- Page 1: David L. Carter, Ph.D. School of Cr
- Page 5 and 6: Preface The world of law enforcemen
- Page 7 and 8: Executive Summary New expectations
- Page 9 and 10: Management and Human Resources Read
- Page 11 and 12: Intelligence Center (EPIC), Nationa
- Page 13: Challenges to be Faced by Law Enfor
- Page 16 and 17: CHAPTER 6: LAW ENFORCEMENT INTELLIG
- Page 18 and 19: High-Intensity Drug Trafficking Are
- Page 21 and 22: Introduction 1
- Page 23 and 24: Every law enforcement agency in the
- Page 25 and 26: To be effective, the law enforcemen
- Page 27 and 28: Understanding Contemporary Law Enfo
- Page 29 and 30: Understanding Contemporary Law Enfo
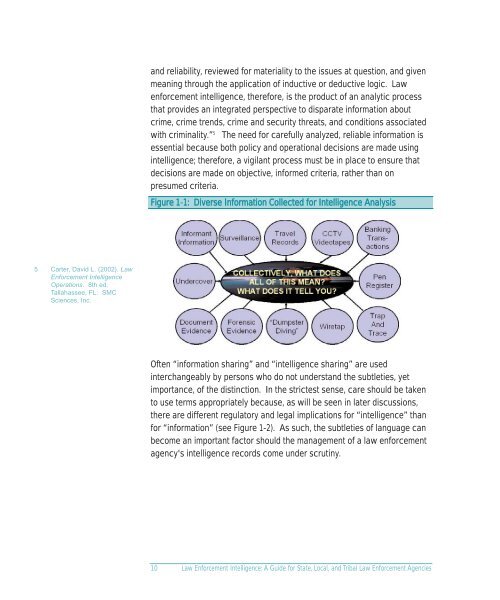
- Page 31: Defining Intelligence Definitions b
- Page 35 and 36: Chapter 3 will show that there is a
- Page 37 and 38: Figure 1-3: Intelligence Community
- Page 39: The lessons learned from this brief
- Page 42 and 43: CHAPTER THREE
- Page 44 and 45: Aggravating these factors has been
- Page 46 and 47: 22 Among the most often cited are M
- Page 48 and 49: 25 United States Senate Select Comm
- Page 50 and 51: In 1975, the Rockefeller Commission
- Page 52 and 53: 37 The President's Commission on La
- Page 54 and 55: 47 Commission on Accreditation for
- Page 56 and 57: 49 Maureen Baginski, FBI Executive
- Page 58 and 59: ecords mandates that the distinctio
- Page 60 and 61: CHAPTER FOUR
- Page 62 and 63: 55 http://it.ojp.gov/topic.jsp? top
- Page 64 and 65: 57 For a good contemporary discussi
- Page 66 and 67: timely and effective deployment of
- Page 68 and 69: officers and members of the communi
- Page 70 and 71: 61 Oftentimes, targets may not be r
- Page 72 and 73: 64 The official Justice Department
- Page 74 and 75: 68 Source: http://www.ci.austin.tx.
- Page 76 and 77: Figure 4-4: Austin, Texas Police De
- Page 78 and 79: CHAPTER FIVE
- Page 80 and 81: 69 See http://www.nationalcrimesqua
- Page 82 and 83:
71 N.B. = “nota bene” means “
- Page 84 and 85:
Figure 5-3: Commodity Flow Chart Il
- Page 86 and 87:
74 NOTE: Discussion of or reference
- Page 88 and 89:
75 Of course, software compatibilit
- Page 90 and 91:
The significant growth of wireless
- Page 92 and 93:
82 Technology Considerations in the
- Page 94 and 95:
See pg. 71 99 http://www.state.gov/
- Page 96 and 97:
public. As a general rule, responsi
- Page 99 and 100:
Law Enforcement Intelligence Classi
- Page 101 and 102:
Law Enforcement Intelligence Classi
- Page 103 and 104:
well as the collection and analytic
- Page 105 and 106:
carefully consider the legal and et
- Page 107 and 108:
geographic and temporal variables w
- Page 109 and 110:
4. Lack of intelligence analysis. 5
- Page 111 and 112:
Figure 6-1: Fact Sheet - National C
- Page 113 and 114:
Managing the Intelligence Function
- Page 115 and 116:
Managing the Intelligence Function
- Page 117 and 118:
• Establishing the ability to det
- Page 119 and 120:
(IALEIA) and the Law Enforcement In
- Page 121 and 122:
Figure 7-1: Sample Mission Statemen
- Page 123 and 124:
180 variables to assess in an intel
- Page 125 and 126:
A key element to understand is that
- Page 127:
http://www.terrorismcentral.com/New
- Page 130 and 131:
CHAPTER EIGHT
- Page 132 and 133:
131 For more detail, see: Wells, Ia
- Page 134 and 135:
133 Bureau of Justice Assistance, C
- Page 136 and 137:
137 See http://www.rcta.org/counter
- Page 138 and 139:
141 For further information on DEA
- Page 140 and 141:
146 See http://www.whitehousedrugpo
- Page 142 and 143:
155 It is anticipated that the curr
- Page 144 and 145:
122 Law Enforcement Intelligence: A
- Page 146 and 147:
CHAPTER NINE
- Page 148 and 149:
158 http://www.iir.com/riss/maglocl
- Page 150 and 151:
Traditional support services provid
- Page 152 and 153:
161 The LEO web page is at http://w
- Page 154 and 155:
163 For more information on LEIU se
- Page 156 and 157:
eal-time threat information at the
- Page 158 and 159:
164 For contact information and mor
- Page 160 and 161:
Organization (INTERPOL) 167 INTERPO
- Page 162 and 163:
169 Regional Intelligence Centers a
- Page 164 and 165:
Figure 9-4: Law Enforcement Intelli
- Page 167 and 168:
Intelligence Requirements and Threa
- Page 169 and 170:
Intelligence Requirements and Threa
- Page 171 and 172:
Figure 10-1: Traditional Collection
- Page 173 and 174:
Figure 10-2: Threat Assessment Mode
- Page 175 and 176:
procedures can enhance this process
- Page 177 and 178:
Figure 10-4: “Baseline” Intelli
- Page 179 and 180:
IIN Modes of transportation and con
- Page 181 and 182:
Federal Law Enforcement Intelligenc
- Page 183 and 184:
Federal Law Enforcement Intelligenc
- Page 185 and 186:
• “Confidential” shall be app
- Page 187 and 188:
of officers while not jeopardizing
- Page 189 and 190:
FBI Office of Intelligence The FBI
- Page 191 and 192:
FBI Counterterrorism 190 Designated
- Page 193 and 194:
a comprehensive, all-source-based p
- Page 195 and 196:
question, or release the subject. I
- Page 197 and 198:
and finance, energy, and transporta
- Page 199 and 200:
Figure 11-3: DHS Information Bullet
- Page 201 and 202:
Figure 11-5: DHS Cyber Advisory Fed
- Page 203 and 204:
the Intelligence Division at DEA He
- Page 205 and 206:
developed the National Clandestine
- Page 207 and 208:
• It will rely on web-based commu
- Page 209 and 210:
(HIDTA) Regional Intelligence Cente
- Page 211 and 212:
During FY 2000, the Intelligence Di
- Page 213 and 214:
FinCEN's information sources fall i
- Page 215 and 216:
eing generated by federal law enfor
- Page 217 and 218:
Summary, Conclusions, and Next Step
- Page 219 and 220:
Summary, Conclusions, and Next Step
- Page 221 and 222:
National Criminal Intelligence Shar
- Page 223 and 224:
Refocusing Guided by the results of
- Page 225 and 226:
Appendices
- Page 227 and 228:
Advisory Board 205
- Page 230 and 231:
APPENDIX B
- Page 232 and 233:
212 Reproduced with permission of t
- Page 234 and 235:
B. Specific types of records (inclu
- Page 236 and 237:
several pieces of information indic
- Page 238 and 239:
(2) Probable - The information is c
- Page 240 and 241:
criteria that would indicate when s
- Page 242 and 243:
Security Level Sensitive Confidenti
- Page 244 and 245:
C. Manner of Destruction: Material
- Page 246 and 247:
APPENDIX C
- Page 248 and 249:
213 Prepared by David L. Carter, Mi
- Page 250 and 251:
228 The questions in this audit out
- Page 252 and 253:
229 For example, Intelligence repor
- Page 254 and 255:
3. How often does a review and purg
- Page 256 and 257:
a. How is the possession of persona
- Page 258 and 259:
11. How are physical records secure
- Page 260 and 261:
4. Does the police department have
- Page 262 and 263:
231 Note: Training should go beyond
- Page 264 and 265:
233 For example, grants, cooperativ
- Page 266 and 267:
Section F. Collection 1. Is there a
- Page 268 and 269:
236 A Pointer System - also known a
- Page 270 and 271:
APPENDIX D
- Page 272 and 273:
238 Based on Executive Order 12291,
- Page 274 and 275:
(b) A project shall not collect or
- Page 276 and 277:
(4) The project must institute proc
- Page 278 and 279:
§ 23.30 Funding guidelines. The fo
- Page 280 and 281:
28 CFR Part 23: 1993 Revision and C
- Page 282 and 283:
EFFECTIVE DATE: This clarification
- Page 284 and 285:
“Northwest Market” would not be
- Page 286 and 287:
APPENDIX E
- Page 288 and 289:
Federal Security Clearance Process
- Page 290 and 291:
classified information. Applicants
- Page 292 and 293:
APPENDIX F
- Page 294:
David L. Carter (Ph.D., Sam Houston
- Page 297:
Intelligence Unit Management Audit
- Page 300 and 301:
Law Enforcement Intelligence: A Gui
- Page 302 and 303:
Law Enforcement Intelligence: A Gui
- Page 304 and 305:
Law Enforcement Intelligence: A Gui
- Page 306 and 307:
Law Enforcement Intelligence: A Gui
- Page 308 and 309:
Law Enforcement Intelligence: A Gui
- Page 310 and 311:
Law Enforcement Intelligence: A Gui
- Page 312 and 313:
Law Enforcement Intelligence: A Gui
- Page 314 and 315:
Law Enforcement Intelligence: A Gui
- Page 316 and 317:
Law Enforcement Intelligence: A Gui
- Page 318 and 319:
Law Enforcement Intelligence: A Gui
- Page 320:
Law Enforcement Intelligence: A Gui