Architecture and Best Practices - Recommendations for PI ... - OSIsoft
Architecture and Best Practices - Recommendations for PI ... - OSIsoft
Architecture and Best Practices - Recommendations for PI ... - OSIsoft
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
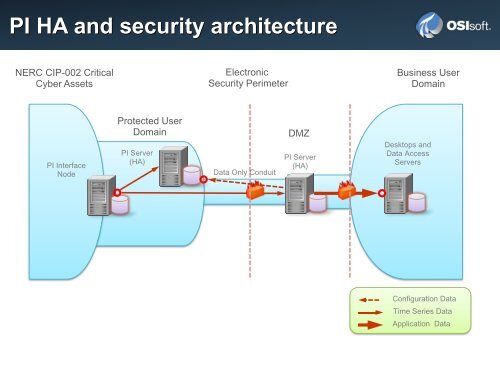
<strong>PI</strong> HA <strong>and</strong> security architecture<br />
NERC CIP-002 Critical<br />
Cyber Assets<br />
<strong>PI</strong> Interface<br />
Node<br />
Protected User<br />
Domain<br />
<strong>PI</strong> Server<br />
(HA)<br />
Electronic<br />
Security Perimeter<br />
Data Only Conduit<br />
DMZ<br />
<strong>PI</strong> Server<br />
(HA)<br />
Business User<br />
Domain<br />
Desktops <strong>and</strong><br />
Data Access<br />
Servers<br />
Configuration Data<br />
Time Series Data<br />
Application Data