Algorithms and Data Structures for External Memory
Algorithms and Data Structures for External Memory
Algorithms and Data Structures for External Memory
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
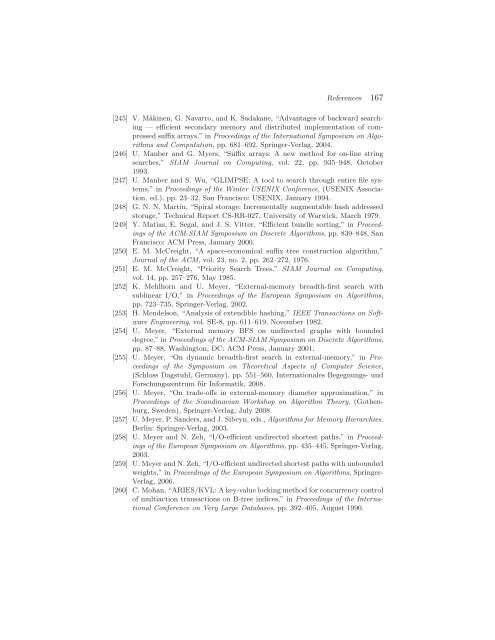
References 167<br />
[245] V. Mäkinen, G. Navarro, <strong>and</strong> K. Sadakane, “Advantages of backward searching<br />
— efficient secondary memory <strong>and</strong> distributed implementation of compressed<br />
suffix arrays,” in Proceedings of the International Symposium on <strong>Algorithms</strong><br />
<strong>and</strong> Computation, pp. 681–692, Springer-Verlag, 2004.<br />
[246] U. Manber <strong>and</strong> G. Myers, “Suffix arrays: A new method <strong>for</strong> on-line string<br />
searches,” SIAM Journal on Computing, vol. 22, pp. 935–948, October<br />
1993.<br />
[247] U. Manber <strong>and</strong> S. Wu, “GLIMPSE: A tool to search through entire file systems,”<br />
in Proceedings of the Winter USENIX Conference, (USENIX Association,<br />
ed.), pp. 23–32, San Francisco: USENIX, January 1994.<br />
[248] G. N. N. Martin, “Spiral storage: Incrementally augmentable hash addressed<br />
storage,” Technical Report CS-RR-027, University of Warwick, March 1979.<br />
[249] Y. Matias, E. Segal, <strong>and</strong> J. S. Vitter, “Efficient bundle sorting,” in Proceedings<br />
of the ACM-SIAM Symposium on Discrete <strong>Algorithms</strong>, pp. 839–848, San<br />
Francisco: ACM Press, January 2000.<br />
[250] E. M. McCreight, “A space-economical suffix tree construction algorithm,”<br />
Journal of the ACM, vol. 23, no. 2, pp. 262–272, 1976.<br />
[251] E. M. McCreight, “Priority Search Trees,” SIAM Journal on Computing,<br />
vol. 14, pp. 257–276, May 1985.<br />
[252] K. Mehlhorn <strong>and</strong> U. Meyer, “<strong>External</strong>-memory breadth-first search with<br />
sublinear I/O,” in Proceedings of the European Symposium on <strong>Algorithms</strong>,<br />
pp. 723–735, Springer-Verlag, 2002.<br />
[253] H. Mendelson, “Analysis of extendible hashing,” IEEE Transactions on Software<br />
Engineering, vol. SE-8, pp. 611–619, November 1982.<br />
[254] U. Meyer, “<strong>External</strong> memory BFS on undirected graphs with bounded<br />
degree,” in Proceedings of the ACM-SIAM Symposium on Discrete <strong>Algorithms</strong>,<br />
pp. 87–88, Washington, DC: ACM Press, January 2001.<br />
[255] U. Meyer, “On dynamic breadth-first search in external-memory,” in Proceedings<br />
of the Symposium on Theoretical Aspects of Computer Science,<br />
(Schloss Dagstuhl, Germany), pp. 551–560, Internationales Begegnungs- und<br />
Forschungszentrum für In<strong>for</strong>matik, 2008.<br />
[256] U. Meyer, “On trade-offs in external-memory diameter approximation,” in<br />
Proceedings of the Sc<strong>and</strong>inavian Workshop on Algorithm Theory, (Gothenburg,<br />
Sweden), Springer-Verlag, July 2008.<br />
[257] U. Meyer, P. S<strong>and</strong>ers, <strong>and</strong> J. Sibeyn, eds., <strong>Algorithms</strong> <strong>for</strong> <strong>Memory</strong> Hierarchies.<br />
Berlin: Springer-Verlag, 2003.<br />
[258] U. Meyer <strong>and</strong> N. Zeh, “I/O-efficient undirected shortest paths,” in Proceedings<br />
of the European Symposium on <strong>Algorithms</strong>, pp. 435–445, Springer-Verlag,<br />
2003.<br />
[259] U. Meyer <strong>and</strong> N. Zeh, “I/O-efficient undirected shortest paths with unbounded<br />
weights,” in Proceedings of the European Symposium on <strong>Algorithms</strong>, Springer-<br />
Verlag, 2006.<br />
[260] C. Mohan, “ARIES/KVL: A key-value locking method <strong>for</strong> concurrency control<br />
of multiaction transactions on B-tree indices,” in Proceedings of the International<br />
Conference on Very Large <strong>Data</strong>bases, pp. 392–405, August 1990.