- Page 1 and 2:
Proceedings of the 10th European Co
- Page 3 and 4:
Contents Paper Title Author(s) Page
- Page 5 and 6:
Paper Title Author(s) Page No. PhD
- Page 7 and 8:
Biographies of Conference Chairs, P
- Page 9 and 10:
esearch and teaching interest inclu
- Page 11:
Tampere, Military History and Strat
- Page 14 and 15:
Kari Alenius power and stayed there
- Page 16 and 17:
Kari Alenius The last two closely r
- Page 18 and 19:
Kari Alenius Bush, G. W. (2003-03-1
- Page 20 and 21:
Dominic Asamoah and William Oblitey
- Page 22 and 23:
Dominic Asamoah and William Oblitey
- Page 24 and 25:
Debi Ashenden cyberspace. As a resu
- Page 26 and 27:
Debi Ashenden (specifically the Bus
- Page 28 and 29:
Debi Ashenden implications are. It
- Page 30 and 31:
David Barnard-Wills Karen Fierke su
- Page 32 and 33:
David Barnard-Wills justifies prior
- Page 34 and 35:
David Barnard-Wills The extent to w
- Page 36 and 37:
Potential Threats of UAS Swarms and
- Page 38 and 39:
Isolated individuals Laurent Beaudo
- Page 40 and 41:
Laurent Beaudoinet al. priori the s
- Page 42 and 43:
Laurent Beaudoinet al. about approp
- Page 44 and 45:
Alexander Bligh The following paper
- Page 46 and 47:
Alexander Bligh Are differences in
- Page 48 and 49:
Alexander Bligh Characterization of
- Page 50 and 51:
A Secure Architecture for Electroni
- Page 52 and 53:
Paul Crocker and Vasco Nicolau Spo
- Page 54 and 55:
4.2 General overview Paul Crocker a
- Page 56 and 57:
4.3 Security layer Paul Crocker and
- Page 58 and 59:
Paul Crocker and Vasco Nicolau The
- Page 60 and 61:
Figure 14: Strong biometric authent
- Page 62 and 63:
Evaluation of the Armed Forces Webs
- Page 64 and 65:
1.2 The problem Pedro Cunha et al.
- Page 66 and 67:
Pedro Cunha et al. Another obtained
- Page 68 and 69:
Pedro Cunha et al. When classifying
- Page 70 and 71:
Christian Czosseck et al. The 2007
- Page 72 and 73:
3.1 Penal code Christian Czosseck e
- Page 74 and 75:
Christian Czosseck et al. Political
- Page 76 and 77:
Christian Czosseck et al. file_id=1
- Page 78 and 79:
Christian Czosseck and Karlis Podin
- Page 80 and 81:
Christian Czosseck and Karlis Podin
- Page 82 and 83:
Christian Czosseck and Karlis Podin
- Page 84 and 85:
Christian Czosseck and Karlis Podin
- Page 86 and 87:
Moses Dlamini et al. then tested in
- Page 88 and 89:
Moses Dlamini et al. Network of Liv
- Page 90 and 91:
Moses Dlamini et al. phase. This is
- Page 92 and 93:
Moses Dlamini et al. Santoro, R. an
- Page 94 and 95:
João Ferreira et al. Host-based In
- Page 96 and 97:
5. Proposed solution João Ferreira
- Page 98 and 99:
João Ferreira et al. Therefore, pu
- Page 100 and 101:
5.5 Profile updating João Ferreira
- Page 102 and 103:
João Ferreira et al. Lynch, D.M. (
- Page 104 and 105:
Eric Filiol et al. exist as well an
- Page 106 and 107:
Eric Filiol et al. Level 2: warnin
- Page 108 and 109:
Eric Filiol et al. method “saveAs
- Page 110 and 111:
puts("Key Generated"); Eric Filiol
- Page 112 and 113:
eturn -1; size = strlen(file); rt =
- Page 114 and 115:
4.2 Email wiretapping Eric Filiol e
- Page 116 and 117:
Eric Filiol et al. For Each myItem2
- Page 118 and 119:
The Computer Security of Public/Ope
- Page 120 and 121:
A USB stick containing portable app
- Page 122 and 123:
