Report - CrySyS Lab
Report - CrySyS Lab
Report - CrySyS Lab
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
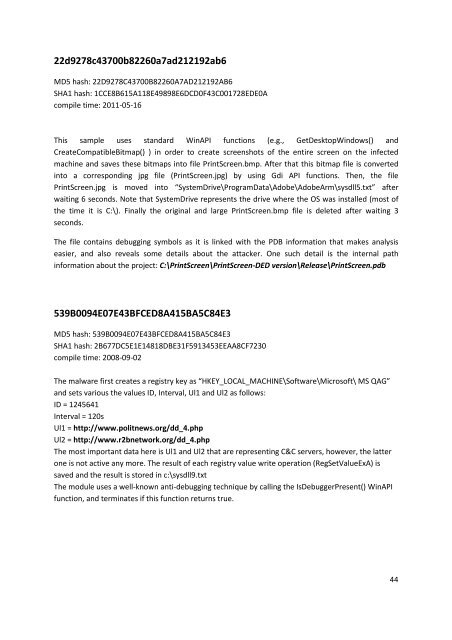
22d9278c43700b82260a7ad212192ab6<br />
MD5 hash: 22D9278C43700B82260A7AD212192AB6<br />
SHA1 hash: 1CCE8B615A118E49898E6DCD0F43C001728EDE0A<br />
compile time: 2011-05-16<br />
This sample uses standard WinAPI functions (e.g., GetDesktopWindows() and<br />
CreateCompatibleBitmap() ) in order to create screenshots of the entire screen on the infected<br />
machine and saves these bitmaps into file PrintScreen.bmp. After that this bitmap file is converted<br />
into a corresponding jpg file (PrintScreen.jpg) by using Gdi API functions. Then, the file<br />
PrintScreen.jpg is moved into “SystemDrive\ProgramData\Adobe\AdobeArm\sysdll5.txt” after<br />
waiting 6 seconds. Note that SystemDrive represents the drive where the OS was installed (most of<br />
the time it is C:\). Finally the original and large PrintScreen.bmp file is deleted after waiting 3<br />
seconds.<br />
The file contains debugging symbols as it is linked with the PDB information that makes analysis<br />
easier, and also reveals some details about the attacker. One such detail is the internal path<br />
information about the project: C:\PrintScreen\PrintScreen-DED version\Release\PrintScreen.pdb<br />
539B0094E07E43BFCED8A415BA5C84E3<br />
MD5 hash: 539B0094E07E43BFCED8A415BA5C84E3<br />
SHA1 hash: 2B677DC5E1E14818DBE31F5913453EEAA8CF7230<br />
compile time: 2008-09-02<br />
The malware first creates a registry key as “HKEY_LOCAL_MACHINE\Software\Microsoft\ MS QAG”<br />
and sets various the values ID, Interval, Ul1 and Ul2 as follows:<br />
ID = 1245641<br />
Interval = 120s<br />
Ul1 = http://www.politnews.org/dd_4.php<br />
Ul2 = http://www.r2bnetwork.org/dd_4.php<br />
The most important data here is Ul1 and Ul2 that are representing C&C servers, however, the latter<br />
one is not active any more. The result of each registry value write operation (RegSetValueExA) is<br />
saved and the result is stored in c:\sysdll9.txt<br />
The module uses a well-known anti-debugging technique by calling the IsDebuggerPresent() WinAPI<br />
function, and terminates if this function returns true.<br />
44