Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
Defined Categories of Service 2011 - Cloud Security Alliance
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
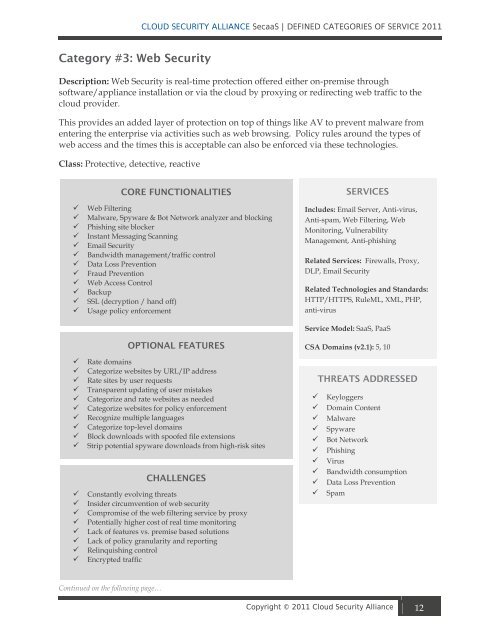
Category #3: Web <strong>Security</strong><br />
CLOUD SECURITY ALLIANCE SecaaS | DEFINED CATEGORIES OF SERVICE <strong>2011</strong><br />
Description: Web <strong>Security</strong> is real-time protection <strong>of</strong>fered either on-premise through<br />
s<strong>of</strong>tware/appliance installation or via the cloud by proxying or redirecting web traffic to the<br />
cloud provider.<br />
This provides an added layer <strong>of</strong> protection on top <strong>of</strong> things like AV to prevent malware from<br />
entering the enterprise via activities such as web browsing. Policy rules around the types <strong>of</strong><br />
web access and the times this is acceptable can also be enforced via these technologies.<br />
Class: Protective, detective, reactive<br />
CORE FUNCTIONALITIES<br />
Web Filtering<br />
Malware, Spyware & Bot Network analyzer and blocking<br />
Phishing site blocker<br />
Instant Messaging Scanning<br />
Email <strong>Security</strong><br />
Bandwidth management/traffic control<br />
Data Loss Prevention<br />
Fraud Prevention<br />
Web Access Control<br />
Backup<br />
SSL (decryption / hand <strong>of</strong>f)<br />
Usage policy enforcement<br />
OPTIONAL FEATURES<br />
Rate domains<br />
Categorize websites by URL/IP address<br />
Rate sites by user requests<br />
Transparent updating <strong>of</strong> user mistakes<br />
Categorize and rate websites as needed<br />
Categorize websites for policy enforcement<br />
Recognize multiple languages<br />
Categorize top-level domains<br />
Block downloads with spo<strong>of</strong>ed file extensions<br />
Strip potential spyware downloads from high-risk sites<br />
CHALLENGES<br />
Constantly evolving threats<br />
Insider circumvention <strong>of</strong> web security<br />
Compromise <strong>of</strong> the web filtering service by proxy<br />
Potentially higher cost <strong>of</strong> real time monitoring<br />
Lack <strong>of</strong> features vs. premise based solutions<br />
Lack <strong>of</strong> policy granularity and reporting<br />
Relinquishing control<br />
Encrypted traffic<br />
Continued on the following page…<br />
SERVICES<br />
Includes: Email Server, Anti-virus,<br />
Anti-spam, Web Filtering, Web<br />
Monitoring, Vulnerability<br />
Management, Anti-phishing<br />
Related <strong>Service</strong>s: Firewalls, Proxy,<br />
DLP, Email <strong>Security</strong><br />
Related Technologies and Standards:<br />
HTTP/HTTPS, RuleML, XML, PHP,<br />
anti-virus<br />
<strong>Service</strong> Model: SaaS, PaaS<br />
CSA Domains (v2.1): 5, 10<br />
THREATS ADDRESSED<br />
Keyloggers<br />
Domain Content<br />
Malware<br />
Spyware<br />
Bot Network<br />
Phishing<br />
Virus<br />
Bandwidth consumption<br />
Data Loss Prevention<br />
Spam<br />
Copyright © <strong>2011</strong> <strong>Cloud</strong> <strong>Security</strong> <strong>Alliance</strong> 12