Eric Filiol Figure 2: Document of t
- Page 124 and 125:
Eric Filiol when pluging those USB
- Page 126 and 127:
Marthie Grobler et al. for launchin
- Page 128 and 129:
Marthie Grobler et al. situation ha
- Page 130 and 131:
Marthie Grobler et al. meaning of s
- Page 132 and 133:
Number of responses 5 4 3 2 1 0 Phy
- Page 134 and 135:
Missionaries of Peace - The Creatio
- Page 136 and 137: Marja Härmänmaa In most cases the
- Page 138 and 139: Marja Härmänmaa romanità, to ser
- Page 140 and 141: Arto Hirvelä OPSEC is concerned wi
- Page 142 and 143: Arto Hirvelä feeling and action of
- Page 144 and 145: Live-Action Role-Play as a Scenario
- Page 146 and 147: Sara Hjalmarsson Cohn et al. (2002)
- Page 148 and 149: Sara Hjalmarsson experience may be
- Page 150 and 151: Sara Hjalmarsson The methodology us
- Page 152 and 153: Sara Hjalmarsson ELIN (2010). “We
- Page 154 and 155: Aki-Mauri Huhtinen between Wikileak
- Page 156 and 157: Aki-Mauri Huhtinen example, militar
- Page 158 and 159: 4.3 Games of the 'postmodern world'
- Page 160 and 161: Information Security Culture or Inf
- Page 162 and 163: Ilona Ilvonen an explicit form and
- Page 164 and 165: Ilona Ilvonen All of the previous s
- Page 166 and 167: Ilona Ilvonen Schlienger, T. & Teuf
- Page 168 and 169: Saara Jantunen The Revolution in Mi
- Page 170 and 171: Saara Jantunen Table 1: "Sample IO
- Page 172 and 173: Saara Jantunen neutralization — (
- Page 174 and 175: Saara Jantunen Raytheon (2010) 'Tim
- Page 176 and 177: Saara Jantunen and Aki-Mauri Huhtin
- Page 178 and 179: Saara Jantunen and Aki-Mauri Huhtin
- Page 180 and 181: Saara Jantunen and Aki-Mauri Huhtin
- Page 182 and 183: Saara Jantunen and Aki-Mauri Huhtin
- Page 184 and 185: Evolutionary Algorithms for Optimal
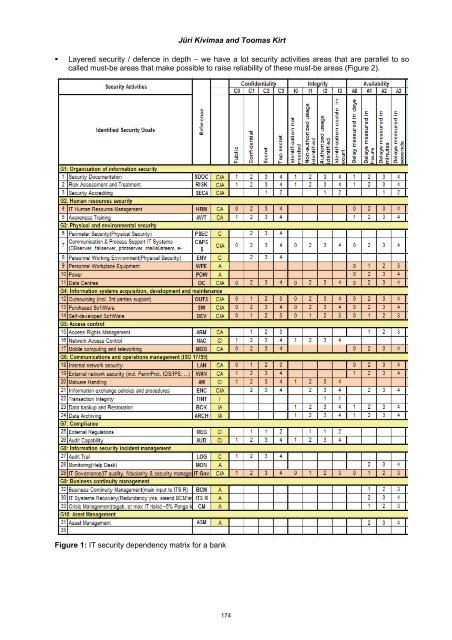
- Page 188 and 189: 2.2 Model optimization Jüri Kivima
- Page 190 and 191: Jüri Kivimaa and Toomas Kirt 5.1.1
- Page 192 and 193: Jüri Kivimaa and Toomas Kirt Fogel
- Page 194 and 195: Jüri Kivimaa and Toomas Kirt As we
- Page 196 and 197: Jüri Kivimaa and Toomas Kirt evolu
- Page 198 and 199: Luís Mendonça and Henrique Santos
- Page 200 and 201: Luís Mendonça and Henrique Santos
- Page 202 and 203: Luís Mendonça and Henrique Santos
- Page 204 and 205: Luís Mendonça and Henrique Santos
- Page 206 and 207: Analysis and Modelling of Critical
- Page 208 and 209: Graeme Pye and Matthew Warren Conn
- Page 210 and 211: Graeme Pye and Matthew Warren 4. Cr
- Page 212 and 213: Graeme Pye and Matthew Warren 7. Au
- Page 214 and 215: Modelling Relational Aspects of Cri
- Page 216 and 217: Graeme Pye and Matthew Warren Tradi
- Page 218 and 219: Graeme Pye and Matthew Warren envir
- Page 220 and 221: Graeme Pye and Matthew Warren A fe
- Page 222 and 223: Graeme Pye and Matthew Warren North
- Page 224 and 225: 3. eGovernment stages @ Kasi Raju T
- Page 226 and 227: Kasi Raju Facilities like single-w
- Page 228 and 229: Figure 2: Usage of online facilitie
- Page 230 and 231: Kasi Raju Figure 5: Suggestion for
- Page 232 and 233: Kasi Raju Figure 6b: Future plan to
- Page 234 and 235: Neil Rowe et al. date. It is time t
- Page 236 and 237:
Neil Rowe et al. sampling of traffi
- Page 238 and 239:
Neil Rowe et al. (Erbschloe 2001).
