SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
SNORT Exposed Hakin9 StarterKit 01/2010 - Computer Science
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
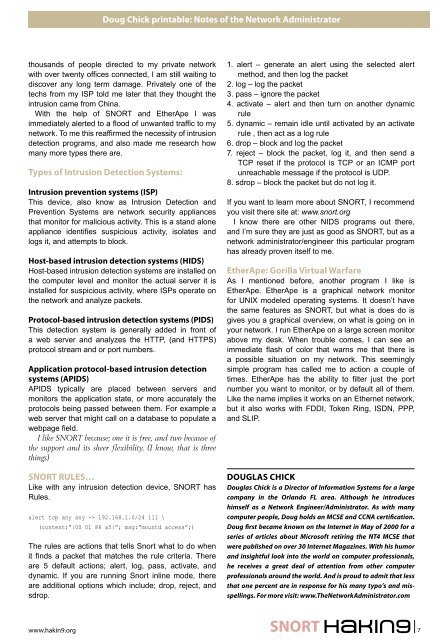
Doug Chick printable: Notes of the Network Administrator<br />
thousands of people directed to my private network<br />
with over twenty offices connected, I am still waiting to<br />
discover any long term damage. Privately one of the<br />
techs from my ISP told me later that they thought the<br />
intrusion came from China.<br />
With the help of <strong>SNORT</strong> and EtherApe I was<br />
immediately alerted to a flood of unwanted traffic to my<br />
network. To me this reaffirmed the necessity of intrusion<br />
detection programs, and also made me research how<br />
many more types there are.<br />
Types of Intrusion Detection Systems:<br />
Intrusion prevention systems (ISP)<br />
This device, also know as Intrusion Detection and<br />
Prevention Systems are network security appliances<br />
that monitor for malicious activity. This is a stand alone<br />
appliance identifies suspicious activity, isolates and<br />
logs it, and attempts to block.<br />
Host-based intrusion detection systems (HIDS)<br />
Host-based intrusion detection systems are installed on<br />
the computer level and monitor the actual server it is<br />
installed for suspicious activity, where ISPs operate on<br />
the network and analyze packets.<br />
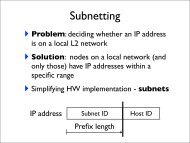
Protocol-based intrusion detection systems (PIDS)<br />
This detection system is generally added in front of<br />
a web server and analyzes the HTTP, (and HTTPS)<br />
protocol stream and or port numbers.<br />
Application protocol-based intrusion detection<br />
systems (APIDS)<br />
APIDS typically are placed between servers and<br />
monitors the application state, or more accurately the<br />
protocols being passed between them. For example a<br />
web server that might call on a database to populate a<br />
webpage field.<br />
I like <strong>SNORT</strong> because; one it is free, and two because of<br />
the support and its sheer flexibility. (I know, that is three<br />
things)<br />
<strong>SNORT</strong> RULES…<br />
Like with any intrusion detection device, <strong>SNORT</strong> has<br />
Rules.<br />
alert tcp any any -> 192.168.1.0/24 111 \<br />
(content:”|00 <strong>01</strong> 86 a5|”; msg:”mountd access”;)<br />
The rules are actions that tells Snort what to do when<br />
it finds a packet that matches the rule criteria. There<br />
are 5 default actions; alert, log, pass, activate, and<br />
dynamic. If you are running Snort inline mode, there<br />
are additional options which include; drop, reject, and<br />
sdrop.<br />
1. alert – generate an alert using the selected alert<br />
method, and then log the packet<br />
2. log – log the packet<br />
3. pass – ignore the packet<br />
4. activate – alert and then turn on another dynamic<br />
rule<br />
5. dynamic – remain idle until activated by an activate<br />
rule , then act as a log rule<br />
6. drop – block and log the packet<br />
7. reject – block the packet, log it, and then send a<br />
TCP reset if the protocol is TCP or an ICMP port<br />
unreachable message if the protocol is UDP.<br />
8. sdrop – block the packet but do not log it.<br />
If you want to learn more about <strong>SNORT</strong>, I recommend<br />
you visit there site at: www.snort.org<br />
I know there are other NIDS programs out there,<br />
and I’m sure they are just as good as <strong>SNORT</strong>, but as a<br />
network administrator/engineer this particular program<br />
has already proven itself to me.<br />
EtherApe: Gorilla Virtual Warfare<br />
As I mentioned before, another program I like is<br />
EtherApe. EtherApe is a graphical network monitor<br />
for UNIX modeled operating systems. It doesn’t have<br />
the same features as <strong>SNORT</strong>, but what is does do is<br />
gives you a graphical overview, on what is going on in<br />
your network. I run EtherApe on a large screen monitor<br />
above my desk. When trouble comes, I can see an<br />
immediate flash of color that warns me that there is<br />
a possible situation on my network. This seemingly<br />
simple program has called me to action a couple of<br />
times. EtherApe has the ability to filter just the port<br />
number you want to monitor, or by default all of them.<br />
Like the name implies it works on an Ethernet network,<br />
but it also works with FDDI, Token Ring, ISDN, PPP,<br />
and SLIP.<br />
DOUGLAS CHICK<br />
Douglas Chick is a Director of Information Systems for a large<br />
company in the Orlando FL area. Although he introduces<br />
himself as a Network Engineer/Administrator. As with many<br />
computer people, Doug holds an MCSE and CCNA certication.<br />
Doug rst became known on the Internet in May of 2000 for a<br />
series of articles about Microsoft retiring the NT4 MCSE that<br />
were published on over 30 Internet Magazines. With his humor<br />
and insightful look into the world on computer professionals,<br />
he receives a great deal of attention from other computer<br />
professionals around the world. And is proud to admit that less<br />
that one percent are in response for his many typo’s and misspellings.<br />
For more visit: www.TheNetworkAdministrator.com<br />
www.hakin9.org <strong>SNORT</strong><br />
7