NC1801
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
OPINION<br />
FORGET VPNS: THE<br />
FUTURE IS SDP<br />
VPN HAS BEEN MUCH RELIED<br />
ON BUT NOT ALWAYS LIKED.<br />
COULD THERE BE A NEW<br />
ALTERNATIVE? ALAN ZEICHICK,<br />
PRINCIPAL ANALYST AT<br />
CAMDEN ASSOCIATES SHARES<br />
HIS THOUGHTS<br />
The VPN model of extending security<br />
through enterprise firewalls is dead,<br />
and the future now belongs to the<br />
Software Defined Perimeter (SDP). Firewalls<br />
imply that there's an inside to the enterprise,<br />
a place where devices can communicate in<br />
a trusted manner. This being so, there must<br />
also be an outside where communications<br />
aren't trusted. Residing between the two is<br />
that firewall which decides which traffic can<br />
egress and which can enter following deep<br />
inspection, based on scans and policies.<br />
What about trusted applications requiring<br />
direct access to corporate resources from<br />
outside the firewall? That's where Virtual<br />
Private Networks came in, by offering a way<br />
to push a hole in the firewall. VPNs are a<br />
complex mechanism for using encryption<br />
and secure tunnels to bridge multiple<br />
networks, such as a head-office and<br />
regional office network. They can also<br />
temporarily allow remote users to become<br />
part of the network.<br />
VPNs are well established but perceived as<br />
difficult to configure on the endpoints, hard<br />
for IT to manage and challenging to scale<br />
for large deployments. There are also issues<br />
of software compatibility: not everything<br />
works through a VPN.<br />
Putting it bluntly, almost nobody likes VPNs<br />
and there is now a better way to securely<br />
connect mobile applications and Industrial<br />
Internet of Things (IIoT) devices into the<br />
world of data centre servers and cloudbased<br />
applications.<br />
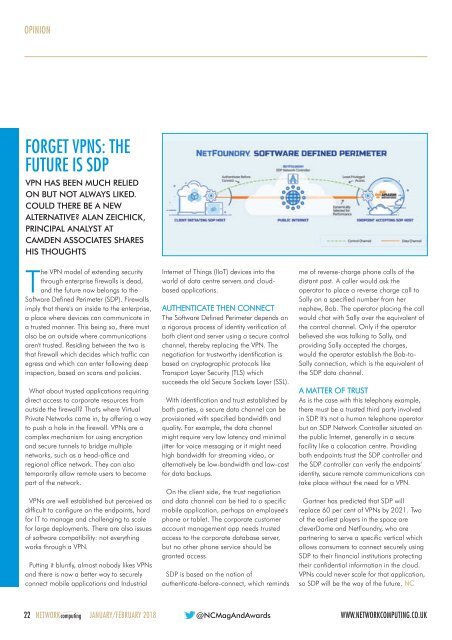
AUTHENTICATE THEN CONNECT<br />
The Software Defined Perimeter depends on<br />
a rigorous process of identity verification of<br />
both client and server using a secure control<br />
channel, thereby replacing the VPN. The<br />
negotiation for trustworthy identification is<br />
based on cryptographic protocols like<br />
Transport Layer Security (TLS) which<br />
succeeds the old Secure Sockets Layer (SSL).<br />
With identification and trust established by<br />
both parties, a secure data channel can be<br />
provisioned with specified bandwidth and<br />
quality. For example, the data channel<br />
might require very low latency and minimal<br />
jitter for voice messaging or it might need<br />
high bandwidth for streaming video, or<br />
alternatively be low-bandwidth and low-cost<br />
for data backups.<br />
On the client side, the trust negotiation<br />
and data channel can be tied to a specific<br />
mobile application, perhaps an employee's<br />
phone or tablet. The corporate customer<br />
account management app needs trusted<br />
access to the corporate database server,<br />
but no other phone service should be<br />
granted access.<br />
SDP is based on the notion of<br />
authenticate-before-connect, which reminds<br />
me of reverse-charge phone calls of the<br />
distant past. A caller would ask the<br />
operator to place a reverse charge call to<br />
Sally on a specified number from her<br />
nephew, Bob. The operator placing the call<br />
would chat with Sally over the equivalent of<br />
the control channel. Only if the operator<br />
believed she was talking to Sally, and<br />
providing Sally accepted the charges,<br />
would the operator establish the Bob-to-<br />
Sally connection, which is the equivalent of<br />
the SDP data channel.<br />
A MATTER OF TRUST<br />
As is the case with this telephony example,<br />
there must be a trusted third party involved<br />
in SDP. It's not a human telephone operator<br />
but an SDP Network Controller situated on<br />
the public Internet, generally in a secure<br />
facility like a colocation centre. Providing<br />
both endpoints trust the SDP controller and<br />
the SDP controller can verify the endpoints'<br />
identity, secure remote communications can<br />
take place without the need for a VPN.<br />
Gartner has predicted that SDP will<br />
replace 60 per cent of VPNs by 2021. Two<br />
of the earliest players in the space are<br />
cleverDome and NetFoundry, who are<br />
partnering to serve a specific vertical which<br />
allows consumers to connect securely using<br />
SDP to their financial institutions protecting<br />
their confidential information in the cloud.<br />
VPNs could never scale for that application,<br />
so SDP will be the way of the future. NC<br />
22 NETWORKcomputing JANUARY/FEBRUARY 2018 @NCMagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK