challenge from a hardware perspective, it approaches the issue from the network side. The next generation secure network processors are in the final stages of the government approval process and have received broadbased support from different DoD bodies and government agencies. “We are bringing our information assurance products to market in the first and second quarter of 2011. The secure network processors themselves are complete and we are doing final testing,” said Ken Peterman, president of ITT Communications Systems. The first recipients of the new secure network processors will include ITT’s soldier radio-based solution for the Army-led Rifleman Radio requirement and secure smart phone technology. The new network approach is central, said Richard Takahashi, IA director. “The last major U.S. government crypto modernization was during the Reagan administration. During that time it was ARPAnet, not the Internet, and everything was single point encryption systems. The hardware and software encryption/cryptographic architectures/products that came out in the ’80s to early 1990s were, because of the applications and certification process, basically still pointto-point solutions [not network aware]. “Today, to use the older encryption hardware, designers have to wrap a lot of external logic around themselves to be network aware. Crypto modernization in 2010 has changed drastically, and is now about cyberinfrastructure—cyber-aware and network aware. We felt that to be a breakthrough technology, we had to design crypto differently to work within the Internet,” Takahashi explained. “ITT’s secure network processor is about the development of products that are a 10th of the power, a 10th the size, a 10th the cost but 10 times the processing power. We designed the engine so it can be applied not just to radios, but also products from USB 26 | MIT 15.1 Ken Peterman Richard Takahashi Chris Wren chris.wren@viasat.com drives and smart phones to entire networks—the whole plethora of systems that DoD needs.” This game-changing technology is made possible by the adoption of systemon-a-chip technology, which takes much of that peripheral circuitry into the device, thus saving on real estate as well as power and cost. “Our secure processor is a multi-architecture processor technology, with multicrypto processor,” Takahashi said. “It has nine RISC 32bit processors inside and offload engines for multiple types for crypto and packet engines, and it is fully programmable. We have designed our secure processor for today’s requirements, and projecting 10 years out for programmability and functionality.” ITT is leveraging and reusing core IA technology from a software/hardware perspective across a family of products. “When you get the fundamental DNA of this product family through the government certification processes, which is now very close, then instantiating that core technology into a variety of different applications across the product family becomes relatively quick to achieve,” Takahashi continued. Encryption is also central and integral to ITT’s tactical communications strategy. “In order to be able to compete effectively in the domestic and global market, one of those technologies is IA; another is RF transceiver technology that has sufficient capability to host wideband and narrowband military waveforms with complex attributes that include frequency hopping and Transec. The IA and the RF transceiver technology is fundamental to developing new products that achieve size weight and objectives. “Secondarily, it allows us to be able to take commercial products, like smart phones, and enhance them to incorporate genuine mid-grade security or to be able to implement military RF tactical waveforms as a companion capability,” he said. A key application for the crypto technology will be secure USB drives, which have been banned under DoD policy. “One of the things that we have come up with was to develop a trusted USB drive in such a way that it completely encrypts the information. Plus, it’s made by an American company in Indiana with a setup that can be trusted in such a way that it can be introduced into your network and there can be no fear of embedded virus or things that can attack you network,” Takahashi said. “That is going to enable the DoD customer to update that technology and change the game because we have a device that overcomes those kinds of vulnerabilities,” Peterman added. data at rest For Chris Wren, IA vice president at ViaSat, the core security challenge is ensuring that the level of security hitherto provided in buildings and data centers can be replicated in a mobile environment, giving warfighters access to classified data while simultaneously ensuring that the data remains secure should the device fall into the hands of opponents. The security of data “at rest” is a critical aspect of the issue, Wren noted. “We have done a lot in terms of data in transit, protecting the data from one entry point to another. But what about data stored on computing devices? What do you do to protect the data? We have recently purchased a company called Stonewood, which has a whole array of products for data at rest that are approved to protect classified data in the U.K. We are now working with the National Security Agency to get those products certified for use in the United States for Secret and below. I think the Eclypt product range from Stonewood is going to change the game in the way processors and end processing points are protected.” ViaSat’s KG200 and KG201 are currently the only Type 1 certified data-at-rest solutions for Top Secret data for DoD. “Right now, U.S. policy doesn’t demand that you have that level of encryption, because DoD doesn’t want to have a policy that no one can meet. We have those products now. So we are working with the services to make sure that policy is set up, which is really there to ensure that warfighters have what they need to do their job,” Wren said. Encryption products are having to adapt to vastly increased numbers of devices in use, www.MIT-kmi.com
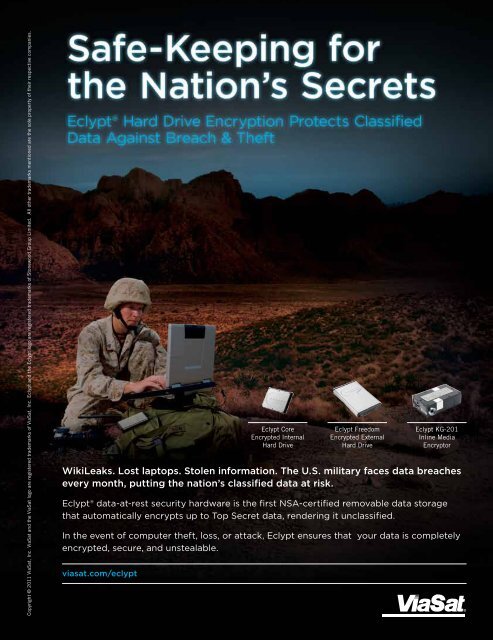
Copyright © 2011 ViaSat, Inc. ViaSat and the ViaSat logo are registered trademarks of ViaSat, Inc. Eclypt and the Eclypt logo are registered trademarks of Stonewood <strong>Group</strong> Limited. All other trademarks mentioned are the sole property of their respective companies. WikiLeaks. Lost laptops. Stolen information. The U.S. military faces data breaches every month, putting the nation’s classified data at risk. Eclypt® data-at-rest security hardware is the first NSA-certified removable data storage that automatically encrypts up to Top Secret data, rendering it unclassified. In the event of computer theft, loss, or attack, Eclypt ensures that your data is completely encrypted, secure, and unstealable. viasat.com/eclypt Eclypt Core Encrypted Internal Hard Drive Eclypt Freedom Encrypted External Hard Drive Eclypt KG-201 Inline <strong>Media</strong> Encryptor