Report - CrySyS Lab
Report - CrySyS Lab
Report - CrySyS Lab
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
5. Analysis of individual modules<br />
5.1 Avicap32.dll<br />
The investigation described in this document was started by the discovery of unusual network traffic<br />
patterns. Later, it was found that the suspicious network traffic is due to a malware based on the<br />
TeamViewer application. The installation of the malware is based on a NullSoft installer. We are<br />
aware of two versions of this installer using the filenames DSC.exe and TeamViewer.ico. During<br />
installation, the following files are saved into the folder “\Documents and Settings\user\Application<br />
Data”:<br />
avicap32.dll<br />
TeamViewer.exe (d0847c10f8b2253b194cda859d3a52a3)<br />
TeamViewer_Resource_ru.dll (165e720c32ae372864b9b654e44e2650)<br />
tv.cfg<br />
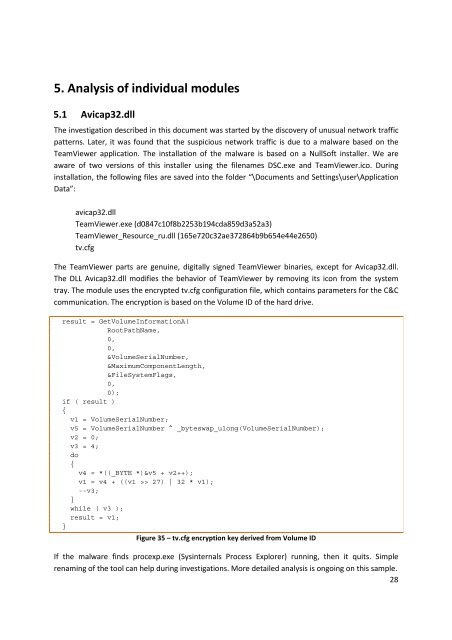
The TeamViewer parts are genuine, digitally signed TeamViewer binaries, except for Avicap32.dll.<br />
The DLL Avicap32.dll modifies the behavior of TeamViewer by removing its icon from the system<br />
tray. The module uses the encrypted tv.cfg configuration file, which contains parameters for the C&C<br />
communication. The encryption is based on the Volume ID of the hard drive.<br />
result = GetVolumeInformationA(<br />
RootPathName,<br />
0,<br />
0,<br />
&VolumeSerialNumber,<br />
&MaximumComponentLength,<br />
&FileSystemFlags,<br />
0,<br />
0);<br />
if ( result )<br />
{<br />
v1 = VolumeSerialNumber;<br />
v5 = VolumeSerialNumber ^ _byteswap_ulong(VolumeSerialNumber);<br />
v2 = 0;<br />
v3 = 4;<br />
do<br />
{<br />
v4 = *((_BYTE *)&v5 + v2++);<br />
v1 = v4 + ((v1 >> 27) | 32 * v1);<br />
--v3;<br />
}<br />
while ( v3 );<br />
result = v1;<br />
}<br />
Figure 35 – tv.cfg encryption key derived from Volume ID<br />
If the malware finds procexp.exe (Sysinternals Process Explorer) running, then it quits. Simple<br />
renaming of the tool can help during investigations. More detailed analysis is ongoing on this sample.<br />
28