Risk Management Process - September 11 Digital Archive
Risk Management Process - September 11 Digital Archive
Risk Management Process - September 11 Digital Archive
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
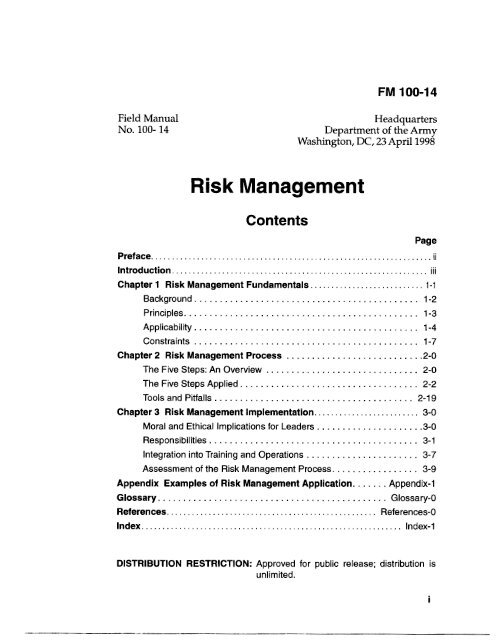
FM 100-14<br />
Field Manual<br />
NO . 100- 14<br />
Headquarters<br />
Department of the Amy<br />
Washington. DC. 23 April 1998<br />
<strong>Risk</strong> <strong>Management</strong><br />
Contents<br />
Page<br />
Preface ................................................................... ii<br />
Introduction ............................................................. ...<br />
III<br />
Chapter 1 <strong>Risk</strong> <strong>Management</strong> Fundamentals ........................... 1-1<br />
Background ............................................ 1-2<br />
Principles .............................................. 1-3<br />
Applicability ............................................ 1-4<br />
Constraints ............................................ 1-7<br />
Chapter 2 <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> ........................... 2-0<br />
The Five Steps: An Overview .............................. 2-0<br />
The Five Steps Applied ................................... 2-2<br />
Tools and Pitfalls ....................................... 2-19<br />
Chapter 3 <strong>Risk</strong> <strong>Management</strong> Implementation ......................... 3-0<br />
Moral and Ethical Implications for Leaders ..................... 3-0<br />
Responsibilities ......................................... 3-1<br />
Integration into Training and Operations ...................... 3-7<br />
Assessment of the <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> ................. 3-9<br />
Appendix Examples of <strong>Risk</strong> <strong>Management</strong> Application ....... Appendix-1<br />
Glossary ............................................. Glossary-0<br />
References .................................................. References-0<br />
Index .............................................................. Index- 1<br />
DISTRIBUTION RESTRICTION: Approved for public release; distribution is<br />
unlimited .<br />
i
Preface<br />
FM 100-14 applies across the wide range of Army operations. It<br />
explains the principles, procedures, and responsibilities to<br />
successfully apply the risk managemenf process to conserve combat<br />
power and resources. The manual applies to both Army and civilian<br />
personnel during all Army activities, including joint, multinational,<br />
and interagency environments.<br />
The manual is intended to help commanders,' their staffs,<br />
leaders,2 and managers develop a framework to make risk<br />
management a routine part of planning, preparing, and executing<br />
operational missions and everyday tasks. This framework will allow<br />
soldiers to operate with maximum initiative, flexibility, and<br />
adaptability. Although the manual's prime focus is the operational<br />
Army, the principles of risk management apply to all Army activities.<br />
Army operations-especially combat operations-are demanding<br />
and complex. They are inherently dangerous, including tough,<br />
realistic training. Managing risks related to such operations requires<br />
educated judgment and professional competence. The risk<br />
management process allows individuals to make informed, conscious<br />
decisions to accept risks at acceptable levels.<br />
This manual is not a substitute for thought. Simply reading it will<br />
not make one adept in building protection around a mi~sion.~ Soldiers<br />
should compare the doctrine herein against their own experience and<br />
think about why, when, and how it applies to their situation and area<br />
of responsibility. If the doctrine herein is to be useful, it must become<br />
second nature.<br />
The proponent of this manual is HQ TRADOC. Send comments<br />
and recommendations on DA Form 2028 directly to Commander, US<br />
Army Training and Doctrine Command, ATTN: ATBO-SO, Fort<br />
Monroe, VA 23651-5000.<br />
Unless this publication states otherwise, masculine nouns and<br />
pronouns do not refer exclusively to men.<br />
The term commander as used herein refers to personnel in a command<br />
position.<br />
The term leader as used herein refers to commanders, personnel in the<br />
chain of command (team, squad, section, platoon leader), and staff members<br />
having personnel supervisory responsibility.<br />
The term mission as used herein includes mission, operation, or task.<br />
ii
Introduction<br />
<strong>Risk</strong> management is not an add-on feature to the decisionmaking<br />
process but rather a fully integrated element of<br />
planning and executing operations.. . <strong>Risk</strong> management helps<br />
us preserve combat power and retain theflexibility for bold and<br />
decisive action. Proper risk management is a combat multiplier<br />
that we can ill aford to squander.<br />
General Dennis J. Reimer<br />
Chief of Staff, Army<br />
27 July 1995<br />
The Army’s fundamental purpose is to fight and win the nation’s<br />
wars. For this purpose, the country gives the Army critical resources,<br />
including those most valuable-its sons and daughters. The Army<br />
uses its resources to generate overwhelming combat power to fight<br />
and win quickly, decisively, and with minimal losses. The Army’s<br />
inherent responsibility to the nation is to protect and preserve its<br />
resources-a responsibility that resides at all levels. <strong>Risk</strong> management<br />
is an effective process for preserving resources. It is not an event. It<br />
is both an art and a science. Soldiers use it to identify tactical and<br />
accident risks, which they reduce by avoiding, controlling, or<br />
eliminating hazards.<br />
The Army introduced the risk management process into training,<br />
the operational environments, and materiel acquisition in the late<br />
1980s. <strong>Risk</strong> management was originally perceived as solely a safety<br />
officer function. However, by the early 1990s, the Army established a<br />
goal to integrate risk management into all Army processes and<br />
activities and into every individual’s behavior, both on and off duty.<br />
Since the process was introduced, the personal involvement of<br />
commanders in preventing accidents-and their aggressive use of the<br />
process-have become driving factors in the steady downward trend<br />
in Army accidental losses.<br />
Leaders must understand the importance of the process in<br />
conserving combat power and resources. <strong>Risk</strong> management, like<br />
reconnaissance and security, is an ongoing process that continues from<br />
mission to mission. Within the mission, leaders must know when the<br />
process begins and who has responsibility. It must be integral to the<br />
military decision. The process is an important means to enhance<br />
situational awareness.<br />
iii
<strong>Risk</strong> <strong>Management</strong><br />
<strong>Risk</strong> decisions are commanders’ business. Such decisions are<br />
normally based on the next higher commander’s guidance on how<br />
much risk he is willing to accept and delegate for the mission. <strong>Risk</strong><br />
decisions should be made at the lowest possible level, except in<br />
extreme circumstances. Training operations, including those at<br />
combat training centers (CTCs), may be of such intensity that risk<br />
decision are retained at a higher level.<br />
Both leaders and staffs manage risk. Staff members continuously<br />
look for hazards associated with their areas of expertise. They then<br />
recommend controls to reduce risks. Hazards and the resulting risks<br />
may vary as circumstances change and experience is gained. Leaders<br />
and individual soldiers become the assessors for ever-changing<br />
hazards such as those associated with environment (weather;<br />
visibility; contaminated air, water, and soil), equipment readiness,<br />
individual and unit experience, and fatigue. Leaders should advise<br />
the chain of command on risks and risk reduction measures.<br />
iv
Chapter 1<br />
<strong>Risk</strong> <strong>Management</strong> Fundamentals<br />
Sizing up opponents to determine victory, assessing dangers<br />
and distances is the proper course of action for milita y leaders.<br />
Sun Tzu, The Art of War, “Terrain”<br />
<strong>Risk</strong> management is the process of identifying, assessing,<br />
and controlling risks arising from operational factors<br />
and making decisions that balance risk costs with<br />
mission benefits. Leaders and soldiers at all levels use<br />
risk management. It applies to all missions and<br />
environments across the wide range of Army<br />
operations. <strong>Risk</strong> management is fundamental in<br />
developing confident and competent leaders and units.<br />
Proficiency in applying risk management is critical to<br />
conserving combat power and resources. Commanders<br />
must firmly ground current and future leaders in the<br />
critical skills of the five-step risk management process.<br />
<strong>Risk</strong> is characterized by both the probability and severity<br />
of a potential loss that may result from hazards due to the<br />
presence of an enemy, an adversary, or some other<br />
hazardous condition. Perception of risk varies from<br />
person to person. What is risky or dangerous to one<br />
person may not be to another. Perception influences<br />
leaders’ decisions. A publicized event such as a training<br />
accident or a relatively minor incident may increase the<br />
public’s perception of risk for that particular event and<br />
time-sometimes to the point of making such risks<br />
unacceptable. Failure to effectively manage the risk<br />
may make an operation too costly-politically,<br />
economically, and in terms of combat power (soldiers<br />
lives and equipment). This chapter presents the<br />
background, principles, applicability, and constraints<br />
relating to the risk management process.<br />
1-1
<strong>Risk</strong> <strong>Management</strong><br />
BACKGROUND<br />
Throughout the history of armed conflict, government and<br />
military leaders have tried to reckon with the effect of casualties on<br />
policy, strategy, and mission accomplishment. Government and<br />
military leaders consider battle losses from different perspectives.<br />
However, both must balance the following against the value of<br />
national objectives:<br />
Effects of casualties.<br />
Impact on civilians.<br />
Damage to the environment.<br />
Loss of equipment.<br />
Level of public reaction.<br />
War is inherently complex, dynamic, and fluid. It is characterized<br />
by uncertainty, ambiguity, and friction. Uncertainty results from<br />
unknowns or lack of information. Ambiguity is the blurring or fog that<br />
makes it difficult to distinguish fact from impression about a situation<br />
and the enemy. Friction results from change, operational hazards,<br />
fatigue, and fears brought on by danger. These characteristics cloud the<br />
operating environment; they create risks that affect an army’s ability to<br />
fight and win. In uncertainty, ambiguity, and friction, both danger and<br />
opportunity exist. Hence, a leader’s ability to adapt and take risks are<br />
key traits. Chapter 2 of FM 100-5 provides information on the<br />
challenging circumstances of military operations during conflict.<br />
Historically the Army has had more accidental losses, including<br />
fratricide (friendly fire), than losses from enemy action. See Figure 1-1.<br />
These accidental losses are the same types experienced in peacetime<br />
World War II<br />
1942-1 945<br />
Korea<br />
1950-1 953<br />
Vietnam<br />
1965-1 972<br />
Desert Shield/<br />
Storm’<br />
1 990-1 991<br />
Accidents<br />
Friendly Fire<br />
56%<br />
1 Yo<br />
44%<br />
1 Yo<br />
54%<br />
1 Yo<br />
75%<br />
5%<br />
Enemv Action 43% 55% 45% 20%<br />
I<br />
’These numbers include the relatively long buildup time and short<br />
period of combat action<br />
Figure 1-1. Battle and Nonbattle Casualties<br />
I<br />
1-2
FM 100-14<br />
during training exercises. These losses are not caused by the enemy or<br />
an adversary. Factors include-<br />
An ever-changing operational environment.<br />
Effects of a fast-paced, high-operational tempo (OPTEMPO) and<br />
a high-personnel tempo (PERSTEMPO) on unit and human<br />
performance. Examples include leader or soldier error or failure<br />
to train or perform to standards.<br />
Equipment failure, support failure, and the effects of the<br />
physical environment.<br />
PRINCIPLES<br />
The basic principles that provide a framework for implementing<br />
the risk management process are-<br />
* Integrating risk management into mission planning, preparation, and<br />
execution. Leaders and staffs continuously identify hazards and<br />
assess both accident and tactical risks. They then develop and<br />
coordinate control measures. They determine the level of residual<br />
risk for accident hazards in order to evaluate courses of action<br />
(COAs). They integrate control measures into staff estimates,<br />
operation plans (OPLANs), operation orders (OPORDs), and<br />
missions. Commanders assess the areas in which they might take<br />
tactical risks. They approve control measures that will reduce<br />
risks. Leaders ensure that all soldiers understand and properly<br />
execute risk controls. They continuously assess variable hazards<br />
and implement risk controls.<br />
Making risk decisions at the appropriate level in the chain of command.<br />
The commander should address risk guidance in his<br />
commander’s guidance. He bases his risk guidance on<br />
established Army and other appropriate policies and on his<br />
higher commander’s direction. He then gives guidance on how<br />
much risk he is willing to accept and delegate. Subordinates seek<br />
the higher commander’s approval to accept risks that might<br />
imperil the next higher commander’s intent.<br />
Accepting no unnecessa y risk. Commanders compare and balance<br />
risks against mission expectations and accept risks only if the<br />
benefits outweigh the potential costs or losses. Commanders<br />
alone decide whether to accept the level of residual risk to<br />
accomplish the mission.<br />
1-3
<strong>Risk</strong> <strong>Management</strong><br />
APPLICABILITY<br />
<strong>Risk</strong> management applies to all situations and environments<br />
across the wide range of Army operations, activities, and<br />
processes. <strong>Risk</strong> management is useful in developing, fielding, and<br />
employing the total Army force. Figure 1-2 summarizes the key<br />
aspects of risk management.<br />
DEVELOPMENT<br />
Development concerns include force design, manpower<br />
allocation, training and training developments, and combat and<br />
materiel developments (equipment and weapons systems) and<br />
battle laboratories.<br />
<strong>Risk</strong> management assists the commander or leader in-<br />
* Conserving lives and resources and avoiding<br />
unnecessary risk.<br />
Making an informed decision to implement a COA.<br />
Identifying feasible and effective control measures where<br />
specific standards do not exist.<br />
Providing reasonable alternatives for mission<br />
accomplishment.<br />
<strong>Risk</strong> management does not-<br />
* Inhibit the commander’s and leader’s flexibility and<br />
in it i at ive.<br />
Remove risk altogether, or support a zero defects<br />
mindset.<br />
Require a GO/NO-GO decision.<br />
Sanction or justify violating the law.<br />
Remove the necessity for standard drills, tactics,<br />
techniques, and procedures.<br />
Figure 1-2. Key Aspects of <strong>Risk</strong> <strong>Management</strong><br />
1 -4
FM 100-14<br />
Force Design<br />
Concerns include risks introduced in trade-off decisions that<br />
involve the design and equipping of-<br />
Tables of organization and equipment (TOE).<br />
Modification tables of organization and equipment (MTOE).<br />
Tables of distribution and allowances (TDA) organizations.<br />
Manpower Allocations<br />
Concerns include shortfalls in manning that put unit readiness<br />
and full use of combat system capabilities at risk.<br />
Training and Training Developments<br />
Concerns include hazardous and critical training tasks and<br />
feasible risk reduction measures that provide leaders with the<br />
flexibility to safely conduct tough, realistic training.<br />
Combat and Materiel Developments and Battle Laboratories<br />
Concerns include providing a means to assist in making informed<br />
trade-off decisions such as-<br />
Balancing equipment form, fit, and function.<br />
Balancing the durability and cost of equipment and spare parts<br />
against their reliability, availability, and maintainability<br />
requirements.<br />
Determining the environmental impact.<br />
Determining whether to accept systems with less than the full<br />
capabilities prescribed in requirement documents and<br />
experimental procedures.<br />
ARs 70-1 and 385-16 and MIL-STD-882 provide details on risk<br />
management application in the Army materiel acquisition process.<br />
FIELDING<br />
Fielding concerns include personnel assignments, sustainment<br />
and logistics, training, and base operations.<br />
Personnel Assignments<br />
Concerns include making informed decisions in assigning<br />
replacement personnel. For example, a risk is associated with<br />
assigning a multiple launch rocket system crewmember as a<br />
replacement for a tube artillery cannon crewmember.<br />
1-5
<strong>Risk</strong> <strong>Management</strong><br />
Sustainment and Logistics<br />
Concerns include enhancing one's ability to determine support<br />
requirements, the order in which they should be received, and the<br />
potential impact of logistics decisions on operations.<br />
Training<br />
Concerns include helping leaders determine the-<br />
* Balance between training realism and unnecessary risks<br />
in training.<br />
Impact of training operations on the environment.<br />
Level of proficiency and experience of soldiers and leaders.<br />
Base Operations<br />
Concerns include prioritizing the execution of base operations<br />
functions to get the most benefit from available resources. Examples<br />
include allocating resources for pollution prevention, correcting safety<br />
and health hazards, and correcting violations of environmental<br />
protection regulations. FM 20-400 provides specific guidance on<br />
environmental protection in military operations.<br />
EMPLOYMENT<br />
Employment concerns include force protection and deployment,<br />
operations, and redeployment.<br />
Force Protection<br />
Concerns include developing a plan that identifies threats and their<br />
associated hazards and balancing resource restraints against the risk.<br />
Deployment, Operations, and Redeployment<br />
Concerns include-<br />
1-6<br />
* Analyzing the factors of mission, enemy terrain, troops, and<br />
time available (METI'-T) to determine both tactical and accident<br />
risks and appropriate risk reduction measures.<br />
Determining the correct units, equipment composition, and<br />
sequence.<br />
Identifying controls essential to safety and environmental<br />
protection.
