security profile for openadr - Open Smart Grid - OpenSG - UCA ...
security profile for openadr - Open Smart Grid - OpenSG - UCA ...
security profile for openadr - Open Smart Grid - OpenSG - UCA ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
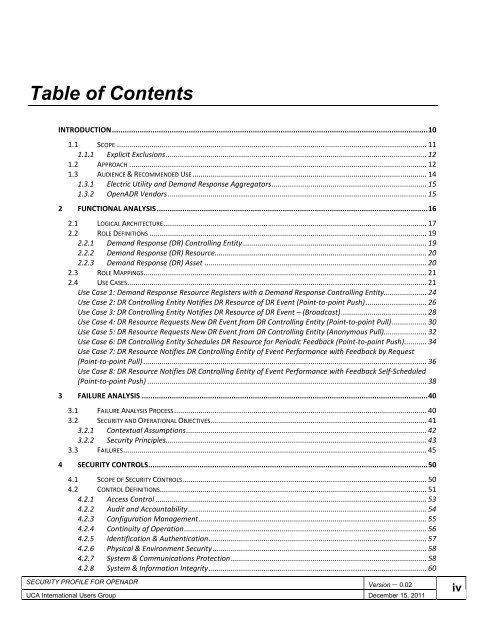
Table of Contents<br />
INTRODUCTION....................................................................................................................................................10<br />
1.1 SCOPE ........................................................................................................................................................ 11<br />
1.1.1 Explicit Exclusions................................................................................................................................ 12<br />
1.2 APPROACH .................................................................................................................................................. 12<br />
1.3 AUDIENCE & RECOMMENDED USE................................................................................................................... 14<br />
1.3.1 Electric Utility and Demand Response Aggregators............................................................................ 15<br />
1.3.2 <strong>Open</strong>ADR Vendors ............................................................................................................................... 15<br />
2 FUNCTIONAL ANALYSIS...............................................................................................................................16<br />
2.1 LOGICAL ARCHITECTURE................................................................................................................................. 17<br />
2.2 ROLE DEFINITIONS ........................................................................................................................................ 19<br />
2.2.1 Demand Response (DR) Controlling Entity .......................................................................................... 19<br />
2.2.2 Demand Response (DR) Resource........................................................................................................ 20<br />
2.2.3 Demand Response (DR) Asset ............................................................................................................. 20<br />
2.3 ROLE MAPPINGS........................................................................................................................................... 21<br />
2.4 USE CASES................................................................................................................................................... 21<br />
Use Case 1: Demand Response Resource Registers with a Demand Response Controlling Entity..................... 24<br />
Use Case 2: DR Controlling Entity Notifies DR Resource of DR Event (Point-to-point Push).............................. 26<br />
Use Case 3: DR Controlling Entity Notifies DR Resource of DR Event – (Broadcast).......................................... 28<br />
Use Case 4: DR Resource Requests New DR Event from DR Controlling Entity (Point-to-point Pull)................. 30<br />
Use Case 5: DR Resource Requests New DR Event from DR Controlling Entity (Anonymous Pull)..................... 32<br />
Use Case 6: DR Controlling Entity Schedules DR Resource <strong>for</strong> Periodic Feedback (Point-to-point Push)........... 34<br />
Use Case 7: DR Resource Notifies DR Controlling Entity of Event Per<strong>for</strong>mance with Feedback by Request<br />
(Point-to-point Pull) ........................................................................................................................................... 36<br />
Use Case 8: DR Resource Notifies DR Controlling Entity of Event Per<strong>for</strong>mance with Feedback Self-Scheduled<br />
(Point-to-point Push) ......................................................................................................................................... 38<br />
3 FAILURE ANALYSIS ......................................................................................................................................40<br />
3.1 FAILURE ANALYSIS PROCESS............................................................................................................................ 40<br />
3.2 SECURITY AND OPERATIONAL OBJECTIVES.......................................................................................................... 41<br />
3.2.1 Contextual Assumptions...................................................................................................................... 42<br />
3.2.2 Security Principles................................................................................................................................ 43<br />
3.3 FAILURES..................................................................................................................................................... 45<br />
4 SECURITY CONTROLS...................................................................................................................................50<br />
4.1 SCOPE OF SECURITY CONTROLS........................................................................................................................ 50<br />
4.2 CONTROL DEFINITIONS................................................................................................................................... 51<br />
4.2.1 Access Control ..................................................................................................................................... 53<br />
4.2.2 Audit and Accountability..................................................................................................................... 54<br />
4.2.3 Configuration Management................................................................................................................ 55<br />
4.2.4 Continuity of Operation....................................................................................................................... 56<br />
4.2.5 Identification & Authentication........................................................................................................... 57<br />
4.2.6 Physical & Environment Security......................................................................................................... 58<br />
4.2.7 System & Communications Protection ................................................................................................ 58<br />
4.2.8 System & In<strong>for</strong>mation Integrity........................................................................................................... 60<br />
SECURITY PROFILE FOR OPENADR<br />
Version – 0.02<br />
<strong>UCA</strong> International Users Group December 15, 2011<br />
iv