Lecture Notes in Computer Science 5185
Lecture Notes in Computer Science 5185
Lecture Notes in Computer Science 5185
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
24 S. Choi et al.<br />
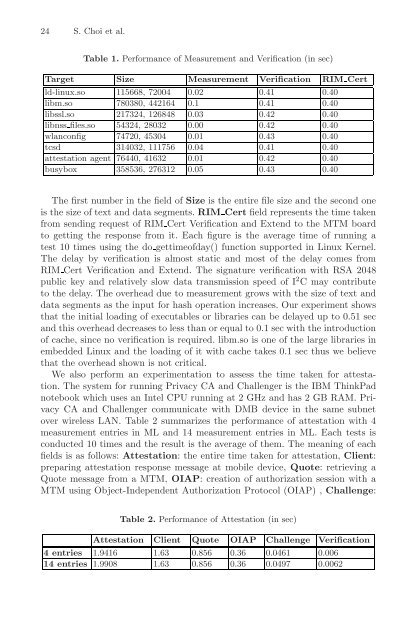
Table 1. Performance of Measurement and Verification (<strong>in</strong> sec)<br />
Target Size Measurement Verification RIM Cert<br />
ld-l<strong>in</strong>ux.so 115668, 72004 0.02 0.41 0.40<br />
libm.so 780380, 442164 0.1 0.41 0.40<br />
libssl.so 217324, 126848 0.03 0.42 0.40<br />
libnss files.so 54324, 28032 0.00 0.42 0.40<br />
wlanconfig 74720, 45304 0.01 0.43 0.40<br />
tcsd 314032, 111756 0.04 0.41 0.40<br />
attestation agent 76440, 41632 0.01 0.42 0.40<br />
busybox 358536, 276312 0.05 0.43 0.40<br />
The first number <strong>in</strong> the field of Size is the entire file size and the second one<br />
is the size of text and data segments. RIM Cert field represents the time taken<br />
from send<strong>in</strong>g request of RIM Cert Verification and Extend to the MTM board<br />
to gett<strong>in</strong>g the response from it. Each figure is the average time of runn<strong>in</strong>g a<br />
test 10 times us<strong>in</strong>g the do gettimeofday() function supported <strong>in</strong> L<strong>in</strong>ux Kernel.<br />
The delay by verification is almost static and most of the delay comes from<br />
RIM Cert Verification and Extend. The signature verification with RSA 2048<br />
public key and relatively slow data transmission speed of I 2 C may contribute<br />
to the delay. The overhead due to measurement grows with the size of text and<br />
data segments as the <strong>in</strong>put for hash operation <strong>in</strong>creases. Our experiment shows<br />
that the <strong>in</strong>itial load<strong>in</strong>g of executables or libraries can be delayed up to 0.51 sec<br />
and this overhead decreases to less than or equal to 0.1 sec with the <strong>in</strong>troduction<br />
of cache, s<strong>in</strong>ce no verification is required. libm.so is one of the large libraries <strong>in</strong><br />
embedded L<strong>in</strong>ux and the load<strong>in</strong>g of it with cache takes 0.1 sec thus we believe<br />
that the overhead shown is not critical.<br />
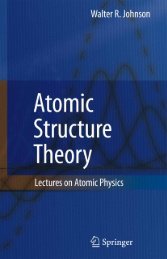
We also perform an experimentation to assess the time taken for attestation.<br />
The system for runn<strong>in</strong>g Privacy CA and Challenger is the IBM Th<strong>in</strong>kPad<br />
notebook which uses an Intel CPU runn<strong>in</strong>g at 2 GHz and has 2 GB RAM. Privacy<br />
CA and Challenger communicate with DMB device <strong>in</strong> the same subnet<br />
over wireless LAN. Table 2 summarizes the performance of attestation with 4<br />
measurement entries <strong>in</strong> ML and 14 measurement entries <strong>in</strong> ML. Each tests is<br />
conducted 10 times and the result is the average of them. The mean<strong>in</strong>g of each<br />
fields is as follows: Attestation: the entire time taken for attestation, Client:<br />
prepar<strong>in</strong>g attestation response message at mobile device, Quote: retriev<strong>in</strong>g a<br />
Quote message from a MTM, OIAP: creation of authorization session with a<br />
MTM us<strong>in</strong>g Object-Independent Authorization Protocol (OIAP) , Challenge:<br />
Table 2. Performance of Attestation (<strong>in</strong> sec)<br />
Attestation Client Quote OIAP Challenge Verification<br />
4entries 1.9416 1.63 0.856 0.36 0.0461 0.006<br />
14 entries 1.9908 1.63 0.856 0.36 0.0497 0.0062