FM 100-14<br />
CONSTRAINTS<br />
<strong>Risk</strong> management does not convey authority to violate the law-ofland<br />
warfare or deliberately disobey local, state, national, or host<br />
nation laws. It does not justify ignoring regulatory restrictions and<br />
applicable standards. Neither does it justify bypassing risk controls<br />
required by law, such as life safety and fire protection codes, physical<br />
security, transport and disposal of hazardous material and waste, or<br />
storage of classified material. Commanders may not use risk<br />
management to alter or bypass legislative intent. However, when<br />
restrictions imposed by other agencies adversely affect the mission,<br />
planners may negotiate a satisfactory COA if the result conforms to<br />
the legislative intent.<br />
<strong>Risk</strong> management assists the commander in complying with<br />
regulatory and legal requirements by-<br />
* Identifying applicable legal standards that affect the mission.<br />
* Idenhfymg alternate COAs or alternate standards that meet the<br />
intent of the law.<br />
Ensuring better use of limited resources through establishing<br />
priorities to correct known hazardous conditions that will result<br />
in projects with the highest return on investment funded first.<br />
1-7
Chapter 2<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
First reckon, then risk<br />
Field Marshal Helmuth von Moltke<br />
This chapter provides the essence of the five-step risk<br />
management process. It illustrates the application of<br />
each step to military operations through the factors<br />
of METT-T.<br />
THE FIVE STEPS: AN OVERVIEW<br />
<strong>Risk</strong> management is the process of identifying and controlling<br />
hazards to conserve combat power and resources. The five steps of<br />
risk management are-<br />
Step 1. Idenhfy hazards.<br />
Step 2. Assess hazards to determine risks.<br />
Step 3. Develop controls and make risk decisions.<br />
Step 4. Implement controls.<br />
Step 5. Supervise and evaluate.<br />
This five-step process is integrated into the military decision-making<br />
process as shown in Figure 2-1.<br />
FM 100-40 provides insight into the context in which the risk<br />
management process is applied herein. Areas of particular interest in<br />
FM 100-40 include<br />
Solving tactical problems (Chapter 1).<br />
The science and art of tactics (Chapter 1).<br />
Hasty versus deliberate operations (Chapter 1).<br />
The plan-prepare-execute cycle (Chapter 1).<br />
Basic tactical control measures (Chapter 2).<br />
The factors of METT-T (Chapter 2).<br />
2-0
FM 100-14<br />
Military Decision<br />
Making <strong>Process</strong><br />
Mission Receipt<br />
Mission Analysis<br />
COA Development<br />
COA Analysis<br />
COA Comparison<br />
COA Approval<br />
Step 1<br />
Identify<br />
Hazards<br />
X<br />
X<br />
X<br />
X<br />
<strong>Risk</strong> <strong>Management</strong> Steps<br />
Step 2<br />
Assess<br />
Hazards<br />
Step 3<br />
Develop<br />
Controls<br />
Step 4<br />
Implement<br />
Controls<br />
Step 5<br />
Supervise and<br />
Evaluate<br />
and<br />
Make <strong>Risk</strong><br />
I<br />
Decision<br />
I x I<br />
Orders Production<br />
Rehearsal’<br />
X<br />
X<br />
Execution and’<br />
Assessment<br />
X<br />
-<br />
’All boxes are marked to emphasize the continued use of the risk management<br />
process throughout the mission<br />
X<br />
Figure 2-1. <strong>Risk</strong> <strong>Management</strong> Steps Correlated with<br />
Military Decision-Making Tasks<br />
<strong>Risk</strong> decisions should be based upon awareness rather than<br />
mechanical habit. Leaders should act on a keen appreciation for the<br />
essential factors that make each situation unique instead of from<br />
conditioned response. Throughout the entire operational continuum,<br />
the commander must consider US Government civilians and contract<br />
support personnel in his risk management process. Hazards can exist,<br />
regardless of enemy or adversary actions, in areas with no direct<br />
enemy contact and in areas outside the enemy’s or adversary’s<br />
2-1
<strong>Risk</strong> <strong>Management</strong><br />
influence. The two types of risk that exist across the wide range of<br />
Army operations are tactical risks and accident risks.<br />
Tactical risk is risk concerned with hazards that exist because of<br />
the presence of either the enemy or an adversary. It applies to all<br />
levels of war and across the spectrum of operations.<br />
Accident risk includes all operational risk considerations other<br />
than tactical risk. It includes risks to the friendly force. It also<br />
includes risks posed to civilians by an operation, as well as an<br />
operations impact on the environment. It can include activities<br />
associated with hazards concerning friendly personnel,<br />
civilians, equipment readiness, and environmental conditions.<br />
STEPS 1 AND 2<br />
Steps 1 and 2 together comprise the risk assessment. In Step 1,<br />
individuals identify the hazards that may be encountered in executing<br />
a mission. In Step 2, they determine the direct impact of each hazard on<br />
the operation. The risk assessment provides for enhanced situational<br />
awareness. This awareness builds confidence and allows soldiers and<br />
units to take timely efficient, and effective protective measures.<br />
STEPS 3 THROUGH 5<br />
Steps 3 through 5 are the essential follow-through actions to<br />
effectively manage risk. In these steps, leaders balance risk against<br />
costs-political, economic, environmental, and to combat powerand<br />
take appropriate actions to eliminate unnecessary risk. During<br />
execution, as well as during planning and preparation, leaders<br />
continuously assess the risk to the overall mission and to those<br />
involved in the task. Finally, leaders and individuals evaluate the<br />
effectiveness of controls and provide lessons learned so that others<br />
may benefit from the experience.<br />
THE FIVE STEPS APPLIED<br />
STEP 1. IDENTIFY HAZARDS<br />
A hazard is an actual or potential condition where the following<br />
can occur due to exposure to the hazard:<br />
Injury, illness, or death of personnel.<br />
Damage to or loss of equipment and property.<br />
Mission degradation.
FM 100-14<br />
Hazards are sources of danger or risks due to enemy or adversary<br />
presence and other conditions not due to enemy or adversary<br />
capabilities. Hazards are found in all operational environments.<br />
Combat operations, stability operations, base support operations, and<br />
training present unique hazards for units involved in these kinds of<br />
missions. Hazards are identified during the first four steps of the<br />
military decision-making process: mission receipt, mission analysis, COA<br />
development, and COA analysis.<br />
The ability of unit leaders and staffs to identify hazards is key. One<br />
reality of today's missions is that the aspect of a hazard can change<br />
rapidly. Things of little risk initially can quickly become major threats<br />
due to unforeseen natural or man-made events. Leaders should be<br />
aware of this possibility. Complacency to the fact that existing controls<br />
may not continue to control hazards in rapidly changing situations<br />
should be viewed as a hazard in itself.<br />
The factors of METT-T provide a sound framework for identifying<br />
hazards when planning, preparing, and executing operations. When<br />
applying risk management to METT-T during mission analysis,<br />
leaders and staffs should look for hazards that affect both tactical and<br />
accident risks. They must identify all hazards that may present<br />
significant risks to the mission.<br />
Mission<br />
Leaders first analyze the assigned mission. They look at the type<br />
of mission to be accomplished and consider possible subsequent<br />
missions. Certain kinds of operations are inherently more dangerous<br />
than others. For example, a deliberate frontal attack, because of the<br />
associated movement, is more likely to expose a unit to losses than<br />
would a defense from prepared positions. Identifying missions that<br />
routinely present great risk is imperative. Leaders also look for<br />
hazards associated with complexity of the plan such as-<br />
A scheme of maneuver that is difficult to understand or too<br />
complex for accurate communications down to the lowest level.<br />
The impact of operating under a fragmentary order (FRAGO).<br />
Enemy<br />
Commanders look for enemy capabilities that pose significant<br />
hazards to the operation. For example, "What can the enemy do to<br />
2-3
<strong>Risk</strong> <strong>Management</strong><br />
defeat my operation?” Common shortfalls that can create hazards<br />
during operations against an enemy include failure to-<br />
Assess potential advantages to the enemy provided by the<br />
battlefield environment.<br />
Fully assess the enemy’s capabilities.<br />
Understand enemy collection capabilities and ,friendly<br />
vulnerabilities to those capabilities.<br />
Accurately determine the enemy’s probable COAs.<br />
Plan and coordinate active ground and aerial reconnaissance<br />
activities.<br />
Disseminate intelligence about the enemy to lower levels.<br />
Identifying terrorist threats and capabilities.<br />
Intelligence plays a critical part in identifying hazards associated<br />
with tactical risk. Intelligence-preparation-of-the-battlefield (IPB) is a<br />
dynamic staff process that continually integrates new information and<br />
intelligence that ultimately becomes input to the commander’s risk<br />
assessment process. Intelligence assists in identifying hazards during<br />
operations by-<br />
* Identifying the opportunities and constraints the battlefield<br />
environment offers to threat and friendly forces.<br />
Thoroughly portraying threat capabilities and vulnerabilities.<br />
Collecting information on populations, governments, and<br />
infrastructures.<br />
FMs 34-130 and 34-60, respectively, provide detailed information on<br />
IPB and on counterintelligence operations and multidiscipline<br />
counterintelligence analysis.<br />
Terrain and Weather<br />
In addition to those due to the enemy or adversaries, the most<br />
obvious hazards to military operations are due to terrain and weather.<br />
Terrain and weather affect the type of hazard encountered. When the<br />
enemy uses terrain to his advantage, the risk is clearly tactical. The<br />
aspects of terrain and weather may create situations where accident<br />
risks predominate. When looking at this from a purely mission<br />
perspective, familiarity of the unit with the terrain and its associated<br />
environment must be paramount. Basic issues include-<br />
* How long the unit has operated in the environment and climate.<br />
Whether the terrain has been crossed before.<br />
2-4
FM 100-14<br />
Terrain. The five main military aspects of terrain-ubservation and<br />
fields offire, cover and concealment, obstacles, key terrain and decisive terrain,<br />
and avenues of approach (OCOKA)-can be used to identify and assess<br />
hazards impacting on friendly forces. Chapter 2 of FM 100-40 has<br />
details on OCOKA. The terrain analysis includes both map and on-theground<br />
reconnaissance to identify how well unit capabilities and<br />
mission demands can be accommodated by the terrain.<br />
Observation and fields offire. Hazards associated with this usually<br />
involve when the enemy will be able to engage a friendly unit and<br />
when friendly unit weapons capabilities allow it to effectively<br />
engage the enemy.<br />
Cover and concealment. Hazards associated with cover and<br />
concealment are created by the enemy’s ability to place direct or<br />
indirect fire on friendly forces.<br />
* Obstacles. Hazards associated with obstacles may be accident or<br />
tactical. They may be due to natural conditions such as rivers or<br />
swamps or man-made such as minefields or built-up areas.<br />
Key terrain and decisive terrain. Hazards are a marked advantage<br />
terrain provides to the enemy if he controls such terrain or<br />
denies its use to friendly forces.<br />
Avenues of approach. Hazards associated with avenues of<br />
approach can affect both tactical and accident risks. Such<br />
hazards include conditions where an avenue of approach<br />
impedes deployment of friendly combat power or where it<br />
supports deployment of enemy combat power.<br />
Weather . Weather works hand-in-hand with terrain to create<br />
hazards. To identify weather hazards, leaders and soldiers must<br />
assess the impact on operating systems. Mistakes include not<br />
considering the-<br />
* Adverse effects of heat and cold hazards on the performance<br />
of soldiers.<br />
Effects of climate and weather on maintenance of vehicles and<br />
equipment before beginning an operation.<br />
Hazardous effects of weather on the five military aspects<br />
of terrain.<br />
2-5
<strong>Risk</strong> <strong>Management</strong><br />
Troops<br />
Leaders analyze the capabilities of available friendly troops.<br />
Associated hazards impact both the soldier and unit. Key<br />
considerations are level of training, manning levels, the condition and<br />
maintenance of vehicles and equipment, morale, availability of<br />
supplies and services, and the physical and emotional health of<br />
soldiers. Leaders and soldiers must be vigilant to the fact that hazards<br />
in these areas can adversely affect a mission, even when all tactical<br />
considerations point to success. Mission failure can be caused by-<br />
* Hazards to the physical and emotional health of soldiers. Inadequate<br />
sanitation facilities, water purification capabilities, medical<br />
attention, and evacuation capabilities are key hazards that can<br />
arise from incomplete logistical planning. Care of troops requires<br />
long-range projections of all classes of supply, with close<br />
monitoring of mission changes that could impact availability or<br />
depletion of supplies. When beginning an operation immediately<br />
upon arriving in theater, hazards include not implementing<br />
measures to help soldiers overcome fatigue or acclimatize them to<br />
the geographical area and associated climate.<br />
Hazards to task organization or units participating in an operation.<br />
Hazards include how long units have worked together under a<br />
particular command relationship. During stability operations,<br />
task organizations may change often. Hazards include poor<br />
communication, unfamiliarity with higher headquarters SOPS,<br />
and insufficient combat power to accomplish the mission.<br />
Hazards associated with long-term missions. Long-term missions<br />
include nation building, peacekeeping, or insurgency/<br />
counterinsurgency operations. Hazards associated with these<br />
missions include the turmoil of personnel turnover, lack of<br />
continuity of leadership, inexperience, and lack of knowledge of<br />
the situation and the unit’s operating procedures. An especially<br />
insidious hazard is critical-skills atrophy that results from not<br />
performing METL-related missions.<br />
Time Available<br />
The hazard is insufficient time to plan, prepare, and execute<br />
operations. Planning time is always at a premium. Leaders routinely<br />
apply the one-third/two-thirds rule to ensure their subordinate units<br />
are given maximum time to plan. Failure to accomplish a mission on<br />
2-6
FM 100-14<br />
time can result in shortages of time for subordinate and adjacent units<br />
to accomplish their mission.<br />
Civilians<br />
The commander’s legal responsibility is to consider hazards to,<br />
and safeguarding of, civilians in his area of operations. Civilians<br />
include nongovernmental organizations (NGOs), private voluntary<br />
organizations (PVOs), US Government civilians, foreign national<br />
civilians, the media, and dislocated civilians put at risk by military<br />
operations. The commander must consider hazards that can occur<br />
across the range of operations, such as-<br />
* In a wartime environment. The commander must consider the<br />
hazard of collateral damage which may result in creating<br />
new adversaries.<br />
In a peacetime environment. The commander must consider the<br />
political attitudes and previous actions of civilians in identifying<br />
hazards to friendly forces and the populace itself.<br />
Adversaries are hostile elements other than the enemy that may be<br />
