Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
CLOUD SECURITY ALLIANCE SecaaS | DEFINED CATEGORIES OF SERVICE <strong>2011</strong><br />
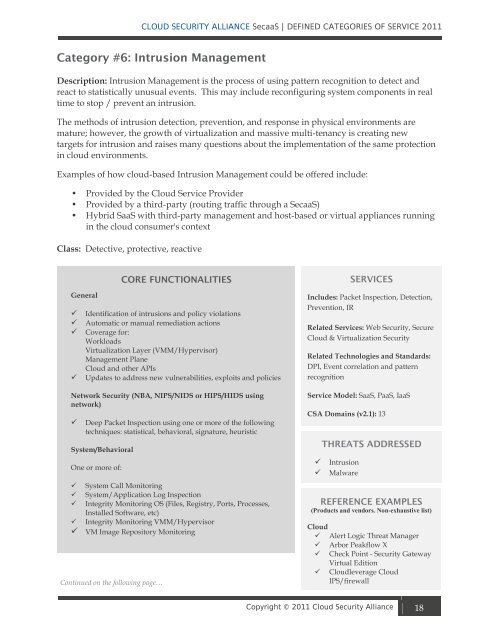
Category #6: Intrusion Management<br />
Description: Intrusion Management is the process <strong>of</strong> using pattern recognition to detect and<br />
react to statistically unusual events. This may include reconfiguring system components in real<br />
time to stop / prevent an intrusion.<br />
The methods <strong>of</strong> intrusion detection, prevention, and response in physical environments are<br />
mature; however, the growth <strong>of</strong> virtualization and massive multi-tenancy is creating new<br />
targets for intrusion and raises many questions about the implementation <strong>of</strong> the same protection<br />
in cloud environments.<br />
Examples <strong>of</strong> how cloud-based Intrusion Management could be <strong>of</strong>fered include:<br />
• Provided by the <strong>Cloud</strong> <strong>Service</strong> Provider<br />
• Provided by a third-party (routing traffic through a SecaaS)<br />
• Hybrid SaaS with third-party management and host-based or virtual appliances running<br />
in the cloud consumer's context<br />
Class: Detective, protective, reactive<br />
General<br />
CORE FUNCTIONALITIES<br />
Identification <strong>of</strong> intrusions and policy violations<br />
Automatic or manual remediation actions<br />
Coverage for:<br />
Workloads<br />
Virtualization Layer (VMM/Hypervisor)<br />
Management Plane<br />
<strong>Cloud</strong> and other APIs<br />
Updates to address new vulnerabilities, exploits and policies<br />
Network <strong>Security</strong> (NBA, NIPS/NIDS or HIPS/HIDS using<br />
network)<br />
Deep Packet Inspection using one or more <strong>of</strong> the following<br />
techniques: statistical, behavioral, signature, heuristic<br />
System/Behavioral<br />
One or more <strong>of</strong>:<br />
System Call Monitoring<br />
System/Application Log Inspection<br />
Integrity Monitoring OS (Files, Registry, Ports, Processes,<br />
Installed S<strong>of</strong>tware, etc)<br />
Integrity Monitoring VMM/Hypervisor<br />
VM Image Repository Monitoring<br />
Continued on the following page…<br />
SERVICES<br />
Includes: Packet Inspection, Detection,<br />
Prevention, IR<br />
Related <strong>Service</strong>s: Web <strong>Security</strong>, Secure<br />
<strong>Cloud</strong> & Virtualization <strong>Security</strong><br />
Related Technologies and Standards:<br />
DPI, Event correlation and pattern<br />
recognition<br />
<strong>Service</strong> Model: SaaS, PaaS, IaaS<br />
CSA Domains (v2.1): 13<br />
THREATS ADDRESSED<br />
Intrusion<br />
Malware<br />
REFERENCE EXAMPLES<br />
(Products and vendors. Non-exhaustive list)<br />
<strong>Cloud</strong><br />
Alert Logic Threat Manager<br />
Arbor Peakflow X<br />
Check Point - <strong>Security</strong> Gateway<br />
Virtual Edition<br />
<strong>Cloud</strong>leverage <strong>Cloud</strong><br />
IPS/firewall<br />
<br />
Copyright © <strong>2011</strong> <strong>Cloud</strong> <strong>Security</strong> <strong>Alliance</strong> 18