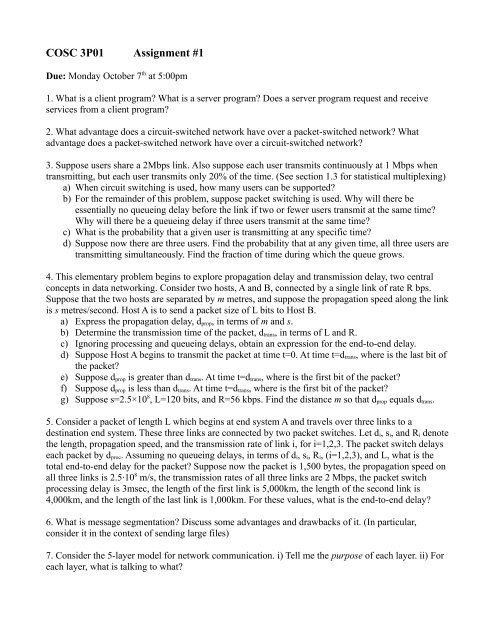
COSC 3P01 Assignment #1
COSC 3P01 Assignment #1
COSC 3P01 Assignment #1
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>COSC</strong> <strong>3P01</strong> <strong>Assignment</strong> <strong>#1</strong><br />
Due: Monday October 7 th at 5:00pm<br />
1. What is a client program? What is a server program? Does a server program request and receive<br />
services from a client program?<br />
2. What advantage does a circuit-switched network have over a packet-switched network? What<br />
advantage does a packet-switched network have over a circuit-switched network?<br />
3. Suppose users share a 2Mbps link. Also suppose each user transmits continuously at 1 Mbps when<br />
transmitting, but each user transmits only 20% of the time. (See section 1.3 for statistical multiplexing)<br />
a) When circuit switching is used, how many users can be supported?<br />
b) For the remainder of this problem, suppose packet switching is used. Why will there be<br />
essentially no queueing delay before the link if two or fewer users transmit at the same time?<br />
Why will there be a queueing delay if three users transmit at the same time?<br />
c) What is the probability that a given user is transmitting at any specific time?<br />
d) Suppose now there are three users. Find the probability that at any given time, all three users are<br />
transmitting simultaneously. Find the fraction of time during which the queue grows.<br />
4. This elementary problem begins to explore propagation delay and transmission delay, two central<br />
concepts in data networking. Consider two hosts, A and B, connected by a single link of rate R bps.<br />
Suppose that the two hosts are separated by m metres, and suppose the propagation speed along the link<br />
is s metres/second. Host A is to send a packet size of L bits to Host B.<br />
a) Express the propagation delay, d prop , in terms of m and s.<br />
b) Determine the transmission time of the packet, d trans , in terms of L and R.<br />
c) Ignoring processing and queueing delays, obtain an expression for the end-to-end delay.<br />
d) Suppose Host A begins to transmit the packet at time t=0. At time t=d trans , where is the last bit of<br />
the packet?<br />
e) Suppose d prop is greater than d trans . At time t=d trans , where is the first bit of the packet?<br />
f) Suppose d prop is less than d trans . At time t=d trans , where is the first bit of the packet?<br />
g) Suppose s=2.5×10 8 , L=120 bits, and R=56 kbps. Find the distance m so that d prop equals d trans .<br />
5. Consider a packet of length L which begins at end system A and travels over three links to a<br />
destination end system. These three links are connected by two packet switches. Let d i , s i , and R i denote<br />
the length, propagation speed, and the transmission rate of link i, for i=1,2,3. The packet switch delays<br />
each packet by d proc . Assuming no queueing delays, in terms of d i , s i , R i , (i=1,2,3), and L, what is the<br />
total end-to-end delay for the packet? Suppose now the packet is 1,500 bytes, the propagation speed on<br />
all three links is 2.5·10 8 m/s, the transmission rates of all three links are 2 Mbps, the packet switch<br />
processing delay is 3msec, the length of the first link is 5,000km, the length of the second link is<br />
4,000km, and the length of the last link is 1,000km. For these values, what is the end-to-end delay?<br />
6. What is message segmentation? Discuss some advantages and drawbacks of it. (In particular,<br />
consider it in the context of sending large files)<br />
7. Consider the 5-layer model for network communication. i) Tell me the purpose of each layer. ii) For<br />
each layer, what is talking to what?
8. (Warning: Very open-ended question! Only worry about being detailed and providing useful<br />
information; not psychically knowing what I'm expecting!) Though professionals in the field will need<br />
to know of numerous security concerns when it comes to networking and IT, everyone has at least<br />
some responsibility to keep their communications and data safe. Tell me about three (separate!)<br />
network/internet security concerns that a regular person should know about and be responsible for<br />
minding: i) What it is, ii) Why it matters, iii) What they should know to do about it. (Note: I said<br />
'regular', meaning layman. The average person probably doesn't have to worry about ARP poisoning,<br />
etc.)<br />
9. Using telnet or nc, download a form from the web. Send a completed form back to the server, and<br />
retrieve the result.<br />
You can PuTTY/SSH into sandcastle to do this if you like.<br />
You'll probably use port 80.<br />
You can choose whatever form you like. You can even make your own if you want.<br />
For submission, show the raw data you receive and send (including header information), and also save<br />
the received payloads as html files so you can load them into a browser and print that out as well.<br />
If the server sent an instruction to set a cookie in the raw data, highlight or underline that part.<br />
Note that there is no mention of bothering with images. If the form you chose includes images, you're<br />
more than welcome to leave them as dead-links.<br />
10. Using telnet or nc, send me an email. Send it from sandcastle's SMTP server, to my sandcastle<br />
account (efoxwell@sandcastle.cosc.brocku.ca). Include a (small!) attachment (an image).<br />
Make sure the attachment is relatively small (
• It doesn't matter if you actually save the contents of FOOTER.html to a file, or simply<br />
download to display on the console<br />
• Save and print the results of both channels (the control channel as one printout, and the data<br />
channels as another)<br />
Some questions are taken from the course textbook.<br />
Submission Guidelines:<br />
For 'write-y' questions, please ensure that all of your answers are entirely legible. Typing it out is<br />
strongly suggested. Showing your work (for calculations) is also strongly advisable. For those<br />
involving the manual use of application layer protocols, make sure you err on the side of including too<br />
much, rather than not enough. Staple your answers together, place them in an envelope if you so<br />
choose, and then attach a proper departmental coverpage with your student number and barcode on it.<br />
Electronic submission is not required for this assignment. However, if you do happen to do everything<br />
electronically, it's permitted (if you feel safer having a version submitted that can't get lost).