encountered during any operation. They present additional hazards.<br />
They may be organized opposition or individuals that challenge<br />
authority. They may include such diverse elements as rioters,<br />
criminals, rogues, or gangs that might want to harass a peace<br />
enforcement mission.<br />
STEP 2. ASSESS HAZARDS<br />
Step 2 completes the risk assessment. <strong>Risk</strong> is the chance of hazard<br />
or bad consequences. This step examines each hazard in terms of<br />
probability and severity to determine the risk level of one or more<br />
hazardous incidents that can result from exposure to the hazard. This<br />
step is conducted during three steps of the military decision-making<br />
process-mission analysis, COA devebpment, and COA analysis. This<br />
step is also conducted after controls are developed.<br />
The incident must be credible in that it must have a reasonable<br />
expectation of happening. The end result is an estimate of risk from<br />
each hazard and an estimate of the overall risk to the mission caused<br />
by hazards that cannot be eliminated. Leaders must also assess the<br />
risk to civilians posed by the operation. They may need to assess the<br />
operations’ impact on the environment. This step is conducted in<br />
three substeps.<br />
2-7
<strong>Risk</strong> <strong>Management</strong><br />
Substep A<br />
Leaders and staffs assess each hazard in relation to the probability<br />
of a hazardous incident. The probability levels estimated for each<br />
hazard may be based on the mission, COAs being developed and<br />
analyzed, or frequency of a similar event. Figure 2-2 provides a<br />
summary of the five degrees of probability. The letters in parentheses<br />
following each degree (A through E) provide a symbol for depicting<br />
probability. For example, the letter A representsfrepent probability.<br />
Single item<br />
Fleet or inventory of<br />
items<br />
Individual soldier<br />
All soldiers exposed<br />
Occurs very often in service life. Expected to occur<br />
several times over duration of a specific mission or<br />
operation. Always occurs.<br />
Occurs continuously during a specific mission or<br />
operation, or over a service life.<br />
Occurs very often in career. Expected to occur several<br />
times during mission or operation. Always occurs.<br />
Occurs continuously during a specific mission or<br />
operation.<br />
Single item<br />
Fleet or inventory of<br />
items<br />
Individual soldier<br />
All soldiers exposed<br />
Occurs several times in service life. Expected to occur<br />
during a specific mission or operation.<br />
Occurs at a high rate, but experienced intermittently<br />
(regular intervals, generally often,).<br />
Occurs several times in career. Expected to occur during<br />
a specific mission or operation.<br />
Occurs at a high rate, but experienced intermittently.<br />
Single item<br />
Fleet or inventory of<br />
items<br />
Individual soldier<br />
All soldiers exposed<br />
Occurs some time in service life. May occur about as<br />
often as not during a specific mission or operation.<br />
Occurs several times in service life.<br />
Occurs some time in career. May occur during a specific<br />
mission or operation, but not often.<br />
I Occurs sporadically (irregularly, sparsely, or sometimes).<br />
Figure 2-2. Hazard Probability<br />
2-8
FM 100-14<br />
Single item<br />
Fleet or inventory of<br />
items<br />
Individual soldier<br />
All soldiers exposed<br />
Occurs in service life, but only remotely possible. Not<br />
expected to occur during a specific mission or operation.<br />
Occurs as isolated incidents. Possible to occur some time<br />
in service life, but rarely. Usually does not occur.<br />
Occurs as isolated incident during a career. Remotely<br />
possible, but not expected to occur during a specific<br />
mission or operation.<br />
Occurs rarely within exposed population as isolated<br />
incidents.<br />
Single item<br />
Fleet or inventory of<br />
items<br />
Individual soldier<br />
All soldiers exposed<br />
Occurrence not impossible, but can assume will almost<br />
never occur in service life. Can assume will not occur<br />
during a specific mission or operation.<br />
Occurs very rarely (almost never or improbable). Incidents<br />
may occur over service life.<br />
Occurrence not impossible, but may assume will not occur<br />
in career or during a specific mission or operation.<br />
Occurs very rarely, but not impossible.<br />
Substep B<br />
Substep B addresses the severity of each hazard. It is expressed in<br />
terms of-<br />
Degree of injury or illness.<br />
Loss of or damage to equipment or property.<br />
Environment a1 damage.<br />
Other mission-impairing factors such as lost combat power.<br />
The degree of severity estimated for each hazard may be based on<br />
knowledge of the results of similar past events. Figure 2-3 provides a<br />
summary of the four degrees of hazard severity. The Roman numerals<br />
in parentheses following each degree (I through IV) provide a<br />
convenient symbol for depicting severity. For example, I represents<br />
the catastrophic degree of severity.<br />
2-9
<strong>Risk</strong> <strong>Management</strong><br />
CATASTROPHIC (I)<br />
CRITICAL (<strong>11</strong>)<br />
MARGINAL (<strong>11</strong>1)<br />
NEGLIGIBLE (IV)<br />
Loss of ability to accomplish the mission or<br />
mission failure. Death or permanent total<br />
disability (accident risk). Loss of major or<br />
mission-critical system or equipment. Major<br />
property (facility) damage. Severe<br />
environmental damage. Mission-critical<br />
secu r i ty failu re. Unacceptable collateral<br />
damage.<br />
Significantly (severely) degraded mission<br />
capability or unit readiness. Permanent<br />
partial disability, temporary total disability<br />
exceeding 3 months time (accident risk).<br />
Extensive (major) damage to equipment or<br />
systems. Significant damage to property or<br />
the environment. Security failure.<br />
Significant collateral damage.<br />
Degraded mission capability or unit<br />
readiness. Minor damage to equipment or<br />
systems, property, or the environment. Lost<br />
day due to injury or illness not exceeding 3<br />
months (accident risk). Minor damage to<br />
property or the environment.<br />
Little or no adverse impact on mission<br />
capability. First aid or minor medical<br />
treatment (accident risk). Slight equipment<br />
or system damage, but fully functional and<br />
serviceable. Little or no property or<br />
environmental damage.<br />
Figure 2-3. Hazard Severity<br />
Substep C<br />
In this substep leaders and staffs expand what they understand<br />
about probable hazardous incidents into estimates of levels of risk for<br />
each identified hazard and an estimate of the overall risk for the<br />
operation. Estimating risk follows from examining the outcomes of<br />
Substeps A and B; that is, both the probability and severity of<br />
hazardous incidents. This substep is more art than science. Much<br />
depends on the use of historical lessons learned, intuitive analysis,<br />
2-1 0
FM 100-14<br />
experience, and judgment. Uncertainty can arise in the assessment of<br />
both the probability and severity of a hazardous incident. Uncertainty<br />
results from unknowns about a situation; from incomplete, inaccurate,<br />
undependable, or contradictory information; and from unforeseen<br />
circumstances. Therefore, assessment of risk requires good judgment.<br />
Figure 2-4 is a standardized matrix that can be used to assist in this<br />
process. Leaders and staffs enter the estimated degree of severity and<br />
probability for each hazard in Substeps A and B from the severity row<br />
and probability column, respectively. The point where the severity<br />
row and probability column intersect defines the €eve1 of risk. For<br />
example, if the hazard is estimated to have a critical severity (<strong>11</strong>) and a<br />
Zikely probability (B), the level of risk is high (H).<br />
Figure 2-5 provides a summary of the levels of risk. It also<br />
provides examples of hazardous incidents for each risk level. Several<br />
examples illustrate the trade-off between tactical and accident risks.<br />
Probability<br />
Severity<br />
Frequent<br />
A<br />
Likely Occasional Seldom Unlikely<br />
B C D E<br />
Catastrophic<br />
I<br />
Critical<br />
II<br />
Marginal<br />
<strong>11</strong>1<br />
Negligible<br />
IV<br />
M L L L L<br />
E - Extremely High <strong>Risk</strong><br />
H - High <strong>Risk</strong><br />
M - Moderate <strong>Risk</strong><br />
L - Low <strong>Risk</strong><br />
Figure 2-4. <strong>Risk</strong> Assessment Matrix<br />
2-1 1
<strong>Risk</strong> <strong>Management</strong><br />
E - Extremely High: Loss of ability to accomplish the mission if hazards<br />
occur during mission. A frequent or likely probability of catastrophic loss<br />
(IA or IB) or frequent probability of critical loss (HA) exists.<br />
Example: A commander finds that one of his implied tasks to attack an<br />
objective involves crossing a normally shallow riverbed. After looking at<br />
the factors of METT-T, he discovers that three days of intense rain have<br />
raised the water level to rise above flood stage, with currents far in<br />
excess of his ability to safely ford with armored vehicles. After<br />
discussing COAs with his staff, he determines the accident risk is<br />
extremely high because of the likely probability and catastrophic<br />
severity of losing vehicles and killing soldiers. His conclusions are<br />
based on his experience with and knowledge of fording armored<br />
vehicles under the existing conditions of water depth and current<br />
speed.<br />
H - High: Significant degradation of mission capabilities in terms of the<br />
required mission standard, inability to accomplish all parts of the<br />
mission, or inability to complete the mission to standard if hazards<br />
occur during the mission. Occasional to seldom probability of<br />
catastrophic loss (IC or ID) exists. A likely to occasional probability<br />
exists of a critical loss (IlB or IIC) occurring. Frequent probability of<br />
marginal losses (I I IA) exists.<br />
Example: During a preplanned ambush, the leader discovers that the<br />
force he intends to ambush has significantly more combat power than<br />
his own force can accommodate. He realizes that he could only detay<br />
rather than destroy the enemy. He knows his casualty estimates would<br />
be very high if the enemy reorganized and counterattacked. He also<br />
knows that the size of the enemy force could seriously impact adjacent<br />
units conducting a movement to contact. He determines the situation is<br />
high risk because he estimates (based on his training and experience)<br />
there is a likely probability of the enemy reor anizing and<br />
counterattacking and the severity of loss to his unit wou B d be critical.<br />
M - Moderate: Expected degraded mission capabilities in terms of the<br />
required mission standard will have a reduced mission capability if<br />
hazards occur during mission. An unlikely probability of catastrophic<br />
loss (IE) exists.The probability of a criticalloss is seldom (IID). Marginal<br />
losses occur with a likely or occasional probability (IIIB or IIIC). A<br />
frequent probability of negligible (IVA) losses exists.<br />
Example: A commander in a defensive position receives a warning order<br />
to be prepared to counterattack if the enemy attacks again. He chooses<br />
to use pre-positioned ammunition caches to support his defense, as<br />
opposed to moving his ammunition resupply forward by truck. He<br />
determines that the severity of not having an immediate resupply of<br />
ammunition available during the counterattack will have a criticalimpact<br />
on his combat power. He realizes that if the enemy forces him to<br />
abandon his forward positions, the severity of the loss of his<br />
Figure 2-5. Levels of <strong>Risk</strong><br />
2-1 2
FM 100-14<br />
ammunition caches will critically impact his combat power. He<br />
considers that his unit is deployed in excellent defensive positions. He<br />
has repelled two attacks that resulted in the destruction of an estimated<br />
50 percent of the enemy’s combat power. He receives information that<br />
the probability of the enemy attacking is likely; but that the probability<br />
of the enemy being reinforced and attacking in overwhelming force is<br />
remote (seldom). The commander concludes that the risk of conducting<br />
a counterattack with limited ammunition is greater than the moderate<br />
risk of the enemy pushing him back.<br />
L - Low: Expected losses have little or no impact on accomplishing the<br />
mission. The probability of critical loss is unlikely (IIE), while that of<br />
marginal loss is seldom (HID) or unlikely (HIE). The probability of a<br />
negligible loss is likelyor less (IVB through (WE).<br />
Example: A mechanized task force (TF) conducting a movement to<br />
contact in a desert environment is overtaken by nightfall before<br />
reaching its limit of advance (LOA). The terrain along the axis of<br />
advance is flat and open. Visibility is about 800 meters under a clear sky<br />
illuminated by a full moon. Estimates put the enemy, which has been<br />
hastily withdrawing for the past three days, at approximately 30 percent<br />
strength. Contact has been iight with no defensible terrain along the<br />
TF’s axis. The TF commander considers all the factors. In addition, the<br />
TF is 100 percent operational in using night vision devices. The TF<br />
commander estimates that it is unlikely that his unit will incur losses of<br />
critical severity by being surprised by the enemy or lose critical combat<br />
power due to an accident. He estimates the risk to his force in<br />
continuing a nighttime movement is low<br />
Figure 2-5. Levels of <strong>Risk</strong> (continued)<br />
STEP 3. DEVELOP CONTROLS AND MAKE RISK DECISIONS<br />
<strong>Risk</strong> management is the recognition that decision making<br />
occurs under conditions of uncertainty. Decisions must remain<br />
consistent with the commander’s stated intent and offer a good<br />
expectation of success. The risk-taking skill requires<br />
competency as a prerequisite.<br />
FM 100-7, Decisive Force:<br />
The Army in Theater Operations, May 1995<br />
Step 3 is accomplished in two substeps: develop controls and<br />
make risk decisions. This is done during the COA development, COA<br />
analysis, COA comparison, and COA approval of the military<br />
decision-making process.<br />
Substep A - Develop Controls<br />
After assessing each hazard, leaders develop one or more controls<br />
that either eliminate the hazard or reduce the risk (probability and/or<br />
2-1 3
<strong>Risk</strong> <strong>Management</strong><br />
severity) of a hazardous incident. When developing controls, they<br />
consider the reason for the hazard not just the hazard itself.<br />
Types of ControlGontrols can take many forms, but fall<br />
into three basic categories-educat ional controls, physical controls,<br />
and avoidance.<br />
EducationaZ controls. These controls are based on the knowledge<br />
and skills of the units and individuals. Effective control is<br />
implemented through individual and collective training that<br />
ensures performance to standard.<br />
Physical controls. These controls may take the form of barriers<br />
and guards or signs to warn individuals and units that a hazard<br />
exists. Additionally, special controller or oversight personnel<br />
responsible for locating specific hazards fall into this category.<br />
Avoidance. These controls are applied when leaders take positive<br />
action to prevent contact with an identified hazard.<br />
Criteria for Contro?bsbe effective, each control developed<br />
must meet the following criteria:<br />
Suitability. It must remove the hazard or mitigate (reduce) the<br />
residual risk to an acceptable level.<br />
FeasibiZity. The unit must have the capability to implement<br />
the control.<br />
Accqtability. The benefit gained by implementing the control<br />
must justify the cost in resources and time. The assessment of<br />
acceptability is largely subjective. Figure 2-6 gives criteria for<br />
determining acceptability of controls for each identified hazard.<br />
Support<br />
Standards<br />
Tra i n in g<br />
Leadership<br />
Individual<br />
Availability of adequate personnel, equipment,<br />
supplies, and facilities necessary to implement a<br />
