NC Sep-Oct 2022
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
NETWORKcomputing<br />
I N F O R M A T I O N A N D C O M M U N I C A T I O N S – N E T W O R K E D www.networkcomputing.co.uk<br />
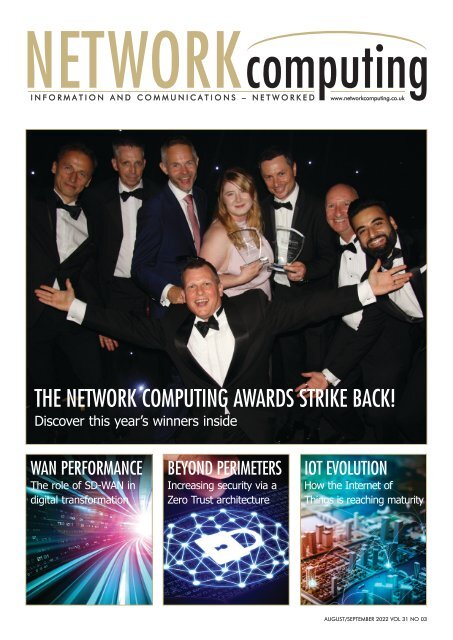
THE NETWORK COMPUTING AWARDS STRIKE BACK!<br />
Discover this year’s winners inside<br />
WAN PERFORMA<strong>NC</strong>E<br />
The role of SD-WAN in<br />
digital transformation<br />
BEYOND PERIMETERS<br />
Increasing security via a<br />
Zero Trust architecture<br />
IOT EVOLUTION<br />
How the Internet of<br />
Things is reaching maturity<br />
AUGUST/SEPTEMBER <strong>2022</strong> VOL 31 NO 03
Platinum Sponsor<br />
Lead Strategy<br />
Stream Sponsor<br />
16-17 Nov <strong>2022</strong><br />
RDS, Dublin<br />
Infrastructure • Services • Solutions<br />
DataCentres Ireland combines a dedicated<br />
exhibition and multi-streamed conference<br />
to address every aspect of planning,<br />
designing and operating your Datacentre,<br />
Server/Comms room and Digital storage<br />
solution – Whether internally, outsourced<br />
or in the Cloud.<br />
EVENT HIGHLIGHTS I<strong>NC</strong>LUDE:<br />
Multi Stream Conference • 25 Hours of Conference<br />
Content • International & Local Experts • 60 Speakers<br />
& Panellists • 100 Exhibitors • Networking Reception<br />
Entry to ALL aspects of DataCentres<br />
Ireland is FREE<br />
DataCentres Ireland is the largest and most<br />
complete event in the country. It is where<br />
you will meet the key decision makers as<br />
well as those directly involved in the<br />
day to day operations.<br />
• Market Overview<br />
• Power Sessions<br />
• Connectivity<br />
• Regional Developments<br />
• Open Compute Project<br />
• Heat Networks and the<br />
Data Centre<br />
• Renewable Energy<br />
• Standby Generation<br />
• Updating Legacy Data Centres<br />
Supporting Organisations<br />
Media Partners<br />
Meet your market<br />
For the latest information & to register online visit<br />
www.datacentres-ireland.com
COMMENT<br />
COMMENT<br />
WHEN IT RAINS, IT POURS<br />
At the time of writing significant areas of England and Wales are still experiencing a<br />
hosepipe ban and drought conditions, with no end and precious little rain in sight. But<br />
are we also in danger of edging closer to a different, but equally concerning, form of utility<br />
crisis? In August South Staffs Water was subject to a cyber attack from a ransomware group.<br />
In a statement the water utility said that, while they experienced disruption to their IT network, the<br />
attackers failed to compromise the water supplies in any way. However "The attack demonstrates<br />
that even non-nation state attackers are now getting more brazen in their attempts at high value<br />
targets," according to Stephen Kines, COO of cyber security hardware start-up Goldilock.<br />
"Whilst many APT (advanced persistent threats) groups don’t have the skills to penetrate to the<br />
actual industrial control systems, it shows there is potential to severely disrupt the IT networks that<br />
surround them, freezing up daily operations and impacting customers," he added.<br />
This isn't the only instance of a water utility being subject to a cyber attack that we've looked<br />
at recently - or even the most alarming. In our Jan/Feb issue David Higgins at CyberArk<br />
detailed the failed attempt to poison the water supply of a Florida city. In this instance the<br />
threat actor was only thwarted by the swift actions of a water plant operator who spotted the<br />
attack as it was taking place - but not before the attacker "allegedly boosted the concentration<br />
of sodium hydroxide in the water by a factor of 100." As David wrote at the time, "For a variety<br />
of reasons the public utilities industry is particularly vulnerable to threat actors. For one thing,<br />
much of the infrastructure that controls industrial control systems - the systems supporting key<br />
services - was developed in the 1980s or 1990s. Because of the crucial nature of utility operations,<br />
the creators of these systems had to prioritise system availability and interoperability over<br />
security. As these systems got more integrated with internet-connected IT over time, they<br />
became more appealing targets for hackers."<br />
REVIEWS:<br />
Dave Mitchell<br />
DEPUTY EDITOR: Mark Lyward<br />
(netcomputing@btc.co.uk)<br />
PRODUCTION: Abby Penn<br />
(abby.penn@btc.co.uk)<br />
DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk<br />
SALES:<br />
David Bonner<br />
(david.bonner@btc.co.uk)<br />
Julie Cornish<br />
(julie.cornish@btc.co.uk)<br />
SUBSCRIPTIONS: Christina Willis<br />
(christina.willis@btc.co.uk)<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexion Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK £35/year, £60/two years,<br />
£80/three years;<br />
Europe:<br />
£48/year, £85/two years £127/three years;<br />
ROW:<br />
£62/year, £115/two years, £168/three years;<br />
Subscribers get SPECIAL OFFERS — see subscriptions<br />
advertisement; Single copies of<br />
Network Computing can be bought for £8;<br />
(including postage & packing).<br />
© <strong>2022</strong> Barrow & Thompkins<br />
Connexion Ltd.<br />
All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent, in<br />
writing, from the publisher.<br />
The fact that the South Staffs Water ransomware attack took place during a national drought<br />
is also alarming, and could indicate that threat actors are now deliberately targeting authorities<br />
during critical periods. And our current water shortage could also have significant implications<br />
for UK data centers, according to David Bicknell at GlobalData: "With the UK experiencing its<br />
driest summer for 50 years - and water companies failing to reduce leaks - operators hoping<br />
to use 25 liters of drinking water an hour to cool data centers as a cheaper alternative to energy-guzzling<br />
refrigeration systems are finding their options running dry."<br />
On a more positive note Phil Beecher, CEO and President of Wi-SUN Alliance, writes in his<br />
article in this issue that the utilities sector is set to benefit from new IoT initiatives that include<br />
water loss/leak detection. This is according to the findings of Wi-SUN’s latest IoT research study.<br />
With three in four organisations planning to implement these initiatives "the opportunities for savings<br />
and increased efficiency in some of these use cases are high." We'll drink to that... <strong>NC</strong><br />
GET FUTURE COPIES FREE<br />
BY REGISTERING ONLINE AT<br />
WWW.NETWORKCOMPUTING.CO.UK/REGISTER<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 03
CONTENTS<br />
CONTENTS<br />
COMMENT.....................................3<br />
When it rains, it pours<br />
INDUSTRY NEWS.............................6<br />
The latest networking news<br />
ARTICLES<br />
A QUESTION OF TRUST...................8<br />
By Mark Cooke at Xalient<br />
WAN PERFORMA<strong>NC</strong>E...........20<br />
David Trossell at Bridgeworks offers a guide<br />
to achieving higher WAN performance, and<br />
Simon Hill at Certes Neworks explains why<br />
CISOs should now be looking at SD-WANs<br />
- or risk being left behind<br />
IOT REACHES MATURITY.......26<br />
After many years of hype, the Internet of<br />
Things is finally maturing to a point where<br />
organisations are turning strategies into<br />
reality and planning into action, according<br />
to Wi-SUN Alliance’s Phil Beecher<br />
A U G U S T / S E P T E M B E R 2 0 2 2<br />
BEYOND PERIMETERS............16<br />
As cybercriminals continue to develop new<br />
attack techniques the traditional notion of a<br />
strong external perimeter being the best<br />
defence against compromise has shown<br />
itself to be inadequate<br />
THE SASE APPROACH TO<br />
NETWORK SPRAWL...............22<br />
Sprawling networks and long lead times - is<br />
there another approach we can take? Justin<br />
Day, CEO and Co-Founder of Cloud<br />
Gateway, shows us the way<br />
NETWORK COMPUTING<br />
AWARDS <strong>2022</strong>....................28<br />
Held in London in July, the 16th annual<br />
Network Computing Awards celebrated<br />
industry success stories from the past twelve<br />
months. Discover who won what inside!<br />
WHY EMPLOYEE WORKSTATION<br />
SECURITY CAN’T BE FORGOTTEN....12<br />
By David Higgins at CyberArk<br />
OVERSIGHT ABOVE I.T.<br />
TRANSFORMATION........................14<br />
By Mat Clothier at Cloudhouse<br />
DOWNTIME DOLDRUMS AND SMART<br />
SOLUTIONS...................................15<br />
By Alan Stewart-Brown at Opengear<br />
STAY AWARE OF RANSMOMWARE..18<br />
By Florian Malecki at Arcserve<br />
WHY CISOs MUST NOW<br />
EMBRACE SD-WAN........................20<br />
By Simon Hill at Certes Networks<br />
WAN ACCELERATION OR EDGE<br />
COMPUTING?...............................24<br />
By David Trossell at Bridgeworks<br />
PRODUCT REVIEW<br />
NETALLY ETHERSCOPE EXG-300......10<br />
PROGRESS FLOWMON<br />
COLLECTOR 12.1..........................14<br />
04 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
INDUSTRY NEWS<br />
NEWSNEWS<br />
NEWS NEWS<br />
NEWS NEWS NEWS NEWS<br />
NEWS NEWS<br />
Keeping data centres cool during heat waves<br />
Vertiv has issued new guidance to data centre operators and<br />
associated businesses to help them navigate the increasing<br />
challenge of heat waves, which have caused outages and<br />
disruptions at data centres in the UK. The heat waves have also<br />
led to Thames Water launching a review of the increasing<br />
demand data centres are putting on water supplies, particularly<br />
in the Slough area, which is set to become the second biggest<br />
data centre hub in the world.<br />
To keep systems cool and help ensure data centre availability,<br />
Vertiv experts recommend that, depending on the data hall<br />
load, operators should run as many units as possible to reduce<br />
the load on each cooling unit. Typically, an organisation would<br />
run all redundant units, but if the IT load is not 100%, one<br />
should run enough units to get the per-cooling unit as close as<br />
possible. This keeps the refrigerant pressures lower so there is<br />
not a risk of trips on high pressure with the high ambient<br />
temperature. It also provides a more efficient operating point.<br />
They should also schedule a regular maintenance plan. Vertiv<br />
recommends its customers schedule preventive maintenance<br />
quarterly. For compressor-based (DX) units, they recommend<br />
quarterly or more frequent cleaning of the condenser coil, as<br />
the lack of proper and regular cleaning can cause more of a<br />
reduction in the overall thermal unit capacity than the ambient<br />
temperature itself. Additionally, properly maintaining the<br />
refrigerant charge level helps to enable the design capacity and<br />
operating efficiency to function smoothly. A refrigerant charge<br />
that is too low or too high, can cause operational inefficiencies<br />
"If one thing is clear, it is that we need to be prepared for these<br />
extreme weather conditions to become more commonplace, so<br />
adapting to this inevitability is crucial” said Karsten Winther,<br />
president for Vertiv in EMEA. Our service teams have proved<br />
invaluable in providing the guidance and support required to<br />
not only manage the immediate impact, but to discuss with<br />
customers how they can plan ahead to build in resiliency."<br />
Expereo acquires Breeze Networks<br />
Breeze Networks is a managed service provider of cloudbased<br />
(SD-WAN) network connectivity and security solutions<br />
for enterprises and government agencies. An innovative and<br />
flexible network integrator, Breeze sources and manages the best<br />
SD-WAN networking and security solutions on the market. As<br />
part of the acquisition, Expereo welcomes Matthew Lea, CTO of<br />
Breeze Networks as Technical Portfolio Lead. His expertise will be<br />
a great addition to the knowledge base of Expereo's Technical<br />
team, led by CTO, Kristaps Petrovskis. Lea will drive Expereo's<br />
expansion plans for its SD-WAN/SASE practice, solidifying the<br />
company's presence in the UK market in his new role at Expereo.<br />
"This acquisition comes at an exciting time, as we expand our<br />
SD-WAN services to address the growing need for agile, costeffective<br />
cloud access and global network solutions in the<br />
market. With our shared vision to simplify global connectivity<br />
and provide world-class customer experience, the expertise of<br />
the team of professionals behind Breeze Networks will contribute<br />
great value as we join forces," said Expereo CEO Irwin Fouwels.<br />
Giganet selects Neos Networks for network expansion<br />
Neos Networks has been chosen by Giganet, an<br />
established ISP, to provide backhaul and data centre<br />
connectivity to support its new southern counties network and<br />
its ambitious plans to rollout gigabit Fibre-to-the-Premise<br />
(FTTP) services. Through strategic network partnerships,<br />
Giganet is already able to offer full fibre broadband services to<br />
millions of homes and businesses all over the UK. The next<br />
step for Giganet is an expansion which will see it cover more<br />
homes and businesses, beginning in the south of England<br />
using its own network. In the next four years, Giganet plans to<br />
build to 300,000 homes across Hampshire, Wiltshire, Dorset<br />
and West Sussex with its own fibre network rollout.<br />
Endpoint Detection and Response Beta from VIPRE<br />
VIPRE Security Group is preparing to add a new<br />
cybersecurity tool to its comprehensive suite of offerings.<br />
The new solution, VIPRE Endpoint Detection and Response<br />
(EDR), is designed to help SMBs and IT partners navigate the<br />
complexities of EDR management from a single, easy-to-use<br />
console. While VIPRE EDR will be available publicly towards<br />
the end of <strong>2022</strong>, the company is ready to launch its Beta<br />
program and seeks global users to test the product and<br />
provide feedback. The VIPRE EDR Beta sign-up will be<br />
available here: https://bit.ly/3QFHU4<br />
06 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
INDUSTRY NEWS<br />
Hibs get dibs on new Acronis and Dunedin IT partnership<br />
Hibernian FC has announced an innovative multi-year<br />
partnership with Acronis and Dunedin IT, one of Scotland's<br />
most trusted and experienced technology and connectivity<br />
providers providing end-to-end services. Acronis will provide<br />
hybrid cloud solutions for backup, disaster recovery, secure file<br />
sync, and data access, to become Hibernian FC's Principal<br />
Cyber Protection Partner. This partnership will be supported by<br />
the expertise of Dunedin IT, which will deliver Acronis cyber<br />
protection solutions to improve data storage and access,<br />
creating a more efficient and collaborative workflow. In what is<br />
a significant agreement for the team, Acronis and Dunedin IT<br />
will have Principal Partner status at the club. Dunedin IT will<br />
have its logo printed on the lower back of the men's first team<br />
home, away, and third kits for the <strong>2022</strong>/2023 season.<br />
Increasing IT complexity impacts ROI, finds SolarWinds<br />
With hybrid and remote work amplifying the challenge of<br />
managing distributed IT environments, 84% of IT<br />
professionals believe the ROI of their projects has been<br />
negatively impacted in the last 12 months, according to new<br />
research from SolarWinds. The report, which examines the<br />
