTC Health Program”,<br />
paid by the federal government and<br />
New York City. 9<br />
I was invited to participate in research<br />
into the chemical origins of<br />
the “WTC Cough” by the Naval Postgraduate<br />
School in 2010. Because<br />
no chemical-specific detectors were<br />
used, I used an indirect forensic science<br />
public policy approach, noting<br />
that almost all victims suffered<br />
from what is known in medicine as<br />
a “pulmonary edema”, characterized<br />
by fluid accumulation in the lungs,<br />
which collects in air sacs. Shortness<br />
of breath is the most common symptom<br />
of “pulmonary edema” and is due<br />
to the failure of the lungs to provide<br />
adequate Oxygen to the body.<br />
I examined the materials of construction<br />
used in World Trade Tower<br />
Centers 1 and 2 (WTCs), completed<br />
in 1973 and using from 200<br />
to 250,000 tons of common plastic,<br />
Polyvinyl chloride (PVC) as insulation<br />
in the WTCs. When the jet fuel<br />
ignited on “9/11”, the PVC was partially<br />
combusted, forming incomplete<br />
product of combustion chemicals,<br />
and creating from 10 to 15,000 tons<br />
of Phosgene within minutes. Phosgene<br />
is used both in industry and as a<br />
battle field weapon.<br />
The effects of exposure to irritants<br />
such as Hydrogen chloride, Phosgene,<br />
and particulates are dependent on the<br />
size of the particle and how readily<br />
the chemical dissolves in water. These<br />
properties determine where in the respiratory<br />
tract the chemical or particle<br />
is deposited and absorbed. Hydrogen<br />
chloride is very soluble therefore<br />
injury occurs in the upper airway as<br />
opposed to Phosgene, which effects<br />
mainly in the lower respiratory tract,<br />
the lungs.<br />
Phosgene is deadly at a concentration<br />
of 2 ppm. It appears as a white<br />
cloud and has a characteristic odor of<br />
sweet, newly mown hay in lower concentrations.<br />
Phosgene has low water<br />
solubility, so has a delayed onset of<br />
action, from 30 minutes to 8 hours. It<br />
readily reaches the respiratory alveoli<br />
and has direct toxic effects, leading to<br />
cellular damage of the alveolar-capillary<br />
membrane and subsequent pulmonary<br />
edema. 10 Alveoli tubes transfer<br />
O2 into and CO2 out of the lungs.<br />
Because there is no systemic absorption,<br />
other organs are not affected. 11<br />
I observed that when Phosgene reacted<br />
on the moisture of the alveoli in<br />
the lungs it formed corrosive Hydrogen<br />
chloride (HCl). Phosgene had reacted<br />
with the moisture of the alveoli<br />
to form corrosive Hydrogen chloride<br />
(HCl), causing “pulmonary edemas”<br />
in both residents and fire fighters.<br />
However, all Phosgene produced by<br />
the incomplete combustion of PVC<br />
was destroyed by the large amounts of<br />
14<br />
water used to fire the numerous fires<br />
at “Ground Zero”, preventing detection<br />
after “9/11”.<br />
To mitigate human exposure to<br />
Phosgene and other hazardous chemicals<br />
when responding to emergencies,<br />
I am designing and deploying<br />
autonomously operated chemical security<br />
networks capable of detecting,<br />
identifying and measuring not only<br />
Phosgene, but many other chemicals<br />
using a passive standoff chemical<br />
sensor using commercially available<br />
Fourier Transform Infrared (FTIR).<br />
Integrated with video surveillance,<br />
the chemical security “Tool<br />
Box” warns emergency responders<br />
of chemical hazards from up to three<br />
miles away in real-time, preventing<br />
firefighters and other emergency responders<br />
from becoming “canaries in<br />
a coal mine”, protecting both public<br />
health and critical infrastructure.<br />
Editor’s Note:<br />
Published reports within a few days<br />
of the 15th anniversary of 9/11 have<br />
indicated that Christine Todd Whitman,<br />
who was the administrator of<br />
the Environmental Protection Agency<br />
at the time of the 9/11 disaster, has<br />
finally apologized after fifteen years<br />
for her claim in the days immediately<br />
after the attacks that the air around<br />
Ground Zero and in lower Manhattan<br />
was safe. The reports also indicated<br />
that Ms Whitman had stated that<br />
More on page 46
Canon U.S.A. and National Crime Prevention Council<br />
collaborate to raise awareness of theft and safety<br />
concerns to counterfeit power accessories<br />
MELVILLE, NY – <strong>Oct</strong>ober 13, 2016<br />
– Canon U.S.A., Inc., a leader in<br />
digital imaging solutions, today announced<br />
its collaboration with the<br />
National Crime Prevention Council<br />
(NCPC) to promote awareness<br />
around the safety risks of using<br />
counterfeit power accessories,<br />
such as batteries, chargers, and<br />
external flashes. The production<br />
and sale of counterfeit<br />
products is an issue that not<br />
only affects the consumer electronics<br />
industry, but can affect<br />
consumer safety as well. The<br />
launch of this collaboration is<br />
scheduled to coincide with Crime<br />
Prevention Month in <strong>Oct</strong>ober, and<br />
will continue through 2017.<br />
Together with Canon U.S.A.,<br />
NCPC will use its resources to provide<br />
educational tools to crime prevention<br />
practitioners, law enforcement<br />
officials, and educators who,<br />
in turn, can use those resources to<br />
teach their communities about the<br />
dangers of purchasing counterfeits.<br />
The awareness campaign will also<br />
include digital messaging directed<br />
to consumers and public service announcements<br />
as well as other videos<br />
featuring McGruff the Crime Dog®.<br />
Counterfeit items are illegal replicas<br />
of real products, designed to<br />
deceive and take advantage of the<br />
superior value of genuine merchandise.<br />
They are produced in a manner<br />
that is increasingly more difficult<br />
for average consumers to identify,<br />
which is why awareness and education<br />
efforts are so important. Furthermore,<br />
counterfeit power accessories<br />
can lead to potentially<br />
dangerous results. They typically<br />
do not contain important safety<br />
technologies and are not tested to<br />
meet industry safety standards. As<br />
a result, they may overheat, smoke,<br />
melt, ignite, or create power surges<br />
and electrical irregularities that may<br />
cause personal injury or property<br />
damage.<br />
15<br />
“The safety of our customers is of<br />
paramount importance,” said Yuichi<br />
Ishizuka, president and COO, Canon<br />
U.S.A., Inc. “We want to make<br />
sure our customers are aware of the<br />
dangers of counterfeit power accessories<br />
so they can avoid potential<br />
risks of hurting themselves<br />
or damaging their equipment.”<br />
“As counterfeiting of camera<br />
accessories continues to<br />
evolve, we want to make consumers<br />
aware of this risk so<br />
they can keep themselves and<br />
their equipment safe,” said<br />
Ann Harkins, president and<br />
CEO, NCPC. “Counterfeit products<br />
designed to look like genuine products<br />
from major camera manufacturers<br />
may cause damage to people<br />
and property.”<br />
NCPC is a private, nonprofit<br />
tax-exempt 501(c)(3) organization<br />
whose primary mission is to be the<br />
nation’s leader in helping people<br />
keep themselves, their families and<br />
their communities safe from crime.<br />
To learn more about the campaign,<br />
please visit www.ncpc.org/<br />
stopfakes.<br />
More on page 47
The Technology of War: Advantages of a<br />
Network-Centric approach to modern warfare<br />
By Barry McElroy<br />
While the reasons we go to war –<br />
land, religion, retribution, resources<br />
– have not changed much over the<br />
millennia, warfare itself has changed<br />
dramatically, especially in recent decades.<br />
No longer is a battle a linear operation<br />
with clearly defined lines and<br />
trained soldiers in uniform firing artillery<br />
at each other, as it was for much<br />
of the 20th century. To fight a war in<br />
the 21st century means fighting an<br />
enemy who is everywhere and nowhere<br />
at the same time, who has not<br />
been trained in battle formations or<br />
military strategy, who does not wear<br />
a uniform or use WoRm formulas to<br />
calculate where to fire.<br />
There are no battle lines – anywhere<br />
in a targeted country is a free<br />
fire zone, and the enemy is constantly<br />
moving and changing where they attack<br />
from. There is no symmetry – a<br />
solitary person can destroy a group of<br />
soldiers and their vehicles using an<br />
improvised explosive device (IED) or<br />
rocket.<br />
Twenty-first century warfare requires<br />
that soldiers are constantly on<br />
their guard and ready to fight – and<br />
this need for always-on preparedness<br />
has changed the way the military<br />
collects and uses intelligence, giving<br />
rise to what’s called “network-centric<br />
warfare”: the use of networked technology<br />
to provide advantages on the<br />
battlefield.<br />
The Benefits of the<br />
Network-Centric Approach<br />
A network-centric approach to warfare<br />
links all military assets to each<br />
other and to decision makers via<br />
computer, radio and data networks,<br />
enhancing the way military objectives<br />
are accomplished because of information<br />
superiority: According to David<br />
S. Alberts, who formerly worked in<br />
the office of the Assistant Secretary<br />
of Defense for Networks and Information<br />
Integration, “A robustly networked<br />
force improves information<br />
sharing. Information sharing and<br />
collaboration enhance the quality of<br />
information and shared situational<br />
awareness. Shared situational awareness<br />
enables self-synchronization.<br />
These, in turn, dramatically increase<br />
mission effectiveness.”<br />
A Department of Defense text adds<br />
that while war will always be characterized<br />
by “fog, friction, complexity<br />
and irrationality,” network-centric<br />
operations provide increased aware-<br />
16<br />
ness and more informed decision<br />
making: “… Having a better near real-time<br />
picture of what is happening<br />
… certainly reduces uncertainty in a<br />
meaningful way.”<br />
This method requires a powerful<br />
communications network, however.<br />
A true military-grade<br />
network must provide<br />
continuous<br />
communication<br />
to in-motion<br />
and stationary<br />
personnel,<br />
vehicles and<br />
equipment, giving<br />
commanders and<br />
troops always-connected,<br />
secure access to applications and<br />
information – thus improving situational<br />
awareness and mission effectiveness.<br />
There is no room for security<br />
breaches or outages of any kind<br />
when it can mean the difference between<br />
life and death, or a war won or<br />
lost.<br />
Communications have sometimes<br />
been a weak link between the various<br />
moving parts of the armed forces,<br />
whether between ground, airborne<br />
and seaborne forces, or between<br />
forces and non-aligned units such as<br />
foreign coalitions or sister services
within the Department of Defense.<br />
However, this has been changing in<br />
recent years as military operations<br />
and projects have begun utilizing a<br />
network called kinetic mesh.<br />
Kinetic Mesh on the Battlefield<br />
A kinetic mesh network combines<br />
wireless network nodes and networking<br />
software. It employs multiple<br />
radio frequencies and any-node-toany-node<br />
capabilities to instantaneously<br />
route data via the best<br />
available traffic path<br />
and frequency,<br />
with up to 300<br />
Mbps transfer<br />
rates.<br />
If a certain<br />
path becomes<br />
unavailable for<br />
any reason – due to<br />
antenna failure, for example<br />
– nodes on the network use<br />
an alternate route to deliver the data,<br />
eliminating any gaps in communication<br />
and allowing on-the-fly transmission<br />
of voice, video and data to<br />
provide situational awareness, despite<br />
conditions that would cripple other<br />
networks. Routes are built automatically,<br />
and are evaluated for quality<br />
and performance for every sent and<br />
received packet.<br />
There is no central control node<br />
and no single points of failure. These<br />
self-healing, peer-to-peer networks<br />
support Wi-Fi, integrate easily with<br />
Ethernet-connected devices and<br />
scale to hundreds of high-bandwidth<br />
nodes – in fact, the more nodes added,<br />
the more pathways are established<br />
and the more resilient a network becomes.<br />
The nodes self-configure, making<br />
it simple to expand the network, and<br />
are built to withstand hostile environments<br />
like battlefields. Each node<br />
serves as singular infrastructure,<br />
which enables everything within the<br />
network to be mobile: wireless nodes<br />
can move, clients can move, network<br />
traffic can move – all in real time and<br />
without manual intervention.<br />
A Kinetic mesh network can be easily<br />
redeployed and expanded in multiple<br />
ways, and still operates with the<br />
same level of reliability, even in the<br />
harshest conditions. It eliminates the<br />
challenges of time-consuming, complicated<br />
deployments in the midst of<br />
battlefield pressures, challenging terrain<br />
and changing operations: All a<br />
soldier has to do is hit a power button<br />
on the radio, and the radio immediately<br />
connects to the network and<br />
is up and running. A soldier doesn’t<br />
need extensive training to learn how<br />
to set up a radio, and a company no<br />
longer needs to lay new cable every<br />
time its headquarters moves, which<br />
requires man-hours and taxpayer<br />
dollars.<br />
Not to be overlooked is the network’s<br />
military-grade level of security<br />
(with some radios certified to<br />
“Secret and Below” interoperability).<br />
Kinetic mesh delivers end-to-end,<br />
17<br />
256-bit encryption. When encrypted<br />
information flows through the mesh<br />
and comes out another node, it stays<br />
encrypted all the way through, and is<br />
not decrypted until it is delivered to<br />
its final destination, ensuring privacy.<br />
At each hop in the network, kinetic<br />
mesh provides a per-hop authentication<br />
for each packet. Metadata also is<br />
encrypted; an attacker cannot analyze<br />
the traffic and see which nodes are<br />
communicating with other devices –<br />
which, in a battlefield situation, could<br />
give away position.<br />
Kinetic Mesh in Action<br />
Kinetic mesh has been a part of several<br />
military programs and projects,<br />
including:<br />
C-RAM: The C-RAM program is a<br />
“system of systems” that primarily<br />
uses radar to detect incoming projectiles<br />
(rockets, artillery and mortars)<br />
fired from hostile forces. An engagement<br />
weapon then attempts to intercept<br />
the projectile and destroy it in<br />
flight before it impacts.<br />
There also is a warning component;<br />
once the radar has determined the<br />
trajectory of the projectile, it can determine<br />
what kind of shell or projectile<br />
it is, as well as estimated point of<br />
impact, to determine the blast radius.<br />
It then can send an alert to the affected<br />
area, instructing all personnel<br />
to seek cover. A soldier has about 10<br />
seconds to find cover before detonation<br />
if the projectile is not intercepted
in flight – which does not sound like<br />
a lot of time, but can mean the difference<br />
between life and death.<br />
The C-RAM program was an important<br />
counter measure to enemy<br />
fire during the wars in Iraq, where the<br />
way the enemy fought made it impossible<br />
for troops to deploy counter fire<br />
– because there was simply no one to<br />
fire at. Instead, the enemy would set<br />
up crude stands with rockets on top<br />
and use a triggering device to deploy<br />
the rockets from afar. It was by no<br />
means a scientific method of warfare,<br />
but it was intermittently effective, killing<br />
or injuring soldiers and disabling<br />
military assets.<br />
For the past five years, kinetic mesh<br />
has provided the communications<br />
link between the radars and the command<br />
center, and the warning towers<br />
and the command center. Before kinetic<br />
mesh radios were implemented,<br />
there was a much higher rate of interference<br />
between the various components<br />
and the radios, creating gaps in<br />
communications. With kinetic mesh<br />
radios, system availability rate has increased<br />
significantly – meaning even<br />
more human lives will be saved in<br />
current and future field operations.<br />
Soldier Link: Soldier Link is a communications<br />
network that connects<br />
all military personnel from the lowest<br />
link – the individual soldier – up<br />
to national command. It is intended<br />
to provide and distribute situational<br />
awareness communications, including<br />
position locator information for<br />
soldiers and vehicles. Kinetic mesh<br />
radios will provide plug-and-play<br />
Ethernet connections with IP-based<br />
devices for company-level and below<br />
soldiers. (Soldier Link has been developed<br />
and is being evaluated and<br />
tested.)<br />
Wolfhound: Wolfhound is a manportable<br />
electronic warfare and cyber<br />
capability supporting kinetic<br />
operations in Operation Enduring<br />
Freedom. The system includes three<br />
networked, man-packable nodes capable<br />
of detecting, identifying and<br />
direction-finding conventional communications.<br />
It targets Very High<br />
Frequency (VHF) or Ultra High Frequency<br />
(UHF), push-to-talk, handheld<br />
radio communications, and is a<br />
counter-IED program.<br />
The use of IEDs is an example of the<br />
unconventional military tactics seen<br />
in the asymmetrical warfare of the<br />
late 20th and early 21st centuries: By<br />
burying artillery shells strategically in<br />
roads and other areas where troops<br />
traveled, an enemy can injure or kill<br />
soldiers and damage military assets<br />
– all without needing to take aim or<br />
even remain in the area.<br />
IEDs were used extensively against<br />
U.S.-led forces in Iraq and were responsible<br />
for nearly 2,000 deaths between<br />
July 2003 and January 2009.<br />
Since Wolfhound’s inception, however,<br />
the program has prevented the<br />
detonation of more than 1,000 wouldbe<br />
IEDs and is expected to save many<br />
more lives in the future.<br />
18<br />
The Need for Real-Time<br />
Communications in Modern Warfare<br />
Technology is constantly changing<br />
everything we do. Ray Kurzweil’s Law<br />
of Accelerating Returns avows that<br />
the rate of change in systems – including<br />
technology – increases exponentially,<br />
not linearly, meaning that<br />
each advance doubles the rate of the<br />
next: “30 steps linearly gets you to 30.<br />
One, two, three, four, step 30, you’re<br />
at 30. With exponential growth, it’s<br />
one, two, four, eight. Step 30, you’re<br />
at a billion.”<br />
If this theory holds true, we will<br />
continue to see lightning-fast technological<br />
progress across every part<br />
of our lives – including the way we<br />
conduct combat operations. As warfare<br />
becomes more unpredictable<br />
and asymmetrical, a network-centric<br />
approach will be ever more critical –<br />
without real-time communications<br />
enabling information superiority, all<br />
the artillery in the world won’t make<br />
a difference. Kinetic mesh networks<br />
provide the mobility, reliability, scalability,<br />
security and high bandwidth<br />
needed to ensure mission-critical intelligence<br />
is sent and received in real<br />
time, breaking new ground in wartime<br />
communications and helping to<br />
save lives.<br />
Barry McElroy is Vice President of Rajant.<br />
He can be reached at bmcelroy@<br />
rajant.com.
