ModSecurity Handbook: Getting Started - Bad Request
ModSecurity Handbook: Getting Started - Bad Request
ModSecurity Handbook: Getting Started - Bad Request
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
vi<br />
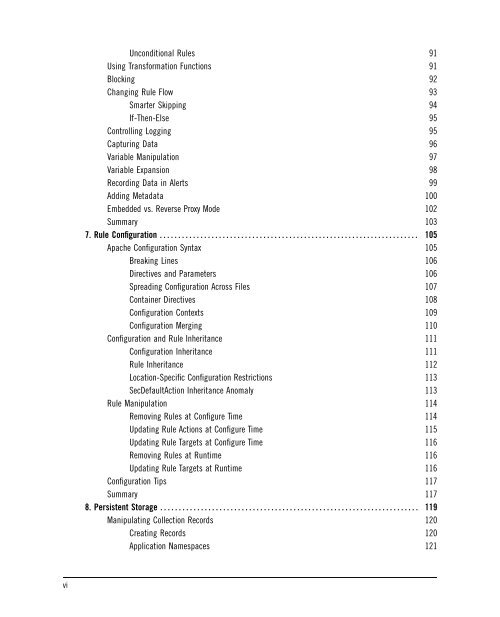
Unconditional Rules 91<br />
Using Transformation Functions 91<br />
Blocking 92<br />
Changing Rule Flow 93<br />
Smarter Skipping 94<br />
If-Then-Else 95<br />
Controlling Logging 95<br />
Capturing Data 96<br />
Variable Manipulation 97<br />
Variable Expansion 98<br />
Recording Data in Alerts 99<br />
Adding Metadata 100<br />
Embedded vs. Reverse Proxy Mode 102<br />
Summary 103<br />
7. Rule Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 105<br />
Apache Configuration Syntax 105<br />
Breaking Lines 106<br />
Directives and Parameters 106<br />
Spreading Configuration Across Files 107<br />
Container Directives 108<br />
Configuration Contexts 109<br />
Configuration Merging 110<br />
Configuration and Rule Inheritance 111<br />
Configuration Inheritance 111<br />
Rule Inheritance 112<br />
Location-Specific Configuration Restrictions 113<br />
SecDefaultAction Inheritance Anomaly 113<br />
Rule Manipulation 114<br />
Removing Rules at Configure Time 114<br />
Updating Rule Actions at Configure Time 115<br />
Updating Rule Targets at Configure Time 116<br />
Removing Rules at Runtime 116<br />
Updating Rule Targets at Runtime 116<br />
Configuration Tips 117<br />
Summary 117<br />
8. Persistent Storage . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119<br />
Manipulating Collection Records 120<br />
Creating Records 120<br />
Application Namespaces 121