Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
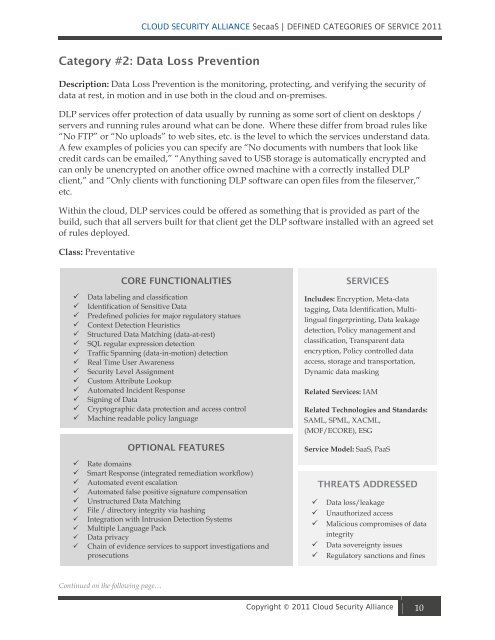
CLOUD SECURITY ALLIANCE SecaaS | DEFINED CATEGORIES OF SERVICE <strong>2011</strong><br />
Category #2: Data Loss Prevention<br />
Description: Data Loss Prevention is the monitoring, protecting, and verifying the security <strong>of</strong><br />
data at rest, in motion and in use both in the cloud and on-premises.<br />
DLP services <strong>of</strong>fer protection <strong>of</strong> data usually by running as some sort <strong>of</strong> client on desktops /<br />
servers and running rules around what can be done. Where these differ from broad rules like<br />
“No FTP” or “No uploads” to web sites, etc. is the level to which the services understand data.<br />
A few examples <strong>of</strong> policies you can specify are “No documents with numbers that look like<br />
credit cards can be emailed,” “Anything saved to USB storage is automatically encrypted and<br />
can only be unencrypted on another <strong>of</strong>fice owned machine with a correctly installed DLP<br />
client,” and “Only clients with functioning DLP s<strong>of</strong>tware can open files from the fileserver,”<br />
etc.<br />
Within the cloud, DLP services could be <strong>of</strong>fered as something that is provided as part <strong>of</strong> the<br />
build, such that all servers built for that client get the DLP s<strong>of</strong>tware installed with an agreed set<br />
<strong>of</strong> rules deployed.<br />
Class: Preventative<br />
CORE FUNCTIONALITIES<br />
Data labeling and classification<br />
Identification <strong>of</strong> Sensitive Data<br />
Predefined policies for major regulatory statues<br />
Context Detection Heuristics<br />
Structured Data Matching (data-at-rest)<br />
SQL regular expression detection<br />
Traffic Spanning (data-in-motion) detection<br />
Real Time User Awareness<br />
<strong>Security</strong> Level Assignment<br />
Custom Attribute Lookup<br />
Automated Incident Response<br />
Signing <strong>of</strong> Data<br />
Cryptographic data protection and access control<br />
Machine readable policy language<br />
OPTIONAL FEATURES<br />
Rate domains<br />
Smart Response (integrated remediation workflow)<br />
Automated event escalation<br />
Automated false positive signature compensation<br />
Unstructured Data Matching<br />
File / directory integrity via hashing<br />
Integration with Intrusion Detection Systems<br />
Multiple Language Pack<br />
Data privacy<br />
Chain <strong>of</strong> evidence services to support investigations and<br />
prosecutions<br />
Continued on the following page…<br />
SERVICES<br />
Includes: Encryption, Meta-data<br />
tagging, Data Identification, Multilingual<br />
fingerprinting, Data leakage<br />
detection, Policy management and<br />
classification, Transparent data<br />
encryption, Policy controlled data<br />
access, storage and transportation,<br />
Dynamic data masking<br />
Related <strong>Service</strong>s: IAM<br />
Related Technologies and Standards:<br />
SAML, SPML, XACML,<br />
(MOF/ECORE), ESG<br />
<strong>Service</strong> Model: SaaS, PaaS<br />
THREATS ADDRESSED<br />
Data loss/leakage<br />
Unauthorized access<br />
Malicious compromises <strong>of</strong> data<br />
integrity<br />
Data sovereignty issues<br />
Regulatory sanctions and fines<br />
Copyright © <strong>2011</strong> <strong>Cloud</strong> <strong>Security</strong> <strong>Alliance</strong> 10