International sports competition in Brazil catapulted to a<br />
Gold Standard of Identity Management with Quantum Secure<br />
SAN JOSE, CA – <strong>Oct</strong>ober 12, 2016<br />
– While millions of viewers were<br />
watching races, volleyball, gymnastics,<br />
swimming and a wide range of<br />
sporting achievements, Quantum<br />
Secure, part of HID Global, a worldwide<br />
leader in secure identity solutions,<br />
worked behind the scenes in<br />
Rio, Brazil this past summer to protect<br />
sports venues by verifying the<br />
identity of athletes, staff members,<br />
guests and volunteers. The use of<br />
SAFE Software from Quantum Secure<br />
helped reduce the risk of intrusions<br />
at the sporting events, preventing<br />
potential threats through one of<br />
the world’s most advanced forms of<br />
managing identities at large events.<br />
Quantum Secure’s SAFE software<br />
tracked approximately 500,000<br />
people who had credentials to come<br />
and go from sporting venues across<br />
Rio. Identity had to be<br />
verified nearly three<br />
million times during<br />
the competitions, ensuring<br />
that each badge<br />
could be trusted and<br />
was not a counterfeit.<br />
Approximately a dozen<br />
issues with badges were<br />
identified, including an<br />
incident in which people<br />
tried to falsify badges in order<br />
to enter a basketball game. Using<br />
its analytics engine, SAFE software<br />
recognized the falsified records, and<br />
the response time was virtually instantaneous.<br />
“Recent incidents around the<br />
world have shown that the highest<br />
profile activities, including sporting,<br />
political and entertainment events,<br />
require better protection and smarter<br />
managing of access to buildings,”<br />
said Ajay Jain, President and CEO,<br />
Quantum Secure. “The power of our<br />
new SAFE Sports and Events Access<br />
Manager moves us from reaction to<br />
prevention, with the ultimate goal<br />
of eliminating potential threats before<br />
they happen.”<br />
SAFE Sports and Events Access<br />
Manager features a mobile app<br />
that quickly validates individuals<br />
19<br />
by simply swiping their identity<br />
credentials on handheld peripherals.<br />
Once the credentials are read,<br />
security personnel can perform an<br />
on-site visual confirmation via a<br />
workstation and/or mobile device.<br />
The system can control entrance of<br />
all participants across different venues<br />
or different locations within the<br />
same venue.<br />
“Quantum Secure specializes in<br />
identifying the weak link that could<br />
turn into an inside threat via a fake<br />
ID, and then neutralizing it without<br />
any disruption to the event,” added<br />
Jain. “With years of experience<br />
managing the lifecycle of identities,<br />
we consistently beat threats to the<br />
finish line.”<br />
Like other solutions in the SAFE<br />
portfolio, SAFE Sports and Events<br />
Access Manager focuses on automating<br />
and simplifying<br />
physical identity and access<br />
management, and<br />
identifying and eliminating<br />
potential risk by<br />
amassing and analyzing<br />
actionable intelligence.<br />
Specific capabilities that<br />
enhance its use in high<br />
profile or high secu-<br />
More on page 48
The 2015 ISIS Attacks on Paris:<br />
Assessment and Lessons Learned<br />
By George Lane<br />
The coordinated attacks<br />
in Paris on November 13,<br />
2015 left 130 people dead<br />
and hundreds wounded.<br />
There were nine attackers,<br />
each wearing a suicide<br />
vest. The attackers targeted<br />
a soccer stadium, bars and<br />
restaurants, and a concert<br />
hall, all venues ISIS knew<br />
would be crowded on a Friday evening.<br />
November 13 is now considered<br />
“11/13”, France’s “9/11”. 1<br />
ISIS has designated France as the<br />
European country they hate most.<br />
France has been an enthusiastic participant<br />
in the U.S.-led coalition that<br />
is bombarding Islamic State positions<br />
in Syria and Iraq. ISIS also has<br />
focused on France because it has the<br />
largest Muslim population in Western<br />
Europe and has become Europe’s<br />
biggest source of recruits. 2<br />
In response to the attacks, President<br />
Francois Hollande declared a state of<br />
emergency. France’s borders were<br />
closed and an additional 1,500 troops<br />
were deployed to Paris. The state of<br />
emergency granted security forces<br />
and police the ability to search homes<br />
and place suspects under house arrest<br />
without judicial approval. Within 48<br />
George Lane<br />
hours of the attacks, 168 homes had<br />
been raided and 104 people placed<br />
under house arrest. The<br />
Paris law enforcement<br />
community responded<br />
well to coordinated, simultaneous<br />
attacks. The death<br />
toll likely would have been<br />
much higher if not for several<br />
key decisions made<br />
immediately after the attacks<br />
began. 3<br />
Incident Management Overview: The<br />
lessons learned from assessment of<br />
the Paris attacks focus on six key areas:<br />
(1) intelligence, (2) community<br />
engagement, (3) investigation, (4)<br />
incident command, (5) crisis communication,<br />
and (6) training/equipment.<br />
In each of these areas, findings<br />
specific to the Paris attacks highlight<br />
the challenges and opportunities facing<br />
the French law enforcement and<br />
public safety communities.<br />
Intelligence: The attacks in Paris in<br />
2015 caught authorities off guard for<br />
several reasons. Previously fighters<br />
had relied on a single mode of attack:<br />
a shooting, an explosion, or hostagetaking.<br />
In Paris, the attackers did all<br />
three, overwhelming the country’s<br />
emergency response capabilities. The<br />
20<br />
terrorists employed new tactics, exploited<br />
weaknesses in Europe’s border<br />
controls and demonstrated a desire<br />
for maximum carnage, as opposed to<br />
directing attacks at symbolic targets.<br />
In many ways, the Paris attacks<br />
closely resembled the Mumbai attacks<br />
in 2008, which required “precise<br />
planning, detailed reconnaissance<br />
and thorough preparation, both<br />
physical and mental. It relied on surprise,<br />
creating confusion and overwhelming<br />
the ability of the authorities<br />
to respond.” 4 As in Mumbai, the<br />
Paris attackers had carefully planned,<br />
carried heavy firepower along with<br />
explosives, and divided into teams,<br />
simultaneously attacking different<br />
locations to prevent the authorities<br />
from developing an accurate assessment<br />
of the situation.<br />
The attackers’ goal was mass murder<br />
rather than targeted killings. At<br />
the Bataclan night club, they knew to<br />
kill the security guard first and then<br />
took large numbers of hostages, creating<br />
a siege. This suggests that the<br />
terrorists studied Mumbai and replicated<br />
what worked. While the Paris<br />
attackers were organized into blind<br />
cells, they had extensive logistical<br />
support.<br />
Investigators believe that ISIS terrorists<br />
used the Sony PlayStation 4
game network to avoid detection of<br />
communication before and during the<br />
attacks. The PlayStation 4 Network allows<br />
video game players from across<br />
the globe to virtually meet and talk<br />
with one another. Players can send<br />
text messages or place calls through<br />
the PlayStation network, spelling out<br />
messages to one another within video<br />
games almost impossible to track. 5<br />
However French authorities do<br />
not believe technological intelligence<br />
could have prevented these attacks.<br />
They said that human intelligence is<br />
the most effective form of counterterrorism,<br />
and the best intelligence<br />
comes from community engagement,<br />
not coercion. But gaining the necessary<br />
trust to build human intelligence<br />
sources within the European Muslim<br />
community has proved particularly<br />
difficult for French authorities. 6<br />
Community Engagement: France has<br />
the largest Muslim population in the<br />
European Union. The Pew Center<br />
for Research estimates that 4.8 million<br />
people, or approximately 7.5% of<br />
French residents, are of Muslim descent.<br />
7 By law the French government<br />
is prohibited from asking or keeping<br />
data on its citizens’ race and religion<br />
so exact demographic data is hard<br />
to obtain. France has a complicated<br />
colonial past that leaves many Muslims<br />
today feeling isolated and discriminated.<br />
Many of France’s Muslim<br />
immigrants come from the former<br />
French colonies of Morocco and Algeria.<br />
In the mid-eighteenth century,<br />
France invaded Algeria and began efforts<br />
to convert the indigenous Muslims<br />
to Christianity.<br />
Algeria remained under French colonial<br />
rule for the next century, not<br />
gaining independence until 1962 after<br />
a brutal eight-year war. Hundreds<br />
of thousands died, and nearly one<br />
million refugees fled to France. But<br />
assimilation was difficult, especially<br />
for practicing Muslims who found<br />
France to be openly hostile to their<br />
21<br />
religious beliefs. France is a deeply<br />
secular country. This tension has increased<br />
in recent decades. In 2004,<br />
France banned the wearing of veils,<br />
crosses and yarmulkes in schools. In<br />
2010, France banned public wearing<br />
of a face veil worn by some Muslim<br />
women.<br />
Today many Muslims live in the Parisian<br />
suburbs known as the “banlieues”.<br />
While the word literally means<br />
“suburbs,” it has become a pejorative<br />
term synonymous with poor, immigrant,<br />
crime-ridden areas. France has<br />
717 “sensitive urban zones” in which<br />
unemployment is over twice the national<br />
rate. Over a third live below the<br />
poverty line and the unemployment<br />
rate is near 40% for young Muslim<br />
men. 8 There are direct connections<br />
between youth, unemployment, and a<br />
rise in Sunni extremism.<br />
Investigation: While the style and<br />
ferocity of the November attacks<br />
caught law enforcement off-guard,
the immediate response was largely<br />
successful. Though the French do not<br />
have a traditional National Incident<br />
Management System/Incident Command<br />
System (NIMS/ICS) structure,<br />
the many responding agencies were<br />
able to coordinate quickly and share<br />
information, despite the difficulties of<br />
encrypted communication, multiple<br />
crime scenes and numerous fatalities.<br />
Investigators later found a cell<br />
phone in a trash bin that contained<br />
detailed information about the attack<br />
and a text message saying, “On est<br />
parti en commence.” (Translation: “We<br />
have left, we are starting.”) 9 Authorities<br />
were able to use geolocation services<br />
on the phone to find the attackers last<br />
known location before the assault in<br />
an apartment in the Parisian suburb<br />
of St. Denis. A seven hour shootout<br />
with police ended with explosions<br />
and the deaths of three people.<br />
Despite the chaos and the variety of<br />
crime scenes, French authorities were<br />
able to achieve situational awareness<br />
with a high degree of accuracy in<br />
a short period of time. After the attacks,<br />
the police were criticized for<br />
their inability to locate attackers, especially<br />
because they were hiding a<br />
short distance away in Brussels. The<br />
deep cultural divide likely impeded<br />
cooperation between Muslim communities<br />
and the authorities.<br />
cide vest outside the stadium, President<br />
Hollande, who had been inside<br />
the stadium watching the game, was<br />
rushed to safety. However, concerned<br />
that the attacker’s intent was to create<br />
a stampede out of the stadium with<br />
other attackers lying in wait to ambush<br />
the exit spectators, Hollande decided<br />
not to tell the fans and players<br />
what was going on. 10 The stadium was<br />
quietly locked down and play continued.<br />
Because of the spotty cell reception<br />
inside the stadium, the public remained<br />
largely unaware of the events<br />
that were unfolding outside. At the<br />
same time, police commanders opted<br />
not to flood the area surrounding the<br />
stadium with resources as French authorities<br />
determined that this was a<br />
likely a terrorist attack.<br />
There was much confusion in the<br />
response phase of the crisis. Because<br />
there were three difference crime<br />
22<br />
Incident Command: Two key decisions<br />
made during the first phase of the attacks<br />