acceleration of digital transformation efforts and its impact on IT<br />
departments, also shows a third (33%) of IT professionals think<br />
complexity added between four and seven months of extra work<br />
to get their project to completion.<br />
Commenting on the news, SolarWinds President and CEO<br />
Sudhakar Ramakrishna said, "Many organisations are struggling<br />
to drive forward transformation amidst increasingly distributed<br />
and complex IT environments. "Amplified by a global move<br />
towards hybrid and remote work, applications and workloads are<br />
now run across both cloud and on-premises infrastructure. This is<br />
not only hindering the ability to deliver benefits to end users in a<br />
timely fashion but also significantly impacting the bottom line.<br />
"In this challenging landscape, IT professionals are increasingly<br />
looking towards observability to manage these growing levels of<br />
complexity. By understanding where to prioritise their efforts,<br />
teams can manage hybrid IT realities more effectively and<br />
achieve the ROI targeted in their planned projects, which spells<br />
long-term success for teams, businesses, and their customers."<br />
Fusion IT appoints new CTO and earns ISO accreditation<br />
Yorkshire-based IT support and solutions provider Fusion IT<br />
Management has announced the appointment of James<br />
Robinson as its new chief technical officer (CTO). James<br />
previously held the role of IT operations manager and, during his<br />
time with the business, has successfully built the firm’s cloud<br />
platform, evolving from a handful of servers to a large multiredundant<br />
array of complex systems, helping the business reach<br />
new heights. Commenting on his new role, James said: "I'm<br />
excited for this next chapter in my new role as the CTO of Fusion<br />
IT. I want to express my gratitude to Jamie for trusting and<br />
supporting me to grow in the past three years."<br />
James Robinson<br />
Fusion IT has also welcomed two new recruits to the wider<br />
team. Karolina Mroz joins Fusion in the role of MatterSphere<br />
developer, after having successfully completed an undergraduate<br />
course in Computer Science at Sheffield Hallam University.<br />
MatterSphere is a robust client and matter management system<br />
that provides legal firms with a single, unified way to view and<br />
manage day-to-day activities. Joining her in the MatterSphere<br />
team is Kamil Sora, who will work as a support developer. A<br />
Computer Science with Artificial Intelligence graduate, Kamil will<br />
support the development team with the MatterSphere product to<br />
generate and produce data reports to help ensure that the most<br />
effective solution is implemented to meet the clients' needs.<br />
To top off a fine period of achievement for Fusion, the firm has<br />
also announced its achievement of ISO 9001 and 27001<br />
standards. Fusion IT is one of only a small number of IT<br />
businesses based in West Yorkshire to achieve this status.<br />
NEWS NEWSNEWS<br />
NEWS<br />
NEWS NEWS NEWS NEWS NEWS<br />
NEWS<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 07
OPINION: ZERO TRUST<br />
A QUESTION OF TRUST<br />
ZERO TRUST IS NOW A BUSINESS IMPERATIVE TO ENABLE THE<br />
SECURE, HYBRID WORKING ENTERPRISE, ACCORDING TO MARK<br />
COOKE, CHIEF OPERATING OFFICER AT XALIENT<br />
Without a doubt, cybersecurity will<br />
continue to be a topic riding high on<br />
the C-Suite agenda throughout<br />
<strong>2022</strong>. With intensifying trade disputes, an<br />
escalating threat landscape, a highly<br />
distributed workforce, supply chains stretched<br />
to breaking point by the pandemic, and extra<br />
pressure exerted by the ongoing effects of<br />
Brexit and other geo-political issues, having a<br />
secure, productive, agile and cost-effective<br />
security framework in place will be paramount.<br />
It's evident that today's enterprises conduct<br />
business and use digital technologies in ways<br />
that are evolving constantly. This digital<br />
transformation is making traditional perimeterbased<br />
cybersecurity IT infrastructure redundant.<br />
The days when every user and every device<br />
operating from within an organisation's<br />
premises or firewall could be automatically<br />
trusted are over for good. The last two years<br />
have accelerated the global shift to the<br />
cloud as enterprises look towards digital<br />
transformation and the need, brought into<br />
even sharper focus by the pandemic, for<br />
business agility and higher productivity,<br />
while also adapting to the new 'here for<br />
good' model of hybrid working. And with<br />
this come new challenges for cybersecurity.<br />
The traditional security perimeter is rendered<br />
ineffective in this new world, and most legacy<br />
security systems, which were designed for a<br />
data centre rather than a cloud-centric world,<br />
equally so. This is because the traffic between<br />
an employee and a cloud-based application<br />
can now completely bypass the traditional<br />
security perimeter, together with any incumbent<br />
security controls or policies. The network is no<br />
longer a secured enterprise network. Instead,<br />
the insecure internet has fast become the new<br />
corporate network. It's time for organisations to<br />
take action if they are to keep attackers out<br />
and keep their businesses and people safe.<br />
As working from home has now become<br />
globally widespread, security technologies and<br />
processes based purely on established<br />
geographic location are becoming irrelevant.<br />
Millions of workers across the world shifted<br />
from being office-based to working from<br />
home, where they share broadband<br />
connections with family and friends. With a<br />
remote workforce, the use of potentially<br />
unsecured Wi-Fi networks and devices<br />
increases security risks exponentially. The<br />
change in workers' expectations, with regards<br />
to being able to work from home, means<br />
remote working is unlikely to be a passing<br />
trend. Subsequently these challenges and risks<br />
around connectivity and security are here for<br />
the long term.<br />
A popular, but now outdated, option in<br />
providing secure connectivity to corporate<br />
applications has been to use a Virtual Private<br />
Network (VPN). Whilst this will encrypt traffic<br />
between a device and an application, and<br />
provide a level of authentication, a VPN<br />
provides access to the corporate network as<br />
well as the applications that are served from it.<br />
As a result, this can give inappropriate levels of<br />
access to applications and functions that are<br />
outside an employee's job role or profile. This<br />
significantly increases the risk of a cyber security<br />
incident. For today's sophisticated threat actors,<br />
it is a trivial task to deduce that an organisation<br />
is using a centralised firewall and launch a<br />
DDoS attack via an online service that seriously<br />
impacts productivity. So, if VPNs are no longer<br />
fit for purpose, is there a better way?<br />
ADAPTING TO ZERO TRUST<br />
In short, yes there is. In this new environment,<br />
more and more enterprises are adopting a<br />
Zero Trust approach. Zero Trust is a security<br />
concept centered on the belief that<br />
organisations should not automatically trust<br />
anything inside or outside its perimeter, and<br />
instead must verify anything and everything<br />
trying to connect to its systems before granting<br />
access. Zero Trust employs "never trust" and<br />
"always-verify" principles, offering a secure<br />
platform for users to access applications, from<br />
anywhere, whether housed in data centres or<br />
the cloud. Security becomes all about context -<br />
where a user is, what role they have, what data<br />
they need and when - rather than about<br />
location - inside or outside the organisation's<br />
firewall. And Zero Trust ensures constantly<br />
adaptive levels of trust and verifications as<br />
these parameters change.<br />
As the pressure to protect enterprise systems<br />
and data grows significantly, and attacks<br />
become more sophisticated, CIOs and CISOs<br />
are moving the implementation of Zero Trust<br />
across all aspects of their infrastructure, to the<br />
08 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION: ZERO TRUST<br />
top of the corporate agenda. By removing the<br />
centralised approach to policy enforcement<br />
and moving towards a distributed model<br />
where security is delivered via the cloud,<br />
organisations can begin to move to a model<br />
where users and devices can be connected to<br />
applications and data securely and efficiently -<br />
regardless of geography.<br />
CHALLENGES AND BENEFITS<br />
It is undoubtedly a challenge for most large<br />
enterprises with established IT teams, that have<br />
worked on a 'trust but verify' basis using<br />
corporate firewalls and VPNs, to change<br />
direction and move towards a Zero Trust<br />
framework. But in our view, adopting this<br />
approach does bring considerable benefits.<br />
Without the concept of a fixed network<br />
perimeter, users can be anywhere and on any<br />
device. It's also true today that the devices<br />
employees are using are much less likely to be<br />
ones assigned by their employer. Employerowned<br />
laptops and phones are traditionally<br />
managed, patched, and kept up to date with<br />
security tools and policies. However, in the era<br />
of remote working, employees may forget<br />
basic cyber hygiene skills and start, or indeed<br />
are actively encouraged, to use their own<br />
devices to access corporate resources. If the<br />
enterprise moves to a Zero Trust approach,<br />
CISOs can reduce the attack surface of the<br />
business by only giving employees access to<br />
the applications they need to work with.<br />
A MODULAR ZERO TRUST APPROACH<br />
In our experience, one of the key questions<br />
when adopting a Zero Trust approach is<br />
"where do we start?" When trying to secure key<br />
milestones of the journey between an<br />
employee (or indeed more often a sensor or<br />
other IoT device) and an application, the sheer<br />
amount of technology touchpoints involved<br />
can prove overwhelming. Most enterprises<br />
typically have a subset of existing tooling that<br />
address some key aspects of trust, e.g.<br />
multifactor authentication, identity and access<br />
management, network access control etc.<br />
Extending the approach across multiple<br />
technology towers, however, is challenging.<br />
This is where a modular approach can work<br />
effectively. <strong>Sep</strong>arating out key functions or<br />
"journeys" into modules can allow a more<br />
focused approach to the application of a<br />
security policy, from a procurement,<br />
implementation and budgetary perspective.<br />
Although every enterprise will have its own<br />
priorities that dictate the appropriate starting<br />
point and path taken. In our view, there are<br />
four key areas to a Zero Trust journey that<br />
need to be considered. Firstly, Identity and<br />
Access, enabling you to recognise and<br />
authenticate user and device access, ensuring<br />
appropriate levels of access are granted<br />
dependent on role-based policies, rather than<br />
location. If your current landscape of IDAM<br />
systems is complex today, as so many are<br />
following acquisitions, disposals and global<br />
reorganisations, then these can now be<br />
simplified with a single cloud overlay. This<br />
takes away complexity, acting as a central<br />
repository of users and devices, managing<br />
starters and leavers, and much more.<br />
The second consideration is the network itself,<br />
ensuring you can connect users and devices to<br />
apps and data over a high performing, secure<br />
and constantly optimised pathway - using<br />
cloud solutions such as SD-WAN for example.<br />
And of course, being able to monitor the entire<br />
pathway is more crucial than ever, helping<br />
spot, avoid or remediate issues before they<br />
impact your business operations. We use an<br />
advanced proprietary AI-powered tool called<br />
Martina that not only does this, but<br />
automatically fixes issues too; in many cases<br />
even before a user sees a problem. Monitoring<br />
these new complex data pathways is critical to<br />
both performance and security.<br />
The third area we focus on is the Secure<br />
Service Edge - this ensures a secure gateway to<br />
the cloud, helping you get users on and off the<br />
internet quickly, efficiently and securely, using<br />
cloud on-ramp solutions, while ensuring a<br />
high-quality digital experience. Finally, we look<br />
at your Apps and Data, a vital stage ensuring<br />
these are properly segmented to protect<br />
against cross-infection should a virus occur.<br />
As an example, if the network itself is your<br />
most pressing area for action, we see SD-WAN<br />
as a core solution component in the journey to<br />
Zero Trust. It makes management of network<br />
infrastructure easy, allowing IT to avoid<br />
complex network-security architectures, whilst<br />
providing the highest security through a clouddelivered<br />
model. All traffic is securely<br />
connected through a cloud-delivered service,<br />
whatever the connection type - mobile, satellite<br />
or home broadband. And because the<br />
intelligence of the network is software-driven<br />
and orchestrated centrally, it can manage the<br />
user's journey through an insecure internet to<br />
the location of the application, at the same<br />
time compressing other applications to<br />
improve the user experience.<br />
An SD-WAN solution can be procured and<br />
implemented as a standalone initiative - but<br />
the real zero trust value comes when it's<br />
incorporated as part of a total security and<br />
networking solution, often known as SASE,<br />
Secure Access Service Edge.<br />
Addressing all four areas described above<br />
will leave your enterprise secure, resilient,<br />
agile and connected - providing firm<br />
foundations for successful digital<br />
transformation. At Xalient we call this our Zero<br />
Trust Framework - and by using this framework<br />
we ensure that we consider every stage of the<br />
journey through the lens of Zero Trust. It's our<br />
belief too, that to achieve successful and<br />
ongoing digital transformation, enterprises<br />
must address the challenges of security<br />
transformation right at the outset.<br />
THE CIO AND CISO IMPERATIVE<br />
Now is the time for CIOs and CISOs to work<br />
together to design their Zero Trust journey<br />
together - investing in modern technologies,<br />
rather than trying to retro-fit legacy systems, to<br />
ensure their organizations are successful and<br />
secure in today's work-from-anywhere and<br />
cloud-centered world. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 09
PRODUCT REVIEW<br />
NetAlly EtherScope<br />
EXG-300<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
NetAlly's EtherScope nXG bowled us<br />
over when we first reviewed it as this<br />
ruggedised handheld device delivers<br />
a stunning range of wired and wireless<br />
diagnostics features. Not content to rest on<br />
its laurels, NetAlly has launched the new<br />
and improved EXG-300 model which<br />
delivers full visibility into Wi-Fi 6 and 6E<br />
networks and supports all three 2.4GHz,<br />
5GHz and 6GHz bands.<br />
A feature that makes the EtherScopes very<br />
appealing to technicians and engineers is<br />
