Report - CrySyS Lab
Report - CrySyS Lab
Report - CrySyS Lab
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
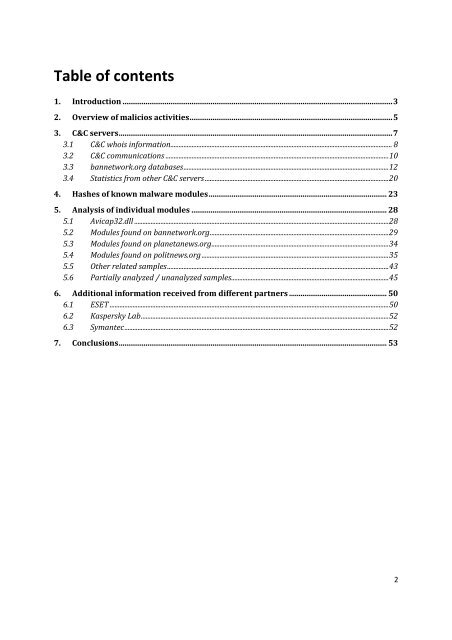
Table of contents<br />
1. Introduction .............................................................................................................................................3<br />
2. Overview of malicios activities..........................................................................................................5<br />
3. C&C servers...............................................................................................................................................7<br />
3.1 C&C whois information....................................................................................................................................... 8<br />
3.2 C&C communications ........................................................................................................................................10<br />
3.3 bannetwork.org databases.............................................................................................................................12<br />
3.4 Statistics from other C&C servers ................................................................................................................20<br />
4. Hashes of known malware modules............................................................................................. 23<br />
5. Analysis of individual modules ...................................................................................................... 28<br />
5.1 Avicap32.dll ...........................................................................................................................................................28<br />
5.2 Modules found on bannetwork.org.............................................................................................................29<br />
5.3 Modules found on planetanews.org............................................................................................................34<br />
5.4 Modules found on politnews.org..................................................................................................................35<br />
5.5 Other related samples.......................................................................................................................................43<br />
5.6 Partially analyzed / unanalyzed samples................................................................................................45<br />
6. Additional information received from different partners ................................................... 50<br />
6.1 ESET ..........................................................................................................................................................................50<br />
6.2 Kaspersky <strong>Lab</strong>.......................................................................................................................................................52<br />
6.3 Symantec.................................................................................................................................................................52<br />
7. Conclusions............................................................................................................................................ 53<br />
2