Report - CrySyS Lab
Report - CrySyS Lab
Report - CrySyS Lab
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Note that the word “saidumlo” means “secret” in Georgian (საიდუმლო), and *секрет*.* and<br />
*парол*.* are written in Cyrillic and they mean “secret” and “password”, respectively, in Russian.<br />
Based on these templates, we can conclude that the attackers are interested in office documents and<br />
files (e.g., *.doc, *.rtf, *.xls, *.mdb), pdf files (*.pdf), disk images (e.g., *.tc, *.vmdk), as well as files<br />
that potentially contain sensitive information such as keys (e.g.,*. pgp, *.p12) and passwords (e.g.,<br />
*pass*, *secret*, *saidumlo*, *секрет*.* and *парол*.*).<br />
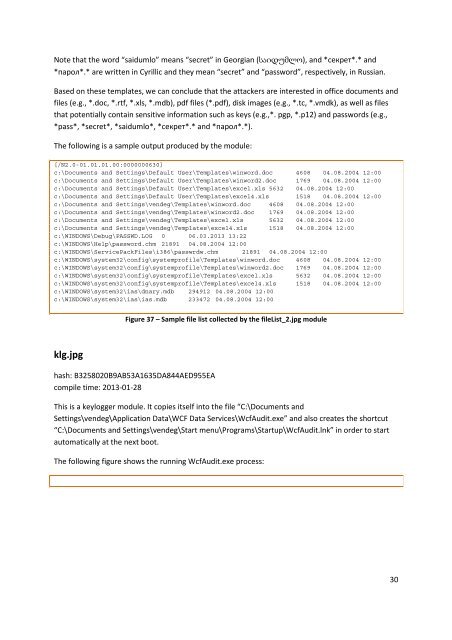
The following is a sample output produced by the module:<br />
[/N2.0-01.01.01.00:0000000630]<br />
c:\Documents and Settings\Default User\Templates\winword.doc 4608 04.08.2004 12:00<br />
c:\Documents and Settings\Default User\Templates\winword2.doc 1769 04.08.2004 12:00<br />
c:\Documents and Settings\Default User\Templates\excel.xls 5632 04.08.2004 12:00<br />
c:\Documents and Settings\Default User\Templates\excel4.xls 1518 04.08.2004 12:00<br />
c:\Documents and Settings\vendeg\Templates\winword.doc 4608 04.08.2004 12:00<br />
c:\Documents and Settings\vendeg\Templates\winword2.doc 1769 04.08.2004 12:00<br />
c:\Documents and Settings\vendeg\Templates\excel.xls 5632 04.08.2004 12:00<br />
c:\Documents and Settings\vendeg\Templates\excel4.xls 1518 04.08.2004 12:00<br />
c:\WINDOWS\Debug\PASSWD.LOG 0 06.03.2013 13:22<br />
c:\WINDOWS\Help\password.chm 21891 04.08.2004 12:00<br />
c:\WINDOWS\ServicePackFiles\i386\passwrdw.chm 21891 04.08.2004 12:00<br />
c:\WINDOWS\system32\config\systemprofile\Templates\winword.doc 4608 04.08.2004 12:00<br />
c:\WINDOWS\system32\config\systemprofile\Templates\winword2.doc 1769 04.08.2004 12:00<br />
c:\WINDOWS\system32\config\systemprofile\Templates\excel.xls 5632 04.08.2004 12:00<br />
c:\WINDOWS\system32\config\systemprofile\Templates\excel4.xls 1518 04.08.2004 12:00<br />
c:\WINDOWS\system32\ias\dnary.mdb 294912 04.08.2004 12:00<br />
c:\WINDOWS\system32\ias\ias.mdb 233472 04.08.2004 12:00<br />
klg.jpg<br />
Figure 37 – Sample file list collected by the fileList_2.jpg module<br />
hash: B3258020B9AB53A1635DA844AED955EA<br />
compile time: 2013-01-28<br />
This is a keylogger module. It copies itself into the file “C:\Documents and<br />
Settings\vendeg\Application Data\WCF Data Services\WcfAudit.exe” and also creates the shortcut<br />
“C:\Documents and Settings\vendeg\Start menu\Programs\Startup\WcfAudit.lnk” in order to start<br />
automatically at the next boot.<br />
The following figure shows the running WcfAudit.exe process:<br />
30