suitable controls.<br />
Guidance and procedures for implementing a control<br />
are clear, practical, and specific.<br />
Knowledge and skills are adequate to implement a<br />
control.<br />
Leaders are competent to implement a control.<br />
Individual soldiers are sufficiently self-disciplined to<br />
implement a control.<br />
2-1 4<br />
Figure 2-6. Criteria for Determining Acceptability of Controls
FM 100-14<br />
Examples of Control &les of controls include-<br />
Engineering or designing to eliminate or control hazards.<br />
Selecting a COA that avoids identified hazards.<br />
Limiting the number of people and the amount of time they are<br />
exposed to hazards, consistent with mission requirements.<br />
Selecting personnel with appropriate mental, emotional, and<br />
physical capabilities.<br />
Providing protective clothing, equipment, and safety and<br />
security devices.<br />
Providing such services as adequate sanitation facilities and<br />
water purification capabilities.<br />
Providing warning signs and signals.<br />
Scheduling vehicle and aircraft silhouette drills.<br />
Planning training, including rehearsals, rock drills, battle drills,<br />
and so forth.<br />
Programming communications links for key civilian organizations.<br />
Establishing battlefield controls such as areas of operations and<br />
boundaries, direct fire control measures, fire support<br />
coordination measures, rules of engagement, airspace control<br />
measures, bridge classification, traffic control, and so forth.<br />
Developing terrorist attack warning systems and response plans.<br />
The key is to specify who, what, where, when, and how each<br />
control is to be used. For example-<br />
Planning and scheduling intensive threat and friendly vehicle<br />
identification refresher training for all antiarmor and air defense<br />
weapons crews before the mission reduces the probability of<br />
engaging a friendly vehicle or aircraft (fratricide).<br />
Programming installation of crashworthy passenger seats in the<br />
UH-60 Blackhawk, when mission circumstances do not indicate<br />
their removal, can reduce the severity of injuries in crashes.<br />
Requiring soldiers to wear flak vests and helmets during<br />
movement to contact, or when riding in vehicles in areas where<br />
enemy fire is likely, can reduce the probability and severity of a<br />
wound from small arms fire or fragments.<br />
2-1 5
<strong>Risk</strong> <strong>Management</strong><br />
Establishing strong continuity documents and planning overlap<br />
tours for key leaders facilitate smooth transitions during<br />
extended operations.<br />
Residual <strong>Risk</strong>once the responsible leader develops and<br />
accepts controls, he determines the residual risk associated with each<br />
hazard and the overall residual risk for the mission.<br />
Residual risk is the risk remaining after controls have been<br />
selected for the hazard. Residual risk is valid (true) only if the<br />
controls for it are implemented. As controls for hazards are<br />
identified and selected, the hazards are reassessed as in Step 2<br />
and the level of risk is then revised. This process is repeated until<br />
the level of residual risk is acceptable to the commander or leader<br />
or cannot be further reduced. See Figures A-3 through A-5.<br />
Overall residual risk of a mission must be determined when more<br />
than one hazard is identified. The residual risk for each of these<br />
hazards may have a different level, depending on the assessed<br />
probability and severity of the hazardous incident. Overall<br />
residual mission risk should be determined based on the incident<br />
having the greatest residual risk. Determining overall mission risk<br />
by averaging the risks of all hazards is not valid. If one hazard has<br />
high risk, the overall residual risk of the mission is high, no matter<br />
how many moderate or low risk hazards are present.<br />
Substep B - Make <strong>Risk</strong> Decision<br />
A key element of the risk decision is determining if the risk is<br />
justified. The commander must compare and balance the risk against<br />
mission expectations. He alone decides if controls are sufficient and<br />
acceptable and whether to accept the resulting residual risk. If he<br />
determines the risk level is too high, he directs the development of<br />
additional controls or alternate controls, or he modifies, changes, or<br />
rejects the COA.<br />
Leaders can use the risk assessment matrix in Figure 2-4-in<br />
conjunction with their commanders’ guidance-to communicate how<br />
much risk they are willing to delegate. For example, a commander may<br />
place constraints on his subordinates that restrict their freedom of action<br />
to accept risk in instances where the risk might imperil his intent, his<br />
higher commander’s intent, or a critical capability of the unit.<br />
2-1 6
FM 100-14<br />
STEP 4. IMPLEMENT CONTROLS<br />
Leaders and staffs ensure that controls are integrated into SOPS,<br />
written and verbal orders, mission briefings, and staff estimates. The<br />
critical check for this step, with oversight, is to ensure that controls<br />
are converted into clear, simple execution orders understood at all<br />
levels. Implementing controls includes coordination and<br />
communication wit h-<br />
Appropriate superior, adjacent, and subordinate units and those<br />
executing the mission.<br />
Logistics Civil Augmentation Program (LOGCAP) organizations<br />
and civilian agencies that are part of the force.<br />
The media, NGOs, and PVOs must be included in coordination when<br />
their presence impacts or is impacted by the force.<br />
Leaders must explain how supervisors will implement controls.<br />
Examples of control implementation include-<br />
Conducting vehicle and aircraft silhouette drills.<br />
Conducting rehearsals, rock drills, battle drills, and so forth.<br />
Conducting intensive threat and friendly vehicle<br />
identification refresher training for all antiarmor and air<br />
defense weapons crews.<br />
Conducting orientation for replacement personnel.<br />
Installing and maintaining communications :links for key<br />
civilian organizations.<br />
Operating in convoys of four vehicles minimum.<br />
Carrying weapons and wearing flak jackets and helmets when<br />
outside secure compounds.<br />
STEP 5. SUPERVISE AND EVALUATE<br />
Leaders must supervise the execution of their orders. The more<br />
untrained the troops, the more detailed this supervision must be.<br />
Infantry in Battle, 1939<br />
During mission preparation and execution, leaders must ensure<br />
that their subordinates understand how to execute risk controls.<br />
Leaders continuously assess risks during the conduct of operations,<br />
2-1 7
<strong>Risk</strong> <strong>Management</strong><br />
especially during long-term missions. Leaders maintain situational<br />
awareness. They guard against complacency to ensure that risk<br />
control standards are not relaxed or violated. To gain insight into areas<br />
needing improvement, leaders must continuously evaluate their<br />
units’ effectiveness in managing mission risks.<br />
Supervise<br />
Leaders supervise mission rehearsal and execution to ensure<br />
standards and controls are enforced. Techniques may include spotchecks,<br />
inspections, situation reports and brief-backs, buddy checks,<br />
and close supervision. During the mission, leaders continuously<br />
monitor controls to ensure they remain effective. They mod* them as<br />
necessary. Leaders and individuals anticipate, idenw, and assess new<br />
hazards to implement controls. They continually assess variable<br />
hazards such as fatigue, equipment serviceability,, and the environment.<br />
Leaders mod* controls to keep risks at an acceptable level.<br />
During sustained operations, leaders continue planning to ensure<br />
that controls emplaced at the beginning of the mission apply to<br />
changes in the operation’s current situation and to hazardous<br />
conditions. Leaders must maintain an extraordinary degree of<br />
discipline. They must avoid complacency, which can result from<br />
boredom and overconfidence. Leaders must ensure that soldiers do<br />
not relax their vigilance due to performing repetitive tasks-despite<br />
changing roles and missions, unit turbulence and turnover, and<br />
declining skills. Leaders maintain a close ovenvatch on controls put in<br />
place to reduce risks over a prolonged period. For example, during<br />
stability operations, land mine hazards may not be solved in the near<br />
term, but may require continual attention. Other examples of longterm<br />
hazards that may be encountered include-<br />
Climatic extremes.<br />
NBC and hazardous waste contamination.<br />
Diseases native to a particular area of operation or indigenous<br />
population.<br />
Terrorist threats.<br />
Evaluate<br />
After a mission, leaders and individuals evaluate how well the<br />
risk management process was executed. They-<br />
Determine how to ensure that successes are continued to the<br />
next mission.<br />
2-1 8
FM 100-14<br />
Capture and disseminate lessons learned so that others may<br />
benefit from the experience.<br />
Consider the effectiveness of the risk assessment in identifying<br />
and accurately assessing the probability and severity of hazards<br />
that resulted in mission degradation.<br />
Determine whether the level of residual risk of each hazard and<br />
of the overall mission were accurately estimated.<br />
Evaluate the effectiveness of each control in reducing or<br />
removing risk, including whether controls were effectively<br />
communicated, implemented and enforced.<br />
Leaders and individuals determine why some controls were<br />
ineffective and what should be done when the hazard is encountered<br />
again. A control may be altered; the way it is implemented or<br />
supervised may be changed to make it effective; or a completely<br />
different control may be more effective. Leaders must energize the<br />
system to fix systemic problems that hinder combat effectiveness.<br />
Figure 2-7 shows that the risk management process continues<br />
throughout a mission as well as from mission to mission. It is<br />
integral to the military decision-making process. Its application<br />
requires good judgment and intuitive analysis borne of confidence,<br />
experience, and situational awareness.<br />
TOOLS AND PITFALLS<br />
The appendix provides examples of risk management tools to<br />
help leaders assess identified hazards, develop controls, and make<br />
risk decisions. The tools should be tailored to suit particular situations<br />
and missions. The examples in Figures A-3 through A-5 are tools to<br />
manage risk at the tactical level. The example in Figure A-6 is a tool to<br />
manage risk at the operational level. Units may develop additional<br />
tools suitable for their needs.<br />
Units train to a standard. They operate and train regardless of the<br />
degree of real or perceived difficulty. <strong>Risk</strong> reduction begins with<br />
commanders identifying their METLs. Commanders use the risk<br />
management process to assess the degree of risk related to each METL<br />
their unit must perform. From this assessment, risk reducing standard<br />
operating procedures evolve.<br />
Figure A-7 provides an example of risk management<br />
considerations integrated into a mission training plan (MTP) task.<br />
2-1 9
<strong>Risk</strong> <strong>Management</strong><br />
-<br />
Step 2. Assess Hazards<br />
Estimate<br />
probability<br />
I Step 5. Supervise and Evaluate I<br />
<strong>11</strong> Supervise 1 I) 1 Evaluate 1 I<br />
'. '<br />
Estimate<br />
severity<br />
h 1<br />
Determine risk level for<br />
each hazard and overall<br />
8<br />
I<br />
'#I<br />
Step 4. Implement Controls I ---: *;<br />
.,<br />
Step 3. Develop Controls and<br />
Make <strong>Risk</strong> Decision<br />
Develop<br />
controls<br />
Determine residual risk<br />
level for each hazard<br />
and overall residual<br />
mission risk'<br />
Make<br />
decision<br />
'As controls for hazards are identified and selected the hazards are<br />
reassessed as in Step 2<br />
Figure 2-7. Continuous Application of <strong>Risk</strong> <strong>Management</strong><br />
2-20
FM 100-14<br />
Pitfalls arise when risk management tools are used without<br />
adaptation to the factors of METT-T. Using a standardized risk<br />
assessment card or checklist may be of some value initially in the<br />
mission analysis and COA development or in cases where a routine<br />
task is performed in an unchanging environment or static situation.<br />
However, such a tool used alone will not likely identify all hazards for<br />
every mission in a changing operational environment.<br />
Completing the risk assessment alone, but failing to identify<br />
effective controls, usually results in a GO or NO-GO decision based on<br />
the initial risk. If the risk assessment does not accurately identify the<br />
hazards and determine the level of residual risk, the leader is likely to<br />
make his risk decision based upon incomplete or inaccurate<br />
information. If the risk assessment places missions in a routine, lowrisk<br />
category, the commander may not be informed of a risk decision<br />
resulting in an accepted risk level that could imperil his or his higher<br />
commander’s intent or other affected organizations. The risk<br />
management process is intended to provide reasonable controls to<br />
support mission accomplishment without exposing the force to<br />
unnecessary residual risk.<br />
2-2 1
Chapter 3<br />
<strong>Risk</strong> <strong>Management</strong> Implementation<br />
It is imperative to develop twenty-first century leaders who<br />
trust their subordinates’ abilities and judgment. Such leaders<br />
must be willing to underwrite their subordinates’ honest errors<br />
and coach them on to excellence, without tolerating<br />
incompetence or laxity. We must recognize that Army leaders<br />
are not perfect, and that activity at the ragged edge of audacity<br />
sometimes leaves debris in its wake.<br />
GEN William W. Hartzog<br />
Commanding General<br />
US Army Training and Doctrine Command<br />
This chapter presents the moral and ethical<br />
implications of risk management. It outlines essential<br />
responsibilities and considerations necessary to<br />
effectively integrate and assess risk management<br />
within the Army. Leaders should tailor these essentials<br />
to develop specific how-to procedures suited to their<br />
circumstances , available resources , and mission.<br />
MORAL AND ETHICAL IMPLICATIONS<br />
FOR LEADERS<br />
To be successful, risk management must be underwritten by the<br />
chain of command. Leaders should not expect that all missions will be<br />
accomplished with zero defects-free from errors, flaws, or less-thanperfect<br />
performance. Demanding such rigid standards leads to<br />
oversupervision and paralysis; it produces timid leaders, afraid to<br />
make tough decisions in crisis and unwilling to take risks necessary<br />
for success in military operations. A zero defects mindset creates<br />
conditions that will lead inevitably, in the larger sense, to failure in<br />
battle and higher casualties. Leaders are morally bound to support a<br />
subordinate’s decision to accept risks that are within his commander’s<br />
intent and guidance, as he understands it.<br />
Leaders accept that things may go wrong, even with the certain<br />
knowledge that a subordinate has done all within his power to<br />
prevent an incident. In such an event, the leader steps forward and<br />
3-0
FM 100-14<br />
accepts the responsibility along with his subordinate. Furthermore,<br />
risk management does not justify taking actions to facilitate an<br />
unethical or immoral action. FM 22-100 addresses the moral and<br />
ethical aspects of protecting the force within the overall framework of<br />
how to apply leadership at all levels to meet mission requirements.<br />
Everyday as we respond to the nation’s needs, we expose our<br />
soldiers to hazards in uncertain and complex environments. We<br />
do this with the full knowledge that there are inherent risks<br />
associated with any military operation. The nature of our<br />
profession will not allow for either complacency or a cavalier<br />
acceptance of risk.<br />
General Dennis J. Reimer<br />
Chief of Staff, Army<br />
RESPONSIBILITIES<br />
