204 W. Brandi, M.S. Olivier, and A. Zugenmaier 4. Du, W., Atallah, M.J.: Secure multi-party computation problems and their applications: a review and open problems. In: NSPW 2001: Proceed<strong>in</strong>gs of the 2001 workshop on New security paradigms, pp. 13–22. ACM Press, New York (2001) 5. Du, W., Zhan, Z.: A practical approach to solve secure multi-party computation problems. In: NSPW 2002: Proceed<strong>in</strong>gs of the 2002 workshop on New security paradigms, pp. 127–135. ACM Press, New York (2002) 6. Goldreich, O.: Foundations of Cryptography. Basic Applications, vol. 2. Cambridge University Press, New York (2004) 7. Goldreich, O., Micali, S., Wigderson, A.: How to play any mental game. In: Proceed<strong>in</strong>gs of the n<strong>in</strong>eteenth annual ACM conference on Theory of comput<strong>in</strong>g, pp. 218–229. ACM, New York (1987) 8. Gorlach, A., He<strong>in</strong>emann, A., Terpstra, W.: Survey on location privacy <strong>in</strong> pervasive comput<strong>in</strong>g. In: Rob<strong>in</strong>son, P., Vogt, H., Wagealla, W. (eds.) Privacy, Security and Trust with<strong>in</strong> the Context of Pervasive Comput<strong>in</strong>g. The Kluwer International Series <strong>in</strong> Eng<strong>in</strong>eer<strong>in</strong>g and <strong>Computer</strong> <strong>Science</strong> (2004) 9. Ioannidis, I., Grama, A., Atallah, M.: A secure protocol for comput<strong>in</strong>g dot-products <strong>in</strong> clustered and distributed environments. In: ICPP 2002: Proceed<strong>in</strong>gs of the 2002 International Conference on Parallel Process<strong>in</strong>g (ICPP 2002), Wash<strong>in</strong>gton, DC, USA, p. 379. IEEE <strong>Computer</strong> Society Press, Los Alamitos (2002) 10. Kiltz, E., Leander, G., Malone-Lee, J.: Secure computation of the mean and related statistics. In: Kilian, J. (ed.) TCC 2005. LNCS, vol. 3378, pp. 283–302. Spr<strong>in</strong>ger, Heidelberg (2005) 11. Li, S., Dai, Y.: Secure two-party computational geometry. J. Comput. Sci. Technol. 20(2), 258–263 (2005) 12. Luo, Y., Huang, L., Chen, G., Shen, H.: Privacy-preserv<strong>in</strong>g distance measurement and its applications. Ch<strong>in</strong>ese Journal of Electronics 15(2), 237–241 (2006) 13. Naor, M., Nissim, K.: Communication preserv<strong>in</strong>g protocols for secure function evaluation. In: STOC 2001: Proceed<strong>in</strong>gs of the thirty-third annual ACM symposium on Theory of comput<strong>in</strong>g, pp. 590–599. ACM Press, New York (2001) 14. Friedman, E., Resnick, P., Zeckhauser, R., Kuwabara, K.: Reputation systems. Communication of the ACM 43(12), 45–48 (2000) 15. Resnick, P., Zeckhauser, R., Swanson, J., Lockwood, K.: The value of reputation on ebay: A controlled experiment (2003) 16. Shundong, L., Tiange, S., Yiqi, D.: Secure multi-party computation of set-<strong>in</strong>clusion and graph-<strong>in</strong>clusion. <strong>Computer</strong> Research and Development 42(10), 1647–1653 (2005) 17. Vaidya, J., Clifton, C.: Leverag<strong>in</strong>g the “multi” <strong>in</strong> secure multi-party computation. In: WPES 2003: Proceed<strong>in</strong>gs of the 2003 ACM workshop on Privacy <strong>in</strong> the electronic society, pp. 53–59. ACM Press, New York (2003) 18. Vaidya, J., Clifton, C.: Secure set <strong>in</strong>tersection card<strong>in</strong>ality with application to association rule m<strong>in</strong><strong>in</strong>g. Journal of <strong>Computer</strong> Security 13(4), 593–622 (2005) 19. Yao, A.: Protocols for secure computations (extended abstract). In: Proceed<strong>in</strong>gs of FOCS 1982, pp. 160–164 (1982) 20. Yao, A.: How to generate and exchange secrets. In: Proceed<strong>in</strong>gs of FOCS 1986, pp. 162–167 (1986)