- Page 240 and 241:
Distributed Denial of Service Attac
- Page 242 and 243:
2.1.1 Smurf / ICMP Libor Sarga and
- Page 244 and 245:
Figure 2: Procedural decision-makin
- Page 246 and 247:
Libor Sarga and Roman Jašek eBay s
- Page 248 and 249:
References Libor Sarga and Roman Ja
- Page 250 and 251:
Małgorzata Skórzewska-Amberg and
- Page 252 and 253:
Małgorzata Skórzewska-Amberg trat
- Page 254 and 255:
Małgorzata Skórzewska-Amberg Rest
- Page 256 and 257:
Małgorzata Skórzewska-Amberg It i
- Page 258 and 259:
Ewald Stieger and Rossouw von Solms
- Page 260 and 261:
Ewald Stieger and Rossouw von Solms
- Page 262 and 263:
4.2.5 Evolving Ewald Stieger and Ro
- Page 264 and 265:
Ewald Stieger and Rossouw von Solms
- Page 266 and 267:
Anna-Maria Talihärm all have impac
- Page 268 and 269:
Anna-Maria Talihärm introducing co
- Page 270 and 271:
Anna-Maria Talihärm among the many
- Page 272 and 273:
Anna-Maria Talihärm Council of Eur
- Page 274 and 275:
Risto Vaarandi monitoring, since th
- Page 276 and 277:
Risto Vaarandi supersets with the s
- Page 278 and 279:
Risto Vaarandi During the experimen
- Page 280 and 281:
Locating the Enemy Marja Vuorinen U
- Page 282 and 283:
Marja Vuorinen Needless to say, an
- Page 284 and 285:
Marja Vuorinen society into lower,
- Page 286 and 287:
Marja Vuorinen Huhta, I. (2001) ”
- Page 288 and 289:
Matthew Warren and Shona Leitch In
- Page 290 and 291:
Matthew Warren and Shona Leitch 39
- Page 292 and 293:
Matthew Warren and Shona Leitch thi
- Page 294 and 295:
282
- Page 296 and 297:
Mudassar Aslam and Christian Gehrma
- Page 298 and 299:
Table 1: Telecommunication cloud th
- Page 300 and 301:
Mudassar Aslam and Christian Gehrma
- Page 302 and 303:
Mudassar Aslam and Christian Gehrma
- Page 304 and 305:
Anthony Desnos and Geoffroy Gueguen
- Page 306 and 307:
Anthony Desnos and Geoffroy Gueguen
- Page 308 and 309:
Anthony Desnos and Geoffroy Gueguen
- Page 310 and 311:
Regulatory Compliance to Ensure Inf
- Page 312 and 313:
2.1 Research model Andro Kull The i
- Page 314 and 315:
Andro Kull IT risk management is th
- Page 316 and 317:
Andro Kull Presented classic inform
- Page 318 and 319:
Andro Kull Risk assessment was ment
- Page 320 and 321:
Fudong Li et al. several networks s
- Page 322 and 323:
Fudong Li et al. users have the fre
- Page 324 and 325:
Fudong Li et al. Table 4: Experimen
- Page 326 and 327:
Fudong Li et al. authentication mec
- Page 328 and 329:
2. COBIT Teresa Pereira and Henriqu
- Page 330 and 331:
ITIL Transition; ITIL Operation;
- Page 332 and 333:
Teresa Pereira and Henrique Santos
- Page 334 and 335:
6. Conclusions and future work Tere
- Page 336 and 337:
Mirva Salminen shooting and the dis
- Page 338 and 339:
Mirva Salminen supplement to the US
- Page 340 and 341:
Mirva Salminen armed vehicle. A thi
- Page 342 and 343:
330
- Page 344 and 345:
332
- Page 346 and 347:
Andrea Rigoni and Salvatore Di Blas
- Page 348 and 349:
Andrea Rigoni and Salvatore Di Blas
- Page 350 and 351:
338
- Page 352 and 353:
Robert Erra Denial Of Services (DOS