One critical task for all operations is minimizing risk. Every military<br />
plan must make this a priority. It is an inherent part of every mission<br />
and a basic responsibility of commanders. Whether for training or<br />
operational deployments, commanders issue clear risk guidance.<br />
Minimizing risk-eliminating unnecessary risk-is the responsibility of<br />
everyone in the chain of command. This responsibility runs from the<br />
highest commander, through his subordinate leaders, to the soldier.<br />
The commander and his staff must look at tactical risks and<br />
accident risks. They use the same risk management process to manage<br />
both types. Commanders-with the assistance of their leaders and<br />
staffs-manage accident risks. Commanders determine how and<br />
where they are willing to take tactical risks.<br />
Leaders and soldiers at all levels are responsible and<br />
accountable for managing risks by ensuring that hazards and<br />
associated<br />
.<br />
risks are-<br />
Identified during planning, preparation, and execution of<br />
operations.<br />
Controlled during preparation and execution of operations.<br />
Soldiers are responsible for executing risk controls to standards. They<br />
must continuously assess variable hazards such as fatigue, equipment<br />
serviceability, and the environment. They must take care of one<br />
3-1
<strong>Risk</strong> <strong>Management</strong><br />
another and make risk decisions consistent with the higher<br />
commander’s guidance.<br />
Sometimes commanders are not properly advised in situations<br />
where the assumption of risk may affect or imperil their units, the<br />
intent of their higher commander, or the operations of an adjacent<br />
unit. This is most often attributed to-<br />
* The risk denial syndrome in which leaders do not want to know of<br />
the risk.<br />
A staff member who believes that the risk decision is part of his<br />
job and does not want to bother his commander or section leader.<br />
A subordinate who does not fully understand the higher<br />
commander’s guidance.<br />
Complacency-outright failure to recognize a hazard or the<br />
level of risk involved, or overconfidence in one’s abilities or the<br />
unit’s capabilities to avoid or recover from a hazardous incident.<br />
Use of a standardized risk assessment tool, such as a risk<br />
assessment card, that is not tailored to the unit’s mission or<br />
adapted to the factors of MET-T and which may put missions<br />
in the routine low-risk category.<br />
COMMANDERS<br />
The commander directs the organization and sets priorities and<br />
the command climate (values, attitudes, and beliefs). Successful<br />
preservation of combat power requires embedding risk management<br />
into unit behavior. This requires commitment and creative<br />
leadership-innovative planning, careful management. It also<br />
requires the chain of command’s demonstrated support of the risk<br />
management process. Only then will the Army begin to capture the<br />
full power of risk management. Commanders establish a command<br />
climate favorable for risk management integration by-<br />
3-2<br />
* Demonstrating consistent and sustained risk management<br />
behavior through leading by example-habitually doing risk<br />
management-and actively participating throughout the risk<br />
management process.<br />
Providing clear guidance, when appropriate, on where or what<br />
risk to accept.
FM 100-14<br />
Obtaining and providing to subordinates the necessary assets to<br />
control risk.<br />
Knowing their own limitations, their leaders’ and soldiers’<br />
limitations, and their unit’s capabilities.<br />
Preventing a zero-defects mindset from creeping into their<br />
command’s culture.<br />
Allowing subordinates to make mistakes and learn from them.<br />
Demonstrating full confidence in subordinates’ mastery of their<br />
trade and their ability to execute a chosen COA.<br />
Keeping subordinates informed; consulting with subordinate<br />
leaders before making a decision, if feasible.<br />
Listening to subordinates.<br />
Commanders are responsible and accountable for their own<br />
actions and those of units under their charge. Commanders must<br />
weigh the repercussions of casualties, damage to the environment,<br />
and loss of equipment. They must also consider the level of public<br />
reaction to loss against national, strategic, operational, or tactical<br />
objectives. Commanders are also responsible for keeping soldiers<br />
from falling into complacency. During sustained operations in<br />
particular, complacency can creep in as a result of accepting the status<br />
quo. For example, a unit can be deployed for several months and<br />
nothing may happen. The unit then gets very satisfied with itself and<br />
its performance. It gets conditioned to its initial circumstances-being<br />
well-armed, well-equipped, well-disciplined, and well-trained. It<br />
thinks it has risks under control and does not need to change. Such<br />
complacency, and the associated loss of situational awareness, can<br />
result in leaders and soldiers taking a gamble instead of a prudent<br />
risk. A risk is the accepted result of an informed decision; a gamble is<br />
an uninformed bet or guess on a hopeful outcome. Leaders and<br />
soldiers must clearly understand the difference.<br />
Command is often exercised in conditions of uncertainty and<br />
ambiguity, where violence, danger, fear, and friction abound, and<br />
under the ever present time constraints driven by OPTEMPO. <strong>Risk</strong><br />
decisions are frequently required by and dependent on the immediate<br />
situation. Judgment is required; a formula, rule, or checklist, by itself,<br />
is not appropriate under such circumstances.<br />
Avoiding the zero-risk mindset requires the exercise of positive<br />
leadership. The commander’s approach to managing risk should be<br />
3-3
<strong>Risk</strong> <strong>Management</strong><br />
through empowering leaders by pushing risk decisions as far down<br />
the chain of command as feasible within the next higher commander’s<br />
guidance. Commanders must insist that subordinates exercise their<br />
freedom of action to act decisively and aggressively to complete<br />
assigned missions and promote success of the larger force.<br />
Subordinates must consider hazards outside their assigned<br />
responsibilities that impact the mission. The result is to encourage<br />
coordination and communication-laterally and up and down the<br />
chain of command. This requires and encourages initiative, which<br />
demands well-trained, determined, disciplined soldiers.<br />
<strong>Risk</strong> management is a two-way street. It is important that those<br />
involved in mission preparation and execution be fully aware of the<br />
amount of command involvement and actions necessary to control or<br />
remove hazards. The higher commander’s guidance specifies the<br />
degree of damage or risk to subordinate units that he is willing to accept<br />
during the current operation. Subordinates ensure they understand and<br />
implement their commander’s intent and guidance. If, during the<br />
planning process, the accident and/or tactical residual risk exceeds that<br />
which the higher commander is willing to accept, the subordinate<br />
informs his commander. He requests the resources necessary to mitigate<br />
the risk. If, during mission execution, the subordinate determines the<br />
risk is too great, he directs the development of additional or alternate<br />
controls or modifies or changes the COA. He should notify his next<br />
higher commander of his decision. Requiring subordinates to report to<br />
the higher commander when a risk decision point is reached during<br />
mission execution can result in paralysis.<br />
The objective of managing risk is not to remove all risk, but to<br />
eliminate unnecessary risk. Commanders conduct tough, realistic<br />
training, knowing that they may put lives and property at risk in the<br />
course of military operations. Nothing is worth the cost of a life as the<br />
result of taking unnecessary risk. If an action will result in an<br />
unacceptable risk, measures should be taken to mitigate it. If the risk<br />
cannot be mitigated to an acceptable level, the action should not be<br />
executed. Circumstances may occur during mission execution when a<br />
decision to stop and defer execution of the operation should be made<br />
to avoid taking unwarranted risk. Such a situation will generally occur<br />
at the tactical level. For example, circumstances may determine if a<br />
trade-off between maintaining the momentum of the attack or risking<br />
fratricide or serious accidents is justified. For example, during the<br />
deployment of TF Eagle to Bosnia-Herzegovina, there was pressure to<br />
3-4
FM 100-14<br />
complete the Sava River bridge as quickly as possible. The<br />
commander assessed the situation and decided to call for a short rest<br />
period because his soldiers were tired and getting careless.<br />
Consequently, they completed the bridge ahead of schedule under the<br />
most difficult conditions imaginable and without injuries.<br />
LEADERS<br />
Many of the tasks identified for commanders apply to all leaders.<br />
Leaders’ specific responsibilities in managing risk include-<br />
* Establishing clear, feasible risk management policies and goals.<br />
Conducting detailed planning within time constraints; assessing<br />
each mission and task in terms of its risk; continuously<br />
reassessing risk as the mission and conditions change and<br />
experience is gained.<br />
Making informed risk decisions and establishing and clearly<br />
communicating risk guidance.<br />
Training the risk management process. Ensuring subordinates<br />
understand the who, what, where, when, how, and why of<br />
managing risk and how the process applies to their<br />
circumstances and assigned responsibilities.<br />
Examining how subordinates manage risk and how soldiers<br />
protect themselves.<br />
Supervising and evaluating the unit’s execution of risk controls<br />
during the mission to correct areas needing improvement.<br />
Advising his chain of command on risks and risk-reduction<br />
measures.<br />
Providing subordinates with feedback on their performance and<br />
ways to improve.<br />
Assessing the effectiveness of their unit’s risk management<br />
program.<br />
Capturing and disseminating lessons learned to ensure they are<br />
continued from mission to mission so that others may benefit<br />
from the experience.<br />
3-5
<strong>Risk</strong> <strong>Management</strong><br />
STAFFS<br />
The chief of staff or executive officer is responsible for supervising<br />
integration of risk management across the staff. He coordinates<br />
development of risk reduction controls with emphasis on<br />
deconflicting controls that affect multiple functional areas and<br />
adjacent units. The staff officer helps the commander eliminate<br />
unnecessary risks by-<br />
* Analyzing his functional area and applying risk management<br />
during the military decision-making process.<br />
Iden-g<br />
constraints in the higher commander’s risk guidance.<br />
Including hazards and their risks in the mission analysis briefing.<br />
* Including a risk assessment for the commander’s estimate.<br />
Considering the risk assessment in the operations estimate.<br />
Including risks and recommending ways to reduce their impact<br />
in the staff estimate.<br />
Implementing risk controls by coordinating and integrating<br />
them into the appropriate paragraphs and graphics of the<br />
OPORD and into products such as SOPS and OPLANs.<br />
Establishing procedures and standards that are clear and<br />
practical.<br />
Determining the effectiveness of hazard/risk controls and<br />
c on t inu o u s 1 y a s s e s s in g their sui tab i li t y, f e a s i b i 1 it y, an d<br />
acceptability.<br />
Supervising, evaluating, and assessing the integration of risk<br />
management during an operation.<br />
Continuously identifymg hazards, assessing initial and residual<br />
risks for each hazard, recommending control measures to reduce<br />
the risk to the force.<br />
Identifying and assessing hazards associated with complacency,<br />
especially during extended operations, and recommending<br />
appropriate actions to the commander.<br />
At the operational level, staffs focus on hazards and their risks across<br />
the spectrum of protecting the force<br />
3-6
FM 100-14<br />
INDIVIDUALS<br />
The level of expertise and maturity of the individual influence his<br />
proficiency in managing risk. Managing risk is subjective because its<br />
basis is individual judgment. Young soldiers are routinely charged<br />
with executing hazard controls and risk reduction measures. By<br />
nature, some them are impulsive risk takers. Their limited experience,<br />
coupled with an infallible attitude, can significantly increase the level<br />
of risk they are willing to accept. Their sense of indestructibility,<br />
motivation (esprit de corps), and willingness to achieve the mission at<br />
any cost also play a part.<br />
Some soldiers and individuals ignore existing standards and<br />
improvise their own. Due to inexperience or complacency, they<br />
become susceptible to-<br />
* Overestimating their ability to respond to or recover from a<br />
hazardous incident-they become overconfident.<br />
Underestimating the level of risk posed by a hazard.<br />
It is imperative that individuals understand and execute controls<br />
implemented by leaders and staffs.<br />
Individuals must maintain situational awareness and selfdiscipline<br />
when they perform their duties. They must-<br />
Understand and apply risk management.<br />
Execute controls directed by their leaders, that is, perform to<br />
standards.<br />
Carry risk management over into training and activities-both<br />
on and off duty.<br />
Look out for others-anyone has authority to halt something<br />
that is inherently unsafe.<br />
INTEGRATION INTO TRAINING<br />
AND OPERATIONS<br />
ARFOR commanders/leaders must continuously employ risk<br />
management approaches to efectively preclude unacceptable<br />
risks to personnel and property, including protecting forces<br />
preparing for or en route to combat.<br />
FM 100-7, Decisive Force: The Army in Theater Operations,<br />
May 1995<br />
3-7
<strong>Risk</strong> <strong>Management</strong><br />
Integrating risk management into training and operations-<br />
* Preserves the lives and well-being of everyone.<br />
Conserves equipment, facilities, environmental resources, and<br />
combat power.<br />
<strong>Risk</strong> management must not be treated as an afterthought. It must be<br />
planned for up front. Leaders and managers of materiel acquisition,<br />
base operations, and industrial operations must budget risk control<br />
costs up front at the level of expected payback over the duration of the<br />
activity, or the life cycle of materiel/weapons system.<br />
When integrating risk management into sustained operations,<br />
leaders must consider increases in turbulence, personnel turnover,<br />
critical skill atrophy, and mission development. Leaders must<br />
continuously assess-<br />
* The complexity of mission development and associated<br />
changing interrelationships with other agencies.<br />
The inclusion of civilian contractors, for example, LOGCAP, as<br />
part of the force.<br />
The presence of the media, NGOs, and PVOs.<br />
These diverse elements need to be integrated into the risk<br />
management process.<br />
Two key considerations relevant to managing risk in complex<br />
operational environments include-<br />
3-8<br />
* Understanding the culture of the indigenous population or<br />
society and its way of doing business. Leaders should respect<br />
their way of life and not interfere with local customs. Such<br />
interference could risk damage to relationships and increase the<br />
potential for introducing instability into the local society.<br />
Leaders must not, however, intentionally allow these<br />
considerations to endanger their force or its mission.<br />
The dynamics of managing risk and the way the leader and his<br />
subordinates manage risk. Leaders manage risk by-<br />
- Having the right combination of well-trained, disciplined,<br />
well-armed, and well-equipped forces.<br />
- Issuing clear guidance to minimize risk.<br />
- Determining and implementing risk controls for carrying<br />
out the mission.