that they run an Android-based OS - anyone<br />
that can use a mobile will find the EXG-300<br />
very easy to use. The large 5in. colour<br />
touchscreen presents a wide selection of<br />
icons for all tasks and the screen's FAB<br />
(floating access button) opens floating action<br />
menus offering instant access to further<br />
analysis tools related to the selected task.<br />
The EXG-300 offers a wealth of wired<br />
cable testing and network diagnostics<br />
features and supports 10GbE copper and<br />
fibre, multi-Gigabit and Gigabit<br />
connections, plus it can uniquely display<br />
data gathered from wired and wireless<br />
networks simultaneously. It can analyse and<br />
report on PoE switch ports and supports the<br />
802.3af/at/bt standards, all classes from 0<br />
to 8 and Cisco's proprietary UPoE.<br />
The device is, indeed, very easy to use and<br />
we started by analysing the lab's Wi-Fi 6<br />
network using the AutoTest profiles. The<br />
default Wi-Fi profile includes a set of<br />
predefined tests covering areas such as<br />
SSIDs, channels, AP details, DNS connectivity<br />
and so on, and once we had connected it to<br />
our Zyxel WAX610D Wi-Fi 6 AP, the EXG-300<br />
automatically created a new test profile for us<br />
which we started with one tap.<br />
The test only takes a few seconds and the<br />
EXG-300 returned a wealth of wireless<br />
information presented as 'cards' in its screen,<br />
each with colour coding to indicate<br />
warnings or errors. Tapping on the SSID<br />
card revealed graphs and tables for signal<br />
quality, channel utilisation, retries and PHY<br />
transmission rates, while the Channel card<br />
confirmed that our AP's 160MHz channels<br />
were operational, showing all others in use<br />
and their frequency range.<br />
All this is just to whet your appetite as tapping<br />
on the main WiFi icon reveals everything<br />
about all discovered internal and external<br />
wireless networks in your vicinity. Along with<br />
channel maps and overlap graphs, it shows all<br />
channels, their active SSIDs and the APs using<br />
them, every detected SSID and their security<br />
status and all clients along with their<br />
associated SSIDs and the encryption standard<br />
being used plus RF and traffic statistics graphs.<br />
There's more, as the integral AirMapper app<br />
is provided for indoor and outdoor Wi-Fi site<br />
surveys and creating signal heatmaps. Copy a<br />
site map to the EXG-300, create a survey, add<br />
your datapoints and the results can be<br />
uploaded with one tap to the NetAlly Link-Live<br />
cloud portal for further analysis and sharing<br />
with colleagues.<br />
We aren't done yet, as along with the Test<br />
Accessory iPerf server unit and a tri-band<br />
directional antenna, the EXG-300 kit option<br />
includes NetAlly's NXT-1000 dual-band<br />
spectrum analyser. We plugged it into the<br />
device's upper USB port, tapped the Spectrum<br />
icon and were presented with frequency<br />
spectrum heat map, historical waterfall and<br />
real-time signal level graphs - great for<br />
spotting rogue devices that may be interfering<br />
with your wireless services.<br />
We didn't think it was possible to cram any<br />
more features into the EtherScope nXG - but<br />
NetAlly has proved us wrong. The compact<br />
and portable EXG-300 teams up an incredible<br />
range of wired and wireless diagnostics and<br />
troubleshooting tools with extreme ease of use,<br />
making it the perfect partner for network<br />
engineers - especially those tasked with<br />
installing and maintaining high performance<br />
Wi-Fi 6/6E wireless networks. <strong>NC</strong><br />
Product: EtherScope EXG-300<br />
Supplier: NetAlly<br />
Website: www.netally.com<br />
Telephone UK: +44 (0)141 816 9600<br />
Telephone US: +1-719-755-0770<br />
Price: From £8,575 exc VAT<br />
10 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION: ENDPOINT SECURITY<br />
WHY EMPLOYEE WORKSTATION SECURITY CAN'T BE FORGOTTEN<br />
DAVID HIGGINS, SENIOR DIRECTOR, FIELD TECHNOLOGY OFFICE AT CYBERARK GIVES US SIX<br />
ENDPOINT SECURITY RULES TO ISOLATE ATTACKER ACTIVITY, REDUCE THE IMPACT OF A BREACH<br />
AND ALLOW ORGANISATIONS TO REGAIN CONTROL OF THEIR ENVIRONMENTS<br />
Arecent Accenture study found that 63%<br />
of high-growth companies have<br />
already adopted 'productivity<br />
anywhere'. It's a switch which, two years later,<br />
is still causing issues for businesses -<br />
specifically their security teams. This is mainly<br />
as a result of employee workstations now<br />
being put at the edge. Far beyond the 'walls'<br />
of the traditional corporate network, they're<br />
an easy route in for attackers looking to<br />
compromise identities, launch ransomware<br />
attacks, exploit privileged credentials and<br />
infiltrate sensitive corporate networks.<br />
PROTECTING THE ENDPOINT<br />
Having these workstations - or endpoints - in<br />
such an unsecure situation is leaving<br />
organisations at an unnecessary and increased<br />
risk of an endpoint attack. This is especially<br />
worrying as we know that, during these types of<br />
attack, by the time incident response specialists<br />
are called in the environment has already<br />
become overrun by threat actors.<br />
It is vital to an organisation's overall security<br />
posture that they don't neglect endpoints -<br />
especially workstations. Doing so will inevitably<br />
end in a cyber assault. While this might sound<br />
like a big task, there are actually only six steps<br />
which security teams need to adhere to in order<br />
to protect them. These are fundamental identity<br />
security rules and safeguards:<br />
1. Remove local admin rights: Administrator<br />
accounts are vital. Not only are they used to<br />
install and update workstation software and set<br />
up system preferences, but they are critical to<br />
the smooth running and management of user<br />
accounts. The security issues arise however, as<br />
admin accounts are privileged, making them<br />
more valuable to attackers and more<br />
susceptible targets for those looking to run<br />
ransomware and other malicious software,<br />
disable antivirus, and block disaster recovery<br />
tools. Moving local admin powers away from<br />
normal users and into a secure digital vault with<br />
credential rotation is the quickest and most<br />
straightforward way to secure employee<br />
workstations. Doing so reduces the ability of<br />
attackers to move through networks, while<br />
lessening the impact of employee mistakes.<br />
2. Implement least privilege: Employees<br />
frequently need to carry out an action which<br />
requires administrative privileges. While these<br />
are usually legitimate and necessary tasks, justin-time<br />
privileged access enables teams to<br />
safely carry out work both in accordance with<br />
policy, and appropriately.<br />
3. Policies for application control: The endpoint<br />
must be able to defend against attacks, as well<br />
as allow or deny known applications. To do<br />
this, and lessen the risk of threats such as<br />
ransomware, organisations must be able to<br />
"greylist" apps and implement advanced control<br />
policies, ensuring workers use only secure,<br />
trusted applications.<br />
4. Don't forget cached credentials: Credential<br />
theft is one of the greatest risks to<br />
organisations. These can be saved in memory<br />
by many common business apps, and web<br />
browsers and password managers store<br />
application and website credentials<br />
locally. The fact threat<br />
actors can easily and<br />
frequently get cached<br />
credentials without<br />
requiring admin<br />
capabilities, makes<br />
having an<br />
endpoint security<br />
layer even more<br />
essential to overall security.<br />
5. Leave and set traps: It may sound left-field,<br />
but endpoint protection technologies that<br />
support privilege deception functionality, such<br />
as the capability to generate phoney "honeypot"<br />
privileged accounts, can help identify potential<br />
attackers in real-time.<br />
6. Monitor privileged activities: Attackers are<br />
sneaky and often go unnoticed when testing a<br />
network's defences. By proactively monitoring<br />
privileged workstation activity, organisations<br />
can automatically identify and stop adversaries<br />
before they move laterally, elevate privileges, or<br />
do significant harm.<br />
FINAL THOUGHTS<br />
Endpoint security has been something<br />
organisations have been battling against for<br />
years, and the added challenges they face<br />
thanks to the proliferation of hybrid working are<br />
cause for concern. With inadequately protected<br />
employee workstations posing as the perfect<br />
vulnerability for attackers to exploit, it's<br />
imperative for organisations to act swiftly to<br />
protect endpoints. <strong>NC</strong><br />
12 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
PRODUCT REVIEW<br />
Progress Flowmon<br />
Collector 12.1<br />
PRODUCT REVIEW<br />
PRODUCT<br />
REVIEWPRODUCT RE<br />
NetOps and SecOps teams that<br />
demand full visibility into their<br />
networks will find the Flowmon<br />
product family from Progress delivers precisely<br />
what they need. The suite provides a wealth of<br />
network traffic flow monitoring, analysis and<br />
reporting tools and the best part is they are all<br />
managed centrally from a single web console.<br />
Features include traffic, application, server<br />
latency and end-user experience monitoring<br />
along with packet capture and analysis. This<br />
latest version takes monitoring into the cloud<br />
with support for native flow logs from AWS,<br />
Azure and Google Cloud.<br />
Previously, monitoring these cloud platforms<br />
required a probe installed to the relevant<br />
service and traffic mirroring configured -<br />
requirements that will ramp up ongoing costs,<br />
making cloud flow monitoring very expensive.<br />
Flowmon's support for native flows means<br />
probes aren't required and as much smaller<br />
quantities of data are generated, cloud data<br />
transfer charges are reduced significantly.<br />
The Flowmon network operations solution on<br />
review comprises the Flowmon Collector,<br />
Probe, agentless APM (application performance<br />
monitoring) and packet investigator modules.<br />
SecOps teams should consider the full<br />
Flowmon network and security operations<br />
solution as it adds the ADS module which<br />
provides detection services for unknown threats,<br />
malware, ransomware and malicious activity<br />
along with incident response and forensics.<br />
The Flowmon Collector appliances handle<br />
collection, long-term storage and analysis of all<br />
industry standard log flow formats including<br />
NetFlow, IPFIX, sFlow, jFlow and NetStream<br />
and can receive them from a wide range of<br />
network devices including load balancers,<br />
routers, switches, firewalls, packet brokers and<br />
dedicated Flowmon Probes. The Collector<br />
includes an integral Flowmon Probe for native<br />
collection of L2/L4 information along with L7<br />
statistical data and more external Probes can<br />
be added as needed.<br />
Collector deployment options include turnkey<br />
hardware rack-mount models, installation on<br />
cloud services such as AWS, Azure and Google<br />
Cloud Platform or virtualisation on VMware,<br />
Hyper-V and KVM hosts. We chose our<br />
VMware vSphere host and swiftly deployed the<br />
Collector using the supplied OVF template,<br />
placed our Probe monitoring ports on separate<br />
vSwitches and dedicated physical adapters with<br />
promiscuous mode enabled and cabled them<br />
to our switch span ports.<br />
The web console's home page provides easy<br />
access to the Flowmon Monitoring Center<br />
(FMC) which manages flow sources, provides<br />
traffic graphs for each one and offers an Analysis<br />
section for drilling down for more information.<br />
The smart Chapters feature combines profiles<br />
and source data channels to present information<br />
on areas such as problematic connections, top<br />
talkers, L7 analysis for service usage and, of<br />
course, cloud flow monitoring.<br />
Configuring AWS cloud monitoring was a<br />
lengthy process but the detailed documentation<br />
and assistance from Progress' knowledgeable<br />
support staff helped us over any hurdles. Once<br />
we had AWS IAM access, EC2 instance<br />
network interface flow logging and an Amazon<br />
CloudWatch log group configured, we used<br />
FCC to enable AWS flow logs and watched as<br />
FMC spotted the new source for the monitored<br />
Linux instance.<br />
The Dashboard and Report console presents<br />
an incredible amount of graphical information,<br />
and widgets allow it to be easily customised to<br />
your requirements. We added a Chapter for the<br />
AWS source, used it to create a new widget and<br />
after dragging it to a prominent position on our<br />
dashboard, could see all traffic and IP addresses<br />
related to our EC2 instance and set monitoring<br />
periods of between one hour and three months.<br />
Progress Flowmon is the perfect partner for<br />
NetOps and SecOps teams as it provides a<br />
stunning amount of information on network,<br />
service and application performance. Fully<br />
centralised management makes it easy to<br />
identify and analyse problem areas while the<br />
native cloud flow monitoring services add<br />
valuable new dimensions and keep cloud costs<br />
to a minimum. <strong>NC</strong><br />
Product: Flowmon Collector 12.1<br />
Supplier: Progress Software<br />
Website: www.flowmon.com<br />
Sales: support@flowmon.com<br />
WWW.NETWORKCOMPUTING.CO.UK AUGUST/SEPTEMBER 13<br />
NETWORKcomputing<br />
@<strong>NC</strong>MagAndAwards
OPINION: DIGITAL TRANSFORMATION<br />
OVERSIGHT ABOVE I.T. TRANSFORMATION<br />
EVERYONE IS TALKING ABOUT TRANSFORMATION IN THE I.T.<br />
SPACE, BUT DO PROFESSIONALS HAVE COMPLETE VISIBILITY AS<br />
TO WHICH DEVICES, SYSTEMS AND APPLICATIONS ARE<br />
UNDERGOING THIS PROCESS? MAT CLOTHIER, CEO AT<br />
CLOUDHOUSE GIVES US HIS TAKE<br />
Digital transformation is nothing new, but<br />
we are living through a period of<br />
particularly rapid change. Internal and<br />
external factors have combined to accelerate<br />
this trend. The Covid pandemic brought with it<br />
a seismic shift in the way people work and<br />
consume products, and this change is here to<br />
stay. Enterprises are busy making positive<br />
changes, driven by a desire to provide best<br />
levels of service to customers and ensure the<br />
business remains fully compliant and resilient<br />
in the face of change.<br />
COMPLEXITIES OF THE CLOUD<br />
Arguably the biggest transformation still<br />
playing out in the IT industry is moving to the<br />
cloud, with predictions that the global cloud<br />
computing market will continue to grow at<br />
pace to the end of 2028, as small and<br />
medium enterprises make their migration and<br />
businesses seek to improve efficiency with the<br />
adoption of advanced technologies such as<br />
big data, AI and machine learning.<br />
Using multiple cloud providers has become<br />
the standard for many organisations, with 80%<br />
using both public and private clouds in a hybrid<br />
model. The hybrid model offers agility and<br />
competitive advantage, but having your IT<br />
estate spread out in this way can create its own<br />
problems. Maintaining oversight of all parts of<br />
the estate is essential for resilience but can<br />
