The 2011 (ISC)2 Security Congress
The 2011 (ISC)2 Security Congress
The 2011 (ISC)2 Security Congress
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
notifying customers about the outage?”<br />
he says. � ese are examples of processes<br />
and elements that technologists o� en fail<br />
to consider.<br />
“Disaster recovery has been narrowed<br />
down to IT capabilities,” says Zuk.<br />
“� ere is less and less involvement with<br />
the business, which is discouraging. It<br />
should be involved a lot more with DR<br />
planning and testing.”<br />
Addressing people and processes<br />
doesn’t require a huge � nancial investment,<br />
but it does require you to sit down<br />
with the right people and plan for these<br />
actualities. “It takes time and it takes<br />
thought and it takes expertise. You have<br />
to sit down and talk through some of this<br />
stu� , and say ‘what if?’ � e people who<br />
have gone through this problem before<br />
or experienced a disaster are good people<br />
to bring to the table,” Dunlap says.<br />
“You can look at a manual to � gure out<br />
how to back up to tape. But are you backing<br />
up and restoring the right stu� ? What<br />
gets restored � rst? Who in the organization<br />
gets their stu� done � rst?” asks Dunlap.<br />
“� at’s a hard conversation, but they’re<br />
the ones that, as practitioners, we need to<br />
come to the table prepared to have.”<br />
MANAGING RISK<br />
IN THE BOARD ROOM<br />
<strong>The</strong>re is another risk associated with<br />
a company’s people that puts business<br />
continuity in danger. It resides in conference<br />
rooms of businesses everywhere:<br />
potential executive or corporate risk<br />
behavior. “Businesses run the risk of<br />
being knocked out by bad business decisions,<br />
but they don’t take that into consideration,”<br />
says Dunlap.<br />
According to Chris Kaufman, president<br />
of Agovia Consulting, companies<br />
lose millions of dollars every day because<br />
of poor business decisions. Managing this<br />
business risk is an essential part of business<br />
continuity, and it’s vital in today’s<br />
environment. Moreover, “It’s a low-cost<br />
way to manage risk,” Kaufman says.<br />
Kaufman cites a number of examples<br />
of risky business decisions that should be<br />
a red � ag to systems security professionals.<br />
One of these is when management<br />
pushes to release a product on time even<br />
if it’s not ready. “Nobody will remember a<br />
year from now if we’re three months late;<br />
everyone will remember if we lose 10<br />
14 INFOSECURITY PROFESSIONAL ISSUE NUMBER 16<br />
percent of our business,” says Kaufman.<br />
Another risky behavior is the purchase<br />
of systems, products and consulting services<br />
based on hype from trade shows<br />
or industry conferences; or continuing<br />
a rollout that is costing the organization<br />
millions of dollars and is clearly doomed<br />
to fail.<br />
Luckily, it doesn’t cost much to mitigate<br />
risky behavior to ensure business<br />
continuity. It’s simply a new way to<br />
approach decision making. “It’s common<br />
sense,” he says, “getting people to think<br />
along the lines of applying the decisions<br />
they’re making today to the place they<br />
want to be two, or � ve, or even 10 years<br />
from now.” In other words, think about<br />
Become an<br />
the long-term impact of the decisions<br />
you’re making.<br />
� is approach also o� ers a bene� t to<br />
CISOs. “Organizations are holistic, and<br />
to be successful, they should operate as<br />
a uni� ed entity. � ese concepts overarch<br />
and tie the various pieces of the organization<br />
together. � e ideas of risk evaluation,<br />
risk management, and business<br />
continuity have begun to mature. � is<br />
should give a natural entre to partnering<br />
with and being a part of the business, as<br />
opposed to being an order taker,” Kaufman<br />
says.<br />
Crystal Bedell is a freelance writer specializing<br />
in technology.<br />
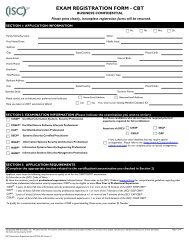
IEEE Certified Biometrics<br />
®<br />
Professional<br />
Why CBP?<br />
<strong>The</strong> IEEE Certified Biometrics Professional ® (CBP)<br />
program has two major components: Certification and<br />
Training. Professionals and organizations can<br />
both benefit from the IEEE CBP program.<br />
Key advantages are:<br />
n Prove your knowledge<br />
n Increase your credibility<br />
n Learn a baseline of industry<br />
knowledge<br />
n Train employees<br />
n Gain a competitive advantage<br />
Learn more and register today!<br />
www.IEEEBiometricsCertification.org