Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
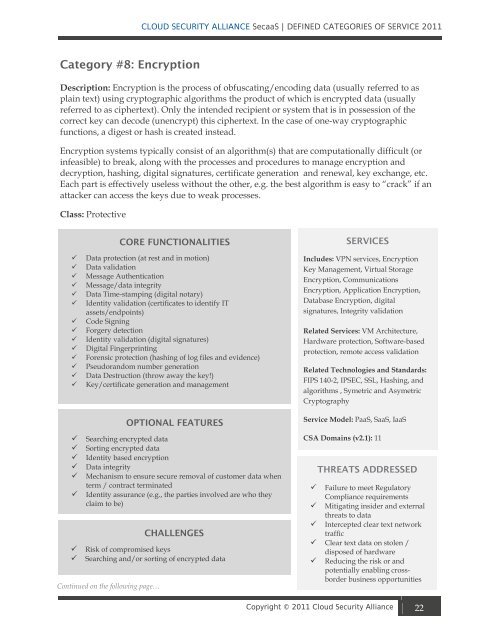
Category #8: Encryption<br />
CLOUD SECURITY ALLIANCE SecaaS | DEFINED CATEGORIES OF SERVICE <strong>2011</strong><br />
Description: Encryption is the process <strong>of</strong> obfuscating/encoding data (usually referred to as<br />
plain text) using cryptographic algorithms the product <strong>of</strong> which is encrypted data (usually<br />
referred to as ciphertext). Only the intended recipient or system that is in possession <strong>of</strong> the<br />
correct key can decode (unencrypt) this ciphertext. In the case <strong>of</strong> one-way cryptographic<br />
functions, a digest or hash is created instead.<br />
Encryption systems typically consist <strong>of</strong> an algorithm(s) that are computationally difficult (or<br />
infeasible) to break, along with the processes and procedures to manage encryption and<br />
decryption, hashing, digital signatures, certificate generation and renewal, key exchange, etc.<br />
Each part is effectively useless without the other, e.g. the best algorithm is easy to “crack” if an<br />
attacker can access the keys due to weak processes.<br />
Class: Protective<br />
CORE FUNCTIONALITIES<br />
Data protection (at rest and in motion)<br />
Data validation<br />
Message Authentication<br />
Message/data integrity<br />
Data Time-stamping (digital notary)<br />
Identity validation (certificates to identify IT<br />
assets/endpoints)<br />
Code Signing<br />
Forgery detection<br />
Identity validation (digital signatures)<br />
Digital Fingerprinting<br />
Forensic protection (hashing <strong>of</strong> log files and evidence)<br />
Pseudorandom number generation<br />
Data Destruction (throw away the key!)<br />
Key/certificate generation and management<br />
OPTIONAL FEATURES<br />
Searching encrypted data<br />
Sorting encrypted data<br />
Identity based encryption<br />
Data integrity<br />
Mechanism to ensure secure removal <strong>of</strong> customer data when<br />
term / contract terminated<br />
Identity assurance (e.g., the parties involved are who they<br />
claim to be)<br />
CHALLENGES<br />
Risk <strong>of</strong> compromised keys<br />
Searching and/or sorting <strong>of</strong> encrypted data<br />
Continued on the following page…<br />
SERVICES<br />
Includes: VPN services, Encryption<br />
Key Management, Virtual Storage<br />
Encryption, Communications<br />
Encryption, Application Encryption,<br />
Database Encryption, digital<br />
signatures, Integrity validation<br />
Related <strong>Service</strong>s: VM Architecture,<br />
Hardware protection, S<strong>of</strong>tware-based<br />
protection, remote access validation<br />
Related Technologies and Standards:<br />
FIPS 140-2, IPSEC, SSL, Hashing, and<br />
algorithms , Symetric and Asymetric<br />
Cryptography<br />
<strong>Service</strong> Model: PaaS, SaaS, IaaS<br />
CSA Domains (v2.1): 11<br />
THREATS ADDRESSED<br />
Failure to meet Regulatory<br />
Compliance requirements<br />
Mitigating insider and external<br />
threats to data<br />
Intercepted clear text network<br />
traffic<br />
Clear text data on stolen /<br />
disposed <strong>of</strong> hardware<br />
Reducing the risk or and<br />
potentially enabling crossborder<br />
business opportunities<br />
Copyright © <strong>2011</strong> <strong>Cloud</strong> <strong>Security</strong> <strong>Alliance</strong> 22