prove complex and time consuming in practice.<br />
While human resources in the business are<br />
busy working on positive change, it's as crucial<br />
to ensure that technology can enable<br />
monitoring of those developments. With so<br />
much at stake, monitoring is essential to<br />
minimise disruption and ensure a seamless<br />
customer experience. It is also an important<br />
element in making sure regulatory standards<br />
and compliance are maintained.<br />
The risks of breaching regulatory<br />
compliance, with the potential consequences<br />
of legal action and fines, as well as<br />
reputational damage, are well documented.<br />
For example, data for 2021 shows that data<br />
breach costs rose to an average total of<br />
$4.24 million, the highest ever recorded - but<br />
the same report noted that costs were<br />
significantly higher for organisations that<br />
lagged in areas such as security AI and<br />
automation and cloud security. And the costs<br />
are not just financial: there is huge potential<br />
for reputational damage. For those operating<br />
in highly regulated industries, such as finance<br />
and healthcare, the consequences of<br />
breaching regulatory compliance can be even<br />
more severe.<br />
OVERSIGHT TOOLKIT<br />
CTOs and CIOs, now more than ever, need to<br />
keep on top of their IT transformation, monitor<br />
change and have full oversight of their estates.<br />
Being across so many things at once can be<br />
daunting and laborious, especially for those<br />
working with a matrix management structure.<br />
So how can they best achieve oversight?<br />
This is where configuration management<br />
tools come to the fore. These tools give a toplevel<br />
overview - a clear and unambiguous<br />
assessment of every element of the full suite -<br />
all in one place, and can find and fix<br />
compliance and change management issues<br />
quickly. They allow omnipresence, facilitating<br />
best practice oversight over even the most<br />
complex transformation projects.<br />
Having all this information in one easy-toaccess<br />
place also makes it easier to bring<br />
teams together - particularly beneficial for<br />
those working with a matrix management<br />
structure. You won't miss a thing.<br />
Change management is made simple as the<br />
tools look at the different environments across<br />
the estate and compare them, giving full<br />
transparency on where you are on the journey<br />
to migration. They allow oversight of the<br />
tracking, testing and deployment of updates,<br />
pre-empting issues before they arise. What's<br />
more, they work across server, desktop and<br />
network as well as multiple vendors, making<br />
them ideal for those working with hybrid cloud<br />
systems, giving full peace of mind.<br />
Management tools not only identify issues<br />
when they happen: they can also provide a<br />
further layer of protection by allowing CTOs<br />
and CIOs to take full control by setting policies<br />
and permissions to pre-empt compliance<br />
problems before they occur. Policies can be<br />
created or selected from the Center for Internet<br />
Security's 20 critical security controls, which<br />
satisfy regulatory requirements like PCI and<br />
SOX. This means companies can automatically<br />
achieve compliance by setting policies<br />
according to best practice configuration.<br />
The automated health checks offered by<br />
configuration management tools act as an<br />
early warning system, building a company's<br />
resilience by allowing them to act fast not just<br />
when problems crop up, but by catching<br />
misconfigurations before they can be<br />
exploited. Configuration management tools<br />
are a powerful addition to the CTO and CIO<br />
toolkit. <strong>NC</strong><br />
14 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINON: NETWORK DOWNTIME<br />
DOWNTIME DOLDRUMS AND SMART SOLUTIONS<br />
ALAN STEWART-BROWN, VP EMEA AT OPENGEAR CONSIDERS THE<br />
TOP TRENDS FOR NETWORKS THAT WANT TO STAY ONE STEP<br />
AHEAD OF DOWNTIME<br />
With hybrid working now becoming<br />
the strategy of choice for numerous<br />
businesses, many have had to<br />
undertake a re-evaluation of their network<br />
infrastructure to facilitate collaboration and<br />
productivity while at home and in the office.<br />
However, the road to integrated networks has<br />
proven to be a bumpy ride. As more firms<br />
leverage IoT and smart devices, this<br />
increases the risk of disruptive downtime due<br />
to the increased strain on networks. So what<br />
trends are allowing businesses and their<br />
engineers to effectively escape the downtime<br />
doldrums?<br />
THE CONSTANT THREAT TO UPTIME<br />
Network outages are nothing new, but in<br />
2021, downtime managed to impact some<br />
of the largest enterprises in the world. Even<br />
social media giant Meta was impacted<br />
globally for almost six hours over two days in<br />
<strong>Oct</strong>ober 2021, affecting access to<br />
Facebook, Instagram and WhatsApp. While<br />
detrimental to the technology firm, it also had<br />
ramifications for the people and businesses<br />
around the world that rely on its services.<br />
The biggest causes of downtime for<br />
enterprises will typically be software upgrades<br />
gone wrong, cyber attacks or<br />
misconfiguration errors, such as when writing<br />
a configuration file. The issue is also<br />
compounded by the widespread adoption of<br />
IoT devices. Due to constant connectivity<br />
being needed, any outage will also affect<br />
these endpoints.<br />
Content delivery networks (CDNs) are also<br />
under sharp focus due to their role in<br />
improving site performance and user<br />
experience. Software configuration updates<br />
can trigger bugs in such systems and lead to<br />
severe disruption. In a handful of cases,<br />
natural disasters can prove catastrophic to<br />
intercontinental global data traffic, proving<br />
the fragility of the interconnected world.<br />
However, with correctly chosen solutions,<br />
businesses are able to manage their<br />
infrastructure remotely and securely,<br />
minimising downtime as much as possible.<br />
With today's network challenges,<br />
organisations require access to advanced<br />
technologies to streamline their operations<br />
and agile tools to provide insights into<br />
virtualised environments.<br />
KEEPING DOWNTIME AT BAY<br />
At the core of keeping downtime at a<br />
minimum is an independent management<br />
plane, which essentially allows engineering<br />
teams to roll-back or undo any inadvertently<br />
uptime-threatening actions. This is part of a<br />
wider Smart Out-of-Band management<br />
setup, which unlike In-Band solutions, allows<br />
network engineers to securely connect to<br />
remote equipment during an outage.<br />
Engineers can then also lock down the most<br />
critical functions on the production network<br />
to prevent access from other users.<br />
Smart Out-of-Band interfaces can also be<br />
paired with Failover to Cellular. These<br />
capabilities use 4G LTE, so in the case of<br />
disruption, engineers can leverage bandwidth<br />
to access critical applications when<br />
undergoing issue remediation, even when the<br />
primary network is down. This bandwidth not<br />
only provides the remote access to determine<br />
the root cause of an outage, but also acts as<br />
a path for remote site production network<br />
traffic, ensuring network resilience.<br />
TOWARDS NETOPS AUTOMATION<br />
Another aspect of maintaining uptime is via<br />
the adoption of a NetOps approach for<br />
growing, virtualised environments. Across the<br />
hybrid workforce, it's more important than<br />
ever for enterprises to be able to automate<br />
certain processes, such as the testing of<br />
network processes for latency purposes or<br />
securely provisioning new sites. NetOps<br />
makes this possible, with a growing<br />
awareness of its benefits among businesses<br />
and IT departments.<br />
The NetOps approach provides advantages<br />
such as upskilling and business efficiency,<br />
with opportunities for employees to build<br />
programming skills in Python and<br />
understanding of Docker containers, plus<br />
other commonly used toolsets such as Chef,<br />
Puppet and Ansible. Together with the<br />
independent management plane, NetOps<br />
automation ultimately helps reduce the threat<br />
of downtime and ensures business continuity.<br />
KEEPING THE NETWORK UP AND<br />
RUNNING<br />
Outages ultimately lead to organisations<br />
losing money and can have a significant<br />
impact on industry reputation. The hybrid<br />
working era has required businesses to be<br />
more agile and offer a network that's secure,<br />
connected, and scalable for employees to<br />
benefit, regardless of where they are based.<br />
To ensure downtime is kept to a minimum,<br />
enterprises need to be proactive in securing<br />
their network resilience with trending<br />
technologies such as the independent<br />
management plane, Smart Out-of-Band<br />
technologies and NetOps to ensure optimum<br />
business continuity and keep the network up<br />
and running. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK AUGUST/SEPTEMBER 15<br />
NETWORKcomputing<br />
@<strong>NC</strong>MagAndAwards
SECURITY UPDATE<br />
HOW TO I<strong>NC</strong>REASE SECURITY VIA A ZERO TRUST ARCHITECTURE<br />
AS CYBERCRIMINALS CONTINUE TO DEVELOP NEW ATTACK TECHNIQUES AND BECOME MORE<br />
SOPHISTICATED, THE TRADITIONAL NOTION OF A STRONG EXTERNAL<br />
PERIMETER BEING THE BEST - AND OFTEN ONLY - DEFE<strong>NC</strong>E<br />
AGAINST COMPROMISE HAS SHOWN ITSELF TO BE<br />
INADEQUATE. SANJAY RADIA, CHIEF SOLUTIONS<br />
ARCHITECT AT NETSCOUT EXPLAINS WHY<br />
Nowadays,<br />
perimeter-based<br />
network access<br />
controls are unable to detect or prevent<br />
compromise, as vectors of attack have<br />
evolved and the threat surface continues<br />
to grow. Evidence of this can be seen<br />
with direct attacks, such as the recent<br />
log4j vulnerability, as well as indirect<br />
attacks, an example of which is phishing<br />
with malware. Prevention at the edge has<br />
been the saviour side of the arms race<br />
but has always, and will always, come in<br />
second place.<br />
Things get worse when we consider the<br />
implicit security assumption that<br />
everything inside an organisation's<br />
network is trustworthy. This means that if<br />
threat actors are on the network, they<br />
have the ability to move laterally within it<br />
- allowing them to seek further<br />
compromise. The concept of a Zero Trust<br />
architecture was introduced to allow<br />
services that drive digital transformation,<br />
while improving the network's security<br />
posture.<br />
ZERO TRUST<br />
The National Cyber Security Centre's<br />
16 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
SECURITY UPDATE<br />
(<strong>NC</strong>SC) Zero Trust design principles<br />
present a new method of solving an ageold<br />
problem - securing networks and<br />
information. As a result, organisations of<br />
all sizes are rethinking their security<br />
architecture, processes, and procedures<br />
to adopt Zero Trust features.<br />
According to the <strong>NC</strong>SC, "Zero Trust is an<br />
architectural approach where inherent<br />
trust in the network is removed, the<br />
network is assumed hostile and each<br />
request is verified based on an access<br />
policy". In order for a request to be<br />
deemed trustworthy, context must be<br />
sought. This relies on a number of factors,<br />
including strong authentication,<br />
authorisation, the health of the device,<br />
and the value of accessible data.<br />
An example of a Zero Trust approach is<br />
multifactor authentication (MFA). MFA<br />
adds an extra layer of security by<br />
requiring additional factors to prove<br />
the identity of users. For example,<br />
users may be required to scan their<br />
fingerprint or confirm a PIN sent to<br />
their device before they can access a<br />
resource. From a Zero Trust architecture<br />
perspective, MFA is utilised as a doublecheck<br />
against its own security measures,<br />
ensuring that users are indeed who they<br />
are claiming to be. This significantly<br />
reduces the possibility of bad actors using<br />
compromised credentials to access data,<br />
devices and systems.<br />
CREATING A SAFER, MORE SECURE<br />
ENVIRONMENT<br />
The Zero Trust model can be easily<br />
visualised as a set of pillars representing<br />
different security areas, such as devices,<br />
applications, and users. Beneath all of<br />
these pillars lie the foundational aspects<br />
of a Zero Trust architecture. These are:<br />
analytics, visibility, automation, and<br />
governance.<br />
Zero Trust adoption is a gradual and<br />
continual process. As enterprises begin to<br />
refine their architectures, their solutions<br />
become increasingly reliant on<br />
comprehensive visibility and monitoring,<br />
automated processes, and systems, in<br />
addition to becoming closer to full<br />
integration across all of the pillars. This<br />
enables organisations to be more<br />
dynamic in their decisions around policy<br />
implementation.<br />
Implementing and developing a Zero Trust<br />
architecture takes time. The architecture will<br />
continue to develop as policies, processes<br />
and tooling are upgraded. Nevertheless,<br />
verification and ongoing auditing of Zero<br />
Trust models is vital to knowing and<br />
demonstrating that an organisation's<br />
security measures are working.<br />
A key characteristic of a Zero Trust<br />
architecture is that it comes with no false<br />
sense of security. In traditional perimeterbased<br />
models, anything taking place<br />
inside the network is considered<br />
trustworthy, due to the assumption that<br />
any users or activities taking place in the<br />
network have already passed<br />
authentication and are authorised to be<br />
there. Therefore, this architecture<br />
assumes that insiders are never<br />
dangerous or destructive and that<br />
perimeter security is faultless.<br />
However, there are obvious flaws with<br />
this model. There are numerous scenarios<br />
in which users and events inside your<br />
perimeter shouldn't be trusted - for<br />
example, when a cybercriminal has<br />
gained access using compromised<br />
credentials, enabling them to abuse<br />
privileges or move laterally through the<br />
network. A Zero Trust architecture<br />
prioritises protection against potential<br />
insider threats, thus preventing a situation<br />
like this from unfolding.<br />
VISIBLE BENEFITS<br />
When it comes to implementing a Zero<br />
Trust architecture, comprehensive visibility<br />
of the entire network is a requirement for<br />
all organisations. This ensures that the<br />
Zero Trust model is effective. In addition,<br />
the architecture should contain network<br />
taps to mirror traffic from the wire, as well<br />
as a tool that is capable of replicating<br />
and distributing packets to existing<br />
cybersecurity monitoring tools.<br />
Only with this level of visibility will<br />
enterprises be able to detect potential<br />
threats, view historical usage, trace<br />
interconnected devices, and assist in<br />
orchestrating mitigation through<br />
Application Programming Interfaces<br />
(APIs). Additionally, organisations should<br />
have the capacity to utilise protection<br />
groups so as to classify networks, servers<br />