at the Stade de France stadium<br />
likely saved hundreds of lives. After<br />
the first attacker detonated his suiscenes,<br />
there were also three separate<br />
command posts that were operating<br />
independently, hindering police attempts<br />
to get accurate information<br />
in real time. France allows the selfdeployment<br />
of officers in an emergency.<br />
Despite good intentions, these<br />
self-deployed officers and their vehicles<br />
created bottlenecks at key locations.<br />
Because resources were not deployed<br />
from a centralized command,<br />
resource management suffered. First<br />
responders had been using their radios<br />
to communicate with the Incident<br />
Command Post. However, Headquarters<br />
took control of the radio communications,<br />
which interfered with the<br />
first responders’ ability to effectively<br />
communicate with each other on<br />
scene.<br />
Crisis Information: Managing crisis<br />
communication and the flow of infor-
mation proved to be one of the most<br />
challenging aspects of the November<br />
13 attacks. First, the emergency information<br />
call system, the French “911”,<br />
was completely overwhelmed. There<br />
were two call centers, each staffed<br />
with forty operators. French authorities<br />
estimated that only one in six<br />
emergency calls was answered. There<br />
were likely many duplicate calls reporting<br />
the same event.<br />
Second, the media in France is<br />
largely unregulated and has unrestricted<br />
access to crime scenes even<br />
as an investigation is unfolding. During<br />
the attacks, French stations aired<br />
live feed of police amassing outside<br />
the market, preparing their attack.<br />
ISIS was able to watch in real time<br />
and gain situational awareness from<br />
these media reports. The media in<br />
France are not credentialed so there<br />
is no way to enforce crime scene perimeters.<br />
Third, the authorities did not effectively<br />
use social media to share<br />
official news updates. The first coordinated<br />
statement and social media<br />
push came the following morning. In<br />
the hours after the attacks, the informational<br />
void increased the sense of<br />
panic throughout the city. 11<br />
Training/Equipment: In the months<br />
following the Paris attacks, no one discounted<br />
the bravery of the responders,<br />
but critics within and outside the<br />
French law enforcement community<br />
questioned if the police are capable<br />
of adequately responding to this new<br />
generation of terror attacks. Simultaneous<br />
attacks with multiple crime<br />
scenes require a nimble response<br />
from a security force trained in both<br />
crisis and counter-terrorism strategies.<br />
But the French police system is<br />
highly centralized.<br />
Community policing, a common<br />
practice in the United States, is not<br />
the norm in France. In most situations,<br />
local officers are trained to wait<br />
for the specialists to arrive. 12 To effectively<br />
manage a terrorist incident, first<br />
responders need appropriate equipment<br />
and training to neutralize or at<br />
least contain the terrorists. However,<br />
French first responders are currently<br />
only trained in crime scene procedures.<br />
They lack counter terrorism<br />
training and do not have adequate<br />
firepower to match up against automatic<br />
weapons. A key lesson learned<br />
is the importance of tactical training<br />
for patrol officers.<br />
Recommendations: The following are<br />
recommendations for Paris law enforcement:<br />
(1) Intelligence:<br />
• Increase efforts to cultivate and leverage<br />
human intelligence sources<br />
• Improve tracking of fighters who<br />
travel abroad for training and return<br />
to France.<br />
(2) Community Engagement:<br />
• Adopt and/or create training programs<br />
to counter violent extremism.<br />
• Develop training programs to<br />
neutralize the radicalization of incarcerated<br />
individuals.<br />
23<br />
(3) Investigation:<br />
• Study past terrorist attacks to<br />
identify lessons learned.<br />
• Create a tracking system to maintain<br />
real-time information on the<br />
status of the victims of a major attack<br />
in the medical system.<br />
• Improve major case management<br />
software with commercially available<br />
products.<br />
• Use real-time data tracking systems<br />
to enhance situational awareness<br />
for incidents involving multiple<br />
attacks.<br />
(4) Incident Command:<br />
• Encourage application of NIMS/<br />
ICS training to all first responders<br />
and first supporters.<br />
• Ensure protocols so that emergency<br />
operation centers can respond to<br />
terrorist attacks.<br />
• Ensure multiple interactive communications<br />
processes are in place<br />
to main situational awareness and<br />
CONOPS.<br />
(5) Crisis Information:<br />
• Review current media protocols,<br />
including media credentialing systems.<br />
• Incorporate social media into crisis<br />
communications.<br />
• Educate the public on how to react<br />
and respond during an active<br />
shooter incident.<br />
(6) Training/Equipment:<br />
• Enhance counter-terrorist training<br />
provided to patrol officers.<br />
Training such as Multiple Assault<br />
More on page 48
Handheld narcotics analyzer can now detect<br />
lethal W-18 opioid drug<br />
TEWKSBURY, MA – <strong>Oct</strong>ober 5,<br />
2016 – Law enforcement agents,<br />
narcotics officers and customs personnel<br />
can now quickly and safely<br />
detect street drug W-18 and other<br />
lethal drugs with the newest library<br />
update for the Thermo Scientific<br />
TruNarc handheld narcotics analyzer.<br />
W-18 is a new designer drugconsidered<br />
to be significantly more<br />
potent than morphine and fentanyl.<br />
As part of its most recent v1.6<br />
software update, the TruNarc analyzer<br />
adds dibutylone, furanyl fentanyl<br />
andU-47700 to its onboard<br />
library, which now includes nearly<br />
300 suspected narcotics and narcotics<br />
precursorsand an additional 80<br />
common cutting agents. TruNarc<br />
helps combat drug abuse by enabling<br />
law enforcement to quickly<br />
identify core drugs of abuse as well<br />
as emerging threats. These include<br />
dangerouspainkillers that have contributed<br />
to the growing opioid epidemic<br />
in the U.S. Last year, TruNarc<br />
addedfentanyl and acetyl fentanyl to<br />
its library.<br />
Dibutylone, known as “booty” or<br />
“beauty,” is a psychedelic drug in the<br />
phenethylamine, amphetamine andcathinone<br />
class. It has been linked<br />
to recent random acts of violence in<br />
Florida, where the Thermo FisherScientific<br />
Reachback Support<br />
team assisted law enforcement<br />
by identifying the dibutylone<br />
(bk-DMBDB HCl). Furanyl fentanyl<br />
and U-47700 are two synthetic<br />
opioids distributed in the<br />
U.S. as recreational drugs.<br />
Fentanyl has been linked to hundreds<br />
of deaths in the U.S. since<br />
2013, a reason the U.S. Drug EnforcementAgency<br />
issued a briefing<br />
in July 2016 stating that the country<br />
is in the midst of a fentanyl crisis.<br />
“The recent case in Florida highlights<br />
the challenges safety and security<br />
professionals face as newer,<br />
deadlier drugs reach the street,” said<br />
Denzil Vaughn, director of marketing,<br />
portable analytical instruments,<br />
Thermo Fisher. “The TruNarc analyzer’s<br />
latest library update is designed<br />
to equip field agents with<br />
updated capabilities to stay ahead<br />
of emerging narcotics threats and<br />
more quickly get drug users the<br />
treatment they need.”<br />
The TruNarc analyzer, which debuted<br />
in 2012, allows law enforcement<br />
personnel to scan a single<br />
sample for multiple narcotics in one<br />
test and receive the results within<br />
seconds. An increasing number of<br />
24<br />
lawenforcement departments are<br />
deploying TruNarc for presumptive<br />
testing, helping to eliminate<br />
the need to carry multiple chemical<br />
tests, reduce drug testing backlogs<br />
and speed prosecution.<br />
The analyzer identifies chemicals<br />
with Raman spectroscopy, a wellestablished<br />
technique. Features and<br />
benefits of the TruNarc analyzer include:<br />
• Point-and-shoot simplicity that<br />
allows users to accurately identify<br />
narcotics on site with a highspecificity,<br />
non-destructive and noncontact<br />
test for most samples;<br />
• Rapid presumptive testing designed<br />
to enable law enforcement to<br />
more expeditiously prosecute cases.<br />
As an example, the Franklin County,<br />
Missouri, Multi-County Narcotics<br />
and Violent Crimes Enforcement<br />
Unit uses TruNarc to gain probable<br />
cause and charge drug offenders.<br />
• Field-based sample screening<br />
More on page 48
FLIR announces identiFINDER R100 personal radiation<br />
detector with integrated Bluetooth smart technology<br />
WILSONVILLE, OR – <strong>Oct</strong>ober 13,<br />
2016 – FLIR Systems, Inc. (NASDAQ:<br />
FLIR) today announced the identiFINDER®<br />
R100 personal<br />
radiation detector, the latest<br />
addition to its industry-leading<br />
identiFINDER<br />
R-Series handheld radiation<br />
security solutions. The<br />
belt-worn R100 integrates<br />
networking capabilities to<br />
safeguard first responders,<br />
law enforcement, and<br />
military and security personnel<br />
by delivering immediate<br />
radiation threat<br />
FLIR identiFINDER R100<br />
alarms and providing<br />
automatically-generated radiation<br />
dose rate reports to offer increased<br />
situational awareness to central command<br />
personnel.<br />
The identiFINDER R100 is the<br />
industry’s first IP67-certified and<br />
American National Standards Institute<br />
(ANSI) drop-test compliant personal<br />
radiation detector. The device<br />
meets the 1.5M drop criteria required<br />
by ANSI N42.32, one of the key performance<br />
standards for alarming<br />
PRDs in Homeland Security. The IP67<br />
rating assures the R100 is protected<br />
against dust and immersion in water<br />
up to 1M depth. The unit features<br />
integrated Bluetooth® Smart wireless<br />
technology which facilitates recording<br />
and sending real-time dose rates<br />
and geotag information via a companion<br />
mobile app.<br />
The R100 joins the industry-leading<br />
identiFINDER<br />
product family in offering<br />
a complete range of radiation<br />
security solutions,<br />
from threat detection to<br />
threat identification. All<br />
identiFINDER models, including<br />
the identiFINDER<br />
R100, share the same fieldproven,<br />
intuitive user interface,<br />
which enables<br />
coordinated emergency<br />
response between law enforcement,<br />
firefighters, and HAZMAT teams using<br />
any identiFINDER product.<br />
“As the only ANSI drop-test -compliant<br />
and IP67-certified personal<br />
radiation detector, the R100 is the<br />
industry’s most rugged personal radiation<br />
detector for first responders,”<br />
said Dennis Barket, Jr., Vice President<br />
and General Manager of FLIR Detection.<br />
“When deployed across teams,<br />
the R100 provides a primary detection<br />
net that protects the frontline<br />
against radiological threats, while the<br />
integrated networking features eliminate<br />
communication blind spots for<br />
central command.”<br />
25<br />
FLIR will showcase the identiFIND-<br />
ER R100 for the first time at the International<br />
Association of Chiefs of Police<br />
(IACP) Show on <strong>Oct</strong>ober 16 – 18<br />
in San Diego, CA, booth #5251. The<br />
identiFINDER R100 will begin shipping<br />
globally in January 2017 with<br />
pricing starting at $1,195. To learn<br />
more about the identiFINDER R100,<br />
visit: http://www.flir.com/r100.<br />
About FLIR Systems<br />
FLIR Systems, Inc. is a world leader<br />
in the design, manufacture, and<br />
marketing of sensor systems that<br />
enhance perception and awareness.<br />
FLIR’s advanced systems and components<br />
are used for a wide variety of<br />
thermal imaging, situational awareness,<br />
and security applications, including<br />
airborne and ground-based<br />
surveillance, condition monitoring,<br />
navigation, recreation, research and<br />
development, manufacturing process<br />
control, search and rescue, drug<br />
interdiction, transportation safety,<br />
border and maritime patrol, environmental<br />
monitoring, and chemical,<br />
biological, radiological, nuclear, and<br />
explosives (CBRNE) threat detection.<br />
For more information, visit FLIR’s web<br />
site at www.FLIR.com.
