TCPdump & Snort - Intrusion Detection Systems
TCPdump & Snort - Intrusion Detection Systems
TCPdump & Snort - Intrusion Detection Systems
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
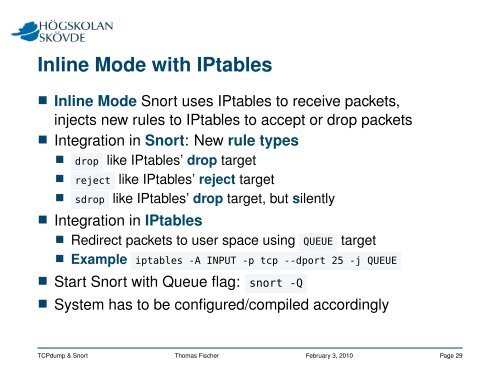
Inline Mode with IPtables<br />
Inline Mode <strong>Snort</strong> uses IPtables to receive packets,<br />
injects new rules to IPtables to accept or drop packets<br />
Integration in <strong>Snort</strong>: New rule types<br />
drop like IPtables’ drop target<br />
reject like IPtables’ reject target<br />
sdrop like IPtables’ drop target, but silently<br />
Integration in IPtables<br />
Redirect packets to user space using QUEUE target<br />
Example iptables -A INPUT -p tcp --dport 25 -j QUEUE<br />
Start <strong>Snort</strong> with Queue flag: snort -Q<br />
System has to be configured/compiled accordingly<br />
<strong>TCPdump</strong> & <strong>Snort</strong> Thomas Fischer February 3, 2010 Page 29