1. ESET NOD32 Antivirus
1. ESET NOD32 Antivirus
1. ESET NOD32 Antivirus
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
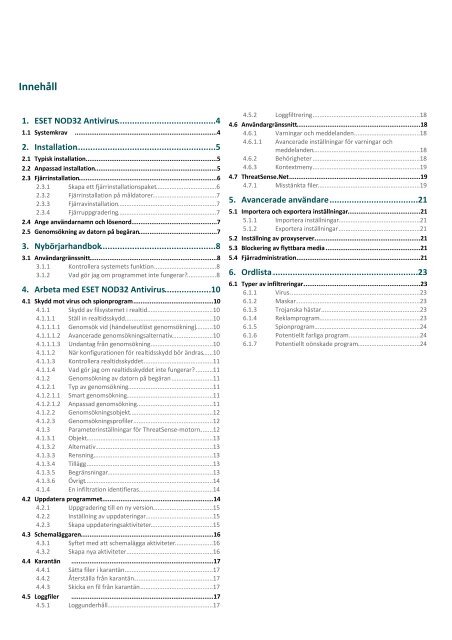
Innehåll<br />
<strong>1.</strong> <strong>ESET</strong> <strong>NOD32</strong> .............................................................4<br />
<strong>Antivirus</strong><br />
<strong>1.</strong>1<br />
Systemkrav<br />
..............................................................................4<br />
2. Installation .............................................................5<br />
2.1<br />
2.2<br />
2.3<br />
2.4<br />
2.5<br />
Typisk installation ..............................................................................5<br />
Anpassad installation ..............................................................................5<br />
Fjärrinstallation ..............................................................................6<br />
2.3.1 Skapa .............................................................................6<br />
ett fjärrinstallationspaket<br />
2.3.2 Fjärrinstallation .............................................................................7<br />
på måldatorer<br />
2.3.3 Fjärravinstallation<br />
.............................................................................7<br />
2.3.4 Fjärruppgradering<br />
.............................................................................7<br />
Ange användarnamn ..............................................................................7<br />
och lösenord<br />
Genomsökning ..............................................................................7<br />
av datorn på begäran<br />
3. Nybörjarhandbok .............................................................8<br />
3.1 Användargränssnitt ..............................................................................8<br />
3.<strong>1.</strong>1 Kontrollera .............................................................................8<br />
systemets funktion<br />
3.<strong>1.</strong>2 Vad gör .............................................................................8<br />
jag om programmet inte fungerar?<br />
4. Arbeta .............................................................10<br />
med <strong>ESET</strong> <strong>NOD32</strong> <strong>Antivirus</strong><br />
4.1 Skydd mot virus ..............................................................................10<br />
och spionprogram<br />
4.<strong>1.</strong>1 Skydd .............................................................................10<br />
av filsystemet i realtid<br />
4.<strong>1.</strong><strong>1.</strong>1 Ställ ............................................................................10<br />
in realtidsskydd<br />
4.<strong>1.</strong><strong>1.</strong><strong>1.</strong>1 Genomsök ..............................................................................10<br />
vid (händelseutlöst genomsökning)<br />
4.<strong>1.</strong><strong>1.</strong><strong>1.</strong>2 Avancerade ..............................................................................10<br />
genomsökningsalternativ<br />
4.<strong>1.</strong><strong>1.</strong><strong>1.</strong>3 Undantag ..............................................................................10<br />
från genomsökning<br />
4.<strong>1.</strong><strong>1.</strong>2 När konfigurationen ............................................................................10<br />
för realtidsskydd bör ändras<br />
4.<strong>1.</strong><strong>1.</strong>3 Kontrollera ............................................................................11<br />
realtidsskyddet<br />
4.<strong>1.</strong><strong>1.</strong>4 Vad gör ............................................................................11<br />
jag om realtidsskyddet inte fungerar?<br />
4.<strong>1.</strong>2 Genomsökning .............................................................................11<br />
av datorn på begäran<br />
4.<strong>1.</strong>2.1 Typ av ............................................................................11<br />
genomsökning<br />
4.<strong>1.</strong>2.<strong>1.</strong>1 Smart ..............................................................................11<br />
genomsökning<br />
4.<strong>1.</strong>2.<strong>1.</strong>2 Anpassad ..............................................................................11<br />
genomsökning<br />
4.<strong>1.</strong>2.2 Genomsökningsobjekt<br />
............................................................................12<br />
4.<strong>1.</strong>2.3 Genomsökningsprofiler<br />
............................................................................12<br />
4.<strong>1.</strong>3 Parameterinställningar .............................................................................12<br />
för ThreatSense-motorn<br />
4.<strong>1.</strong>3.1 Objekt ............................................................................13<br />
4.<strong>1.</strong>3.2 Alternativ ............................................................................13<br />