Cambridge Pixel enhances radar tracking software<br />
to support small target detection<br />
CAMBRIDGE, United Kingdom,<br />
<strong>Oct</strong>ober 12, 2016 – Cambridge Pixel<br />
(www.cambridgepixel.com), an<br />
award-winning supplier of radar display,<br />
tracking and recording subsystems,<br />
has enhanced its popular, fieldproven<br />
SPx radar tracking software<br />
with new modelling algorithms to<br />
support the detection and tracking of<br />
very small targets.<br />
The new Model-based Tracking extensions<br />
allow the operator to create<br />
multiple models that match the signature<br />
of likely small and weak targets<br />
such as a swimmer or crawler, rigid<br />
inflatable boat (RIB), jet ski, helicopter,<br />
small UAV or a motorbike.<br />
The tracker can also be configured<br />
to look for specific scenarios, such<br />
as targets moving towards a sensitive<br />
location or on a specific heading.<br />
Importantly, the tracking software allows<br />
multiple types of target to be acquired<br />
from the same data set.<br />
Richard Warren, Cambridge Pixel’s<br />
director of software said: “Radar sensors<br />
are offering more capabilities to<br />
detect targets of interest, but targets<br />
of interest are getting smaller and<br />
more agile, so advances in software<br />
processing are a key part of the overall<br />
detection solution.<br />
“With our enhanced target tracking<br />
software combining a multi-hypothesis<br />
approach with this multi-model<br />
capability, small and weak targets<br />
can now be detected and tracked<br />
even in cluttered environments. Our<br />
software is highly flexible and can<br />
work with a wide range<br />
of commercial and<br />
military radars to<br />
assist our customers<br />
in providing<br />
effective security<br />
and to combat an increase<br />
in terrorism, smuggling,<br />
piracy and insurgency.”<br />
Cambridge Pixel’s SPx radar tracking<br />
software is designed to operate<br />
with many different radar types and is<br />
already widely deployed in command<br />
and control, maritime navigation, security,<br />
airports and vessel traffic applications.<br />
The software receives radar video<br />
as either radar signals through an acquisition<br />
card, as ASTERIX CAT-240<br />
network data or in one of a number<br />
of radar-specific proprietary formats.<br />
Radar video is processed to attenuate<br />
noise and clutter and then target-like<br />
detections are extracted as plots. The<br />
plots are then correlated to identify<br />
candidate targets for fully automatic<br />
acquisition.<br />
Cambridge Pixel’s SPx radar tracker<br />
is a best-in-class software-based<br />
26<br />
COTS primary radar data extractor<br />
and target tracker that provides target<br />
track identification, heading and<br />
speed. It is fully parameterised, highly<br />
configurable and supports multi-hypothesis<br />
tracking to improve<br />
tracking efficiency<br />
and reduce<br />
nuisance alarms.<br />
Cambridge Pixel’s<br />
SPx radar tracking<br />
software is part of<br />
the company’s world-leading SPx<br />
suite of software libraries and applications<br />
providing highly flexible, readyto-run<br />
software products for radar<br />
scan conversion, visualisation, radar<br />
video distribution, target tracking,<br />
sensor fusion, plot extraction and<br />
clutter processing.<br />
Cambridge Pixel’s technology is<br />
used in naval, air traffic control, vessel<br />
traffic, commercial shipping, security,<br />
surveillance and airborne radar applications.<br />
Its systems have been implemented<br />
in mission critical applications<br />
with companies such as BAE<br />
Systems, Frontier Electronic Systems,<br />
Barco Defence, Blighter Surveillance<br />
Systems, DRS, Exelis, Kelvin Hughes,<br />
Lockheed Martin, Navantia, Navtech<br />
Radar, Raytheon, Saab, Royal Thai<br />
Air Force, Samsung Thales, Sofresud<br />
More on page 49
Vecna attains DoD DIACAP Security Accreditation and<br />
ATO for patient self-service solution<br />
CAMBRIDGE, MA – <strong>Oct</strong>ober 11,<br />
2016– Vecna announced its DIA-<br />
CAP (DoD Information Assurance<br />
Certification and Accreditation<br />
Process) Accreditation and ATO<br />
(Authorization to Operate) issued<br />
by the Department of Defense’s Defense<br />
Health Agency. This latest accreditation<br />
enables DoD customers<br />
to purchase and securely use Vecna’s<br />
patient check-in system on the<br />
DoD network. Vecna’s patient selfservice<br />
solution automates check-in<br />
procedures for medical and dental<br />
clinics, pharmacies, labs, and radiology<br />
centers. Vecna’s system helps<br />
staff to optimize patient flow, reduce<br />
wait times, and increase patient satisfaction.<br />
The system interacts in<br />
real-time with the DoD’s EHR and<br />
Dental Application.<br />
“We are honored to support the<br />
Military Health System,” says Bill<br />
Donnell, Vecna’s VP of Government<br />
Business. “Vecna’s expertise in patient<br />
self-service solutions, combined<br />
with the DoD’s world-class<br />
facilities provide a secure, convenient,<br />
and reliable digital platform<br />
for enhancing patient access to care.<br />
We look forward to showcasing our<br />
very latest capabilities at the upcoming<br />
Joint Federal Pharmacy Seminar<br />
(JFPS) in Washington, DC, <strong>Oct</strong>ober<br />
30 - November 2, 2016.”<br />
Patients use the kiosks to checkin<br />
for scheduled appointments and<br />
unscheduled visits. They can verify<br />
their demographic and insurance<br />
information, respond to satisfaction<br />
surveys, complete forms electronically,<br />
and more.<br />
Staff members use the system to<br />
monitor patient wait times, prioritize<br />
based on individual patient<br />
needs, and manage patient flow in<br />
the facility.<br />
Vecna has deployed and supported<br />
its patient self-service solution<br />
in over 1,000 VA, DoD, and commercial<br />
medical facilities around<br />
the world, including Walter Reed<br />
27<br />
National Military Medical Center.<br />
Vecna’s solution has processed nearly<br />
30 million health care self-service<br />
interactions to date.<br />
About Vecna<br />
Vecna provides innovative healthcare<br />
IT, including patient selfservice,<br />
robotic telepresence and<br />
logistics solutions, to streamline<br />
operations, improve access, reduce<br />
costs, and increase patient satisfaction.<br />
Vecna delivers better technology<br />
to realize a better world for all.<br />
Learn more at www.vecna.com.<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
<strong>GSN</strong> Media Kit<br />
CLICK HERE
Even the Government’s own advisory committee<br />
wants to end family detention<br />
By Lindsay M. Harris<br />
Calls to end the detention of immigrant<br />
children and their mothers<br />
seeking protection in the United<br />
States are not new. What is new is<br />
that the Department of Homeland<br />
Security (DHS) Advisory Committee<br />
on Family Residential Centers, created<br />
by DHS itself, has now added its<br />
voice to the chorus calling for an end<br />
to family detention.<br />
On June 24, 2015, DHS Secretary<br />
Jeh Johnson announced the establishment<br />
of the DHS Committee,<br />
known as the ACFRC (“the Committee”),<br />
which was created to advise<br />
Secretary Johnson and ICE Director<br />
Sarah Saldaña on the family<br />
detention centers. The Committee,<br />
comprised of subject matter experts<br />
with a wide range of expertise, conducted<br />
visits to all three family detention<br />
centers currently operating<br />
in Pennsylvania (Berks County) and<br />
Texas (Dilley and Karnes City) and<br />
spent countless hours analyzing the<br />
practice of family detention prior to<br />
reaching the conclusions outlined in<br />
its lengthy September 30, 2016 draft<br />
report.<br />
DHS tasked the Committee in<br />
March 2016 with developing recommendations<br />
for best practices at family<br />
detention centers, including in the<br />
areas of: education, language, intake<br />
and out-processing procedures, medical<br />
care, and access to legal counsel.<br />
In response to these tasks, the<br />
Committee requested<br />
information and documents<br />
from ICE, some<br />
of which ICE deemed<br />
“beyond the Committee’s<br />
scope.” Nonetheless,<br />
the Committee issued<br />
a thorough and well-researched<br />
draft report last week, demonstrating<br />
their comprehensive understanding<br />
of the problematic elements of family<br />
detention.<br />
Today, by a unanimous vote, the<br />
Committee voted to approve the<br />
report with some additional operational<br />
improvements and procedural<br />
protections for detainees. The report<br />
will be officially submitted to DHS<br />
on <strong>Oct</strong>ober 14, at which time it will<br />
be made publicly available.<br />
First and foremost, the Committee<br />
recommends that DHS adopt a presumption<br />
that “detention is generally<br />
neither appropriate nor necessary<br />
for families” and “never in the best<br />
interest of children.” The Committee<br />
proceeded to issue a series of detailed<br />
recommendations, drawing on the<br />
public documents filed in the ongo-<br />
28<br />
ing Flores litigation, which seeks to<br />
hold the Government accountable to<br />
the commitments it made under the<br />
1997 Flores Settlement that outlines<br />
the required treatment for children<br />
in detention and set a<br />
maximum period of<br />
3-5 days during which<br />
children may be held.<br />
The Committee’s<br />
Report speaks authoritatively<br />
about<br />
ICE’s misguided use of civil detention,<br />
recognizing that management<br />
of family detention centers is currently<br />
“improperly, premised upon<br />
criminal justice models rather than<br />
civil justice requirements or needs.”<br />
Emphasizing that detention cannot<br />
be used to deter migration, to punish,<br />
or to hold people indefinitely, the<br />
Committee highlighted the plight of<br />
the mothers and children detained<br />
in Berks County, PA, some of whom<br />
have now been detained more than a<br />
year. Indeed, this week 17 Senators<br />
wrote to DHS Secretary Johnson,<br />
calling the decision to hold asylumseeking<br />
children and their mothers<br />
at Berks in prolonged detention “unconscionable.”<br />
In making their recommendations,<br />
the Committee relied on various re-<br />
More on page 49
How the Vice Presidential candidates responded to<br />
immigration issues at the debate<br />
By Eric Gibble<br />
During the recent vice presidential<br />
debate, candidates<br />
U.S. Senator Tim Kaine and<br />
Indiana Governor Mike<br />
Pence engaged in a heated<br />
exchange on immigration.<br />
Kaine reiterated his running<br />
mate Hillary Clinton’s stated<br />
policy positions, while<br />
Pence attempted to soften Donald<br />
Trump’s many radical anti-immigrant<br />
statements.<br />
Debate moderator Elaine Quijano<br />
turned to immigration by noting that<br />
Trump has made repeated remarks<br />
that immigrants are dangerous – although<br />
the facts show that immigrants<br />
are less likely to be criminals<br />
and immigration is associated with<br />
lower crime rates and safer communities.<br />
She asked Pence, “what would<br />
you tell the millions of undocumented<br />
immigrants who have not committed<br />
violent crimes?”<br />
Pence, like Trump, favors an enforcement-first<br />
approach to immigration<br />
reform. He stated that their<br />
first order of business would be to begin<br />
deportations to “make our country<br />
safer, then, we will deal with those<br />
that remain.” Later, Pence elaborated<br />
that immigration reform “begins<br />
Photos Courtesy of Gage Skidmore and iprimages<br />
with border security” and that they<br />
would go beyond building a massive<br />
border wall, which experts have noted<br />
would be economically devastating,<br />
and secure the border “beneath<br />
the ground and in the air.”<br />
However, this enforcement-first<br />
policy has already been the law of the<br />
land for decades. Since the last major<br />
overhaul of the U.S. immigration<br />
system in 1986, the federal government<br />
has spent an estimated $186.8<br />
billion on immigration enforcement.<br />
Meanwhile border apprehensions,<br />
the most commonly used metric to<br />
look at the flow of undocumented<br />
immigrants crossing the border, are<br />
at 40 year lows. Under the Obama<br />
administration alone, more than 2.5<br />
million immigrants have already<br />
been deported.<br />
Additionally, Pence said that millions<br />
of Americans “believe that we<br />
29<br />
can end illegal immigration<br />
once and for all.” Yet the reality<br />
is most of the American<br />
public remains committed<br />
to practical immigration solutions.<br />
72 percent of Americans<br />
say undocumented<br />
immigrants currently living<br />
in the United States should<br />
be allowed to stay.<br />
When Kaine addressed<br />
immigration measures, he focused<br />
instead on the importance of keeping<br />
families together and a path to citizenship:<br />
“I want a bipartisan reform that<br />
will keep families together; second,<br />
that will help focus enforcement efforts<br />
on those were violent; third,<br />
that will do more border control; and<br />
fourth, write a path to citizenship for<br />
those who play by the rules and take<br />
criminal background checks.”<br />
As the topic turned to refugees,<br />
Kaine underscored that a Clinton<br />
administration “will do immigration<br />
enforcement and vet refugees<br />
based on whether they are dangerous<br />
or not, not discriminating based on<br />
which country you are from.” He did<br />
not elaborate on whether any changes<br />
would be made to how refugees<br />
are currently vetted, given the United<br />
States already has robust systems in
place to ensure the safety and security<br />
of our nation.<br />
Pence, however, did not disavow<br />
the discriminatory ban on Muslim<br />
immigration proposed by Trump.<br />
His campaign has called “for a total<br />
and complete shutdown of Muslims<br />
entering the United States until our<br />
country’s representatives can figure<br />
out what is going on.”<br />
The debate showed a clear distinction<br />
between the two campaigns,<br />
one that endeavors to balance the<br />
dignity of immigrants and their<br />
families alongside the need to secure<br />
our country. The other seeks to<br />
continue and expand upon today’s<br />
failed enforcement-only policies that<br />
leave many communities living in the<br />
shadows of society.<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
<strong>GSN</strong> Media Kit<br />
CLICK HERE<br />
Class action lawsuit challenging failure of<br />
CBP to respond to Freedom of Information<br />
requests is dismissed following settlement<br />
Washington, D.C. - This week,<br />
in accordance with a settlement<br />
reached by the parties, a federal district<br />
court dismissed a class action<br />
lawsuit which challenged U.S. Customs<br />
and Border Protection’s (CBP)<br />
nationwide practice of failing to<br />
timely respond to requests for case<br />
information under the Freedom of<br />
Information Act (FOIA). The suit<br />
was filed in 2015 by five immigration<br />
attorneys and 13 noncitizens,<br />
all of whom had filed FOIA requests<br />
that had been pending between 7<br />
and 24 months—significantly longer<br />
than the 20-business day period<br />
set by law for an agency to respond<br />
to a FOIA request. At the time of filing,<br />
CBP had a staggering backlog<br />
of over 30,000 FOIA requests that<br />
had been pending for more than 20<br />
business days, many for months or<br />
years. During the course of the lawsuit,<br />
CBP implemented new procedures<br />
for handling FOIA requests<br />
and devoted additional staff. Conse-<br />
30<br />
quently, at the time of the settlement,<br />
CBP’s backlog had been reduced to<br />
approximately 3,000 FOIA requests,<br />
most of which were complex, and<br />
CBP generally was responding to<br />
new requests within 20 days.<br />
In the settlement, CBP committed<br />
to continuing its efforts to<br />
timely process FOIA requests. Additionally,<br />
the agency committed<br />
to increased transparency about its<br />
performance; CBP will now post<br />
monthly FOIA statistics to its website,<br />
including the total number of<br />
FOIA requests pending, how long<br />
they have been pending, how many<br />
new requests are received each<br />
month, and how many are processed.<br />
The Law Office of Stacy Tolchin,<br />
the National Immigration Project of<br />
the National Lawyers Guild, Northwest<br />
Immigrant Rights Project, and<br />
the American Immigration Council<br />
represented the plaintiffs.
