course structure - DSpace at CUSAT
course structure - DSpace at CUSAT
course structure - DSpace at CUSAT
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
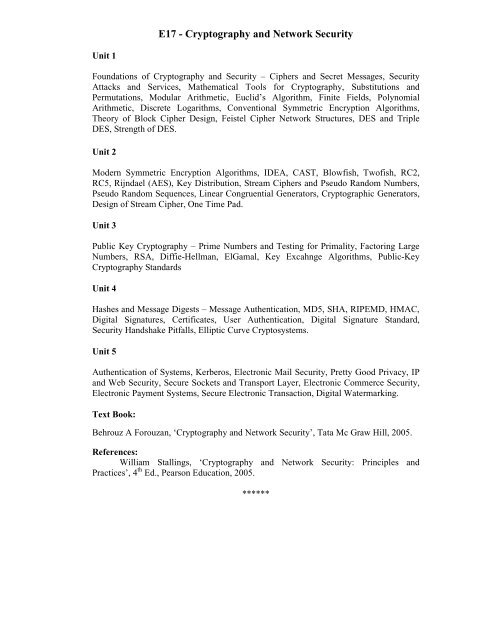
Unit 1<br />
E17 - Cryptography and Network Security<br />
Found<strong>at</strong>ions of Cryptography and Security – Ciphers and Secret Messages, Security<br />
Attacks and Services, M<strong>at</strong>hem<strong>at</strong>ical Tools for Cryptography, Substitutions and<br />
Permut<strong>at</strong>ions, Modular Arithmetic, Euclid’s Algorithm, Finite Fields, Polynomial<br />
Arithmetic, Discrete Logarithms, Conventional Symmetric Encryption Algorithms,<br />
Theory of Block Cipher Design, Feistel Cipher Network Structures, DES and Triple<br />
DES, Strength of DES.<br />
Unit 2<br />
Modern Symmetric Encryption Algorithms, IDEA, CAST, Blowfish, Twofish, RC2,<br />
RC5, Rijndael (AES), Key Distribution, Stream Ciphers and Pseudo Random Numbers,<br />
Pseudo Random Sequences, Linear Congruential Gener<strong>at</strong>ors, Cryptographic Gener<strong>at</strong>ors,<br />
Design of Stream Cipher, One Time Pad.<br />
Unit 3<br />
Public Key Cryptography – Prime Numbers and Testing for Primality, Factoring Large<br />
Numbers, RSA, Diffie-Hellman, ElGamal, Key Excahnge Algorithms, Public-Key<br />
Cryptography Standards<br />
Unit 4<br />
Hashes and Message Digests – Message Authentic<strong>at</strong>ion, MD5, SHA, RIPEMD, HMAC,<br />
Digital Sign<strong>at</strong>ures, Certific<strong>at</strong>es, User Authentic<strong>at</strong>ion, Digital Sign<strong>at</strong>ure Standard,<br />
Security Handshake Pitfalls, Elliptic Curve Cryptosystems.<br />
Unit 5<br />
Authentic<strong>at</strong>ion of Systems, Kerberos, Electronic Mail Security, Pretty Good Privacy, IP<br />
and Web Security, Secure Sockets and Transport Layer, Electronic Commerce Security,<br />
Electronic Payment Systems, Secure Electronic Transaction, Digital W<strong>at</strong>ermarking.<br />
Text Book:<br />
Behrouz A Forouzan, ‘Cryptography and Network Security’, T<strong>at</strong>a Mc Graw Hill, 2005.<br />
References:<br />
William Stallings, ‘Cryptography and Network Security: Principles and<br />
Practices’, 4 th Ed., Pearson Educ<strong>at</strong>ion, 2005.<br />
******