FM 100-14<br />
- Maintaining situational awareness, especially of<br />
vulnerabilities.<br />
- Avoiding unnecessary accident risk.<br />
<strong>Risk</strong> management works best when incorporated into existing<br />
command training and operational planning cycles. They then act as<br />
risk management tools and provide for-<br />
* Development of policy, goals, objectives, and priorities in the<br />
commander’s quarterly training guidance.<br />
The commander’s training assessment, by identifying hazards<br />
and risk controls.<br />
Systematic observation and assessment of the unit’s risk<br />
management performance and feedback into the training<br />
management cycle and SOPS.<br />
Leaders and soldiers must have the skills, knowledge, and<br />
attitude to effectively manage risks inherent in all operations. Effective<br />
training helps soldiers become proficient. It qualifies them technically<br />
and tactically, and as leaders, to accomplish the mission without<br />
unnecessary risk.<br />
Doctrine developers must integrate risk management into planning<br />
for all Army processes, especially the training management cycle<br />
defined in FMs 25-100 and 25-101. Unit leaders and their staffs must<br />
continually assess and evaluate the integration of risk management into<br />
short-, near-, and long-term training plans. They must continually<br />
review METLs to ensure that training is supported by realistic risk<br />
management objectives. In the past, unprepared or improperly trained<br />
units paid a high price for veteran status. The Army must learn from<br />
past experiences if it is to avoid repeating such losses.<br />
ASSESSMENT OF<br />
THE RISK MANAGEMENT PROCESS<br />
To assess the risk management process is to determine a unit’s<br />
current level of proficiency in implementing the process. The term<br />
assessment, as discussed here, differs from evaluation as used in<br />
Step 5 of the process. Evaluation is used to measure demonstrated<br />
ability to accomplish specified objectives within a discrete<br />
operation or exercise. Assessment, as used here, also differs from<br />
3-9
<strong>Risk</strong> <strong>Management</strong><br />
the aspect of assessing hazards for probability and severity, as<br />
addressed in Step 2 of the process.<br />
How well risk is managed affects readiness. Leaders need to know<br />
the current status and effectiveness of their organization’s risk<br />
management program. They self-assess their unit’s effectiveness in<br />
managing risk in order to gain insight into areas for improvement and<br />
get feedback on subordinates’ understanding and application of risk<br />
guidance. The assessment objectives are to determine how-<br />
* Effectively risk management is embedded into planning and<br />
preparing for operations.<br />
Well risk management is understood by subordinate leaders and<br />
soldiers.<br />
Effectively risk management is used to execute operations.<br />
Leaders assess the effectiveness of their units by reviewing how<br />
well hazards are identified and risk controls are-<br />
. Specified in oral and written OPORDs, OPLANs, and SOPS.<br />
Communicated to lowest level of chain of command.<br />
Included in short-, near-, and long-term training plans.<br />
Implemented into training and activities on and off duty.<br />
Embedded into protect-the-force programs such as safety and<br />
health and antiterrorism.<br />
Part of after-action reviews and fed into lessons learned.<br />
<strong>Risk</strong> management cannot be seen as a competitive program<br />
whereby a unit or leader is judged or compared in a competitive sense.<br />
Focus is strictly on both reduction of risk and risk behavior.<br />
Take calculated risks. That is quite diferentfiom being rash.<br />
General George S. Patton, Jr.<br />
3-1 0
Appendix<br />
Examples of <strong>Risk</strong> <strong>Management</strong> Application<br />
The examples in this appendix are designed to help<br />
those charged with managing risk.<br />
TRACKING TOOL<br />
The work sheet instructions are in Figure A-1.<br />
Block<br />
4 - D Self explanatory<br />
E<br />
F<br />
G<br />
H<br />
I<br />
J<br />
K<br />
Identify task relating to the mission or task in Block A<br />
Identify Hazards - Identify hazards by reviewing MET-T factors for<br />
the mission or task. Additional factors include historical lessons learned,<br />
experience, judgment, equipment characteristics and warnings, and<br />
environmental considerations.<br />
Assess Hazards - Assessment includes historical lessons learned,<br />
intuitive analyses, experience, judgment, equipment characteristics and<br />
warnings, and environmental considerations. Determine initial risk for each<br />
hazard by applying risk assessment matrix (Figure 2-4). Enter the risk level<br />
for each hazard.<br />
Develop Controls - Develop one or more controls for each hazard<br />
that will either eliminate the hazard or reduce the risk (probability<br />
and/or severity) of a hazardous incident. Specify who, what, where, why,<br />
when, and how for each control. Enter controls.<br />
Determine Residual <strong>Risk</strong> - Determine the residual risk for each<br />
hazard by applyin the risk assessment matrix (Figure 2-4). Enter the<br />
residual risk level s or each hazard.<br />
Implement Controls - Decide how each control will be put into<br />
effect or communicated to the personnel who will make it happen (written or<br />
verbal instruction; tactical, safety, garrison SOPS, rehearsals). Enter controls.<br />
Determine Overall MissionlTask <strong>Risk</strong> - Select the highest residual<br />
risk level and circle it. This becomes the overall mission or task risk level.<br />
The commander decides whether the controls are sufficient to accept the<br />
level of residual risk. If the risk is too great to continue the mission or task,<br />
the commander directs development of additional controls or modifies,<br />
changes, or rejects the COA.<br />
Supervise and Evaluate - This last step is not on the worksheet.<br />
Plan how each control will be monitored for implementation (continuous<br />
supervision, spot-checks) and reassess hazards as the situation changes.<br />
Determine if the controls worked and if they can be improved. Pass on<br />
lessons learned.<br />
~~<br />
Figure A-I. <strong>Risk</strong> <strong>Management</strong> Work Sheet Instructions<br />
Appendix-1
<strong>Risk</strong> <strong>Management</strong><br />
The work sheet (Figure A-2) provides a starting point to logically<br />
track the process of hazards and risks. It can be used to document risk<br />
management steps taken during planning, preparation, and execution<br />
of training and combat missions and tasks.<br />
..<br />
a<br />
5<br />
P<br />
I!!<br />
n<br />
a<br />
c<br />
t2<br />
6<br />
i<br />
I<br />
QZij<br />
a .-<br />
E&<br />
E<br />
F<br />
a<br />
CI<br />
t2<br />
m<br />
Y<br />
u)<br />
F<br />
L<br />
0<br />
E<br />
0<br />
.-<br />
.-<br />
a<br />
u)<br />
u)<br />
a<br />
Append i x-2<br />
u:<br />
Y<br />
u)<br />
F<br />
CJ<br />
I<br />
I<br />
Figure A-2. Sample <strong>Risk</strong> <strong>Management</strong> Work Sheet
FM 100-14<br />
Examples provided in Figures A-3 through A-6 should help<br />
individuals manage risk at the tactical level.<br />
h<br />
n<br />
E<br />
n n h<br />
E E E<br />
Y<br />
u)<br />
F<br />
w<br />
Figure A-3. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for SquadPlatoon<br />
Appendix-3
<strong>Risk</strong> <strong>Management</strong><br />
xx<br />
xx<br />
5<br />
-<br />
n n<br />
5 5 f<br />
Y<br />
a, a, a,<br />
n<br />
E<br />
E<br />
d. a, d. a,<br />
P U<br />
U<br />
s J<br />
s<br />
E<br />
a,<br />
-0<br />
s<br />
m<br />
n<br />
E<br />
L<br />
0 a<br />
a<br />
Y<br />
u)<br />
F<br />
rri<br />
-<br />
Figure A-4. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for Com panyneam<br />
Appendix-4
FM 100-14<br />
i<br />
n<br />
J<br />
W<br />
6<br />
J<br />
- 0<br />
cn<br />
n<br />
d.<br />
6<br />
-I<br />
n<br />
J<br />
W<br />
J<br />
i<br />
Y<br />
v)<br />
F<br />
rri<br />
Figure A-5. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for Battalionnask Force<br />
Appendix-5
-r<br />
X<br />
<strong>Risk</strong> <strong>Management</strong><br />
i<br />
xx<br />
xx<br />
00<br />
$$<br />
66<br />
LDO<br />
t-90<br />
Om<br />
00<br />
77<br />
00<br />
\i d<br />
-<br />
5<br />
z<br />
h<br />
z<br />
h<br />
S<br />
.- 0<br />
e<br />
la<br />
v)<br />
Figure A-5. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for Battalionnask Force (continued)<br />
Appendix-6
FM 100-14<br />
I<br />
i<br />
n<br />
W<br />
W<br />
xx<br />
xx<br />
00<br />
88<br />
.- b<br />
.- c<br />
v)<br />
0<br />
a<br />
2<br />
2<br />
6<br />
E<br />
Z<br />
c<br />
v)<br />
a<br />
J<br />
J C<br />
(d<br />
E.<br />
i<br />
0<br />
Figure A-5. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for B att al io nnas k Force (con t i n ued)<br />
Append ix-7
~<br />
<strong>Risk</strong> <strong>Management</strong><br />
7<br />
Y<br />
v)<br />
w<br />
Figure A-6.<br />
Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for Division/Corps/EAC Task Force<br />
Appendix-8
FM 100-14<br />
i<br />
O<br />
Appendix-9
<strong>Risk</strong> <strong>Management</strong><br />
Figure A-6. Example of Completed <strong>Risk</strong> <strong>Management</strong> Work Sheet<br />
for Division/Corps/EAC Task Force (continued)<br />
Appendix-1 0
FM 100-14<br />
MISSION TRAINING PLAN<br />
Figure A-7 shows risk management integrated into an MTP task.<br />
The example portrays a possible method for integrating the risk<br />
management process and products into MTPs. The text in bold italics<br />
indicates suggested areas in which to integrate risk management.<br />
TASK C2 THE BATTALION (7-1-1901)(FM 7-20)<br />
ITERATION: 1 2 3 4 5 (circle)<br />
TRAINING STATUS: T P U (circle)<br />
CONDITION: The brigade issues an OPORD or FRAGO<br />
TASK STANDARD :<br />
a. The battalion plan accomplishes the directed mission and<br />
specified tasks according to the brigade commander’s<br />
concept and intent. The plan is received and understood<br />
by the leadership of the battalion, who makes the plan<br />
successful. It is coordinated with higher, adjacent, and<br />
supporting elements.<br />
b. The plan is as fully prepared as time allows to initiate the<br />
mission at the directed time.<br />
c. The battalion controls and synchronizes subordinate and<br />
supporting elements so that it accomplishes the mission and<br />
preserves the force. Include commander‘s risk guidance.<br />
d. The battalion keeps higher, adjacent, subordinate,<br />
supporting, and supported headquarters informed of<br />
essential information key to controlling the battle or<br />
making required decisions.<br />
I<br />
SUBTASKS AND STANDARDS: GO NO-GO<br />
+l. Battalion leaders issue the warning order.<br />
a. A complete warning order is issued within 15 minutes of<br />
receipt of the brigade order.<br />
b. Warning order is received by all platoons within 45<br />
minutes of issuance of battalion warning order.<br />
+ Critical task.<br />
* Leader task.<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
Appendix-1 1<br />
I
~~ ~<br />
<strong>Risk</strong> <strong>Management</strong><br />
*2. Battalion commander analyzes mission and gives<br />
initial guidance.<br />
a. Guidance includes restated mission, which includes<br />
brigade commander’s intent for battalion and identifies all<br />
specified and implied tasks.<br />
b. Guidance is given within 30 minutes of receipt of order.<br />
c. Guidance includes instructions on information<br />
requirements and initially required preparation actions<br />
(movement, resupply) to start. Guidance includes chain of<br />
command authorized to accept risk (extremely high, high,<br />
moderate, and low) aflecting higher command’s intent,<br />
resources, or adjacent units’ missions.<br />
+3. Battalion accomplishes reconnaissance and other<br />
actions to gather needed information.<br />
a. Reconnaissance actions begin to physically gain<br />
information on the enemy and terrain as early as possible.<br />
b. Commander conducts a personal reconnaissance, when<br />
possible. If not, the commander conducts a detailed map<br />
reconnaissance.<br />
c. Subordinate leaders perform a personal reconnaissance<br />
when possible. See subordinate company (ARTEP 7-10-<br />
MTP) and platoon (ARTEP 7-8-MTP) T&EOs.<br />
d. Staff coordinates with subordinate, higher, supporting,<br />
and adjacent headquarters to gather information for<br />
planning. Stag analyzes mission to identify hazards.<br />
e. Staff provides operations, intelligence, and CSS estimates<br />
to include all critical METT-T factors and risk assessment<br />
r<br />
considerations (identified hazardslrisks).<br />
+4. Battalion commander develops and wargames<br />
courses of action and selects one.<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
Appendix-I 2
~<br />
FM 100-14<br />
a. Tactically feasible courses of action (include CS and<br />
maneuver) are made and wargamed with the available<br />