<strong>GSN</strong>’s 2016 Homeland Security Awards Program<br />
Now Accepting Entries at:<br />
www.gsnmagazine.com/hsa2016/welcome<br />
The 2016 Government Security News Awards Program, featuring<br />
many new categories in Cybersecurity, Physical Security, Government<br />
Agency Innovations and Mobile Technologies will open for entries on<br />
August 24 and will close for entries on November 15.<br />
In good news for Winners and Finalists, <strong>GSN</strong> will be reinstating its<br />
annual Homeland Security Awards Dinner in Washington, DC in<br />
the first week of December, in a venue to be announced. Longtime<br />
participants in the <strong>GSN</strong> awards programs will recall that previous<br />
<strong>GSN</strong> Awards Dinners have featured top government, military leaders<br />
and respected television commentators such as 4-Star General<br />
Barry McCaffrey (Ret); Fran Townsend, Homeland Security Advisor to<br />
George W. Bush, James Kallstrom, Assistant Director of the FBI and<br />
Admiral Thad Allen (Ret), Commandant of the U.S. Coast Guard<br />
who came out of retirement twice to serve his county, first in<br />
Hurricane Katrina and later in the BP Oil Spill.<br />
The cost of an entry for vendors is $300 per entry, but there is no<br />
charge for government agencies or departments. All Winners<br />
and Finalists receive Awards Emblems, and all Winners receive a<br />
handsome, gold-trimmed plaque describing their winning entries.<br />
All Winners and Finalists will also be invited to participate in the 2016<br />
Digital Yearbook of Awards Winners.<br />
To see photo gallery of previous Awards Dinners:<br />
https://www.flickr.com/photos/44536438@N06/<br />
For information on the Awards Dinner or Sponsorships,<br />
Contact Adrian Courtenay, Managing Partner, at<br />
acourtenay@gsnmagazine.com, (Mobile) 917-696-5782
International Threat/Cyber Intelligence<br />
Chuck Brooks on Cybersecurity: The weakest link<br />
who talks about where we stand in what many pe<br />
by Larry Karisny<br />
If you’re in the cybersecurity business,<br />
you know the name Chuck<br />
Brooks.<br />
He is an advisor to the Bill and<br />
Melinda Gates Foundation Technology<br />
Partner Network, chairman of<br />
CompTIA’s New and Emerging Tech<br />
Committee, subject matter expert to<br />
the Homeland Defense and Security<br />
Information Analysis Center, “passcode<br />
influencer” for The Christian<br />
Science Monitor, on the Board of<br />
Advisors for CyberTech, and on the<br />
Board of Directors at Bravatek and<br />
the Cyber Resilience Institute.<br />
Brooks also has authored numerous<br />
articles focusing on cybersecurity,<br />
homeland security and technology<br />
innovation for such publications<br />
as Forbes, Huffington Post, InformationWeek,<br />
MIT Sloan Blog, Computerworld,<br />
Federal Times, NextGov,<br />
Government Security News, Cygnus<br />
Security Media, Homeland Security<br />
Today, The Hill and Government Executive.<br />
I recently got a chance to get<br />
Brooks’ take on where we are today<br />
in what many people call the “wild,<br />
wild west” of cybersecurity. Here are<br />
his thoughts.<br />
Q. You wear many hats and certainly<br />
have been focused on cybersecurity<br />
for some time now. So tell me, who is<br />
Chuck Brooks and what is he trying<br />
to accomplish this space?<br />
A. You are right, over my career in<br />
government, corporate and academia,<br />
I have worn many hats. There<br />
have been some strong common<br />
threads [of] science, technology, national<br />
security, and legislative and executive<br />
policy in all my various roles.<br />
32<br />
Chuck Brooks, Cybersecurity Expert<br />
Thankfully, I selected a professional<br />
vocation of government relations<br />
and marketing that encompasses all<br />
those threads.<br />
My passion for cybersecurity issues<br />
was first established over a decade<br />
ago during the time I spent at<br />
the Department of Homeland Security’s<br />
Science and Technology Directorate.<br />
Back then, the threats to<br />
our critical infrastructure were not<br />
as pronounced as they are today. Of<br />
course we were just beginning to<br />
experience the smartphone era. The
will always be the human element, says Chuck,<br />
ople call the “wild, wild west” of cybersecurity<br />
field of cybersecurity has evolved<br />
exponentially along with the technologies,<br />
networks and connectivity<br />
that make up the cyber ecosystem.<br />
And the ecosystem is quite diverse<br />
and expansive, comprising software,<br />
hardware, monitoring, forensics,<br />
governance and more. All these elements<br />
make it an exciting area to<br />
explore since there is always more to<br />
learn from strategy and technology<br />
perspectives. Also, it certainly blends<br />
my common career threads.<br />
For anyone’s career focus, studying<br />
cybersecurity makes [sense] since<br />
it touches everything work- or personal-related.<br />
In both the public and<br />
private sectors — just about every<br />
CIO survey — cybersecurity is the<br />
top concern. And of course, along<br />
with data analytics, cybersecurity is<br />
a annually a budget priority of federal<br />
spending. DHS Secretary Jeh<br />
Johnson recently described cybersecurity<br />
and counterterrorism as the<br />
two top priorities for the protecting<br />
the homeland.<br />
What I want to accomplish in this<br />
space is to continue being a subject<br />
matter expert in cybersecurity; I enjoy<br />
writing and speaking about the<br />
varied aspects of the topic and especially<br />
in educating others on how it<br />
can impact their lives. My advisory<br />
and board director roles with organizations<br />
are a reflection of that interest.<br />
When I retire (which is a long<br />
way off), I hope to join academia<br />
again in a part-time role. I spent<br />
two years at Johns Hopkins University<br />
SAIS [School of Advanced International<br />
Studies] teaching graduate<br />
students homeland security and<br />
found it very fulfilling.<br />
Q. You have one of the most active<br />
groups in LinkedIn under the heading<br />
of the Department of Homeland<br />
Security. How has this helped both<br />
yourself and DHS in feeling the pulse<br />
of the cybersecurity industry?<br />
A. I do operate a half dozen groups<br />
that focus on homeland security and<br />
information security on LinkedIn,<br />
including a few of the largest groups:<br />
“U.S. Department of Homeland Security,<br />
DHS” “Information Technology<br />
(Homeland & National Security)”<br />
and “Homeland Security.”<br />
In all, these groups include about<br />
60,000 people. Among the members<br />
are a host of well-known cybersecurity<br />
professionals who often post and<br />
comment on issues of the day. Also,<br />
33<br />
as any news on data breaches or cyberincidents<br />
occur, they are often<br />
posted in the LinkedIn groups.<br />
Moderating these groups certainly<br />
keeps me updated and in tune with<br />
the pulse of policy. It has also served<br />
as a great networking venue to share<br />
ideas and information with some<br />
of the best security minds around<br />
in both the private and federal sectors.<br />
Many senior-level executives in<br />
the federal government are on social<br />
sites such as LinkedIn, GovLoop,<br />
Facebook and Twitter. There are an<br />
estimated 1.5 million federal government<br />
employees who regularly<br />
use LinkedIn, including over 65,000<br />
from DHS. Because of the growing<br />
need for public/private-sector collaboration<br />
and interface, being actively<br />
involved in social media makes<br />
a lot of sense.<br />
Q. What is Sutherland Government<br />
Relations and what do you do for the<br />
company?<br />
A. Sutherland Global Services is a<br />
global provider of business processing<br />
services, contact centers, IT<br />
service desks and management consulting<br />
serving government and U.S.<br />
leading corporations across multiple
International Threat/Cyber Intelligence<br />
industries, including health care and<br />
insurance, technology, mortgage<br />
and loan services, finance and banking,<br />
retail, and travel. Sutherland has<br />
36,000 employees and annual revenues<br />
of over $1.2 billion, [and] was<br />
listed in 2015 as one of the fastest<br />
growing private companies in America<br />
by Inc.<br />
I work for the recently created<br />
Sutherland Government Solutions<br />
as VP of Government Relations and<br />
Marketing, where we are at several<br />
agencies and are known for integrated<br />
services for citizen service<br />
needs and digital government. Our<br />
cybersecurity operations at Sutherland<br />
Government Services are internal,<br />
but we do have a practice in<br />
customer relations management after<br />
a company or agency has been<br />
breached. Our cybersecurity practice<br />
is led by Glenn Schoonover who has<br />
a deep technical background. He is a<br />
former chief information security officer<br />
for the Army and was responsible<br />
for providing network security to<br />
the Department of the Army headquarters.<br />
He is also a former senior<br />
technology strategist for Worldwide<br />
National Security and Public Safety<br />
at Microsoft.<br />
Q. I see you are active in both the<br />
public and private sectors when it<br />
comes to cybersecurity. What are the<br />
similarities and differences between<br />
these two sectors?<br />
A. The biggest difference is that government<br />
is motivated by mission,<br />
and the private sector (for the most<br />
part) is driven by profit and loss.<br />
The R&D efforts, innovation sector<br />
and skilled technical expertise in<br />
the private sector has been more robust<br />
than in government. Industry is<br />
more agile and able to react to threat<br />
trends.<br />
On the federal side, the landscape<br />
has really changed over the past<br />
few years. [The U.S. Department<br />
of Defense], of course, has had the<br />
cybersecurity war-fighting mission<br />
and continues to build upon new<br />
requirements for operations and for<br />
systems. On the civilian side, DHS<br />
takes an increasingly larger role in<br />
cybersecurity. Presidential and congressional<br />
directives have mandated<br />
that DHS play a growing and more<br />
primary role, especially with protecting<br />
critical infrastructure (transportation,<br />
health, energy, finance) that<br />
is mostly owned by the private sector.<br />
DHS has to step up its activities<br />
in assessing situational awareness,<br />
information sharing, and resilience<br />
research and development plans<br />
with stakeholders. This has led to a<br />
trend in public-private partnering<br />
for sharing threat information and<br />
in creating standards and protocols.<br />
In both the public and private sectors,<br />
training of the next-generation<br />
cybersecurity technical and policy<br />
[subject matter experts] is a major<br />
34<br />
priority.<br />
Q. To date, there seems to be a standoff<br />
between Apple and the federal<br />
government when it comes to iPhone<br />
security. What are your thoughts on<br />
this, and can this bring about some<br />
lessons learned for the cybersecurity<br />
industry?<br />
A. This is the topic of the day, and it<br />
is a complicated issue relating to government<br />
requesting a corporation to<br />
provide software to allow access to<br />
data. My thoughts may be a bit different<br />
from some of the others in the<br />
industry. While I recognize the importance<br />
of privacy and the dire risk<br />
of an Orwellian surveillance state, I<br />
consider protecting innocent lives<br />
as a mitigating circumstance. What<br />
if that data that the FBI is seeking<br />
on the terrorist’s encrypted phone<br />
uncovers a deeper terrorist network<br />
planning more horrific acts? In my<br />
opinion, this is a mitigating circumstance.<br />
What should be done is to establish<br />
protocols between industry and law<br />
enforcement to cooperate in these<br />
type of instances (with proper warrants<br />
and assurances) so that company<br />
Internet protocol can be isolated<br />
and privacy issues for the company’s<br />
customers can be best addressed. I<br />
am quite sure Congress will be looking<br />
closely at this case to establish<br />
legislation to create a working formula.<br />
The lesson for cybersecurity is
that there is a balance between privacy<br />
and security that has to be constantly<br />
reviewed in accordance with<br />
the threats at hand.<br />
Q. With billions of Inernet of Things<br />
devices on the near horizon<br />
and zetabytes of data projected<br />
by 2020, can we secure<br />
and control our digital<br />
processes, or are we<br />
headed for a digital train<br />
wreck?<br />
A. According to Gartner, there<br />
will be nearly 26 billion networked<br />
devices on the Internet of Things<br />
(IoT) by 2020. Moreover, it will keep<br />
expanding as the cost of sensors decreases<br />
and processing power and<br />
bandwidth continue to increase. The<br />
fact is that most of these IT networks<br />
will have some sort of an IoT-based<br />
security breach. We could be headed<br />
for a digital train wreck if IoT security<br />
standards are not adopted. We<br />
may have a digital train wreck even<br />
if they are adopted. Standards will<br />
have to be developed industry by<br />
industry. Protecting a network of<br />
medical devices in a hospital will require<br />
different sets of standards than<br />
protecting utilities with SCADA [supervisory<br />
control and data acquisition]<br />
systems that make up the electric<br />
grid. There are a lot of questions,<br />
including who enforces compliance?<br />
And what are the liabilities of an IoT<br />
breach?<br />
The real danger is that the Internet<br />
was not built for security at its<br />
inception; it was built for connectivity.<br />
There is some truth to the notion<br />
that your network may someday be<br />
betrayed by your toaster or refrigerator.<br />
One thing is for sure:<br />
the Internet of Things will<br />
pose many challenges to<br />
cybersecurity and data<br />
analytics, much of which<br />
we have yet to contemplate.<br />
Q. You’ve had the opportunity to<br />
review many cyberdefense technologies.<br />
Are we really finding new solutions<br />
that can handle this explosion<br />
of digital processes, or are we still<br />
playing the game of catch-up and<br />
patch-and-pray cybersecurity?<br />
A. New solutions are continually<br />
evolving with threats, but there will<br />
always be a need for better encryption,<br />
biometrics, analytics and automated<br />
network security to protect<br />
networks and endpoints. It is<br />
a perpetual game of cat and mouse<br />
between hackers and protectors, and<br />
there is really no such thing as being<br />
invulnerable.<br />
In a sense, we are continually playing<br />
catch-up and reacting to the last<br />
incident with patches. The weakest<br />
link will always be the human element.<br />
However, there are many new<br />
interesting technologies that could<br />
significantly impact cybersecurity in<br />
35<br />
the near future. There are technologies<br />
and algorithms coming out of<br />
the national labs, government, and<br />
from private-sector R&D and startups<br />
that have the potential to be disruptive.<br />
Q. Any final comments? And are<br />
there any speaking engagements or<br />
events you are participating in that<br />
you would like to announce? Could<br />
you also offer a good source for information<br />
on the subject of cybersecurity<br />
that you would suggest for our<br />
readers?<br />
A. Please check my regular posts in<br />
the media and social media, join<br />
my LinkedIn groups and follow me<br />
on Twitter @ChuckDBrooks. I do<br />
have some future blogs with the National<br />
Cybersecurity Institute on my<br />
agenda. Also, in addition to social<br />
media, which I highly recommend,<br />
there are many excellent outlets for<br />
cybersecurity information including<br />
the Homeland Defense and Security<br />
Information Analysis Center. A great<br />
site that aggregated cybersecurity<br />
news daily is The CyberWire.<br />
Larry Karisny is the director of<br />
Project Safety.org, an advisor, consultant,<br />
speaker and writer supporting<br />
advanced cybersecurity technologies<br />
in both the public and private sectors.<br />
Reprinted with permission of authors.
