- Page 1 and 2: Security in Computer Networks Multi
- Page 3 and 4: Equivalence of Encryption Systems a
- Page 5 and 6: message 1 message 2 message 3 messa
- Page 7 and 8: Invisible implicit addresses using
- Page 9 and 10: Fault tolerance (and countering mod
- Page 11 and 12: time Proof of anonymity for a RING
- Page 13 and 14: S i-1 Two RINGs operating if no fau
- Page 15 and 16: ..... ... ..... ... ..... ... stati
- Page 17 and 18: S 1 S 2 S 3 S 4 S 5 0 1 0 0 0 0 1 0
- Page 19: S 1 S 1 (X+Y)-X = Y Pairwise superp
- Page 23 and 24: local superposition mod 2 L 0 1 ...
- Page 25 and 26: Proof of sender anonymity: proposit
- Page 27 and 28: Information-theoretic anonymity in
- Page 29 and 30: t-s t-s Let t-s be the first point
- Page 31 and 32: 31 Blob := committing to 0 or 1, wi
- Page 33 and 34: Blobs based on asymmetric encryptio
- Page 35 and 36: Checking the behavior of the statio
- Page 37 and 38: Fault tolerance: 2 modes of operati
- Page 39 and 40: Protection of the communication rel
- Page 41 and 42: Properties of MIXes MIXes should be
- Page 43 and 44: Maximal protection Pass through MIX
- Page 45 and 46: Indirect re-encryption scheme for r
- Page 47 and 48: d s k s 3 3 Indirect re-encryption
- Page 49 and 50: Indirect re-encryption scheme maint
- Page 51 and 52: Breaking the direct RSA-implementat
- Page 53 and 54: Fault tolerance in MIX-networks (1)
- Page 55 and 56: attacker model expense per user Com
- Page 57 and 58: OSI layers 7 application 6 presenta
- Page 59 and 60: Tolerating errors and active attack
- Page 61 and 62: Network structure • • Solution
- Page 63 and 64: Time-slice channels (1) station R M
- Page 65 and 66: Connection configuration later (1)
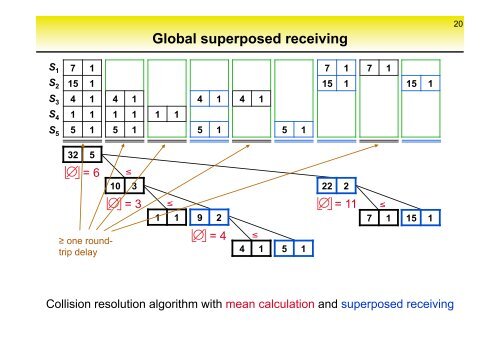
- Page 67 and 68: Query and superpose to receive the
- Page 69 and 70: Outlook (1) Using the network trans
- Page 71 and 72:
Radio networks (1) Difference to wi
- Page 73 and 74:
No movement profiles in radio netwo
- Page 75 and 76:
Security properties of digital paym
- Page 77 and 78:
Pseudonyms: Linkability in detail D
- Page 79 and 80:
79 Pseudonyms: Use across different
- Page 81 and 82:
Authenticated anonymous declaration
- Page 83 and 84:
Security for completely anonymous b
- Page 85 and 86:
Security for completely anonymous b
- Page 87 and 88:
P Z B P Z ¬ Basic scheme of a secu
- Page 89 and 90:
p B [ 3 ] p B E (Y,t) p Z B (X,t)
- Page 91 and 92:
x, (h(x)) s text with signature and
- Page 93 and 94:
p B ¬ authentication of ownership
- Page 95 and 96:
95 Secure and anonymous digit. paym
- Page 97 and 98:
legal certainty vs. liability onlin
- Page 99 and 100:
Role pseudonyms (business-relations
- Page 101 and 102:
Cryptography and the impossibility
- Page 103 and 104:
cover! emb! key! Steganography key!
- Page 105 and 106:
cover! emb! key! Steganography Steg
- Page 107:
Proposals to regulate cryptography
- Page 110 and 111:
Key Escrow encryption without perma
- Page 112 and 113:
Key Escrow encryption without perma
- Page 114 and 115:
Symmetric authentication → Encryp
- Page 116 and 117:
Key exchange without message exchan
- Page 118 and 119:
Digital Signatures Key Escrow witho
- Page 120 and 121:
Encryption# symmetric # Authen-# (M
- Page 122 and 123:
(Im-)Possibility to regulate anonym
- Page 124:
(Im-)Possibility to regulate anonym