and services based on the risk posed to<br />
them. This will allow for the rapid<br />
adoption of a Zero Trust architecture.<br />
Whether an organisation is just starting<br />
out on its Zero Trust implementation<br />
journey, or is are already well on its way,<br />
it is vital to ensure visibility and analytics<br />
are major components within the<br />
detection and validation of their Zero<br />
Trust architecture design. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 17
SECURITY UPDATE<br />
STAY AWARE OF RANSOMWARE<br />
RANSOMWARE ATTACKS ARE GROWING IN COST AND<br />
FREQUE<strong>NC</strong>Y. FLORIAN MALECKI, EXECUTIVE VICE<br />
PRESIDENT MARKETING, ARCSERVE OFFERS 5 STEPS THAT<br />
COMPANIES SHOULD TAKE TO PROTECT THEMSELVES<br />
Ransomware attacks continue to impact<br />
organisations worldwide - and the<br />
costs are staggering. A new global<br />
survey of over 1,100 IT decision-makers at<br />
small and midsize companies found that<br />
50% had been targeted by a ransomware<br />
attack, with 35% asked to pay over<br />
$100,000 in ransom, and 20% asked to<br />
pay between $1 million and $10 million. In<br />
the UK, 50% of respondents said they had<br />
no choice but to pay the ransom.<br />
These numbers are not expected to<br />
improve soon. The sad truth is that, despite<br />
spending billions on cybersecurity tools,<br />
businesses are still poorly prepared for<br />
ransomware attacks. Less than a quarter<br />
(23%) of all respondents to the survey said<br />
they're very confident in their ability to<br />
recover lost data in the event of a<br />
ransomware attack. Smaller businesses are<br />
even less well prepared. Under 20% are<br />
very confident in their ability to recover lost<br />
data in the event of a ransomware attack.<br />
Meanwhile, the attack surface continues<br />
to expand as organisations using<br />
technologies like IoT, artificial intelligence,<br />
and 5G generate even more data - data<br />
that can be compromised and held captive<br />
by ransomware attackers. Remote working<br />
adds to this attack surface. 65% of UK<br />
respondents said they didn't have a<br />
backup and recovery plan for all their<br />
remote workers.<br />
For this reason, companies must take a<br />
new approach to data resilience. They must<br />
strengthen their disaster recovery strategies,<br />
backup systems, and immutable storage<br />
solutions to prevent the loss of missioncritical<br />
data.<br />
Many are. The survey found that 92% of<br />
organisations are making additional<br />
investments to protect against ransomware<br />
attacks, with the top areas of investment<br />
being security software (64%), training<br />
and certification (50%), and managed<br />
services (43%).<br />
While these investments are encouraging<br />
more should be done as, for most<br />
companies, it's not a matter of if their data<br />
will be compromised; it's a matter of when.<br />
With ransomware attacks increasing yearly,<br />
data backup and recovery should be at the<br />
very top of every organisation's priority list.<br />
Here are five steps businesses can take<br />
18 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
SECURITY UPDATE<br />
now to reduce their exposure to<br />
ransomware and avoid staggering losses.<br />
1: Educate employees<br />
It's essential to invest in training for staff so<br />
that they're aware of how ransomware<br />
works. From there, employees will be better<br />
prepared to recognise and prevent it. They<br />
should know that ransomware can sneak in<br />
from anywhere. The training should remind<br />
them to scrutinise every link in emails and<br />
not open attachments in unsolicited emails.<br />
Employees should be reminded to only<br />
download software - especially free - from<br />
websites they know and trust.When<br />
possible, employees should verify the<br />
integrity of downloaded software through a<br />
digital signature before execution.<br />
2: Focus on cures as well as prevention<br />
Companies continue to invest loads of<br />
money in cybersecurity solutions like nextgeneration<br />
firewalls and extended detection<br />
and response (XDR) systems designed to<br />
prevent attacks. Yet these same companies<br />
are still falling prey to ransomware and<br />
being forced to pay a hefty price.<br />
It's time for companies to stop focusing<br />
entirely on prevention. They should also<br />
invest in curative measures like backup &<br />
recovery and immutable storage that allow<br />
them to quickly restore their data and<br />
avoid paying the ransom when attackers<br />
break in.<br />
Regular data backups and encryption play<br />
a key role in protecting an organisation's<br />
data. A consistent backup schedule will<br />
enable you to seamlessly restore any<br />
compromised systems or data. Encrypting<br />
your sensitive data is also highly<br />
recommended. After all, if ransomware<br />
attackers gain access to your critical assets,<br />
encryption has the benefit of keeping data<br />
from being read and further exploited by<br />
the bad guys.<br />
3: Place a premium on data resilience<br />
Your data resilience is only as strong as<br />
your weakest link. Monitor your<br />
weaknesses, fix them when you find them,<br />
and you can bounce back quickly from<br />
disruption and return to normal operation.<br />
To do this, you must have the technologies<br />
required to back up your data and recover<br />
it if necessary, along with the proper<br />
mindset. That means a defensive posture is<br />
regularly sustained with drills that simulate<br />
an intrusion to measure your resiliency and<br />
bolster it where necessary.<br />
Many companies develop a strategy and<br />
then neglect to test it. That's like a basketball<br />
team devising a sophisticated defense and<br />
never bothering to practice it. All companies<br />
should regularly test their data backup and<br />
recovery plans to ensure they can effectively<br />
restore their data and systems if an attack or<br />
natural disaster occurs.<br />
4: Know what data is most critical<br />
Data varies in value. If you're concerned<br />
about costs, as most organisations are these<br />
days, you don't have to store or back up all<br />
your data in the same place. Look into<br />
storage solutions that provide options like<br />
data tiering. These enable you to place lessimportant<br />
data in less-expensive levels of<br />
storage or "tiers."<br />
Another upside of data tiering is lower<br />
energy costs. You'll use less compute power<br />
if you're not storing every last byte of your<br />
data at the highest security level.<br />
5: Put a disaster-recovery plan in place<br />
Despite all the preventive measures you<br />
take, you need to prepare for the possibility<br />
that you will get hit. So, it would be best if<br />
you had a disaster recovery plan. You need<br />
to be able to back up data as often as is<br />
appropriate-ideally every 15 minutes for<br />
critical data. You also need to easily verify<br />
that your whole environment is backed up,<br />
including your remote workers and any<br />
SaaS applications you use, such as<br />
Microsoft 365.<br />
A good disaster-recovery solution will back<br />
up your data to a location of your choice<br />
and on a schedule that suits you. It will also<br />
be easy to test, which is crucial because<br />
testing is the only way you can validate that<br />
your recovery-time goals can be met. It may<br />
seem obvious, but this is where a lot of<br />
solutions fall short. Your disaster-recovery<br />
solution must be able to recover your data<br />
every time and on time. When ransomware<br />
hits, you want to be confident you can<br />
recover your data and get on with business<br />
as soon as possible.<br />
FINAL TAKEAWAY<br />
There is no perfect defense against<br />
ransomware. The best approach is a<br />
multilayered one that includes educating<br />
your staff, investing in reliable data backup<br />
& recovery and immutable storage solutions,<br />
and having a robust disaster recovery plan.<br />
That's how organisations can stay ahead of<br />
this growing threat and protect their data<br />
and bottom line. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 19
FEATURE: WAN PERFORMA<strong>NC</strong>E<br />
WHY CISOs MUST NOW EMBRACE SD-WAN<br />
SIMON HILL, HEAD OF LEGAL & COMPLIA<strong>NC</strong>E AT CERTES NETWORKS INSISTS THAT<br />
IT’S TIME FOR CISOs TO TAKE A LEAD ROLE IN THE DIGITAL TRANSFORMATION<br />
PROCESS - OR RISK BEING SIDELINED FOR GOOD<br />
Digital transformation has become a<br />
business imperative, yet rather than<br />
pulling together to enable essential<br />
change, the friction between network and<br />
security teams is increasing. The business<br />
needs to move away from data centres and<br />
traditional Wide Area Networks (WAN) to<br />
exploit the cost, flexibility and agility<br />
provided by the cloud and Software Defined<br />
WANs (SD-WAN). Chief Information<br />
Security Officers (CISOs), especially those<br />
working in regulated industries, insist the<br />
risks associated with public infrastructure<br />
are too high. Stalemate.<br />
Until now. Organisations are pressing<br />
ahead with digital transformation plans<br />
and excluding the CISO from the<br />
conversation. But at what cost? Who is<br />
assessing the implications for regulatory<br />
compliance? At what point will the Chief<br />
Risk Officer prohibit the use of the SD-<br />
WAN for sensitive data, leaving the<br />
business running legacy and new<br />
infrastructure side by side, fundamentally<br />
undermining the entire digital<br />
transformation project?<br />
A new attitude is urgently required, one<br />
based on collaboration, understanding<br />
and a recognition that a Zero Trust security<br />
posture can safeguard even the most<br />
sensitive data, while unlocking all the<br />
benefits associated with SD-WAN.<br />
ACCEPT CHANGE<br />
CISOs need to face up to the fact that<br />
digital transformation is happening - with<br />
or without them. Organisations need to<br />
embrace the agility, flexibility and cost<br />
benefits offered by the cloud, by Softwareas-a-Service<br />
and, critically, the shift from<br />
expensive WAN technology to SD-WAN.<br />
For CISOs, while the migration to SD-<br />
WAN extends the attack surface, adding<br />
unacceptable data vulnerability, saying no<br />
is not an option any more. CISOs risk<br />
being left out of the digital transformation<br />
loop - and that is not only adding<br />
significant corporate risk but also<br />
compromising the expected benefits of this<br />
essential technology investment.<br />
Network and IT teams are pressing<br />
ahead, insisting the risk is acceptable.<br />
How do they know? For any organisation,<br />
this is a dangerous compromise: critical<br />
risk decisions are being taken by<br />
individuals who have no understanding of<br />
the full implications. For those<br />
organisations operating in regulated<br />
industries, these decisions could result in<br />
an exposure to $10s millions, even $100s<br />
millions of penalties.<br />
Failure to embed security within the initial<br />
digital transformation strategy is also<br />
compromising progress. What happens<br />
when the CISO or Chief Risk Officer<br />
discovers the business is in the process of<br />
migrating from the old WAN to a new SD-<br />
WAN environment? Suddenly the brakes<br />
are on, and the call is for sensitive data to<br />
be encrypted before it hits the network.<br />
Adding Internet Protocol Security (IPsec)<br />
tunnels will degrade performance - so the<br />
business is then stuck using the legacy<br />
WAN for data connectivity while still<br />
paying for the SD-WAN and failing to gain<br />
any of the agility or cost benefits. More<br />
frustration and friction between teams that<br />
should be working together to support<br />
business goals.<br />
DRIVE CHANGE<br />
Security is a fundamental component of<br />
digital transformation - indeed of<br />
corporate operating strategy. Rather than<br />
avoiding change, CISOs have a<br />
responsibility not only to secure the<br />
organisation but to proactively advocate<br />
change, with security as the key enabler of<br />
digital transformation.<br />
20 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATURE: WAN PERFORMA<strong>NC</strong>E<br />
Digital transformation does not by<br />
default create an inherently insecure<br />
environment - but it will require<br />
organisations to, somewhat belatedly,<br />
embrace a Zero Trust model. It has been<br />
clear for many years that there is no<br />
correlation between ownership and trust.<br />
Just because a company owns<br />
infrastructure and assets does not<br />
automatically infer total trust over data<br />
security. Similarly, infrastructure outside<br />
the business is not inherently<br />
untrustworthy.<br />
The key is to build trust into a secure<br />
overlay to protect data that will allow a<br />
business to operate across any<br />
infrastructure, whether it is owned or public.<br />
A High Assurance SD-WAN overlay, for<br />
example, uses crypto-segmentation to<br />
protect and ensure the integrity of<br />
sensitive data. With this Zero Trust<br />
approach, High Assurance SD-WAN<br />
means whether the network is public or<br />
private, trusted or untrusted, is irrelevant:<br />
the data security team simply needs to<br />
define the policy and, with ownership of<br />
the cryptography keys, can be confident<br />
that data is protected at all times<br />
wherever it goes.<br />
WORKING TOGETHER<br />
Adopting a Zero Trust security posture<br />
changes the outlook for CISOs - and<br />
provides a foundation for vital<br />
collaboration with the networking and IT<br />
teams. With confidence that the data is<br />
secure regardless of network location,<br />
everyone involved in digital<br />
transformation can achieve their goals: IT<br />
and network teams can embrace the<br />
flexibility and agility of the cloud, SaaS<br />
and SD-WAN, while the security team still<br />
has control of the security posture.<br />
This can only be achieved if the business<br />
embraces a different mindset. It is<br />
essential to think about security by design<br />
from the outset - and to break down the<br />
barriers between network, IT and security.<br />
The introduction of the Secure Access<br />
Service Edge (SASE) framework provides<br />
clear guidelines for the convergence of<br />
these teams to drive additional business<br />
value but the onus - and opportunity - lies<br />
with the CISO to ensure the entire<br />
organisation truly understands the digital<br />
transformation objectives.<br />
This also demands an essential shift<br />
away from a regulatory compliance<br />
focused security posture - something that<br />
is inherently flawed due to the<br />
impossibility of creating regulations that<br />
keep up with the ever changing security<br />
threats - towards a truly business driven<br />
approach. Working together to plan the<br />
digital transformation process may take a<br />
little more time up front but it will result in<br />
a secure foundation that will remove any<br />
constraints to innovation and agility.<br />
CO<strong>NC</strong>LUSION<br />
It is time for CISOs to change. There is no<br />
value in endlessly blocking essential new<br />
technology projects; and no upside in<br />
being excluded from vital plans as a<br />
result. By taking a proactive stance and<br />
driving digital transformation strategies,<br />
CISOs can redefine the role, become a<br />