International Threat/Cyber Intelligence<br />
Arrest of ex-NSA contractor shows federal<br />
cybersecurity still faces a serious inside threat<br />
By Steve Bittenbender<br />
The latest arrest of a government<br />
contractor charged with stealing<br />
documents and illegally downloading<br />
and retaining classified data indicates<br />
that the threat of an inside<br />
attack on data remains real and, in<br />
many cases, exposes an Achilles’<br />
heel for U.S. cybersecurity efforts.<br />
Court documents released earlier<br />
this week show the Federal Bureau<br />
of Investigation arrested Harold<br />
T. Martin III at his Maryland residence<br />
in late August. In searching<br />
his house and car, investigators<br />
found numerous documents – both<br />
in hard-copy and digital formats –<br />
marked as highly classified that contained<br />
sensitive information vital to<br />
national security.<br />
In at least six cases, the documents<br />
date back to 2014.<br />
Martin worked for Booz Allen<br />
Hamilton, which performs work<br />
for several agencies involved with<br />
federal security and defense. Most<br />
recently, he was working within the<br />
Department of Defense, but documents<br />
found date back to at least<br />
2014. At that time, Martin was a<br />
Booz contractor holding cleared position<br />
within the National Security<br />
Agency.<br />
“The disclosure of the documents<br />
would reveal those sensitive sources,<br />
methods, and capabilities,” said<br />
F.B.I. Special Agent Jeremy Bucalo<br />
in an affidavit filed with Martin’s<br />
criminal complaint.<br />
The NSA monitors and collects<br />
information regarding foreign intelligence<br />
matters. It’s also responsible<br />
for securing federal communications<br />
and computer networks. Booz<br />
Allen Hamilton is the same firm<br />
that employed Edward Snowden,<br />
who released without authorization<br />
classified NSA material three years<br />
ago.<br />
Most of the attention placed on<br />
cybersecurity focuses<br />
on efforts to stop<br />
hackers trying to penetrate<br />
systems from<br />
abroad. However, a<br />
survey conducted by<br />
cybersecurity software<br />
provider Imperva<br />
revealed that 1<br />
in 50 employees (or 2<br />
percent of the work-<br />
36<br />
force) can be considered a threat for<br />
an inside breach.<br />
In addition, 36 percent of companies<br />
surveyed said insider incidents<br />
took place on their systems within<br />
the past year.<br />
“The insider threat is real and<br />
reinforces the fact that the biggest<br />
threat to enterprise security is the<br />
people already on the payroll,” said<br />
Terry Ray, a chief strategist for Imperva.<br />
“The unfortunate reality is<br />
that insiders can do far more damage<br />
than external attackers because<br />
they have legitimate access and vast<br />
opportunity.”<br />
Amichai Shulman, Imperva’s chief<br />
technology officer, said current cybersecurity<br />
solutions target malware<br />
and other tools used by hackers.<br />
Those solutions do<br />
not work properly and<br />
because of that expose<br />
government and other<br />
vital systems to substantial<br />
risk.<br />
Solutions must be<br />
focused on protecting<br />
the target of the<br />
attack, the data, Shul-<br />
More on page 49
Intelligent Automation Inc discusses cyber attacks<br />
and tools of analysis and mitigation<br />
Cyber security is a critical issue as<br />
networks are consistently attacked<br />
and compromised. Due to the evergrowing<br />
dependency on computer<br />
systems and networks for<br />
business transactions, systems<br />
face growing cyber threats<br />
from both inside and outside.<br />
IAI has in-depth knowledge,<br />
advanced technology and extensive<br />
hands-on experience<br />
in providing cyber-attack<br />
analysis and mitigation strategies<br />
and solutions. IAI is focused on<br />
cyber defense through prevention,<br />
attack detection and mitigation, and<br />
reliability and trustworthiness.<br />
Examples of IAI’s cyber attack<br />
analysis and<br />
mitigation solutions include:<br />
Self-shielding Dynamic Network<br />
Architecture (SDNA) changes the<br />
nature of the network by introducing<br />
cryptographically strong<br />
dynamics. SDNA provides an<br />
IPv6-based integrated security architecture<br />
allowing multiple types<br />
of dynamics to be constructively<br />
combined. Various network-level<br />
dynamics like addressing, naming,<br />
routing, availability, etc. are incorporated<br />
into SDNA’s design. SDNA’s<br />
dynamics operate before, during,<br />
and after an attack and place the<br />
burden on the attacker, creating an<br />
environment where the network is<br />
secured by default. This approach<br />
significantly reduces the reliance on<br />
detection to defend against attacks.<br />
NIRVANA is cyber situational<br />
awareness tool that leverages efficient<br />
graphical models and inference/analysis<br />
algorithms to assist<br />
system administrators in enterprise<br />
network security analysis and dynamic<br />
situation awareness. We decouple<br />
the abstract knowledge from<br />
the particular network information<br />
like topology settings, roll out the<br />
instance network attack graph as<br />
needed, use efficient matching algorithms<br />
for situation awareness,<br />
37<br />
and apply inference algorithms under<br />
uncertainty to facilitate what-if<br />
analysis and action planning. IAI’s<br />
graphical models capture the inherence<br />
dependency relationships<br />
of applications on<br />
networks/systems, and of<br />
missions on applications. Our<br />
method enables independent<br />
graphic model development at<br />
different levels while ensuring<br />
interoperability.<br />
NetBEAM is an integrated<br />
tool for enterprise network monitoring<br />
and cyber behavior anomaly<br />
detection based upon the unique<br />
features and characteristics of typical<br />
cyber threats.<br />
JANASSURE is an automated<br />
network mapping tool to detect the<br />
existence of IPv6 transition mechanisms<br />
and evaluate the potential risk<br />
caused by IPv6 transition mechanisms<br />
in networks.<br />
Smart AppShield is a virtualization-based<br />
approach to application<br />
protection which employs an outof-the-box<br />
approach to monitor the<br />
information flow among applications<br />
and enforce the security polic-<br />
More on page 50
Convy on Net-Centric Security<br />
The future of identity management –<br />
on the tips of your fingers<br />
By John Convy, Convy Associates, Washington, DC<br />
Identity management remains an ongoing<br />
challenge for the security industry.<br />
Any number of technologies promise<br />
quick, easy access for authorized<br />
individuals, including card keys, biometric<br />
scans, facial recognition, and<br />
voice recognition. However, issues<br />
with accuracy, false positives, and<br />
false negatives continue to frustrate<br />
security people.<br />
One of the world’s oldest identity<br />
management methods, ironically,<br />
may still be the best. This uses something<br />
each of us carries with us everywhere,<br />
and is almost perfectly unique<br />
to every individual – our fingerprints.<br />
Forensic Science in Literature<br />
Sir Arthur Conan Doyle popularized<br />
fingerprint use as a forensic tool in a<br />
Sherlock Holmes story published in<br />
1890. The first documented application<br />
of fingerprint technology came<br />
from an Argentine police official<br />
around 1892.<br />
Soon after that, fingerprints became<br />
the backbone of many police<br />
operations. Analog images can be<br />
printed and shared easily. Scans can<br />
be turned into digital codes that serve<br />
as unique identifiers that can operate<br />
as both a user ID and password. This<br />
application of biometrics – the use<br />
of physical characteristics for digital<br />
authentication – has been one of the<br />
key goals for the security industry for<br />
many years.<br />
Older fingerprint scanner technologies<br />
had their limitations. They<br />
could not record sufficient information<br />
from a finger to be reliable or<br />
generate a sufficiently sophisticated<br />
numerical code that was fully secure.<br />
Dirty sensors or wet fingertips caused<br />
readability issues. Slow analytics took<br />
too long to validate identity, and some<br />
systems could be fooled by something<br />
as simple as an analog copy of a fingerprint<br />
printed on a clear piece of<br />
plastic.<br />
According to Gary Jones, Director<br />
of Biometric Access and Time Solutions<br />
at MorphoTrak LLC, those legacy<br />
scanners are just as obsolete as the<br />
paper fingerprints in old police ledgers.<br />
Today’s fingerprint sensors are<br />
fast, accurate, and reliable.<br />
“We call this frictionless access,”<br />
Jones told me. “The difference is that<br />
we now know how to capture fingerprints<br />
in 3D. Once you have the whole<br />
fingerprint, including the curvature,<br />
you can capture more information.<br />
38<br />
And that extra information means incredible<br />
accuracy. We can now come<br />
very close to the rolled capture from<br />
ink-and-paper, even with a partial<br />
scan. And we can process that information<br />
very rapidly.”<br />
Always Available, Rarely Lost<br />
Another key element in the evolution<br />
of fingerprint scanning has been the<br />
development of sensors that automatically<br />
account for distorted scans, wet<br />
fingers, or dirty surfaces. These newer<br />
technologies operate under challenging<br />
conditions that confused older<br />
systems, and occasionally rendered<br />
them inoperable.<br />
Speed is another major improvement,<br />
according to MorphoTrak’s<br />
Gary Jones.<br />
“Wave your hand – left or right –<br />
it does not matter. We now see what<br />
we need to see as your fingers move<br />
through the scanning area. It’s like<br />
placing your finger on an older sensor<br />
10, 12, or 15 times – except you<br />
only have to wave once, and you don’t<br />
have to place your finger down on a<br />
surface.”<br />
The result is an advanced identity<br />
management solution that can move<br />
large numbers of people through
doorways, gateways, turnstiles, and<br />
other access points with impressively<br />
little delay. It works when hands<br />
are wet, dirty, or even<br />
damaged. This method<br />
delivers enhanced security<br />
without cards,<br />
key fobs, smartphone<br />
two-factor authentication<br />
apps, or other<br />
devices that need to<br />
be managed and can<br />
easily be lost. It takes<br />
a catastrophic event for someone to<br />
misplace a finger.<br />
Multiple Security Layers<br />
Modern fingerprint sensors can provide<br />
two-factor authentication out of<br />
the same device scanning for fingerprints.<br />
The unit can recognize unique<br />
finger vein patterns at the same time.<br />
In the infinitesimally unlikely event<br />
that two individuals have the same<br />
fingerprint, or that the sensor has<br />
somehow been fooled with a spoofed<br />
print, the vein pattern provides an additional<br />
layer of security that is tough<br />
to fake.<br />
Adding a PIN requirement enables<br />
three-factor authentication – all from<br />
a single sensor and keypad. “MorphoTrak’s<br />
FingerVP product won a<br />
Best-In-Show at ISC West for this innovation,”<br />
Jones pointed out.<br />
The final piece of the puzzle comes<br />
from faster, smarter processing, both<br />
on the sensor and in the back end<br />
systems that handle the significantly<br />
greater amounts of data that each<br />
scan can capture. It has never been<br />
easier to process the volume of data<br />
The final piece of the puzzle comes from<br />
faster, smarter processing, both on the<br />
sensor and in the back end systems that<br />
handle the significantly greater amounts<br />
of data that each scan can capture.<br />
necessary for proper identity management<br />
using something as simple<br />
and unique as a fingerprint. National<br />
Institute of Standards and Technology<br />
(NIST) testing has confirmed the<br />
superior performance of MorphoTrak’s<br />
approach.<br />
“People, especially younger individuals,<br />
quite literally expect the world at<br />
their fingertips through their smartphones,”<br />
Jones added. “And they’re<br />
already used to securing their phones<br />
with their fingerprints. We can now<br />
deliver that same ease of use at the<br />
levels of security demanded by the<br />
toughest of governmental and business<br />
standards.”<br />
Standards Compliance<br />
MorphoTrak’s technology operates<br />
equally well as a mobile solution as<br />
it does at fixed locations, according<br />
to Jones. It complies with essential<br />
government standards to ensure<br />
high levels of effectiveness and performance.<br />
These include FIPS 201<br />
39<br />
Personal Identity Verification (PIV)<br />
approval for Federal contractors and<br />
employees, Transportation Worker<br />
Identity Credential<br />
(TWIC) certification<br />
for Homeland Security<br />
contractors, and FBI<br />
Next Generation Identification<br />
(NGI) Image<br />
Quality Specification<br />
(IQS) compliance.<br />
This commitment to<br />
standards also ensures<br />
that MorphoTrak’s fingerprint solutions<br />
integrate smoothly with other<br />
biometric systems. The company<br />
recognizes that no single technology<br />
provides perfect identity management.<br />
It is essential for organizations<br />
to be able to operate multiple layers<br />
of authentication as transparently as<br />
possible.<br />
Sometimes, what is old becomes<br />
new again.<br />
John Convy and Convy Associates provide<br />
strategic alliance, A&E consultant,<br />
technology ecosystem, and lead<br />
generation programs to monetize relationships<br />
and accelerate demand for<br />
leading security industry manufacturers.<br />
John is the Founder and Managing<br />
Director of the Open Standards<br />
Security Alliance and the IP Security<br />
Academy, and a speaker at many global<br />
industry events. Email: John@ConvyAssociates.com
Oil/Gas/Electric Grid Security<br />
The nation’s power grid is struck by cyber or physical attacks<br />
once every four days, according to Federal energy records<br />
By Bill Gertz<br />
The threat of a devastating cyber<br />
attack on the U.S. electrical grid is<br />
increasing due to the Obama administration’s<br />
politically correct<br />
policies that spend vast sums on<br />
green and smart grid technologies<br />
while failing to secure power grids<br />
from cyber attack.<br />
A report by the Manhattan Institute,<br />
a New York think tank, warns<br />
that the push to integrate wind and<br />
solar electrical power into the $6<br />
trillion electric utility system has<br />
created new vulnerabilities that<br />
other nations could exploit in a future<br />
cyber war.<br />
“Electric grids have always been<br />
vulnerable to natural hazards and<br />
malicious physical attacks,” writes<br />
Mark Mills, a physicist and engineer<br />
who authored the Manhattan<br />
Institute report. “Now the U.S. faces<br />
a new risk—cyber attacks—that<br />
could threaten public safety and<br />
greatly disrupt daily life.”<br />
The U.S. electrical power network<br />
is not made up of a single<br />
grid, but a complex web of eight<br />
40<br />
regional “supergrids” linked to<br />
thousands of local grids. Under a<br />
drive for improved efficiency, government<br />
policymakers and regulators<br />
in recent years have spent tens<br />
of billions of dollars on so-called<br />
“smart grid” technology. But<br />
the efficiency drive has not been<br />
matched with new technology that<br />
will secure grids against cyber attacks.<br />
Utility owners also have resisted<br />
improving cyber security over<br />
concerns doing so would increase<br />
operating costs and force unpopular<br />
rate hikes. Yet the failure to<br />
take steps now to deal with future<br />
threats could prove catastrophic.<br />
The threat, according to the report,<br />
is not the current state of security<br />
but the future use of greener<br />
and smarter electric grids, interconnected<br />
and linked to the Internet.<br />
“These greener, smarter grids<br />
will involve a vast expansion of<br />
the Internet of Things that greatly<br />
increases the cyber attack surface<br />
available to malicious hackers and<br />
hostile nation-state entities,” the<br />
report warns, adding that cyber attacks<br />
overall have risen 60 percent<br />
annually over the past six years<br />
and increasingly include the targeting<br />
of electric utilities.<br />
A recent survey by Cisco Systems<br />
revealed that 70 percent of electric<br />
utility security managers suffered<br />
at least one security breach.<br />
Unfortunately, Obama’s liberal<br />
agenda forced government policymakers<br />
and regulators to promote<br />
green and smart grid technologies<br />
while spending relatively trivial<br />
amounts to secure those grids<br />
from cyber attacks.<br />
“Greater grid cyber security in<br />
the future means that policymakers<br />
must rethink the deployment<br />
of green and smart grids until<br />
there are assurances that security<br />
technologies have caught up,” the<br />
report recommends.<br />
Part of the problem for grid security<br />
is that power networks are<br />
controlled by the private sector<br />
utilities. Government can and<br />
must provide intelligence and<br />
warning of cyber threats. But grid<br />
security is the responsibility of industry<br />
and there is an urgent need
for the private sector to do more to<br />
defend the country from a future<br />
devastating blackout.<br />
Further, the government and<br />
electric companies appear to be<br />
playing down the danger, claiming<br />
cyber attacks are less likely than<br />
squirrels eating electrical cables,<br />
or tree limbs shorting out wires.<br />
This attitude was reflected in<br />
a controversial Department of<br />
Homeland Security Report produced<br />
in January that concluded<br />
the threat of a damaging or disruptive<br />
cyber attack on the electric infrastructure<br />
was low. The study was<br />
an embarrassing reminder that the<br />
federal government is ill-prepared<br />
for future dangers. A month before<br />
the DHS report, Russian hackers<br />
took down portions of Ukraine’s<br />
power grid in what has been called<br />
the first known cyber attack on an<br />
electricity infrastructure.<br />
The problem of grid security<br />
has been made worse by the past<br />
seven years of administration policies<br />
that subordinated building up<br />
security against cyber attacks to<br />
integrating environmental technologies.<br />
The liberal worldview<br />
mistakenly has placed climate<br />
change as a greater national security<br />
threat than future cyber attacks<br />
from nation states.<br />
According to the Manhattan report,<br />
wind and solar power will be<br />
unable to meet the country’s 24/7<br />
41<br />
energy demands for the foreseeable<br />
future. Yet programs to develop<br />
these energy sources received<br />
over 75 percent of all new generating<br />
capacity, with some $150 billion<br />
invested by the federal government<br />
on green and smart grid<br />
programs. By contrast, the Energy<br />
Department spent $150 million on<br />
cyber security research and development.<br />
Blackouts have occurred in the<br />
past, mainly after hurricanes. One<br />
non-natural disaster was the August<br />
2003 blackout that affected<br />
New York City and the Northeast.<br />
That power outage put 50 million<br />
people in the dark for two days,<br />
and caused $6 billion in damage.<br />
The cause was a combination of a<br />
software glitch and human error<br />
that resulted in a localized power<br />
outage in Ohio cascading into a<br />
widespread regional power disruption.<br />
According to the Manhattan Institute<br />
study, Lloyd’s estimates that<br />
the damage from a worst-case cyber<br />
attack that causes a widespread<br />
blackout would cost between $250<br />
billion and $1 trillion.<br />
The coming danger will involve<br />
sophisticated nation state cyber attacks.<br />
U.S. Cyber Command chief<br />
More on page 50
Oil/Gas/Electric Grid Security<br />
Quanergy acquires OTUS People Tracker Software<br />
from Raytheon BBN Technologies to strengthen its<br />
position as complete LiDAR solution provider<br />
SUNNYVALE, Calif.—(BUSINESS<br />
WIRE)—Quanergy Systems, Inc.,<br />
the leading provider of solid state<br />
LiDAR sensors and smart sensing<br />
solutions, today announced the acquisition<br />
of OTUS People Tracker<br />
software from Raytheon BBN Technologies.<br />
The software complements<br />
Quanergy’s existing software portfolio<br />
and, when used with Quanergy’s<br />
LiDAR sensors, creates an<br />
integrated hardware and software<br />
solution for advanced people detection<br />
and tracking applications<br />
within the security and autonomous<br />
driving markets.<br />
OTUS uses sophisticated human<br />
perception algorithms to identify<br />
and track people for safety and security<br />
in crowded environments at<br />
ranges exceeding 100 meters when<br />
used with Quanergy LiDAR sensors.<br />
The system features segmentation<br />
techniques identifying humans,<br />
background extraction, object clustering,<br />
sophisticated merge and split<br />
algorithms, persistent<br />
tracking algorithms, and other advanced<br />
features supporting robust<br />
crowd control. Support for multiple<br />
zones of interest is included, allowing<br />
users fine control over active<br />
monitoring. With the acquisition,<br />
Quanergy is offering the most intelligent<br />
and complete solution to<br />
track people in 3D and in real-time<br />
over large spaces. The combined solution<br />
has advantages over camera<br />
systems including the<br />
ability to work in any<br />
weather or lighting<br />
conditions with fewer<br />
false alarms, along<br />
with the reduction of<br />
equipment and labor<br />
costs.<br />
“The acquisition<br />
of Raytheon BBN’s<br />
42<br />
OTUS People Tracker software is a<br />
significant milestone in Quanergy’s<br />
strategy and long term road map<br />
for LiDAR integration into larger<br />
transportation and automation<br />
platforms,” said Dr. Louay Eldada,<br />
Quanergy CEO. “Raytheon BBN is a<br />
recognized leader in the space, with<br />
the most advanced solution, and<br />
Quanergy is now further positioned<br />
to expand its footprint and accelerate<br />
its ability to deliver new levels of<br />
product performance.”<br />
The software is the foundation for<br />
Q-Guard, Quanergy’s 3D perimeter<br />
fencing and intrusion detection system.<br />
The company recently demonstrated<br />
Q-Guard and the capability<br />
for tracking human subjects at the<br />
tradeshow, ASIS 2016, which was<br />
held September 12-15 at the Orange<br />
County Convention Center in Orlando,<br />
Florida. The demo will show<br />
how Quanergy LiDAR sensors and<br />
software incorporating the OTUS<br />
People Tracker capability can track<br />
people persistently, send commands<br />
to PTZ cameras and enable the cameras<br />
to focus on subjects.