4.<strong>1.</strong>3.3 Rensning ............................................................................13<br />
4.<strong>1.</strong>3.4 Tillägg ............................................................................13<br />
4.<strong>1.</strong>3.5 Begränsningar ............................................................................13<br />
4.<strong>1.</strong>3.6 Övrigt ............................................................................14<br />
4.<strong>1.</strong>4 En infiltration .............................................................................14<br />
identifieras<br />
4.2 Uppdatera programmet<br />
..............................................................................14<br />
4.2.1 Uppgradering .............................................................................15<br />
till en ny version<br />
4.2.2 Inställning .............................................................................15<br />
av uppdateringar<br />
4.2.3 Skapa .............................................................................15<br />
uppdateringsaktiviteter<br />
4.3 Schemaläggaren ..............................................................................16<br />
4.3.1 Syftet .............................................................................16<br />
med att schemalägga aktiviteter<br />
4.3.2 Skapa .............................................................................16<br />
nya aktiviteter<br />
4.4 Karantän ..............................................................................17<br />
4.4.1 Sätta .............................................................................17<br />
filer i karantän<br />
4.4.2 Återställa .............................................................................17<br />
från karantän<br />
4.4.3 Skicka .............................................................................17<br />
en fil från karantän<br />
4.5 Loggfiler ..............................................................................17<br />
4.5.1 Loggunderhåll .............................................................................17<br />
4.6<br />
4.7<br />
4.5.2 Loggfiltrering .............................................................................18<br />
Användargränssnitt ..............................................................................18<br />
4.6.1 Varningar .............................................................................18<br />
och meddelanden<br />
4.6.<strong>1.</strong>1 Avancerade inställningar för varningar och<br />
meddelanden ............................................................................18<br />
4.6.2 Behörigheter .............................................................................18<br />
4.6.3 Kontextmeny .............................................................................19<br />
ThreatSense.Net ..............................................................................19<br />
4.7.1 Misstänkta .............................................................................19<br />
filer<br />
5. Avancerade .............................................................21<br />
användare<br />
5.1 Importera och ..............................................................................21<br />
exportera inställningar<br />
5.<strong>1.</strong>1 Importera .............................................................................21<br />
inställningar<br />
5.<strong>1.</strong>2 Exportera .............................................................................21<br />
inställningar<br />
5.2 Inställning av ..............................................................................21<br />
proxyserver<br />
5.3 Blockering av ..............................................................................21<br />
flyttbara media<br />
5.4 Fjärradministration ..............................................................................21<br />
6. Ordlista.............................................................23<br />
6.1 Typer av infiltreringar ..............................................................................23<br />
6.<strong>1.</strong>1 Virus .............................................................................23<br />
6.<strong>1.</strong>2 Maskar .............................................................................23<br />
6.<strong>1.</strong>3 Trojanska .............................................................................23<br />
hästar<br />
6.<strong>1.</strong>4 Reklamprogram<br />
.............................................................................23<br />
6.<strong>1.</strong>5 Spionprogram .............................................................................24<br />
6.<strong>1.</strong>6 Potentiellt .............................................................................24<br />
farliga program<br />
6.<strong>1.</strong>7<br />
Potentiellt .............................................................................24<br />
oönskade program