staff (commander, S3, and FSO are best for quick planning<br />
sequences; XO, S2, engineer, S4, s 3 ( Safe ADA officer<br />
are best in more deliberate situations). Each course of<br />
action contains assessment of hazards, risk level, and<br />
control measures identifed to lower or control the risk.<br />
b. Best COA is selected.<br />
c. COA is wargamed and refined by the command and staff.<br />
The staff must understand the concept to produce a sound<br />
OPORD and rehearse. The stafcontinually assesses the<br />
situation to identify new hazards, assess the risk from<br />
each hazard, develop acceptable control measures, and<br />
reassess for residual risk to the mission. COA should pose<br />
minimum risk to soldiers, equipment, and mission<br />
accomplishment. <strong>Risk</strong> acceptance decisions for the COA<br />
are made at the appropriate level in the chain of command.<br />
*5. Staff develops an OPLAN and OPORD from the<br />
commander’s guidance.<br />
*6. Battalion commander and staff issue implementing<br />
FRAGOS (accident risk controls) .<br />
-<br />
1 *7. Battalion commander issues the OPORD/FRAGO. I<br />
a. OPORD/FRAGO is issued IAW the one-third, two-thirds<br />
rule and makes full use of daylight time.<br />
b. OPORD/FRAGO accomplishes all directed missions and<br />
tasks, complies with the brigade commander’s intent,<br />
controls r&&is,doctrinally sound. It is based on<br />
evaluator judgment and on comparison of brigade and<br />
battalion OPORDs.<br />
-~ ~<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
Appendix-1 3
<strong>Risk</strong> <strong>Management</strong><br />
c. All subordinate and supporting elements receive the<br />
OPORD/ FRAGO.<br />
d. OPORD/FRAGO contains task organization, mission,<br />
concept, accident risk controls, intent for maneuver,<br />
supporting fires, and obstacles; missions and tasks for each<br />
subordinate; fire support and CSS instructions; and<br />
coordinating instructions to synchronize the efforts of<br />
maneuver forces and CS.<br />
e. If more time is available, the battalion commander issues a<br />
fully developed OPORD (although an initial FRAGO may<br />
be issued to allow subordinates to begin preparation and<br />
followed by a full OPORD.)<br />
f. Order is given at a location that reduces travel time, allows<br />
observation of the zone/sector, and promotes OPSEC.<br />
(Depending upon the METT-T factors, observation of the<br />
zone/sector may not be possible.)<br />
g. Battalion commander should perform brief-backs and war<br />
gaming, to include identifying hazards and control<br />
measures, immediately after the order to improve<br />
subordinate understanding and reaction.<br />
h. Subordinate leaders and staff should perform lateral<br />
coordination before leaving the orders site.<br />
+8. Commander and staff coordinate and refine the plan.<br />
a. Time is well used to continue gathering information and to<br />
improve the plan (contingency plans, hazard identification<br />
and controls, fire plans) .<br />
b. New information is disseminated and coordinated with<br />
higher, adjacent, and supporting headquarters to include-<br />
Changes or refinements in plan.<br />
Information on the enemy in the sector or zone.<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
Appendix-I 4
FM 100-14<br />
Information that impacts on planning and execution<br />
(risk acceptance decisionslhazard controls) of<br />
subordinate elements.<br />
Adjustments/changes in the plans.<br />
1<br />
+*9. Battalion executes changes in task organization.<br />
a. Main CP coordinates link-up location, time, and<br />
responsible element.<br />
b. Attachments/new elements are received at the<br />
coordinated location and time; updated on current<br />
situation, OPORDs, and SOIs; and resupplied.<br />
c. Detachments reach the link-up point at the time and place<br />
direct e d .<br />
+*lo. Battalion performs and commander and staff<br />
perform, supervise, and monitor preparations.<br />
a. Command group/XO performs brief-backs with<br />
subordinate commanders, leaders, and key staff.<br />
b. Main CP maintains status of preparations.<br />
c. Elements make full use of time to prepare for the<br />
operation. Subjective judgment of the evaluator is<br />
based on the analysis of preparation charts and<br />
available preparation time.<br />
1 +*<strong>11</strong>. Battalion sees the battlefield. I<br />
a. Command group is positioned to see and move.<br />
b. Companies and other subordinates accurately report<br />
critical information on actions and changes in combat<br />
status within five minutes. See subordinate MTPs.<br />
c. Main CP collects, analyzes, and passes processed critical<br />
information.<br />
d. Subordinates execute intelligence collection plan. See<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
Appendix-I 5
<strong>Risk</strong> <strong>Management</strong><br />
subordinate element MTPs. Subordinates integrate the<br />
risk management process when developing plans and<br />
executing tasks.<br />
+*12. Battalion leaders command and control the<br />
execution .<br />
a. Subordinate elements report enemy and friendly actions,<br />
change in status, and any other factor that would require<br />
change within three minutes.<br />
b. Battalion leaders win the battle by directing the maneuver<br />
of units, controlling direct and indirect fires, properly<br />
integrating risk management into planning, preparation,<br />
and execution, and directing other CS actions to cope with<br />
new METT-T/risk factors. Indicators are:<br />
(1) Elements not following OPLAN and OPORD<br />
are corrected.<br />
(2) Responses to new METT-T hazards are directed<br />
soon after the new situation occurs.<br />
(3) No friendly casualties inflicted by friendly direct<br />
or indirect fires or other accidents.<br />
(4) Number/percentage of direct fire weapons<br />
engaging the enemy.<br />
(5) Number/percentage of indirect fire rounds fired<br />
and percentage hitting/suppressing the enemy.<br />
(6) Number of enemy casualties.<br />
(7) Number of friendly casualties.<br />
c. The C2 and CSS assets are controlled to support maneuver<br />
effort. Indicators are-<br />
(1) Effective CSS and C2.<br />
(2) C2 or CSS elements not destroyed by enemy<br />
direct fires.<br />
d. FRAGOs are clear, concise, incZude risk management, and<br />
are quickly executed by subordinates.<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
Appendix-1 6
~~~~ ~ ~<br />
~~<br />
~~~~~<br />
FM 100-14<br />
e. Changes that affect the battle are disseminated within<br />
five minutes.<br />
I<br />
+13. Subordinate commanders, leaders, and staff<br />
laterally coordinate actions during the battle.<br />
All battle actions requiring coordination between elements<br />
are coordinated.<br />
+*14. Battalion coordinates with adjacent and<br />
supporting headquarters.<br />
All battle actions requiring coordination with other<br />
headquarters are laterally and promptly coordinated.<br />
I<br />
+*15. Battalion reports.<br />
Battalion CPs submit all critical and required reports to<br />
brigade. They report events to adjacent and supporting<br />
elements that impact on them in time for those units to react.<br />
They advise the chain of command, as appropriate, on risks<br />
and risk-reduction measures.<br />
Figure A-7. Integration of <strong>Risk</strong> <strong>Management</strong> into MTP Task<br />
(continued)<br />
I<br />
Appendix-I7
Glossary<br />
AAR<br />
ADA<br />
ARFOR<br />
ARTEP<br />
assessment<br />
base operations<br />
support<br />
BASOPS<br />
C2<br />
COA<br />
Cof s<br />
combat power<br />
controls<br />
CP<br />
css<br />
CTC<br />
after-action review<br />
air defense artillery<br />
army forces headquarters<br />
Army Training and Evaluation Program<br />
an analytical process to determine an<br />
organization’s current levels of proficiency<br />
on a specific objective (for example, a training<br />
objective or risk management<br />
implementation) (CJCSM 3500.03)<br />
the provision of administrative and logistical<br />
services; includes supply operations,<br />
maintenance of materiel, personnel support,<br />
base services and administrative services<br />
rendered by or through activities of the<br />
supporting installation<br />
base operations support<br />
command and control<br />
course of action<br />
chief of staff<br />
the total means of destructive and/or<br />
disruptive force that a military unit or<br />
formation can apply against an opponent at a<br />
given time; a combination of the effects of<br />
maneuver, firepower, protection, and<br />
leadership<br />
actions taken to eliminate hazards or reduce<br />
their risk<br />
command post<br />
combat service support<br />
combat training center<br />
Glossary-0
FM 100-14<br />
danger<br />
EAC<br />
evaluation<br />
exposure<br />
FM<br />
FRAGO<br />
fratricide<br />
friction<br />
FSO<br />
G3<br />
hazard<br />
inherently<br />
dangerous<br />
IPB<br />
IR<br />
exposure or vulnerability to harm or risk; the<br />
balance between the chance or probability of<br />
a hazardous incident and the result of the<br />
hazardous incident<br />
echelons above corps<br />
the process used to measure the<br />
demonstrated ability to accomplish specified<br />
objectives such as training within a discrete<br />
event or exercise (CJCSM 3500.03);<br />
measurement of the demonstrated ability of<br />
soldiers or units to perform a task and<br />
supporting skill and knowledge or learning<br />
objective against the established standard<br />
the frequency and length of time personnel<br />
and equipment are subjected to a hazard<br />
field manual<br />
fragmentary order<br />
the employment of friendly weapons and<br />
munitions with the intent to kill the enemy or<br />
destroy his equipment or facilities, which<br />
results in unforeseen and unintentional death<br />
or injury to friendly personnel<br />
the accumulation of chance errors,<br />
unexpected difficulties, enemy actions, and<br />
confusion of battle<br />
fire support officer<br />
general staff operations section<br />
any actual or potential condition that can<br />
cause injury, illness, or death of personnel,<br />
damage to or loss of equipment, property or<br />
mission degradation (FM 101-5); a condition<br />
or activity with potential to cause damage,<br />
loss or mission degradation (Joint Pub 1-02)<br />
an activity or task containing a danger to life<br />
or limb that is a permanent and inseparable<br />
element of the activity<br />
intelligence-preparation-of-the-battlefield<br />
infrared<br />
Glossary-I
~ ~~<br />
<strong>Risk</strong> <strong>Management</strong><br />
LOA<br />
LOGCAP<br />
METL<br />
METT-T<br />
MOS<br />
MTP<br />
NBC<br />
NVD<br />
OCOKA<br />
OPCON<br />
operational tempo<br />
OPLAN<br />
OPORD<br />
OPTEMPO<br />
personnel tempo<br />
PERSTEMPO<br />
PIR<br />
probability<br />
PVO<br />
residual risk<br />
risk<br />
limit of advance<br />
Logistics Civil Augmentation Program<br />
mission-essential task list<br />
mission, enemy terrain, troops, and time<br />
available<br />
military occupational specialty<br />
mission training plan<br />
nuclear, biological, chemical<br />
night vision device<br />
0 - observation and fields of fire, C - cover<br />
and concealment, 0 - obstacles, K - key<br />
terrain and decisive terrain, A - avenues of<br />
approach<br />
operational control<br />
the pace of an operation or operations;<br />
OPTEMPO includes all of the activities the<br />
unit is conducting; OPTEMPO can be a single<br />
activity or a series of operations<br />
operations plan<br />
operations order<br />
operational tempo<br />
unit work load level and number of deployed<br />
days per year<br />
personnel tempo<br />
priority intelligence requirements<br />
the likelihood that a hazardous incident will<br />
occur<br />
private voluntary organization<br />
the level of risk remaining after controls have<br />
been identified and selected for hazards that<br />
may result in loss of combat power<br />
chance of hazard or bad consequences; the<br />
probability of exposure to chance of injury or<br />
loss from a hazard; risk level is expressed in<br />
terms of hazard probability and severity<br />
(FM 101-5)<br />
Glossary-2
FM 100-1 4<br />
risk assessment<br />
risk decision<br />
risk management<br />
risk management<br />
integration<br />
s3<br />
severity<br />
situational<br />
awareness<br />
SOP<br />
T&EO<br />
TACSOP<br />
TC<br />
TF<br />
us<br />
xo<br />
identification and assessment of hazards<br />
(first two steps of risk management process);<br />
an identified hazard is assessed to determine<br />
the risk (both the probability of occurrence<br />
and resulting severity) of a hazardous<br />
incident due to the presence of the hazard<br />
the decision to accept or not accept the risks<br />
associated with an action; made by the<br />
commander, leader, or individual responsible<br />
for performing that action<br />
the process of identifying, assessing, and<br />
controlling risks arising from operational<br />
factors and making decisions that balance<br />