About Quanergy Systems, Inc.<br />
Quanergy Systems, Inc. was founded<br />
in 2012 and builds on decades of<br />
experience of its team in the areas<br />
of optics, photonics, optoelectronics,<br />
artificial intelligence software,<br />
and control systems. Headquartered<br />
in Sunnyvale, California, in<br />
the heart of Silicon Valley, Quanergy<br />
offers the leading solid state<br />
LiDAR sensors and software for<br />
real-time capture and processing of<br />
high-definition 3D mapping data<br />
and object detection, tracking, and<br />
classification. Application areas include<br />
transportation, security, mapping<br />
and industrial automation.<br />
Quanergy’s LiDARs lead in six key<br />
commercialization areas (price, performance,<br />
reliability, size, weight,<br />
power efficiency) while meeting the<br />
mass deployment requirements of<br />
durability and dependability using<br />
solid state technology. For more information<br />
about Quanergy, visit us<br />
at www.quanergy.com and follow us<br />
on Twitter @Quanergy.<br />
Sign-up for Free<br />
<strong>GSN</strong> Digital Editions<br />
and Email Newsletters<br />
Free subscription to your selection of <strong>GSN</strong> digital editions<br />
and daily/weekly email newsletters. Add new selections or<br />
opt-out of any selections at any time.<br />
<strong>GSN</strong> Airport, Seaport, Rail, Border Security Weekly<br />
<strong>GSN</strong> Daily Insider Newsletter (5 Days Weekly)<br />
<strong>GSN</strong> Monthly Digital Edition<br />
<strong>GSN</strong> Media Kit<br />
CLICK HERE<br />
The News Leader in Physical, IT and Homeland Security<br />
www.gsnmagazine.com<br />
43
Oil/Gas/Electric Grid Security<br />
InfragardNCR launches national critical infrastructure<br />
security and resilience month awareness campaign<br />
WASHINGTON, DC – <strong>Oct</strong>ober 12<br />
– InfraGard of the National Capital<br />
Region (InfraGardNCR), a partnership<br />
between the FBI and the private<br />
sector to protect critical infrastructure,<br />
today launched a comprehensive<br />
effort to recognize and support<br />
National Critical Infrastructure Security<br />
& Resilience Month (NCIS-<br />
RM). The initiative supports the U.S.<br />
Department of Homeland Security’s<br />
National Protection & Programs<br />
Directorate, Office of Infrastructure<br />
Protection mission to raise awareness<br />
around critical infrastructure<br />
protection during the month of November.<br />
InfraGardNCR unveiled<br />
the NCISRM website and its numerous<br />
social media interaction points<br />
and announced an owner/operator<br />
driven event to focus on CI supply<br />
chain partners.<br />
“Well after the events of September<br />
11 we are still working to understand<br />
and mitigate the complex<br />
challenges posed by our converged<br />
cyber and physical environments.<br />
NCISRM is an opportunity for<br />
both the owners and operators of<br />
our critical infrastructure, and our<br />
government counterparts engaged<br />
in all 16 critical infrastructures<br />
to highlight and<br />
reinforce their work, understand<br />
in-depth the pressing<br />
threats and vulnerabilities,<br />
and work on ways to mitigate<br />
their effects,” said Kristina<br />
Tanasichuk, president of InfraGardNCR<br />
and CEO of the<br />
Government Technology &<br />
Services Coalition.<br />
The Office of Infrastructure<br />
Protection, within the U.S.<br />
Department of Homeland<br />
Security’s National Protec-<br />
44<br />
tion and Programs Directorate, is<br />
partnering with InfraGardNCR to<br />
promote Critical Infrastructure Security<br />
and Resilience Month. InfraGardNCR<br />
has<br />
been working<br />
since January<br />
2016 with numerous<br />
stakeholders<br />
and<br />
national nonprofit<br />
organizations<br />
that are<br />
aligned with the<br />
16 critical infrastructure<br />
sectors<br />
to work together<br />
in November to<br />
raise awareness<br />
and take tangible<br />
steps to improve<br />
the security posture around our<br />
critical infrastructure.<br />
In addition to campaigns to raise<br />
awareness, InfraGardNCR will<br />
bring key stakeholders together to<br />
explore physical and cyber vulnerabilities<br />
to the U.S. electric grid.<br />
The discussions will focus on the<br />
threats to the grid and include briefings<br />
from both the FBI and the Of-
fice of the Director of National Intelligence,<br />
in addition to a targeted<br />
campaign for owners and operators<br />
to invite their vendors and others<br />
who “should” know more about CI<br />
in order to make their supply chain<br />
stronger and educate those who<br />
may not focus on critical infrastructure<br />
security on a daily basis will be<br />
a key part of the<br />
awareness effort.<br />
“Critical infrastructure<br />
organizations<br />
need<br />
to be concerned<br />
about the physical<br />
security as<br />
well as the cybersecurity<br />
of their<br />
small business<br />
suppliers. Those<br />
small businesses<br />
in the supply<br />
chain need to be<br />
concerned about<br />
their security<br />
primarily for the common good,<br />
but also to differentiate themselves<br />
to their critical infrastructure customers.<br />
The BBB is engaging with<br />
NCISRM to raise awareness of sector<br />
interdependencies and to provide<br />
training for small businesses<br />
across North America based on the<br />
NIST Cybersecurity Framework,”<br />
added Bill Fanelli, CISSP, Chief<br />
Security Officer, Council of Better<br />
Business Bureaus Inc.<br />
Owners and operators of critical<br />
infrastructure, non-profit organizations<br />
that represent critical<br />
infrastructure sectors, colleges and<br />
universities, and private companies<br />
are all invited to partner during November<br />
to raise awareness and educate<br />
their constituents. More information<br />
on partnership is available<br />
here.<br />
The NCISRM website, which will<br />
provide tools, resources, and tips<br />
throughout November, is available<br />
at www.NCISRM.org.<br />
More information on the in-person<br />
event, Attacking the Grid: Left<br />
and Right of Boom, will take place<br />
in Tysons Corner, Virginia and<br />
focus on uncovering interdependencies<br />
due to an extended power<br />
outage. This year’s NCISRM event<br />
will provide attendees with three<br />
things: 1) the most recent, accurate<br />
threat assessments from the<br />
FBI and ODNI; 2) an in-depth look<br />
45<br />
at the December 2015 cyberattack<br />
on the electric grid in Ukraine and<br />
an analysis of the implications of a<br />
similar attack in the United States;<br />
and 3) scenario-based facilitated<br />
breakout sessions with stakeholders<br />
across critical infrastructure sectors<br />
to discuss best practices and tangible<br />
tools for preventing, detecting,<br />
responding, and recovering from a<br />
large power outage.<br />
More information on all of these<br />
activities can be found at: www.<br />
NCISRM.org.<br />
About InfraGardNCR<br />
InfraGardNCR is a partnership between<br />
the FBI and the private sector<br />
to share information to protect the<br />
nation’s critical infrastructure. InfraGardNCR<br />
serves as a critical link<br />
that connects owners and operators<br />
with the entities that strive to protect<br />
their assets. More information<br />
is available at www.InfraGardNCR.<br />
org.
GTT releases most advanced TSP<br />
solution to date<br />
Continued from page 5<br />
reliable traffic solutions to communities<br />
for over 40 years. GTT proactively<br />
delivers advanced transportation<br />
solutions to help emergency, transit<br />
and traffic personnel increase safety,<br />
minimize traffic congestion and reduce<br />
greenhouse gas emissions, while<br />
maximizing resource efficiency and<br />
performance. Headquartered in St.<br />
Paul, Minnesota, GTT is the market<br />
leader in traffic management systems,<br />
with its system installed in intersections<br />
in 41 of the 50 largest U.S. cities.<br />
To find out more about GTT, visit their<br />
website (www.gtt.com).<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
<strong>GSN</strong> Media Kit<br />
CLICK HERE<br />
HID Global Helps Streamline<br />
Bhutan’s Driver License Issuance<br />
and Management System<br />
Continued from page 10<br />
benefit from the change to the<br />
printing process. In the months<br />
since the new IDs were issued, law<br />
enforcement officers have observed<br />
a decline in incidents involving<br />
fake IDs. The new security features<br />
on the IDs prove to be an effective<br />
deterrence against counterfeiting.<br />
Those counterfeit driver’s licenses<br />
circulating in the market can easily<br />
be distinguished from the genuine<br />
ones. The inability to create a counterfeit<br />
of the new IDs has resulted<br />
in a drop in the production of inauthentic<br />
IDs.ww<br />
“We are very pleased with the deployment<br />
of the HDP5000 printers<br />
and are are currently exploring how<br />
we can expand our use of technology.<br />
Smart chip encoding, which<br />
can be supported by the printers<br />
with an upgrade, would enable us to<br />
augment the cards and make them<br />
multifunctional, and is a feature we<br />
are interested in implementing in<br />
the near future,” said Nidup.<br />
© 2016 HID Global Corporation/ASSA ABLOY<br />
AB. All rights reserved. HID, HID Global,<br />
the HID Blue Brick logo, and Chain Design<br />
and FARGO are trademarks or registered<br />
trademarks of HID Global or its licensor(s)/<br />
supplier(s) in the US and other countries and<br />
may not be used without permission. All other<br />
trademarks, service marks, and product or service<br />
names are trademarks or registered trademarks<br />
of their respective owners. hidglobal.com<br />
46<br />
What was in the World Trade<br />
Center chemical plume created at<br />
Ground Zero on “9/11”?<br />
Continued from page 14<br />
“we did the very best we could at the<br />
time” and she was sorry that people<br />
had died as a result of her “mistake”<br />
– a claim which was disputed and rejected<br />
by numerous firefighters, who<br />
made it clear that they knew the air<br />
was polluted with toxins, but they did<br />
the clean-up work and searches for<br />
survivors because that was their job.<br />
Other firefighters described the EPA<br />
decision to be absurd in light of the<br />
fact that seven days after the attacks<br />
virtually all the buildings in downtown<br />
Manhattan were coated with<br />
dust, debris, lead, asbestos and other<br />
toxic substances. Still others argued<br />
that Ms Whitman’s decision jeopardized<br />
the health of every school child<br />
and every educator who went back to<br />
teach the children, along with every<br />
person who lived in the area who returned<br />
home to breathe in toxic dust.<br />
According to a post-fifteenth anniversary<br />
article by the Associated<br />
Press, “More than 1,000 people who<br />
registered with the World Trade Center<br />
Health Program, set up to oversee<br />
those affected by the aftermath<br />
of the attacks, have died in the past<br />
15 years. According to a summary<br />
of five research articles on the health<br />
impacts on rescuers and others who<br />
worked the site, both the number<br />
of people sickened and the type of<br />
illnesses present were greater than
anticipated. According to Jake Lemonda,<br />
union head of the Uniformed<br />
Fire Officer’s Association, there are<br />
currently 1,396 afflicted with cancer;<br />
5,456 with a lower respiratory illness<br />
and there are many more firefighters<br />
who responded on 9/11 who are very<br />
sick.”<br />
References<br />
1. Amy Goodman, “Ex-EPA Head Christine<br />
Todd Whitman Denies Misleading Public over<br />
Environmental Dangers After ‘9/11’ ”, Independent<br />
Global News, June 26, 2007; www.democracynow.org/2007/6/26/ex_epa_head_christine_todd_whitman<br />
2. Thomas K. Aldrich, M.D., Jackson Gustave,<br />
M.P.H., Charles B. Hall, Ph.D., “Lung Function<br />
in Rescue Workers at the World Trade Center after<br />
7 Years”, New England Journal of Medicine,<br />
2010; 362:1263-1272, April 8, 2010<br />
3. David Biello, “What Was in the World<br />
Trade Center Plume? Ten years later, what exactly<br />
residents and rescue workers were exposed<br />
to remains at least a partial mystery”, Scientific<br />
American, September 7, 2011; www.scientificamerican.com/article/what-was-in-the-worldtrade-center-plume/<br />
4. Rachel Zeig-Owens, Anna Nolan, Barbara<br />
Putman, Ankura Singh, David J. Prezant, Michael<br />
D. Weiden. “Biomarkers of patient intrinsic<br />
risk for upper and lower airway injury after exposure<br />
at the World Trade Center”, American Journal<br />
of Industrial Medicine, 2016, 59:9, 788-794.<br />
5. Jennifer Yip, Mayris P. Webber, Rachel<br />
Zeig-Owens, Madeline Vossbrinck, Ankura<br />
Singh, Kerry Kelly, David J. Prezant, “FDNY and<br />
9/11: Clinical services and health outcomes in<br />
World Trade Center-exposed firefighters and EMS<br />
workers from 2001 to 2016”, American Journal of<br />
Industrial Medicine, 2016 59:9, 695-708<br />
6. Caralee Caplan-Shaw, Angeliki Kazeros,<br />
Deepak Pradhan, Kenneth Berger, Roberta<br />
Goldring, Sibo Zhao, Mengling Liu, Yongzhao<br />
Shao; “Improvement in severe lower respiratory<br />
symptoms and small airway function in World<br />
Trade Center dust exposed community members”,<br />
American Journal of Industrial Medicine, 2016<br />
Canon U.S.A. and National Crime<br />
Prevention Council collaborate<br />
Continued from page 15<br />
About Canon U.S.A., Inc.<br />
Canon U.S.A., Inc., is a leading provider<br />
of consumer, business-to-business,<br />
and industrial digital imaging<br />
solutions to the United States and to<br />
Latin America and the Caribbean<br />
(excluding Mexico) markets. With<br />
approximately $31 billion in global<br />
revenue, its parent company, Canon<br />
Inc. (NYSE: CAJ), ranks third overall<br />
in U.S. patents granted in 2015†<br />
and is one of Fortune Magazine’s<br />
World’s Most Admired Companies<br />
in 2016. Canon U.S.A. is committed<br />
to the highest level of customer satisfaction<br />
and loyalty, providing 100<br />
percent U.S.-based consumer service<br />
and support for all of the products<br />
it distributes. Canon U.S.A.<br />
59:9, 777-787.<br />
7. James E. Cone, Sukhminder Osahan, Christine<br />
C. Ekenga, Sara A. Miller-Archie; “Asthma<br />
among Staten Island fresh kills landfill and barge<br />
workers following the September 11, 2001 World<br />
Trade Center terrorist attacks”, American Journal<br />
of Industrial Medicine, 2016, 59:9, 795-804<br />
8. “Lung function indices”, www.spirxpert.<br />
com/indices7.htm<br />
9. “James L. Zadroga 9/11 Health and Compensation<br />
Act”, “9/11 Health”, www.nyc.gov/<br />
html/doh/wtc/html/health_compensation/<br />
health_compensation_act.shtml<br />
10. “Medical management of chemical casualties<br />
handbook”, 3rd ed. USAMRICD, Aberdeen<br />
Proving Ground, MD. July 2000.<br />
11. Kales S, Christiani D., “Acute chemical injuries”,<br />
New England Journal of Medicine 2004;<br />
350:800-808.<br />
47<br />
is dedicated to its Kyosei philosophy<br />
of social and environmental<br />
responsibility. In 2014, the Canon<br />
Americas Headquarters secured<br />
LEED® Gold certification, a recognition<br />
for the design, construction,<br />
operations and maintenance of<br />
high-performance green buildings.<br />
To keep apprised of the latest news<br />
from Canon U.S.A., sign up for the<br />
Company’s RSS news feed by visiting<br />
www.usa.canon.com/rss and<br />
follow us on Twitter @CanonUSA.<br />
For media inquiries, please contact<br />
pr@cusa.canon.com.<br />
About National Crime<br />
Prevention Council<br />
The National Crime Prevention<br />
Council is the nonprofit leader in<br />
crime prevention. For more than 35<br />
years, our symbol of safety, McGruff<br />
the Crime Dog®, has delivered easyto-use<br />
crime prevention tips that<br />
protect what matters most—you,<br />
your family, and your community.<br />
Since 1982, NCPC has continuously<br />
provided the American public with<br />
comprehensive educational materials,<br />
training programs, and effective<br />
crime prevention messaging, delivered<br />
in large part through its vast<br />
network of more than 10,000 state<br />
and local law enforcement agencies,<br />
crime prevention associations,<br />
community groups, foundations,<br />
and corporate partners.<br />
For more information on how NCPC<br />
can be a public safety expert for<br />
you or how to “Take A Bite Out of<br />
Crime®,” visit www.ncpc.org.
