Code (In)Security - ISC
Code (In)Security - ISC
Code (In)Security - ISC
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Configuration differences between the development and<br />
production environments must be ensured so that code can<br />
execute with least privilege, irrespective of the environment. It<br />
is also imperative to ensure that code explicitly set to run with<br />
elevated privileges is carefully monitored (audited) and managed.<br />
Conclusion<br />
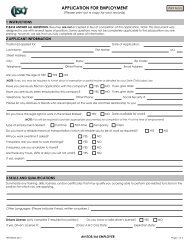
‘Don’t write insecure code’ is one of the eight secure habits discussed<br />
in “8 Simple Rules for Developing More Secure <strong>Code</strong>”. i Without a<br />
thorough understanding of what constitutes insecure code, it would<br />
be unfair to expect developers to write more secure code.<br />
“It is critical to all those who write<br />
code to make it a habit to incorporate<br />
security in the code they write. ”<br />
Should your code fall victim to a security breach, the code itself<br />
would be deemed innocent, but that kind of leniency will not be<br />
extended to the individual, team, or organization that wrote the<br />
code. So it is critical to all those who write code to make it a habit<br />
to incorporate security in the code they write.<br />
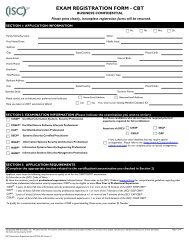
• Validates input<br />
Secure <strong>Code</strong> Characteristics<br />
• Does not allow dynamic construction of queries using<br />
user-supplied data<br />
• Audits and logs business-critical functions<br />
• Is signed to verify the authenticity of its origin<br />
• Does not use predictable session identifiers<br />
• Does not hard-code secrets inline<br />
• Does not cache credentials<br />
• Is properly instrumented<br />
• Handles exceptions explicitly<br />
• Does not disclose too much information in its errors<br />
• Does not reinvent existing functionality, and uses proven<br />
cryptographic algorithms<br />
• Does not use weak cryptographic algorithms<br />
• Uses randomness in the derivation of cryptographic keys<br />
• Stores cryptographic keys securely<br />
• Does not use banned APIs and unsafe functions<br />
• Is obfuscated or shrouded<br />
• Is built to run with least privilege<br />
6<br />
“Writing secure code has the added benefit<br />
of producing code that is of quality –<br />
functional, reliable, and less error-prone.”<br />
It would be far beyond the scope of this paper to enumerate all the<br />
ways that one can avoid writing insecure code, and/or write secure<br />
code. <strong>In</strong>stead, this should be treated as merely an eye-opener to<br />
how to code securely, and the tremendous risks of not doing so.<br />
Just as a game of chess produces an infinite number of moves<br />
once the game begins, with a limited number of opening gambits,<br />
understanding the characteristics of insecure code is one of the<br />
first moves to ensure that code is written to be hacker-resistant.<br />
<strong>In</strong>secure code means checkmate.<br />
www.isc2.org