1 Gaceta Digital FI ⢠No. 2 ⢠Febrero 2013 - Facultad de IngenierÃa
1 Gaceta Digital FI ⢠No. 2 ⢠Febrero 2013 - Facultad de IngenierÃa
1 Gaceta Digital FI ⢠No. 2 ⢠Febrero 2013 - Facultad de IngenierÃa
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
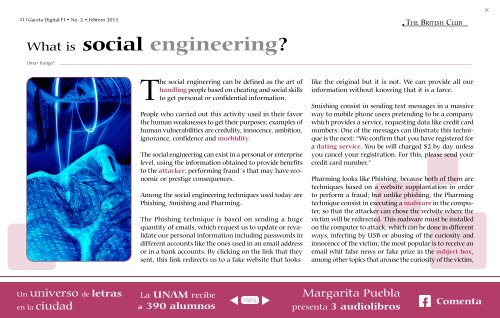
21 <strong>Gaceta</strong> <strong>Digital</strong> <strong>FI</strong> • <strong>No</strong>. 2 • <strong>Febrero</strong> <strong>2013</strong><br />
The British Club<br />
What is social engineering?<br />
Omar Rangel<br />
The social engineering can be <strong>de</strong>fined as the art of<br />
people based on cheating and social skills<br />
to get personal or confi<strong>de</strong>ntial information.<br />
People who carried out this activity used in their favor<br />
the human weaknesses to get their purposes; examples of<br />
human vulnerabilities are credulity, innocence, ambition,<br />
ignorance, confi<strong>de</strong>nce and<br />
The social engineering can exist in a personal or enterprise<br />
level, using the information obtained to provi<strong>de</strong> benefits<br />
to the , performing fraud´s that may have economic<br />
or prestige consequences.<br />
Among the social engineering techniques used today are<br />
Phishing, Smishing and Pharming.<br />
The Phishing technique is based on sending a huge<br />
quantity of emails, which request us to update or revalidate<br />
our personal information including passwords in<br />
different accounts like the ones used in an email address<br />
or in a bank accounts. By clicking on the link that they<br />
sent, this link redirects us to a fake website that looks<br />
like the original but it is not. We can provi<strong>de</strong> all our<br />
information without knowing that it is a farce.<br />
Smishing consist in sending text messages in a massive<br />
way to mobile phone users pretending to be a company<br />
which provi<strong>de</strong>s a service, requesting data like credit card<br />
numbers. One of the messages can illustrate this technique<br />
is the next: “We confirm that you have registered for<br />
a<br />
. You be will charged $2 by day unless<br />
you cancel your registration. For this, please send your<br />
credit card number.”<br />
Pharming looks like Phishing, because both of them are<br />
techniques based on a website supplantation in or<strong>de</strong>r<br />
to perform a fraud; but unlike phishing, the Pharming<br />
technique consist in executing a in the computer,<br />
so that the attacker can chose the website where the<br />
victim will be redirected. This malware must be installed<br />
on the computer to attack, which can be done in different<br />
ways, infecting by USB or abusing of the curiosity and<br />
innocence of the victim; the most popular is to receive an<br />
email whit false news or fake prize in the ,<br />
among other topics that arouse the curiosity of the victim,