SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
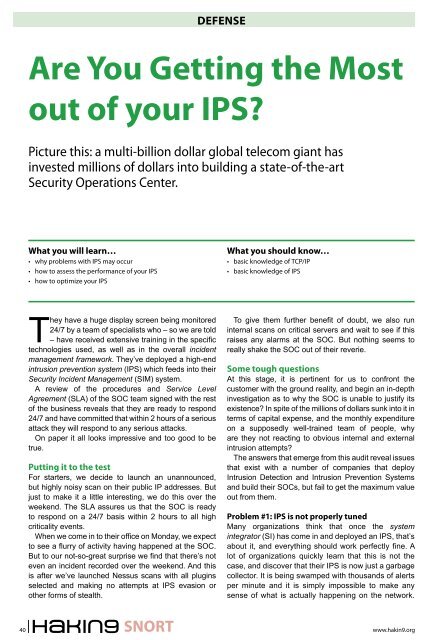
DEFENSE<br />
Are You Getting the Most<br />
out of your IPS?<br />
Picture this: a multi-billion dollar global telecom giant has<br />
invested millions of dollars into building a state-of-the-art<br />
Security Operations Center.<br />
What you will learn…<br />
• why problems with IPS may occur<br />
• how to assess the performance of your IPS<br />
• how to optimize your IPS<br />
What you should know…<br />
• basic knowledge of TCP/IP<br />
• basic knowledge of IPS<br />
They have a huge display screen being monitored<br />
24/7 by a team of specialists who – so we are told<br />
– have received extensive training in the specific<br />
technologies used, as well as in the overall incident<br />
management framework. They’ve deployed a high-end<br />
intrusion prevention system (IPS) which feeds into their<br />
Security Incident Management (SIM) system.<br />
A review of the procedures and Service Level<br />
Agreement (SLA) of the SOC team signed with the rest<br />
of the business reveals that they are ready to respond<br />
24/7 and have committed that within 2 hours of a serious<br />
attack they will respond to any serious attacks.<br />
On paper it all looks impressive and too good to be<br />
true.<br />
Putting it to the test<br />
For starters, we decide to launch an unannounced,<br />
but highly noisy scan on their public IP addresses. But<br />
just to make it a little interesting, we do this over the<br />
weekend. The SLA assures us that the SOC is ready<br />
to respond on a 24/7 basis within 2 hours to all high<br />
criticality events.<br />
When we come in to their office on Monday, we expect<br />
to see a flurry of activity having happened at the SOC.<br />
But to our not-so-great surprise we find that there’s not<br />
even an incident recorded over the weekend. And this<br />
is after we’ve launched Nessus scans with all plugins<br />
selected and making no attempts at IPS evasion or<br />
other forms of stealth.<br />
To give them further benefit of doubt, we also run<br />
internal scans on critical servers and wait to see if this<br />
raises any alarms at the SOC. But nothing seems to<br />
really shake the SOC out of their reverie.<br />
Some tough questions<br />
At this stage, it is pertinent for us to confront the<br />
customer with the ground reality, and begin an in-depth<br />
investigation as to why the SOC is unable to justify its<br />
existence? In spite of the millions of dollars sunk into it in<br />
terms of capital expense, and the monthly expenditure<br />
on a supposedly well-trained team of people, why<br />
are they not reacting to obvious internal and external<br />
intrusion attempts?<br />
The answers that emerge from this audit reveal issues<br />
that exist with a number of companies that deploy<br />
Intrusion Detection and Intrusion Prevention Systems<br />
and build their SOCs, but fail to get the maximum value<br />
out from them.<br />
Problem #1: IPS is not properly tuned<br />
Many organizations think that once the system<br />
integrator (SI) has come in and deployed an IPS, that’s<br />
about it, and everything should work perfectly fine. A<br />
lot of organizations quickly learn that this is not the<br />
case, and discover that their IPS is now just a garbage<br />
collector. It is being swamped with thousands of alerts<br />
per minute and it is simply impossible to make any<br />
sense of what is actually happening on the network.<br />
40<br />
<strong>SNORT</strong><br />
www.hakin9.org