C4 Marine Brig. Gen. Kevin J. Nally - KMI Media Group
C4 Marine Brig. Gen. Kevin J. Nally - KMI Media Group
C4 Marine Brig. Gen. Kevin J. Nally - KMI Media Group
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
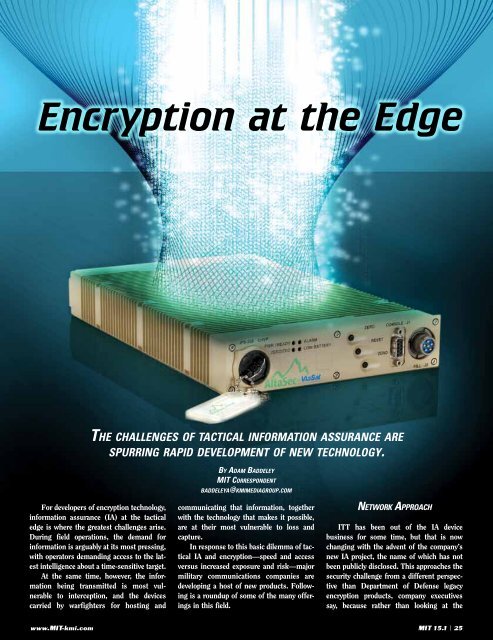
Encryption at the Edge<br />
For developers of encryption technology,<br />
information assurance (IA) at the tactical<br />
edge is where the greatest challenges arise.<br />
During field operations, the demand for<br />
information is arguably at its most pressing,<br />
with operators demanding access to the latest<br />
intelligence about a time-sensitive target.<br />
At the same time, however, the information<br />
being transmitted is most vulnerable<br />
to interception, and the devices<br />
carried by warfighters for hosting and<br />
www.MIT-kmi.com<br />
the Challenges of taCtICal InformatIon assuranCe are<br />
sPurrIng raPId develoPment of new teChnology.<br />
By adam Baddeley<br />
mIt CorresPondent<br />
Baddeleya@kmImedIagrouP.Com<br />
communicating that information, together<br />
with the technology that makes it possible,<br />
are at their most vulnerable to loss and<br />
capture.<br />
In response to this basic dilemma of tactical<br />
IA and encryption—speed and access<br />
versus increased exposure and risk—major<br />
military communications companies are<br />
developing a host of new products. Following<br />
is a roundup of some of the many offerings<br />
in this field.<br />
network aPProaCh<br />
ITT has been out of the IA device<br />
business for some time, but that is now<br />
changing with the advent of the company’s<br />
new IA project, the name of which has not<br />
been publicly disclosed. This approaches the<br />
security challenge from a different perspective<br />
than Department of Defense legacy<br />
encryption products, company executives<br />
say, because rather than looking at the<br />
MIT 15.1 | 25