International sports competition<br />
in Brazil<br />
Continued from page 19<br />
rity applications include real-time<br />
credential validation; integration<br />
with multiple handheld peripherals;<br />
tracking of all access activity; and<br />
instantly provisioning and managing<br />
secure access to each identity<br />
per their access profile.<br />
SAFE Sports and Events Access<br />
Manager offers an ideal solution for<br />
temporary or limited engagement<br />
events where security is a high priority.<br />
About Quantum Secure, Inc.<br />
Quantum Secure’s SAFE software<br />
suite provides a single, fully interoperable<br />
and integrated physical security<br />
policy platform to manage and<br />
streamline security identities, compliance,<br />
and operations across multiple<br />
sites and systems. Quantum<br />
Secure’s customers include both<br />
commercial and government organizations.<br />
Quantum Secure is part<br />
of HID Global, an ASSA ABLOY<br />
Group brand.<br />
For more information, visit www.<br />
quantumsecure.com<br />
The 2015 ISIS Attacks on Paris:<br />
Assessment and Lessons Learned<br />
Continued from page 23<br />
Counter Terrorism Action Capabilities<br />
or an equivalent course should<br />
be offered to all first responders.<br />
• Enhance efforts regarding Tactical<br />
Emergency Medical Service to include<br />
Special Weapons and Tactics<br />
(SWAT) teams cross-training with<br />
Fire Department personnel.<br />
References<br />
1. Geert Vanden Wijngaert, AP, “Lessons<br />
Learned from the Paris and Brussels Terrorist<br />
Attacks”, March 23, 2016, www.USAToday.com<br />
2. “An ISIS Militant from Belgium Whose<br />
Own Family Wants Him Dead,” New York<br />
Times, November 17, 2015.<br />
3. “France under first state of emergency since<br />
1961”, The Guardian, November 15, 2016.<br />
4. “The Lessons of Mumbai”, The RAND Corporation,<br />
January 9, 2009.<br />
5. Paul Tassi, “How ISIS Terrorists May<br />
Have Used PlayStation 4 to Discuss And Plan<br />
Attacks”, Forbes, November 14, 2015; www.<br />
forbes.com/sites/insertcoin/2015/11/14/whythe-paris-isis-terrorists-used-ps4-to-planattacks/#2f03878c731a<br />
6. “Five Facts about the Muslim Population<br />
in Europe”, Pew Research Center, November 17,<br />
2015.<br />
7. “Forgotten in the Banlieus”, The Economist,<br />
February 23, 2013.<br />
8. “France: Efforts to Counter Islamist Terrorism<br />
and the Islamic State”, Congressional Research<br />
Service, November 18, 2015<br />
9. “Islamic, Yet Integrated,” The Economist,<br />
September 6, 2014.<br />
10. “Paris Attacks”, New York Times, November<br />
18, 2015.<br />
11. “Behind Francois Hollande’s Snap Decision”,<br />
Wall Street Journal, November 15, 2015.<br />
12. David, Edward F. III, Alejandro A. Alves<br />
and David Alan Sklansky, “Social Media and Police<br />
Leadership: Lessons from Boston”, New Perspectives<br />
in Policing Bulletin, Washington, DC,<br />
U.S. Department of Justice, National Institute of<br />
Justice, 2014<br />
Handheld Narcotics Analyzer<br />
Continued from page 24<br />
designed to reduce sample backlogs<br />
and ensure valuable resources are<br />
put to use on high-profile cases and<br />
analysis of unconfirmed samples;<br />
and<br />
• Free library updates that add<br />
newly discovered substances to the<br />
analyzer’s “fingerprint” library. For<br />
more information on the Thermo<br />
Scientific TruNarc handheld narcotics<br />
analyzer, please visit www.thermofisher.com/trunarc.<br />
About Thermo Fisher Scientific<br />
Thermo Fisher Scientific Inc. is the<br />
world leader in serving science,<br />
with revenues of $17 billion and<br />
more than 50,000 employees in 50<br />
countries. Our mission is to enable<br />
our customers to make the world<br />
healthier, cleaner and safer. We help<br />
our customers accelerate life sciences<br />
research, solve complex analytical<br />
challenges, improve patient<br />
diagnostics and increase laboratory<br />
productivity. Through our premier<br />
brands.<br />
Thermo Scientific, Applied Biosystems,<br />
Invitrogen, Fisher Scientific<br />
and Unity Lab Services – we offer<br />
an unmatched combination of innovative<br />
technologies, purchasing<br />
convenience and comprehensive<br />
support.<br />
For more information, please visit<br />
www.thermofisher.com.<br />
48
Cambridge Pixel enhances radar<br />
tracking software<br />
Continued from page 26<br />
and Tellumat.<br />
Cambridge Pixel will be showcasing<br />
its new SPx radar tracking software<br />
on stand G27 in Hall 2b (UK<br />
Pavilion) at Euronaval in Paris from<br />
17-21 <strong>Oct</strong>ober 2016.<br />
For more information about<br />
Cambridge Pixel’s radar tracker and<br />
range of software modules, please<br />
visit www.cambridgepixel.com or<br />
call: +44 (0) 1763 852749 or email:<br />
enquiries@cambridgepixel.com.<br />
About Cambridge Pixel<br />
Founded in 2007, Cambridge Pixel<br />
is an award-winning developer of<br />
sensor processing and display solutions<br />
including primary and secondary<br />
radar interfacing, processing<br />
and display components for military<br />
and commercial radar applications.<br />
It is a world-leading supplier of<br />
software-based radar tracking and<br />
scan conversion solutions through<br />
its modular SPx software, and HPx<br />
hardware product range. Based near<br />
Cambridge in the UK, the company<br />
operates worldwide through a network<br />
of agents and distributors. In<br />
2015, Cambridge Pixel received a<br />
Queen’s Award for Enterprise in International<br />
Trade for ‘outstanding<br />
overseas sales growth over the last<br />
three years.<br />
Government’s advisory committee<br />
want to end family detention<br />
Continued from page 28<br />
cent reports on family detention, including:<br />
• The S. Commission on International<br />
Religious Freedom’s Report<br />
on the extremely troubling practice<br />
of expedited removal that funnels<br />
children and families into detention<br />
• The American Immigration Lawyers’<br />
Association Report on Central<br />
Americans Seeking Asylum<br />
and Legal Protection in the U.S.<br />
• The American Immigration<br />
Council report on family separation<br />
in family detention and on<br />
families deported back to danger<br />
in Central America.<br />
• Human Rights First reports including<br />
Lifeline on Lockdown and<br />
Family Detention: Still Happening,<br />
Still Damaging.<br />
The Committee’s report will be worth<br />
reading in full and makes concrete,<br />
specific, practical recommendations<br />
throughout to comprehensively address<br />
the myriad of problems posed<br />
by detaining families, but the bottom<br />
line is clear – the U.S. government<br />
should end family detention.<br />
Lindsay Harris is Assistant Professor<br />
of Law at the University of the District<br />
of Columbia, David A. Clarke School<br />
of Law.<br />
Arrest of ex-NSA contractor shows<br />
federal cybersecurity still faces a<br />
serious inside threat<br />
Continued from page 36<br />
man said.<br />
“The main line of defense must be<br />
around your data,” he said. “These<br />
are the only assets you can control.<br />
It may not be a physical location—<br />
it could be in the cloud. There are<br />
endless possibilities for the ways a<br />
hacker or bad actor can get in, so<br />
you can’t try to control it all. The<br />
right approach to managing the insider<br />
threat problem starts with protecting<br />
against inappropriate access<br />
to all of your data repositories–databases,<br />
file servers and cloud applications.”<br />
Martin faces up to 10 years in<br />
federal prison for theft of government<br />
property and a year for the<br />
unauthorized retention of classified<br />
materials. He appeared in federal<br />
court in Maryland on Aug. 29 and<br />
remains in custody, according to the<br />
Department of Justice.<br />
49
Intelligent Automation Inc<br />
discusses Cyber Attacks<br />
Continued from page 37<br />
es to regulate the secure information<br />
flow. Smart AppShield shields<br />
the application from the cyber<br />
attacks and prevents information<br />
leakage, thus providing a trusted<br />
computing base.<br />
Trusted Computing Framework<br />
for Embedded System<br />
(TCES) is a hardware and software<br />
solution that provides broad capabilities<br />
for ensuring the security<br />
of highly distributed embedded<br />
systems, with high-level security<br />
assurance rooted in the hardware,<br />
and high flexibility provided by<br />
the software implementation.<br />
SecureVisor is a platform for<br />
efficiently protecting weapon systems<br />
against cyber threats. Secure-<br />
Visor has three major components<br />
including a whitelisting tool to<br />
identify allowed safe programs,<br />
a security enhanced hypervisor,<br />
and a Trusted Platform Module<br />
(TPM) to provide the root of trust.<br />
SecureVisor is a combined hardware-software<br />
security solution<br />
that provides a high level of security,<br />
and also minimizes impact on<br />
platforms in terms of power, processing<br />
cycles and operation performance.<br />
www.i-a-i.com<br />
The nation’s power grid is struck<br />
by cyber or physical attacks once<br />
every four days<br />
Continued from page 41<br />
Adm. Mike Rogers announced in<br />
March that it is a matter of “when,<br />
not if ” a foreign power will attack<br />
critical U.S. infrastructures.<br />
Peter Pry, a former CIA officer<br />
and grid security advocate, says<br />
the report correctly identified the<br />
contradiction between Obama administration’s<br />
green agenda and<br />
the need to protect the nation’s energy<br />
security.<br />
“The ‘war on coal’ and other hydrocarbon<br />
sources of energy, and<br />
the Obama administration’s environmental<br />
obstacles to development<br />
of nuclear power, is making<br />
the nation less safe,” said Pry, executive<br />
director of the Task Force on<br />
National and Homeland Security.<br />
Coal-fired electric plants and<br />
potentially nuclear power provide<br />
the country with the most resilient<br />
source of electric power. But<br />
the administration’s push to phase<br />
them out and replace them with<br />
wind and solar energy generation<br />
is not only technologically unrealistic.<br />
It will reduce national electrical<br />
supplies at a time when demand<br />
is increasing sharply.<br />
The result will be both increase<br />
costs for electric power and increase<br />
risks to national survival in<br />
50<br />
the aftermath a major cyber attack.<br />
“The increased risks to the national<br />
electric grid and national<br />
security by Obama’s green agenda,<br />
driven by the alleged threat from<br />
climate change, is even more true<br />
for greater threats to the grid posed<br />
by natural and manmade electromagnetic<br />
pulse (EMP),” Pry said.<br />
“These threats and cyber are here<br />
and now, while climate change—if<br />
this scientifically dubious threat<br />
occurs at all—is in the future.”<br />
Mills, the Manhattan Institute<br />
researcher, told the Washington<br />
Free Beacon that cyber security<br />
“is the existential challenge of the<br />
Internet, but so far mainly about<br />
private info and financial data.”<br />
“Meanwhile, the so-called smarter<br />
grid and green power both require<br />
a vast increase of Internet<br />
connectivity bolted onto our electrical<br />
grids,” he said. “What in the<br />
world makes green pundits think<br />
that rapidly expanding and exposing<br />
our critical grid infrastructure<br />
to the Internet is a good idea to<br />
rush into?”<br />
Editor’s Note: Bill Gertz article reproduced<br />
with permission of Washington<br />
Free Beacon: www.freebeacon.com
The News Leader in Physical, IT and Homeland Security<br />
CEO/Editorial Director<br />
Adrian Courtenay<br />
917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Editor<br />
Steve Bittenbender<br />
502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Senior Writer<br />
Karen Ferrick-Roman<br />
412-671-1456<br />
karenferrickroman@gmail.com<br />
Columnist<br />
Shawn Campbell<br />
Campbell on Crypto<br />
shawn.campbell@safenetat.com<br />
Columnist<br />
George Lane<br />
Hazmat Science & Public Policy<br />
georgelane@hotmail.com<br />
Contributing Author<br />
Lloyd McCoy Jr<br />
Immix Group<br />
Contributing Author<br />
Walter Ewing<br />
Contributing Author<br />
Wendy Feliz<br />
Contributing Author<br />
Joshua Breisblatt<br />
Contributing Author<br />
J. Michael Barrett<br />
Contributing Author<br />
Christopher Millar<br />
Gatekeeper Security<br />
Art Director<br />
Gerry O’Hara, OHDesign3<br />
gerry@ohd3.com<br />
203-249-0626<br />
Production Manager<br />
Brenden Hitt<br />
Brenden.hitt@gsnmagazine.com<br />
Direct: 203-216-7798<br />
COMING ATTRACTIONS<br />
November<br />
Tech Focus<br />
Perimeter Protection/<br />
Intrusion Detection<br />
Market Sector Focus<br />
Mass Notification/<br />
Disaster Response<br />
December<br />
Late News<br />
Tech Focus<br />
2016 Technology Roundup<br />
Special Awards Review:<br />
2016 Digital Yearbook of<br />
Awards Winners<br />
51