Exterminator- A ... with High Probability.pdf - DSpace at CUSAT ...
Exterminator- A ... with High Probability.pdf - DSpace at CUSAT ...
Exterminator- A ... with High Probability.pdf - DSpace at CUSAT ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
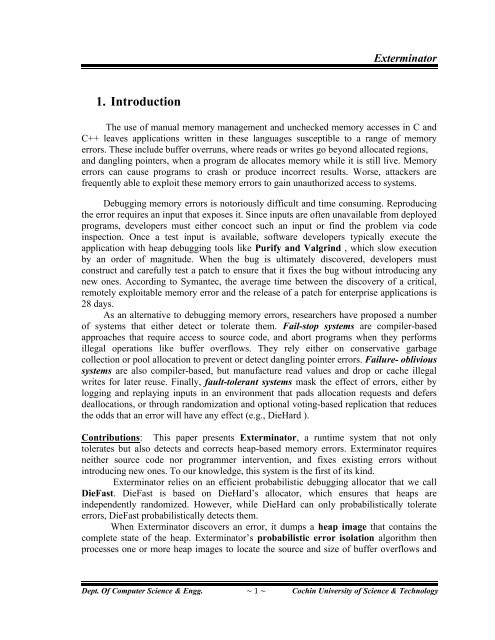
1. Introduction<br />
<strong>Extermin<strong>at</strong>or</strong><br />
The use of manual memory management and unchecked memory accesses in C and<br />
C++ leaves applic<strong>at</strong>ions written in these languages susceptible to a range of memory<br />
errors. These include buffer overruns, where reads or writes go beyond alloc<strong>at</strong>ed regions,<br />
and dangling pointers, when a program de alloc<strong>at</strong>es memory while it is still live. Memory<br />
errors can cause programs to crash or produce incorrect results. Worse, <strong>at</strong>tackers are<br />
frequently able to exploit these memory errors to gain unauthorized access to systems.<br />
Debugging memory errors is notoriously difficult and time consuming. Reproducing<br />
the error requires an input th<strong>at</strong> exposes it. Since inputs are often unavailable from deployed<br />
programs, developers must either concoct such an input or find the problem via code<br />
inspection. Once a test input is available, software developers typically execute the<br />
applic<strong>at</strong>ion <strong>with</strong> heap debugging tools like Purify and Valgrind , which slow execution<br />
by an order of magnitude. When the bug is ultim<strong>at</strong>ely discovered, developers must<br />
construct and carefully test a p<strong>at</strong>ch to ensure th<strong>at</strong> it fixes the bug <strong>with</strong>out introducing any<br />
new ones. According to Symantec, the average time between the discovery of a critical,<br />
remotely exploitable memory error and the release of a p<strong>at</strong>ch for enterprise applic<strong>at</strong>ions is<br />
28 days.<br />
As an altern<strong>at</strong>ive to debugging memory errors, researchers have proposed a number<br />
of systems th<strong>at</strong> either detect or toler<strong>at</strong>e them. Fail-stop systems are compiler-based<br />
approaches th<strong>at</strong> require access to source code, and abort programs when they performs<br />
illegal oper<strong>at</strong>ions like buffer overflows. They rely either on conserv<strong>at</strong>ive garbage<br />
collection or pool alloc<strong>at</strong>ion to prevent or detect dangling pointer errors. Failure- oblivious<br />
systems are also compiler-based, but manufacture read values and drop or cache illegal<br />
writes for l<strong>at</strong>er reuse. Finally, fault-tolerant systems mask the effect of errors, either by<br />
logging and replaying inputs in an environment th<strong>at</strong> pads alloc<strong>at</strong>ion requests and defers<br />
dealloc<strong>at</strong>ions, or through randomiz<strong>at</strong>ion and optional voting-based replic<strong>at</strong>ion th<strong>at</strong> reduces<br />
the odds th<strong>at</strong> an error will have any effect (e.g., DieHard ).<br />
Contributions: This paper presents <strong>Extermin<strong>at</strong>or</strong>, a runtime system th<strong>at</strong> not only<br />
toler<strong>at</strong>es but also detects and corrects heap-based memory errors. <strong>Extermin<strong>at</strong>or</strong> requires<br />
neither source code nor programmer intervention, and fixes existing errors <strong>with</strong>out<br />
introducing new ones. To our knowledge, this system is the first of its kind.<br />
<strong>Extermin<strong>at</strong>or</strong> relies on an efficient probabilistic debugging alloc<strong>at</strong>or th<strong>at</strong> we call<br />
DieFast. DieFast is based on DieHard’s alloc<strong>at</strong>or, which ensures th<strong>at</strong> heaps are<br />
independently randomized. However, while DieHard can only probabilistically toler<strong>at</strong>e<br />
errors, DieFast probabilistically detects them.<br />
When <strong>Extermin<strong>at</strong>or</strong> discovers an error, it dumps a heap image th<strong>at</strong> contains the<br />
complete st<strong>at</strong>e of the heap. <strong>Extermin<strong>at</strong>or</strong>’s probabilistic error isol<strong>at</strong>ion algorithm then<br />
processes one or more heap images to loc<strong>at</strong>e the source and size of buffer overflows and<br />
Dept. Of Computer Science & Engg. ~ 1 ~ Cochin University of Science & Technology