key strategic player within the business<br />
and act as an enabler, rather than a<br />
constraint, to operational success. It is<br />
time to find a way to say yes to secure<br />
digital transformation - without<br />
compromise. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 21
OPINION: SASE<br />
THE SASE APPROACH TO NETWORK SPRAWL<br />
SPRAWLING NETWORKS AND LONG LEAD TIMES - IS THERE ANOTHER APPROACH WE CAN TAKE?<br />
JUSTIN DAY, CEO AND CO-FOUNDER OF CLOUD GATEWAY, SHOWS US THE WAY<br />
There's no denying that, post-pandemic, IT<br />
teams are more focused on architectures<br />
and investments to help them better<br />
manage change, whilst delivering seamless<br />
experiences and keeping their organisation's<br />
infrastructure secure. However, for many<br />
organisations their digital estate has expanded,<br />
with an increasing number of cloud-based<br />
technologies and services provided by multiple<br />
suppliers, with multiple agreements to monitor<br />
and manage.<br />
The thing is, getting cloud services up and<br />
running isn't the end goal for IT teams. They<br />
understand that the real aim is to easily<br />
connect and secure all the organisation's<br />
resources, data and users in an agile, cost<br />
effective and scalable manner.<br />
GRADUAL CHANGE IS ACHIEVABLE<br />
Many organisations still use legacy technologies<br />
and networks that stifle growth, leaving IT teams<br />
with hard-to-manage siloed technologies and a<br />
more complex route to cloud adoption. Change<br />
shouldn't be feared. While the larger telecoms<br />
providers will tell their customers to stick out the<br />
current chip shortage, there are gradual steps<br />
that can be taken to remove dependence on<br />
legacy networks. The key takeaway here is that<br />
gradual change is achievable and acting now is<br />
a positive way to stop adding to technical debt.<br />
It's important to point out that migrating<br />
applications to a cloud infrastructure requires<br />
scale and performance. Achieving this can be<br />
challenging due to limited visibility into the<br />
network and the fact that each platform has<br />
proprietary controls for networking and security.<br />
This is where taking a different approach can<br />
be beneficial. By consolidating multiple network<br />
and security solutions into a single, cloud native<br />
managed service, organisations can build a<br />
digital foundation that will deliver greater agility,<br />
flexibility and choice for the business. This<br />
framework, known as Secure Access Service<br />
Edge (SASE) allows IT teams to reach that goal<br />
of eliminating the time and costs involved with<br />
unnecessary network complexity and managing<br />
multiple vendor contracts.<br />
The components of SASE are not new, rather<br />
they are well-established technologies that have<br />
been around for a long time. Software-defined<br />
wide-area network (SD-WAN), Secure Web<br />
Gateway (SWG), Cloud Access Security Broker<br />
(CASB), Firewall-as-a-service, and Zero Trust<br />
network access (ZTNA). However, the SASE<br />
approach takes this collection of technologies to<br />
deliver a fresh, modern networking solution -<br />
one that supports increased traffic, improves real<br />
time communications, delivers secure cloud<br />
connectivity and facilitates digital growth. This<br />
reduces the administrative burden on IT teams<br />
and facilitates cost savings compared to<br />
traditional networking infrastructure.<br />
With SASE, all traffic - no matter where it<br />
originates from - can be tracked, cleansed, and<br />
recorded. This level of detail provides<br />
organisations with full control over which cloud,<br />
technology and connectivity providers are<br />
utilised. This means the right tool or<br />
technologies can be selected in a timescale and<br />
budget that meets their individual requirements.<br />
Ineffective or expensive services and<br />
infrastructure can be phased out more easily<br />
and as the needs of the organisation evolve,<br />
there is no reason to be tied to a vendor who is<br />
delaying the project or isn't innovating.<br />
EMBRACING CHANGE<br />
SASE is all about enabling a simple and secure<br />
access experience. Organisations need the<br />
ability to provision scalable, secure connectivity<br />
between their physical sites, on premise and<br />
cloud environments, partner ecosystems and<br />
remote workers. SASE delivers network and<br />
connectivity solutions that behave and act like<br />
the cloud, so that IT teams can get a site,<br />
application or service online within minutes<br />
rather than waiting weeks or months. As new<br />
technologies emerge, a SASE approach can<br />
deliver the scalability needed alongside a<br />
solution that protects against data breaches and<br />
threats, whilst also providing complete visibility<br />
of the network, users and data for an optimised<br />
user experience.<br />
For most organisations, the skills and resources<br />
needed to effectively manage their network and<br />
security operations are in short supply. Look for a<br />
partner that is well-versed in the movement of<br />
critical data and secures it in transit, one that can<br />
support you with the tools to future-proof<br />
performance, reliability and the security of your<br />
network. That way, no matter where you are in<br />
your journey you can rely on your partner to help<br />
you adopt SASE in a phased manner, at a pace<br />
that suits your organisation, and which doesn't<br />
cause disruption to staff or customers. <strong>NC</strong><br />
22 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
EVENT ORGANISERS:<br />
Do you have something coming up that may<br />
interest readers of Network Computing?<br />
Contact dave.bonner@btc.co.uk<br />
FORTHCOMING EVENTS<br />
FORTHCOMING EVENTS<br />
<strong>2022</strong><br />
FORTHCOMING EVENTS<br />
27-28<br />
SEPT<br />
06<br />
OCT<br />
20<br />
OCT<br />
16-17<br />
NOV<br />
INTERNATIONAL CYBER EXPO<br />
Olympia, London<br />
www.internationalcyberexpo.com<br />
CIO/CISO UK SUMMIT<br />
Etihad Stadium, Manchester<br />
https://bit.ly/3z7gRcc<br />
CIO/CISO FRA<strong>NC</strong>E SUMMIT<br />
Paris, France<br />
https://bit.ly/3IDLSHI<br />
DATACENTRES IRELAND<br />
RDS Dublin<br />
www.datacentres-ireland.com
FEATURE: WAN PERFORMA<strong>NC</strong>E<br />
WAN ACCELERATION OR EDGE COMPUTING?<br />
DAVID TROSSELL, CEO AND CTO OF BRIDGEWORKS, ON DELIVERING HIGHER WAN PERFORMA<strong>NC</strong>E<br />
The effects of the pandemic over the past<br />
couple of years has hastened the move<br />
towards digital transformation and the<br />
cloud for many companies. Organisations<br />
concerned for the safety of their personnel and<br />
what shape organisations will look like in the<br />
future, moved from a traditional capital<br />
expenditure (CapEx) model, to a work from<br />
home and operational expenditure- (OpEx)<br />
based SAAS model. At the same time, there is<br />
a push for IoT devices to monitor and manage<br />
many aspects of our daily lives.<br />
Asynchronous IoT devices only monitor and<br />
report. Many of them are semi-synchronous,<br />
meaning that they not only monitor but also<br />
manage resolutions. However, they are not<br />
time critical. Then there are the IoT devices that<br />
offer fully synchronous monitoring, and which<br />
enact resolutions immediately. These typically<br />
use the cloud for reporting back to a central<br />
collection and decision point. However, we are<br />
seeing more sophisticated IoT applications that<br />
are latency-sensitive and require considerably<br />
more computing resources.<br />
To support the time-sensitive aspect, many<br />
have added an intermediate computing node<br />
between the IoT device and the central cloud<br />
compute and storage node. This can be on<br />
premise of a locally-managed service provider.<br />
CAPTURING DIGITAL<br />
TRANSFORMATION<br />
Laura LaBerge, a director at McKinsey &<br />
Company of capabilities for digital strategy;<br />
Kate Smaje, a senior partner; and Rodney<br />
Zemmel, a senior partner at the firm, write in<br />
their analysis of a survey entitled, 'Three new<br />
mandates for capturing a digital<br />
transformation's full value': "As organisations<br />
continue to navigate an era of massive<br />
uncertainty and disruption, digital tech is an<br />
increasingly critical differentiator of both<br />
strategy and performance. The actions of<br />
today's best-performing companies reflect that<br />
fact. For all other companies, three lessons<br />
emerge: use digital tech to achieve strategic<br />
differentiation on customer engagement and<br />
innovation; build proprietary assets, such as<br />
software, data and AI, then combine them with<br />
a scalable, cloud-based architecture to create<br />
a strategic advantage; and focus the quest for<br />
digital talent on C-suite and other executives,<br />
given the talent integration challenges that<br />
many companies continue to face."<br />
EDGE CO<strong>NC</strong>ERNS REMAIN<br />
Part of the digital transformation equation -<br />
particularly with the rise of the Internet of<br />
Things - is the growing use of edge computing.<br />
But while the pandemic has certainly led to a<br />
growth in edge and fog computing, as with<br />
digital transformation itself, some concerns<br />
remain. With edge computing, there is an<br />
increased number of attack points open to<br />
cyber-attacks. Also, the distance from the IoT<br />
devices creates limitations, and so there is a<br />
need to put computing power into the edge<br />
computing environment because of latency.<br />
Nevertheless, much still depends on where the<br />
'edge' is, and it very much depends on the<br />
communications infrastructure. That aside, with<br />
more storage and compute capacity at the<br />
edge, organisations can implement AI<br />
functionality, further reducing the workload at<br />
the central cloud compute node.<br />
With latency being a concern, to what extent<br />
does edge computing rely on artificial<br />
intelligence and machine learning to boost<br />
WAN performance? Well, for example, the<br />
pandemic has reshaped the way in which we<br />
now consume entertainment. There has been a<br />
massive transition from free to air television,<br />
24 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
FEATURE: WAN PERFORMA<strong>NC</strong>E<br />
cable TV and cinema to streaming services<br />
over the internet directly to the home. At<br />
present, autonomous vehicles are also<br />
nascent, and their foretold prediction is coming<br />
to fruition. Whilst streaming services are a big<br />
consumer of bandwidth, the individual data<br />
volume and speeds are not that great. It's the<br />
new high-volume applications that are causing<br />
problems in transmission times both to and<br />
from the edge. Even with edge undertaking<br />
data validation, there are massive amounts of<br />
data involved with each connected and<br />
autonomous vehicle.<br />
Traditional methods using compression and<br />
deduplication techniques will struggle to move<br />
this data between and across clouds - with<br />
their inherent latency issues, as well as<br />
requiring heavy compute capabilities. The only<br />
option that can move this volume of data with<br />
low compute overheads is WAN optimisation<br />
that uses AI to manage the data flow. However,<br />
it isn't capable of transferring encrypted data,<br />
nor does it completely fulfil its promise in terms<br />
of improving WAN performance.<br />
WAN ACCELERATION BOOST<br />
WAN Acceleration is, therefore, the answer,<br />
and it's needed where you have a lot of data -<br />
including where there is a certain amount of<br />
edge computation that needs to go back to a<br />
central location. That data includes what is<br />
received and transmitted to and from<br />
connected and autonomous vehicles, road<br />
and smart city infrastructure.<br />
There are two key factors that affect data<br />
transmission over long distances - latency and<br />
packet loss. Bandwidth is a factor as well, but<br />
past 10-15ms of latency. So, adding more<br />
bandwidth has little effect on data throughput.<br />
WAN Optimisation, which uses dedupe<br />
technology, is a great system if you are<br />
transmitting data that you have already seen<br />
(warm data), and when you have compressible<br />
data streams. If the data is "new" (cold data),<br />
then the process is typically slow. Every byte<br />
sequence has to be inspected. With cloud data<br />
that is transmitted over the internet, encryption<br />
is a must. If the data is already encrypted then<br />
WAN optimisation can only optimise the data if<br />
it has the keys - it first has to decrypt, optimise<br />
and re encrypt before it can transmit the data.<br />
Storage and power means it requires a larger<br />
edge node and therefore can increase costs.<br />
WAN optimisation and compression<br />
manipulate the data. WAN Acceleration<br />
approaches the issue from a different angle:<br />
the only way to reduce latency is to move the<br />
two nodes physically closer together. So,<br />
rather than manipulate the data, it manages<br />
the data flow across the connection to<br />
mitigate the effects of latency and packet loss<br />
by using parallel data streams across the<br />
network managed by AI. Utilisation and,<br />
therefore, throughput, is 90%+ of the<br />
network bandwidth.<br />
As the data is not manipulated in any way, the<br />
process is data agnostic and means there is no<br />
need to provide keys. WAN Acceleration is<br />
data agnostic and can transmit encrypted data.<br />
So, the transmission rate is the same as every<br />
other data type. Companies looking to deploy<br />
digital transformation, edge computing, IoT<br />
and the analysis of Big Data could benefit from<br />
WAN Acceleration.<br />
HIGHER WAN PERFORMA<strong>NC</strong>E<br />
My top 4 tips for achieving higher WAN<br />
performance to enable the innovation for<br />
digital transformation, edge computing and<br />
IoT as a result of this are:<br />
1. Remember that throwing more bandwidth at<br />
latency and packet loss won't increase WAN<br />
performance. This very rarely solves the issue<br />
and only increases your cost. If your<br />
throughput requirements aren't high and your<br />
data is compressible, think about implementing<br />
SD-WANs. Many of these have encryption and<br />
WAN optimisation options.<br />
2. Avoid, if possible, solutions that use UDP<br />
as the transmission protocol. It tends to be<br />
CPU intensive as it is trying to replicate a<br />
TCP/IP protocol and tends to have a low<br />
bandwidth capability - again increasing the<br />
cloud node costs.<br />
3. If your data is uncompressible or<br />
encrypted and you have high latency links<br />
with packet loss, the WAN Acceleration is an<br />
optimum choice.<br />
4. If network performance is key, select your<br />
edge and central node capability on<br />
network capacity.<br />
Ryan Perera, Vice President, Asia Content &<br />
Subsea Networks at Ciena, claims that the<br />
world is now operating on a distributed cloud<br />
computing environment. Consumer workloads,<br />
enterprise workloads, and now even telco's<br />
internal function workloads are being moved<br />
to the cloud: public, private, hybrid; then there<br />
is also the growth of edge computing.<br />
"Edge computing is an important part of this<br />
distributed cloud computing<br />
environment…[and it is] a natural extension of<br />
the core cloud", he writes in his article for The<br />