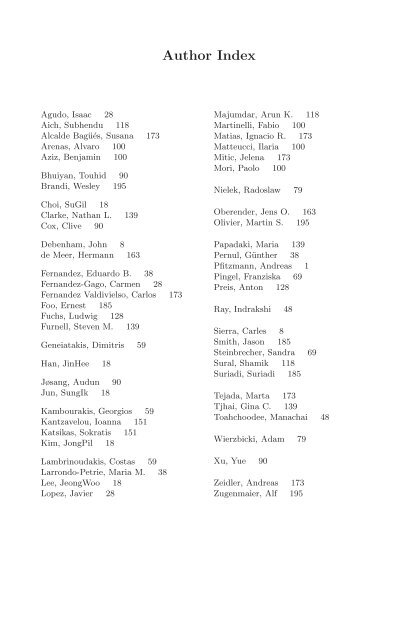
Agudo, Isaac 28 Aich, Subhendu 118 Alcalde Bagüés, Susana 173 Arenas, Alvaro 100 Aziz, Benjam<strong>in</strong> 100 Bhuiyan, Touhid 90 Brandi, Wesley 195 Choi, SuGil 18 Clarke, Nathan L. 139 Cox, Clive 90 Debenham, John 8 de Meer, Hermann 163 Fernandez, Eduardo B. 38 Fernandez-Gago, Carmen 28 Fernandez Valdivielso, Carlos 173 Foo, Ernest 185 Fuchs, Ludwig 128 Furnell, Steven M. 139 Geneiatakis, Dimitris 59 Han, J<strong>in</strong>Hee 18 Jøsang, Audun 90 Jun, SungIk 18 Kambourakis, Georgios 59 Kantzavelou, Ioanna 151 Katsikas, Sokratis 151 Kim, JongPil 18 Lambr<strong>in</strong>oudakis, Costas 59 Larrondo-Petrie, Maria M. 38 Lee, JeongWoo 18 Lopez, Javier 28 Author Index Majumdar, Arun K. 118 Mart<strong>in</strong>elli, Fabio 100 Matias, Ignacio R. 173 Matteucci, Ilaria 100 Mitic, Jelena 173 Mori, Paolo 100 Nielek, Radoslaw 79 Oberender, Jens O. 163 Olivier, Mart<strong>in</strong> S. 195 Papadaki, Maria 139 Pernul, Günther 38 Pfitzmann, Andreas 1 P<strong>in</strong>gel, Franziska 69 Preis, Anton 128 Ray, Indrakshi 48 Sierra, Carles 8 Smith, Jason 185 Ste<strong>in</strong>brecher, Sandra 69 Sural, Shamik 118 Suriadi, Suriadi 185 Tejada, Marta 173 Tjhai, G<strong>in</strong>a C. 139 Toahchoodee, Manachai 48 Wierzbicki, Adam 79 Xu, Yue 90 Zeidler, Andreas 173 Zugenmaier, Alf 195
- Page 1 and 2:
Lecture Notes in Computer Science 5
- Page 3 and 4:
Volume Editors Steven Furnell Unive
- Page 5 and 6:
Program Committee General Chairpers
- Page 7 and 8:
Invited Lecture Table of Contents B
- Page 9 and 10:
Biometrics - How to Put to Use and
- Page 11 and 12:
Biometrics-HowtoPuttoUseandHowNotat
- Page 13 and 14:
Biometrics-HowtoPuttoUseandHowNotat
- Page 15 and 16:
7 Outlook Biometrics-HowtoPuttoUsea
- Page 17 and 18:
A Map of Trust between Trading Part
- Page 19 and 20:
A Map of Trust between Trading Part
- Page 21 and 22:
A Map of Trust between Trading Part
- Page 23 and 24:
A Map of Trust between Trading Part
- Page 25 and 26:
A Map of Trust between Trading Part
- Page 27 and 28:
Implementation of a TCG-Based Trust
- Page 29 and 30:
Implementation of a TCG-Based Trust
- Page 31 and 32:
Implementation of a TCG-Based Trust
- Page 33 and 34:
Implementation of a TCG-Based Trust
- Page 35 and 36:
Implementation of a TCG-Based Trust
- Page 37 and 38:
A Model for Trust Metrics Analysis
- Page 39 and 40:
A Model for Trust Metrics Analysis
- Page 41 and 42:
A Model for Trust Metrics Analysis
- Page 43 and 44:
A Model for Trust Metrics Analysis
- Page 45 and 46:
A Model for Trust Metrics Analysis
- Page 47 and 48:
Patterns and Pattern Diagrams for A
- Page 49 and 50:
Patterns and Pattern Diagrams for A
- Page 51 and 52:
Policy Model AC model Patterns and
- Page 53 and 54:
Broker Investor Doctor Patient 1
- Page 55 and 56:
Patterns and Pattern Diagrams for A
- Page 57 and 58:
A Spatio-temporal Access Control Mo
- Page 59 and 60:
A Spatio-temporal Access Control Mo
- Page 61 and 62:
A Spatio-temporal Access Control Mo
- Page 63 and 64:
A Spatio-temporal Access Control Mo
- Page 65 and 66:
A Spatio-temporal Access Control Mo
- Page 67 and 68:
A Mechanism for Ensuring the Validi
- Page 69 and 70:
A Mechanism for Ensuring the Validi
- Page 71 and 72:
A Mechanism for Ensuring the Validi
- Page 73 and 74:
A Mechanism for Ensuring the Validi
- Page 75 and 76:
A Mechanism for Ensuring the Validi
- Page 77 and 78:
Multilateral Secure Cross-Community
- Page 79 and 80:
Multilateral Secure Cross-Community
- Page 81 and 82:
Multilateral Secure Cross-Community
- Page 83 and 84:
Multilateral Secure Cross-Community
- Page 85 and 86:
Multilateral Secure Cross-Community
- Page 87 and 88:
Fairness Emergence through Simple R
- Page 89 and 90:
Fairness Emergence through Simple R
- Page 91 and 92:
Fairness Emergence through Simple R
- Page 93 and 94:
Fairness Emergence through Simple R
- Page 95 and 96:
Fairness Emergence through Simple R
- Page 97 and 98:
Fairness Emergence through Simple R
- Page 99 and 100:
Combining Trust and Reputation Mana
- Page 101 and 102:
Combining Trust and Reputation Mana
- Page 103 and 104:
Combining Trust and Reputation Mana
- Page 105 and 106:
Combining Trust and Reputation Mana
- Page 107 and 108:
Combining Trust and Reputation Mana
- Page 109 and 110:
Controlling Usage in Business Proce
- Page 111 and 112:
Controlling Usage in Business Proce
- Page 113 and 114:
Controlling Usage in Business Proce
- Page 115 and 116:
Controlling Usage in Business Proce
- Page 117 and 118:
Controlling Usage in Business Proce
- Page 119 and 120:
Controlling Usage in Business Proce
- Page 121 and 122:
Controlling Usage in Business Proce
- Page 123 and 124:
A Semantics Rules for POLPA-Control
- Page 125 and 126:
Controlling Usage in Business Proce
- Page 127 and 128:
Spatiotemporal Connectives for Secu
- Page 129 and 130:
Spatiotemporal Connectives for Secu
- Page 131 and 132:
Spatiotemporal Connectives for Secu
- Page 133 and 134:
5.2 Expressiveness Spatiotemporal C
- Page 135 and 136:
Acknowledgement Spatiotemporal Conn
- Page 137 and 138:
BusiROLE: A Model for Integrating B
- Page 139 and 140:
BusiROLE: A Model for Integrating B
- Page 141 and 142:
BusiROLE: A Model for Integrating B
- Page 143 and 144:
BusiROLE: A Model for Integrating B
- Page 145 and 146:
BusiROLE: A Model for Integrating B
- Page 147 and 148:
The Problem of False Alarms: Evalua
- Page 149 and 150:
The Problem of False Alarms 141 pro
- Page 151 and 152:
The Problem of False Alarms 143 To
- Page 153 and 154:
The Problem of False Alarms 145 mad
- Page 155 and 156:
The Problem of False Alarms 147 Des
- Page 157 and 158:
The Problem of False Alarms 149 3.
- Page 159 and 160:
A Generic Intrusion Detection Game
- Page 161 and 162: A Generic Intrusion Detection Game
- Page 163 and 164: A Generic Intrusion Detection Game
- Page 165 and 166: A Generic Intrusion Detection Game
- Page 167 and 168: A Generic Intrusion Detection Game
- Page 169 and 170: A Generic Intrusion Detection Game
- Page 171 and 172: On the Design Dilemma in Dining Cry
- Page 173 and 174: On the Design Dilemma in Dining Cry
- Page 175 and 176: On the Design Dilemma in Dining Cry
- Page 177 and 178: On the Design Dilemma in Dining Cry
- Page 179 and 180: On the Design Dilemma in Dining Cry
- Page 181 and 182: Obligations: Building a Bridge betw
- Page 183 and 184: Obligations: Building a Bridge betw
- Page 185 and 186: Obligations: Building a Bridge betw
- Page 187 and 188: Obligations: Building a Bridge betw
- Page 189 and 190: Obligations: Building a Bridge betw
- Page 191 and 192: Obligations: Building a Bridge betw
- Page 193 and 194: A User-Centric Protocol for Conditi
- Page 195 and 196: A User-Centric Protocol for Conditi
- Page 197 and 198: A User-Centric Protocol for Conditi
- Page 199 and 200: Identity Escrow: A User-Centric Pro
- Page 201 and 202: A User-Centric Protocol for Conditi
- Page 203 and 204: Preservation of Privacy in Thwartin
- Page 205 and 206: Preservation of Privacy in Thwartin
- Page 207 and 208: Preservation of Privacy in Thwartin
- Page 209 and 210: Preservation of Privacy in Thwartin
- Page 211: Preservation of Privacy in Thwartin