Economic Times' Telecom supplement. He<br />
believes there are several key macro trends that<br />
will impact on the distributed cloud computing<br />
world. They include the advent of 5G, the rise<br />
in residential networks demand and the high<br />
traffic across data centres.<br />
In addition to his own predictions, it's<br />
important to remember that when there are<br />
multiple edge instances, SD-WANs are a great<br />
technology. Bridgeworks has proved this with<br />
one large, international IT security company,<br />
and it has been shown that SD-WANs and<br />
WAN Acceleration are very complementary.<br />
They can work well together to support digital<br />
transformation, IoT, cloud and edge<br />
computing. SD-WAN performance is increased<br />
with an overlay of WAN Acceleration with<br />
solutions, such as PORTrockIT. To summarise, it<br />
is not always an either-or case. Technologies<br />
can complement each other. <strong>NC</strong><br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 25
OPINION: IOT<br />
HOW THE INTERNET OF THINGS IS<br />
REACHING MATURITY<br />
AFTER MANY YEARS OF HYPE, THE INTERNET OF THINGS (IOT) IS<br />
FINALLY MATURING TO A POINT WHERE ORGANISATIONS ARE<br />
TURNING STRATEGIES INTO REALITY AND PLANNING INTO ACTION,<br />
ACCORDING TO PHIL BEECHER, CEO AND PRESIDENT, WI-SUN<br />
ALLIA<strong>NC</strong>E<br />
This maturing of IoT comes across clearly<br />
in Wi-SUN's recent IoT research study, a<br />
follow up to the one we published in<br />
2017. It's clear that IoT is a much bigger IT<br />
priority for organisations than it was five years<br />
ago. Half of the research sample - IT decision<br />
makers in UK and US organisations across a<br />
range of industries - view IoT enablement as a<br />
top three priority for the next 12 months. It's<br />
also most likely to be the single top priority<br />
among respondents.<br />
Implementations and the technology itself are<br />
maturing and ambitions are growing. Decision<br />
makers see their peers benefitting from IoT<br />
initiatives and are looking increasingly to the<br />
technology to differentiate themselves in the<br />
market. More than 90% of respondents believe<br />
that they must invest in IoT over the next 12<br />
months to remain competitive.<br />
IoT can help to make them more agile - a<br />
key driver for adoption. This equips users to<br />
meet volatile operating conditions during a<br />
pandemic that has changed the operating<br />
rules, and new challenges we face in a rapidly<br />
changing world.<br />
Businesses and public sector bodies need to<br />
enhance their user experiences, both internally<br />
and externally, as they look for new ways to<br />
engage people in no-touch and remote<br />
environments. This is especially true for smart<br />
cities, which must find safe ways for<br />
increasingly dense populations to co-exist<br />
alongside each other.<br />
CHANGING IOT INITIATIVES<br />
Overall, plans to roll out IoT initiatives have<br />
grown. In 2017, respondents were asked<br />
about their plans to implement a series of<br />
different IoT-related projects, and the<br />
proportion stating that their organisation was<br />
'very likely' or 'definitely' going to deploy them<br />
within 12-18 months ranged from 57%-77%<br />
across various projects. In <strong>2022</strong>, this rose to<br />
72%-87%.<br />
While the use cases for utilities, including<br />
distribution automation and advanced meter<br />
infrastructure, remain popular, we are starting<br />
to see new opportunities emerge both for<br />
smart utility and smart city environments. Waste<br />
management sensors, for example, which<br />
could monitor bins and alert councils when<br />
they need emptying.<br />
With more vehicles on our roads and traffic<br />
congestion a growing problem, it's no surprise<br />
that traffic management is an area of<br />
increased focus for smart cities adopting IoT.<br />
More organisations are planning to implement<br />
traffic lights and controls, with an 18%<br />
increase, while smart parking saw the biggest<br />
rise since 2017, with 77% planning to deploy<br />
this, compared to 57% in 2017. It's clear from<br />
the report that environmental and<br />
sustainability-focused use cases are also<br />
moving up the IoT priority list, particularly for<br />
smart city initiatives.<br />
With the global urban population predicted<br />
to more than double by 2050, according to<br />
the World Bank, we will see smart technology<br />
playing an increasingly important role. This<br />
includes devices like pollution sensors that<br />
monitor air quality, acoustic sensors that<br />
measure noise levels, and an electric vehicle<br />
charging infrastructure that can cope with<br />
growing demand for electric vehicles.<br />
Two new initiatives on our list for <strong>2022</strong>,<br />
include water loss/leak detection and<br />
mandatory carbon monitoring, with three in<br />
four organisations planning to implement<br />
these. The opportunities for savings and<br />
increased efficiency in some of these use cases<br />
are high.<br />
But it's not just about environmental<br />
26 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
OPINION: IOT<br />
outcomes and efficiencies. Large-scale<br />
streetlighting projects are being rolled out<br />
across many cities, with three-quarters of<br />
respondents planning to deploy streetlighting<br />
projects in the next 12-18 months, up from<br />
61% in 2017.<br />
Such initiatives enable city developers and<br />
municipalities not only to control energy usage<br />
and costs across large installations, but also to<br />
maintain safety and security for residents and<br />
workers. Almost one in eight respondents in our<br />
report cite improving citizen safety and quality<br />
of life as a top driver for implementation.<br />
DRIVERS TO IOT ADOPTION<br />
When it comes to drivers to adoption, cost<br />
reduction is still the top one, but the<br />
motivations for implementing the technology<br />
are shifting. Just 6% of respondents rank<br />
reduction of operational costs as their top<br />
driver in <strong>2022</strong>, compared to 16% five years<br />
ago. The focus, it seems, has shifted largely to<br />
the need for competitive advantage, which<br />
perhaps demonstrates a maturing of IoT<br />
business cases, with organisations reimagining<br />
the technology as a way to stand out in a<br />
highly competitive marketplace.<br />
We introduced some new potential drivers<br />
this year, and one stood out; improving agility<br />
and the ability to react to the market,<br />
reinforcing the shift from internal efficiencies to<br />
a more external, user-focused approach.<br />
We saw another marked change<br />
demonstrating a shift from simple cost<br />
management to more sophisticated drivers<br />
affecting external stakeholders. One in ten<br />
respondents say that their top reason for<br />
implementing IoT initiatives and processes is<br />
that "everyone is doing it or thinking of doing<br />
it". Five years ago, only one respondent cited<br />
this as a reason. There's a sea change<br />
happening here; as more organisations deploy<br />
successful IoT projects and demonstrate the<br />
benefits of investing in this technology, others<br />
are taking notice.<br />
RECOGNISING THE CHALLENGES<br />
The journey to IoT maturity isn't without<br />
stumbling blocks, however. Smart cities, utilities<br />
and others adopting IoT still face challenges<br />
that prevent them from fully implementing the<br />
technology, but even these are shifting as their<br />
goals and understanding evolve.<br />
Our study has highlighted some interesting<br />
developments. While the number of<br />
respondents reporting extreme difficulty in<br />
implementing IoT went up slightly to 17% from<br />
14% in 2017, the number of people<br />
experiencing no challenges at all also went up<br />
to 14% from 9% in 2017. These increased<br />
numbers eroded the middle ground. Those<br />
experiencing only moderate difficulty fell 12%<br />
to 45% in <strong>2022</strong> compared to 57% five years<br />
ago. This suggests that as IoT projects continue<br />
to mature, adopters are becoming more adept<br />
at solving the easier problems while the harder<br />
ones remain, or sourcing expertise that can<br />
help them along the right path.<br />
While some of the barriers to adoption are<br />
certainly easing, others are increasing, as<br />
companies comprehend the full implications of<br />
designing and deploying an IoT solution. One<br />
that stands out is IT infrastructure complexity,<br />
concerns over which have risen by 10% in the<br />
last five years.<br />
As organisations look to more sophisticated<br />
use cases for IoT, integration challenges will<br />
naturally arise. IT and IoT have different<br />
technical and operating characteristics,<br />
ranging from the scale of implementation to<br />
the remote management challenges involved<br />
in IoT projects and data aggregation. It's<br />
understandable to see concerns as the<br />
approach to IoT migrates from discrete<br />
projects to more strategic initiatives.<br />
The much-reported shortage of technical<br />
talent is more evident as companies realise the<br />
complexity of creating and integrating IoT<br />
solutions. In 2017, 34% of respondents cited<br />
recruiting sufficient IoT talent as a challenge.<br />
This has now risen to 41% in the latest report.<br />
In <strong>2022</strong> and in a post-pandemic period,<br />
organisations are also less able to devote time<br />
or resources to IoT solutions in the face of other<br />
challenges. Over a third of respondents cite a<br />
need to reprioritise spending due to COVID-<br />
19. This has a direct impact on funding<br />
projects, with 35% of respondents citing<br />
pandemic-related budget cuts as an issue.<br />
THE ADVANTAGE OF OPEN STANDARDS<br />
The biggest change for IoT adopters is the<br />
importance of industry-wide open standards.<br />
One reason for this increased focus could be<br />
expansion. Companies that enjoyed benefits<br />
from IoT projects early on might have become<br />
more confident in the technology and explored<br />
other complementary projects. A city that<br />
deploys a smart lighting canopy, for example,<br />
can then use this distributed infrastructure as<br />
an integration point for other IoT initiatives,<br />
such as air quality sensors and traffic<br />
management. Open standards make it easier<br />
to integrate new IoT equipment and software<br />
with existing infrastructure, while lowering the<br />
cost of further deployments.<br />
IoT adopters are also thinking more about<br />
keeping their connectivity options open by<br />
supporting multiple network topologies. In the<br />
latest report, 68% prefer a hybrid network<br />
topology, supporting both star and mesh<br />
configurations, up from 58% five years ago,<br />
reflecting a move towards mesh-based<br />
networking. Star topologies lost significant<br />
traction, with 12% preferring it exclusively in<br />
<strong>2022</strong>, down from 21% in 2017.<br />
Five years ago, the market was less mature<br />
with many smart city and smart utility projects still<br />
in their infancy. Our latest research shows that<br />
organisations are becoming more ambitious<br />
and more sophisticated in their thinking - IoT is<br />
now a bigger priority than ever. <strong>NC</strong><br />
To see the full Wi-SUN alliance report visit<br />
https://wi-sun.org/iot-maturity-model/<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 27
AWARDS <strong>2022</strong><br />
SPONSORED BY:<br />
Photo gallery: https://flic.kr/s/aHBqjzYZk6<br />
YouTube: https://youtu.be/X6IL_D5o2YA<br />
The Network Computing Awards strike back!<br />
After being delayed due to the July<br />
rail strikes (perhaps we should've<br />
presented Network Rail with an<br />
award for 'Most Disruptive Network') we're<br />
very pleased to report that the <strong>2022</strong><br />
Network Computing Awards took place<br />
on July 21st at the Leonardo City Hotel in<br />
London. While the disruption and<br />
rescheduling ultimately affected the<br />
number of guests and nominees able to<br />
attend on the night there was still a great<br />
atmosphere at the evening awards<br />
ceremony, as talkSPORT's Paul Coyte<br />
revealed this year's winners assisted by<br />
Network Computing's David Bonner.<br />
Our <strong>2022</strong> winners include Fluke<br />
Networks, who won the New Product of<br />
the Year award for the FiberLert live fiber<br />
tester, Brigantia, who were named<br />
Distributor of the Year, and ExaGrid, who<br />
took home a trio of trophies including<br />
Company of the Year.<br />
Over the following pages you'll find a<br />
complete round-up of all of this year's<br />
winners and runners-up. We'd like to thank<br />
everyone who took the time to nominate<br />
and vote online, our awards sponsors, and<br />
all of our guests and nominees on the<br />
night, and offer our congratulations once<br />
more to all of this year's winners. We hope<br />
to see you all again next year - ideally<br />
without any more train strikes!<br />
www.networkcomputingawards.co.uk<br />
28 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS <strong>2022</strong><br />
NETWORK INFRASTRUCTURE PRODUCT OF THE YEAR<br />
WINNER: Zyxel Networks - Zyxel XS3800<br />
RUNNER-UP: Extreme Networks - Extreme IQ Site Engine<br />
The XS3800 switch is suitable for network aggregation such as SMB or campus network that require low latency and high-density 10G<br />
backbone architectures with basic routing capability. There are 16 dedicated 10G fibre ports and 8 Multi-gigabit combo ports that can be<br />
used as copper or fibre making it flexible for your networks. The XS3800 is also Nebula Flex Pro, which allows you to easily switch<br />
standalone management and intuitive Nebula cloud management platform with 1-year Pro Pack bundled anytime, with just a few clicks.<br />
DATA PROTECTION PRODUCT OF THE YEAR<br />
WINNER: Veritas Technologies - Veritas Backup Exec<br />
RUNNER-UP: Cohesity - Cohesity DataProtect<br />
With Backup Exec, you get a simple, powerful solution that ensures your business-critical data is never at risk of being lost, stolen, or<br />
corrupted. And as your data management needs grow, Backup Exec seamlessly scales to meet them-providing confidence and cost-savings<br />
over the long term.<br />
The speed of recovery is also crucial. Backup Exec provides Instant Recovery and Recovery Ready capabilities for VMware and Hyper-V<br />
virtual machines, and Instant Cloud Recovery with seamless failover for Microsoft's Azure Cloud in case of disaster. Support is also available<br />
for other generic S3 compatible cloud storage solutions like AWS and Google.<br />
TESTING/MONITORING PRODUCT OF THE YEAR<br />
WINNER: Netreo - Netreo<br />
RUNNER-UP: Endace - EndaceProbe Analytics Platform<br />
Netreo's full-stack IT Infrastructure Management (ITIM) solution features AIOps and high-performance Network Performance Monitoring and<br />
Diagnostics (NPMD) to empower enterprise and IT leaders with AIOps-driven observability, actionable insights, process automation, and<br />
accelerated issue resolution. By having real-time intelligence on all resources, devices and applications deployed in cloud, on-premises and<br />
hybrid networks.<br />
Netreo users have the confidence to deliver more reliable and innovative internal and external customer experiences. Netreo is one of Inc.<br />
5000's fastest-growing companies, trusted worldwide by thousands of private and public entities managing half a billion resources per day,<br />
and available via subscription in on-premises and cloud deployment models.<br />
TELEPHONY PRODUCT OF THE YEAR<br />
WINNER: CloudCall - CloudCall<br />
RUNNER-UP: MyPhones - Altos<br />
CloudCall helps businesses solve challenges by bringing people and technology closer together. We're an intelligent phone system, that<br />
captures the value of conversations and stores them within your CRM system; helping you to take control of your teams, work well from<br />
anywhere and complete more tasks, faster.<br />
As the only communications platform that's dedicated to businesses using CRM's, we work with some of the world's leading CRM systems<br />
across the recruitment, sales, and customer service sectors.<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards<br />
AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 29
AWARDS <strong>2022</strong><br />
STORAGE PRODUCT OF THE YEAR<br />
WINNER: ExaGrid - Tiered Backup Storage<br />
RUNNER-UP: Veritas - Veritas Backup Exec<br />
ExaGrid Tiered Backup Storage has a disk-cache Landing Zone tier for fast backup and restore performance, and a repository tier for the<br />
lowest cost long-term retention, as well as a scale-out architecture that ensures a fixed-length backup window as data grows, eliminating<br />
forklift upgrades and product obsolescence.<br />
In addition, ExaGrid offers the largest scale-out system in the industry-comprised of 32 EX84 appliances that can take in up to a 2.7PB full<br />
backup in a single system, which is 50% larger than any other solution with aggressive deduplication, and offers the only backup storage<br />
approach with a non-network-facing tier, delayed deletes, and immutable objects to recover from ransomware attacks.<br />
REMOTE WORKING PRODUCT OF THE YEAR<br />
WINNER: OneUp Sales - OneUp Sales<br />
RUNNER-UP: Mitel - Mitel Teamwork<br />
BEST SUPPLIER TO THE DATABASE<br />
WINNER: Prism DCS<br />
RUNNER-UP: Sudlows<br />
Prism DCS provides solutions for the data centre including hot aisle containment, cold aisle containment, caging and data centre cabinets.<br />
As the UK’s market leader, Prism has the right network rack, data or server cabinet for any application with secure online ordering and next<br />
day UK delivery. Each Prism cabinet can be pre-configured to suit your requirements and a wide range of off-the-shelf server rack<br />
accessories are available for both Prism PI and FI Range of cabinets.<br />
Call: 01923 698231 email: sales@prismdcs.co.uk<br />
NETWORK MANAGEMENT PRODUCT OF THE YEAR<br />
WINNER: Perle Systems - IOLAN SCG LWM Secure Console Server<br />
RUNNER-UP: Progress - Progress WhatsUp Gold<br />
The Perle IOLAN SCG LWM Console Server is a hardware solution that provides Out-of-Band (OOB) access to securely reboot ITequipment<br />
that has crashed or been powered down during network outages. The core idea is to preserve 24/7 network uptime by<br />
establishing secure direct access to the USB, RS232, or Ethernet console management port of critical IT assets like routers, switches,<br />
firewalls, servers, power, storage, and telecom appliances.<br />
Disruption and downtime are minimised by providing better visibility of the physical environment and the physical status of equipment. This<br />
ensures business continuity through improved uptime and efficiencies.<br />
30 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS <strong>2022</strong><br />
EDUCATION & TRAINING PROVIDER OF THE YEAR<br />
WINNER: CNet Training<br />
RUNNER-UP: Mindflex<br />
THE RETURN ON INVESTMENT AWARD<br />
WINNER: Veritas Technologies - Veritas BackupExec<br />
RUNNER-UP: OneUp Sales - OneUp Sales<br />
Veritas Backup Exec is the enhanced 'go-to' application to protect your data with fast and effective protection or recovery. Ransomware<br />
Resilience is just one of a number of vital data management tools available in the unified backup and recovery solution. Information is<br />
perpetually in a fluid state and can be held on private, public or hybrid clouds in Microsoft, Linux, UNIX or virtual workloads. Integrated with<br />
VMware, Microsoft and Linux platforms Backup Exec can protect one to thousands of servers and virtual machines from one user console.<br />
DISTRIBUTOR OF THE YEAR<br />
WINNER: Brigantia<br />
RUNNER-UP: Nuvias<br />
Formed from a management buyout from Claranet in 2016, Brigantia saw an opportunity to create a real value-adding cybersecurity and<br />
communications distributor that could serve channel partners across the UK & Ireland.<br />
Brigantia offers a complementary portfolio of market-leading vendors focusing on "layers" of protection. A portfolio that meets and exceeds<br />
every customer need, but which also offers the best managed service features, support, recurring revenue opportunities and margin for<br />
partners. An energised and award-winning team, led by Angus Shaw and headquartered in Ripon, North Yorkshire. Brigantia prides itself on<br />
putting customer service at the forefront of everything they do.<br />
RESELLER OF THE YEAR<br />
WINNER: Storm Technologies<br />
RUNNER-UP: 101 Data Solutions<br />
Established in June 2000, Storm has grown from strength to strength as a focused IT value-added reseller. Our business aim is to deliver<br />
exceptional service to our customers in corporate and public sector organisations. Whether you require developing a specific technology<br />
strategy or just looking for some knowledgeable and friendly guidance, we maintain top-tier accreditations to ensure we can bring you the<br />
best possible expertise and pricing. The success of your projects is what drives us. Our people and operations are second to none, we listen<br />
to you and deal with your enquiry quickly and efficiently irrespective of the size of your business.<br />
Storm Technologies are delighted to have won Reseller of the Year <strong>2022</strong> for another year running! We are incredibly proud of every member<br />
of the team at Storm, our success wouldn't be possible without them.<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards<br />
AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 31
AWARDS <strong>2022</strong><br />
NETWORK PROJECT OF THE YEAR<br />
WINNER: Boras Stad / Extreme Networks<br />
RUNNER-UP: The Inspiration Trust/Zyxel Networks<br />
In partnership with NetNordic, Extreme Networks has established one of the largest cloud-managed network infrastructures in Borås Stad,<br />
Sweden, transforming the municipality into a smart city. The new infrastructure delivers faster and more advanced connectivity, extending<br />
secure public Wi-Fi for its citizens, local government, schools, and services, while automating and simplifying network management for the<br />
IT team. The transition to smart cities is designed to provide more sustainable resources to residents, while improving quality of life and<br />
fueling business innovation.<br />
BE<strong>NC</strong>H TESTED PRODUCT OF THE YEAR<br />
WINNER: ExaGrid - EX84 RUNNER UP: Progress - Progress WhatsUp Gold <strong>2022</strong><br />
ExaGrid stands tall in the enterprise data backup and disaster recovery market as its Tiered Backup Storage family of EX appliances deliver a<br />
unique data protection solution with a sharp focus on performance and reduced storage costs<br />
Enterprises looking for new ways to energise their data protection strategies and reduce ongoing storage costs will find this ExaGrid and<br />
Commvault team provides an innovative solution. ExaGrid's scale-out architecture delivers huge, cost-effective backup capacities, its smart<br />
Landing Zone provides a boost in performance, and combining its Adaptive Deduplication with Commvault's own highly efficient data<br />
reduction technologies offers industry-leading storage savings.<br />
HARDWARE PRODUCT OF THE YEAR<br />
WINNER: Vertiv - Vertiv VRC-S Edge-Ready Micro Data Center System<br />
RUNNER-UP: Endace - EndaceProbe Analytics Platform<br />
Vertiv VRC-S is a micro data centre solution, fully assembled at the factory and designed specifically for IT edge applications. Available in<br />
various configurations, the Vertiv VRC-S is delivered in days and installed in hours. Choose from four different cabinet sizes with two<br />
separate cooling methods (split and self-contained) with back-up, and the option to integrate a UPS. Plus, an intelligent switched PDU,<br />
including monitoring of all components, and a comprehensive software package completes the offer.<br />
SOFTWARE PRODUCT OF THE YEAR<br />
WINNER: Rohde & Schwarz Cybersecurity - R&S®Browser in the Box<br />
RUNNER-UP: ExaGrid - ExaGrid Cloud Tier to AWS<br />
Developed with the German Federal Office for Information Security (BSI), the fully virtualised R&S®Browser in the Box surfing environment<br />
offers an innovative, multi-level concept for secure and convenient Internet surfing and optimum protection against malware for public<br />
authorities and companies.<br />
The virtual browser closes the "Internet" security gap by enabling a digital quarantine for attacks: malware is isolated before it even comes to<br />
execution. Instead of detecting malicious code - as with antivirus programs - execution is prevented from the outset. All potentially<br />
dangerous activities are isolated in a closed virtual browser.<br />
32 NETWORKcomputing AUGUST/SEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
AWARDS <strong>2022</strong><br />
CLOUD BASED SOLUTION OF THE YEAR<br />
WINNER: Juniper Networks - Mist AI<br />
RUNNER-UP: Extreme Networks - Extreme Cloud IQ<br />
Mist AI uses a combination of artificial intelligence, machine learning, and data science techniques to optimise user experiences and simplify<br />
operations across the wireless access, wired access, and SD-WAN domains.<br />
Data is ingested from numerous sources, including Juniper Mist Access Points, Switches, Session Smart Routers, and Firewalls for end-to-end<br />
insight into user experiences. These devices work in concert with Mist AI to optimise user experiences from client-to-cloud, including automated<br />
event correlation, root cause identification, Self-Driving Network operations, network assurance, proactive anomaly detection, and more.<br />
THE INSPIRATION AWARD<br />
WINNER: Andy Hirst - Sudlows<br />
RUNNER-UP: Angus Shaw - Brigantia<br />
As Managing Director of Sudlows, Andy heads the full critical infrastructure department. Andy has served as Chairman of the ECA ICCT and<br />
is an incorporated Engineer and Fellow of the IET. Andy promotes the upskilling of young engineers and is a mentor for the IET, and holds<br />
the uptime institutes' ATD and the TIA942 accreditation. Andy encoureages continual learning within his team and as a testimony to this has<br />
recently studied and attained his MSc in Data Centre Leadership and Management. Andy's drive within Sudlows has lead him to open up<br />
offices in the Middle East and India.<br />
THE CUSTOMER SERVICE AWARD<br />
WINNER: Prism DCS<br />
RUNNER-UP: Veritas Technologies<br />
Prism DCS is an award-winning data centre solutions provider specialising in the design, manufacture and installation of bespoke solutions<br />
including hot and cold aisle containment solutions, security caging and data centre cabinets. We utilise expert in-house design,<br />
manufacturing and installation teams to provide a high quality service with unrivalled lead times.<br />
Call: 01923 698231 email: sales@prismdcs.co.uk<br />
THE INNOVATION AWARD<br />
WINNER: Veritas Technologies - Backup Exec's Ransomware Resilience<br />
RUNNER-UP: Paessler - New sensors for PRTG<br />
Veritas has introduced Ransomware Resilience in its latest release of Veritas Backup Exec, the leading data management and security<br />
solution. Ransomware Resilience prevents data files on a wide range of media servers from being modified by unauthorised processes. It<br />
uses AI processes to monitor and actively inform administrators about data attacks. This is just one of a number of vital data management<br />
tools available in the unified backup and recovery solution.<br />
Backup Exec provides Instant Recovery and Recovery Ready capabilities for VMware and Hyper-V virtual machines, and Instant Cloud<br />
Recovery with seamless failover for Microsoft's Azure Cloud in case of disaster. Support is also available for other generic S3 compatible<br />
cloud storage solutions like AWS and Google.<br />
WWW.NETWORKCOMPUTING.CO.UK @<strong>NC</strong>MagAndAwards<br />
AUGUST/SEPTEMBER <strong>2022</strong> NETWORKcomputing 33
AWARDS <strong>2022</strong><br />
NEW PRODUCT OF THE YEAR<br />
WINNER: Fluke Networks - FiberLert<br />
RUNNER-UP: Trend Networks - LanTEK IV-S<br />
The FiberLert from Fluke Networks is an elegantly simple and eminently safe testing solution that is designed to detect active fibre signals,<br />
allowing it to be used to troubleshoot switch and host ports, transceivers, cables and polarity. It detects active signals in single-mode and<br />
multimode fibre with an infrared range of 850nm to 1625nm and can be used for ports and patch cords, SM, MM, UPC and APC<br />
connections. The FiberLert takes all the guesswork out of troubleshooting fibre activity, polarity and connectivity. It's very affordable and we<br />
found it so simple to use - right-thinking network engineers won't leave home without it.<br />
THE ONE TO WATCH COMPANY<br />
WINNER: Vertiv<br />
RUNNER-UP: Exclusive Networks<br />
With a deep history of industry-changing solutions and a well-earned reputation for innovation, Vertiv and its partners continue to raise the<br />
bar in the areas of power, cooling, access and control, monitoring, and manageability.<br />
Driven by customer satisfaction Vertiv supports any application with an extensive service offering including installation, startup,<br />
commissioning, maintenance, replacements, 24x7 remote monitoring and diagnostics,and much more. Vertiv offers the expertise you<br />
need, the reliability you demand, and the resources only a global partner can provide.<br />
PRODUCT OF THE YEAR<br />
WINNER: Rohde & Schwarz Cybersecurity - R&S®Browser in the Box<br />
RUNNER-UP: ExaGrid - Tiered Backup Storage<br />
Browser in the Box offers proactive protection against cyber attacks. Thanks to the separation of the Browser from the rest of the PC, you and<br />
your corporate network are protected against Trojans, ransomware, APTs and zero-day attacks. Java, JavaScript, Flash and the opening of<br />
dangerous links are no longer a threat. Developed in cooperation with the BSI, R&S®Browser in the Box provides full virtualisation and<br />
separation of Internet and intranet, delivering optimal protection against malware including harmful email attachments, along with the<br />
proactive blocking of all telemetry services.<br />
COMPANY OF THE YEAR<br />
WINNER: ExaGrid<br />
RUNNER-UP: Zyxel Networks<br />
"We are honoured to win the Company of the Year award" said Bill Andrews, President and CEO of ExaGrid. "Our company is solely<br />
focused on offering the best backup storage possible - by improving the performance, scalability, and economics of backup, and offering<br />
the best customer support in the industry. Many thanks to everyone who voted for us and to the editorial team at Network Computing, we<br />
are truly grateful."<br />
34 NETWORKcomputing AUGUST/DEPTEMBER <strong>2022</strong> @<strong>NC</strong>MagAndAwards<br />
WWW.NETWORKCOMPUTING.CO.UK
On-Prem Cloud Success Stories<br />
IDC Interviews with Three IT Leaders Achieving Superior Cost,<br />
Control and Competitive Advantage<br />
Powered by Intel ®<br />
Learn more at<br />
www.supermicro.com/en/on-prem-cloud