risk cost with mission benefits<br />
the embedding of risk management<br />
principles and practices into Army<br />
operations, culture, organizations, systems,<br />
and individual behavior<br />
operations officer<br />
the expected consequence of an event<br />
(hazardous incident) in terms of degree of<br />
injury, property damage, or other missionimpairing<br />
factors (loss of combat power and<br />
so on) that could occur<br />
ability to have accurate and real-time<br />
information on friendly, enemy neutral, and<br />
noncombatant locations; a common, relevant<br />
picture of the battlefield scaled to specific<br />
level of interest and special need<br />
standing operating procedure<br />
test and evaluation outline<br />
tactical standing operating procedure<br />
training circular<br />
task force<br />
United States<br />
executive officer<br />
Glossary-3
References<br />
SOURCES USED<br />
FM 20-400. Military Environmental Protection. 1997 (draft).<br />
FM 22-9. Soldier Performance in Continuous Operations.<br />
12 December 1991.<br />
FM 22-100. Army Leadership. 1997 (draft).<br />
FM 25-100. Training the Force. 15 November 1988.<br />
FM 25-101. Battle-Focused Training. 30 <strong>September</strong> 1990.<br />
FM 34-60. Counterintelligence. 5 February 1990.<br />
FM 34-130. Intelligence Prqaration of the Battlefield. 23 May 1989.<br />
FM 100-5. Operations. August 1997 (draft).<br />
FM 100-40. Tactics. 29 October 1997 (draft).<br />
FM 100-7. Decisive Force: The Army in Theater Operations. 31 May 1995.<br />
FM 101-5. Staff Organization and Operations. 31 May 1997.<br />
READINGS RECOMMENDED<br />
Army Regulation 70-1. Systems Acquisition Policy and Procedures. 1997.<br />
Army Regulation 385-16. System Safety Engineering and <strong>Management</strong>.<br />
3 May 1990.<br />
CSA Statement on <strong>Risk</strong> <strong>Management</strong>. 27 July 1995.<br />
HQDA Letter 5-97-1. <strong>Risk</strong> <strong>Management</strong> Integration Responsibilities.<br />
1 May 1997.<br />
MIL-STD-882C. System Safety Program Requirements. 19 January 1993.<br />
”<strong>Risk</strong> <strong>Management</strong> for Brigades and Battalions.” Center for Army<br />
Lessons Learned (CALL) Newsletter 95-9. June 1995.<br />
References-0
Index<br />
A<br />
accident risks 2-2, 2-4, 2-1 1, 3-1<br />
adversaries 2-7<br />
after-action reviews 3-1 0<br />
ambiguity 1-2<br />
antiterrorism 3-1 0<br />
assessment 3-9<br />
avenues of approach 2-5<br />
avoidance controls.<br />
See controls, types of<br />
awareness. See situational<br />
awareness<br />
B<br />
battlefield controls. See controls<br />
C<br />
chain of command 3-2<br />
civilians 2-1, 2-7<br />
climate 2-6<br />
COA<br />
analysis 2-3, 2-7<br />
development 2-3, 2-7, 2-8<br />
enemy 2-4<br />
evaluation 1-3<br />
combat operations ii<br />
combat power ii, iii, 1-1, 2-2,2-6,<br />
2-12, 2-13<br />
conserving 2-0<br />
critical 2-1 3<br />
enemy deployment of 2-5<br />
friendly 2-5<br />
IOSS of 2-9<br />
command climate 3-2<br />
commander<br />
and identification of METL<br />
2-19<br />
and the risk management<br />
process 2-19<br />
responsibilities of iv, 2-3,<br />
2-16, 3-2-3-5<br />
commander’s guidance 2-16,3-2,<br />
3-4<br />
complacency 3-3<br />
constraints 1-7<br />
contract support personnel 2-1<br />
control measures. See controls<br />
controls iv, 1-3, 1-7,2-3, 2-7<br />
acceptability of 2-14<br />
alternate 2-16<br />
approval of 1-3<br />
battlefield 2-15<br />
conversion of 2-17<br />
coordination and<br />
communication 2-17<br />
criteria for (Fig 2-6) 2-14<br />
development of 2-0, 2-13,<br />
2-14, 3-4<br />
effectiveness of 2-2,2-19<br />
emplacement of 2-18<br />
enforcement of 2-18<br />
examples of 2-15-2-1 6<br />
execution of 2-17, 3-1, 3-5<br />
feasibility of 2-14<br />
implementation of 2-0, 2-14,<br />
2-17, 2-18<br />
ineffective 2-19, 2-21<br />
integration into OPORDs 1-3<br />
modification of 2-18<br />
monitoring of 2-18<br />
Index-1
<strong>Risk</strong> <strong>Management</strong><br />
reassessment of 2-1 6<br />
and residual risk 2-1 6<br />
and risk decision 2-1 6<br />
safety and environmental 1-6<br />
suitabiity of 2-1 4<br />
and tools for development<br />
2-19<br />
types of 2-14<br />
counterinsurgency operations 2-6<br />
counterintelligence 2-4.<br />
See also intelligence<br />
courses of action. See COA<br />
cover and concealment 2-5<br />
D<br />
danger, sources of 1-2, 2-3, 3-3<br />
decision levels 1-3<br />
decisive terrain 2-5.<br />
See also terrain<br />
degree of severity.<br />
See severity, degree of<br />
discipline 2-1 8<br />
E<br />
educational controls.<br />
See types of controls<br />
enemy, as part of METT-T 2-3.<br />
See also combat power<br />
environment<br />
damage to 1-2<br />
impact on 2-7<br />
evaluation 3-9<br />
evaluation, of risk management<br />
process 2-18<br />
examples of risk management<br />
work sheets<br />
for battalionhask force<br />
(Fig A-5) Appendix-5-7<br />
for company/team<br />
(Fig A-4) Appendix-4<br />
for division/corps/EAC<br />
(Fig A-6) Appendix-8-1 0<br />
for squad/platoon<br />
(Fig A-3) Appendix-3<br />
exposure to hazards 2-2, 2-7,<br />
2-15<br />
F<br />
fatigue 1-2, 2-6<br />
fear 1-2, 3-3<br />
foreign nationals 2-7<br />
fragmentary order. See FRAGO<br />
FRAGO 2-3<br />
fratricide 1-2, 2-15, 3-4<br />
friction 1 -2, 3-3<br />
friendly fire. See fratricide<br />
friendly vulnerabilities 2-4<br />
geographical area,<br />
acclimatization to 2-6<br />
H<br />
hazard, definition of 2-2<br />
hazards iii, iv, 3-1, 3-6<br />
and accident risks 2-2<br />
assessment of 2-7, 3-10<br />
and common shortfalls 2-4<br />
control of 3-4<br />
heat and cold 2-5<br />
identifying and controlling<br />
2-0, 2-2, 2-3, 3-6, 3-9<br />
long-term 2-18<br />
outside of assigned<br />
responsibilities 3-4<br />
review of 3-10<br />
and tactical risk 2-2<br />
variable 2-18, 3-1<br />
health considerations 2-6<br />
hostile elements. See adversaries<br />
Index-2
FM 100-14<br />
implementation of controls 2-1 7<br />
incident, credibility of 2-7<br />
I<br />
individuals, responsibilities of 3-7<br />
inexperience 2-6<br />
infrastructures, collecting<br />
information on 2-4<br />
instructions for work sheet<br />
Appendix-1<br />
insurgency operations 2-6<br />
integration of risk management<br />
into MTP task (Fig A-7)<br />
Appendix-1 1-1 7<br />
intelligence. See<br />
also counterintelligence<br />
collection plan Appendix-I 5<br />
dissemination of 2-4<br />
estimates Appendix-1 2<br />
and identification of hazards<br />
2-4<br />
intelligence-preparation-of-thebattlefield.<br />
See IPB<br />
IPB 2-4<br />
K<br />
key terrain 2-5. See also terrain<br />
knowledge, lack of 2-6<br />
L<br />
leaders. See also supervisors<br />
and assessment of hazards<br />
2-8<br />
and avoidance 2-14<br />
and continuous planning<br />
2-18<br />
and development of controls<br />
2-13<br />
and discipline 2-18<br />
and estimated degree of<br />
severity 2-<strong>11</strong><br />
and evaluation of risk<br />
management process<br />
2-18, 2-19<br />
and implementation of<br />
controls 2-17<br />
and METT-T 2-3<br />
and mission analysis 2-3<br />
and mission preparation 2-17<br />
and mission rehearsal and<br />
execution 2-18<br />
and modification of controls<br />
2-18<br />
and moral and ethical<br />
implications 3-0<br />
and overlap tours 2-16<br />
and overwatch of controls<br />
2-18<br />
responsibilities of iii, 2-1,2-2,<br />
2-3, 3-5<br />
and risk assessment 2-16<br />
and situational awareness<br />
2-18<br />
and time available 2-6<br />
and tools to assess identified<br />
hazards 2-19<br />
and troops 2-6<br />
and weather 2-5<br />
as supervisors 2-17<br />
unit 2-3<br />
leadership 2-6, 2-14, 3-2<br />
lessons learned 2-10, 3-10<br />
levels of risk 2-<strong>11</strong>, (Fig 2-5) 2-12,<br />
2-13<br />
extremely high 2-12<br />
high 2-12<br />
low 2-13<br />
moderate 2-12<br />
LOGCAP 2-17, 3-8<br />
Logistics Civil Augmentation<br />
Program. See LOGCAP<br />
losses 1 -2. See also fratricide<br />
Index-3
<strong>Risk</strong> <strong>Management</strong><br />
manning levels 2-6<br />
matrix. See risk assessment<br />
matrix<br />
media, hazards to 2-7<br />
METL 3-9<br />
and degree of related risk<br />
2-19<br />
identification of 2-19<br />
-related missions 2-6<br />
MET-T 1-6, 2-0,2-3,2-12,2-21,<br />
3-2<br />
military decision-making process<br />
2-O(Fig 2-I), 2-1, 2-3, 2-7, 2-13<br />
minimizing risk 3-1<br />
mission<br />
analysis 2-3, 2-7<br />
failure, causes of 2-6<br />
as part of MET-T 2-3<br />
receipt of 2-3<br />
mission, enemy, terrain, troops,<br />
and time available.<br />
See METT-T<br />
mission training plan. See MTP<br />
missions, long-term 2-6<br />
morale 2-6<br />
moral and ethical implications<br />
3-0-3-1<br />
MTP<br />
integrating risk management<br />
into Appendix-1 1<br />
and risk management<br />
considerations 2-19<br />
multidiscipline counterintelligence<br />
analysis 2-4<br />
N<br />
nation building 2-6<br />
NGOs 2-7, 2-17, 3-8<br />
nongovernmental organizations.<br />
See NGOs<br />
observation and fields of fire,<br />
cover and concealment,<br />
obstacles, key terrain and<br />
decisive terrain, and avenues of<br />
approach. See OCOKA<br />
OCOKA 2-5<br />
one-third/two-thirds rule 2-6<br />
operating environment 1-2, 1-3<br />
operational deployment 3-1<br />
operational hazards 1-2<br />
operational tempo.<br />
See OPTEMPO<br />
OPLANs 1-3, 3-10<br />
OPORDs 3-10<br />
OPTEMPO 1-3, 3-3<br />
overall risk 2-7, 2-10<br />
overlap tours 2-16<br />
overwatch of controls 2-18<br />
peacekeeping 2-6<br />
peacetime environment 2-7<br />
perception, and leaders’<br />
decisions 1-1<br />
personnel tempo.<br />
See PERSTEMPO<br />
personnel turnover 2-6<br />
PERSTEMPO 1-3<br />
physical controls.<br />
See types of controls<br />
pitfalls of risk management 2-1 9<br />
planning time 2-6<br />
private voluntary organizations.<br />
See PVOs<br />
probability 1-1, 2-7, 2-8, 2-10,<br />
2-<strong>11</strong>, 2-12, 2-13, 2-15, 2-16,<br />
2-19, 3-10<br />
degrees of 2-8<br />
frequent 2-8, 2-12<br />
Index-4
FM 100-14<br />
of hazards (Fig 2-2) 2-8, 2-9<br />
levels 2-8<br />
likely 2-1 2, 2-1 3<br />
occasional 2-1 2<br />
seldom 2-12, 2-13<br />
unlikely 2-1 2, 2-1 3<br />
proficiency 1-1<br />
PVOS 2-7, 2-1 7, 3-8<br />
R<br />
readiness 3-1 0<br />
reconnaissance activities 2-4<br />
residual risk 1-3,2-14,2-16,2-19,<br />
2-21, 3-6<br />
definition of 2-16<br />
tactical 3-4<br />
resources ii, iii, 1-1<br />
resources, conservation of iii<br />
responsibilities of commanders,<br />
leaders, staffs, and individuals<br />
3- 1 -3-7<br />
risk<br />
definition of 1-1, 2-7<br />
estimate of 2-7<br />
levels of 2-10<br />
perception of 1-1<br />
risk assessment 2-2,2-4, 2-7,<br />
2-1 1, 2-19, 2-21, 3-6<br />
card 2-21, 3-2<br />
matrix (Fig 2-4) 2-1 1, 2-1 6<br />
process 3-8<br />
tools 3-2<br />
risk controls. See controls<br />
risk decision iv, 1-3, 2-0, 2-1,<br />
2-1 3,2-16,2-19,2-21,3-2,3-3,<br />
3-4, 3-5<br />
risk denial syndrome 3-2<br />
risk levels. See risk, levels of<br />
risk management 1-1, 1-7, 2-1 6,<br />
3-4, 3-5, 3-6<br />
applicability 1-4 - 1-6<br />
background of 1-1-1 -2<br />
and the chain of command<br />
3-0<br />
continuous application of<br />
(Fig 2-7) 2-20<br />
examples of application,<br />
Appendix-1 -Appendix-1 2<br />
fundamentals 1-2-1 -7<br />
implementation of 3-0-3-1 0<br />
integrating into planning,<br />
preparation, and execution<br />
iii, 1-3<br />
key aspects of 1-4<br />
principles of 1-3<br />
and regulatory and legal<br />
requirements 1-7<br />
risk management process ii, 1-1,<br />
1-3, 2-0-2-21, 3-1, 3-2, 3-5<br />
assessment of 3-9-3-1 0<br />
and constraints 1-7<br />
continuous application of<br />
2-19<br />
the five steps 2-0<br />
introduction of iii<br />
risk management steps<br />
2-1 (Fig 2-1), 2-2<br />
risk management work sheet<br />
instructions<br />
(Fig A-1) Appendix-1<br />
risk reduction controls 3-6<br />
safety programs 3-1 0<br />
sample risk management work<br />
sheet (Fig A-2) Appendix-2<br />
severity 1-1, 2-7, 2-9, 2-1 0, 2-1 1,<br />
2-15, 2-16, 2-19, 3-10<br />
catastrophic 2-9, 2-1 0<br />
critical 2-1 0<br />
degree of 2-9<br />
of hazards (Fig 2-3) 2-1 0<br />
Index-5
<strong>Risk</strong> <strong>Management</strong><br />
marginal 2-10<br />
negligible 2-10<br />
situational awareness iii, 2-2,<br />
2-18, 2-19, 3-3, 3-7, 3-9<br />
soldiers, health of 2-6<br />
soldiers’ responsibilities. See<br />
individuals, responsibilities of<br />
SOPS 3-10<br />
stability operations 2-6, 2-18<br />
staffs, responsibiity of 2-<strong>11</strong>, 3-6<br />
steps, of the risk management<br />
process<br />
Step 1. Identify Hazards<br />
2-2-2-7<br />
Step 2. Assess Hazards<br />
2-7-2-1 3<br />
Step 3. Develop Controls and<br />
Make <strong>Risk</strong> Decisions<br />
2-13-2-1 6<br />
Step 4. Implement Controls<br />
2-17<br />
Step 5. Supervise and<br />
Evaluate 2-17-2-1 9<br />
supervise and evaluate.<br />
See steps, of the risk<br />
management process<br />
supervision techniques 2-18<br />
supervisors, and examples of<br />
control implementation 2-17<br />
supplies and services 2-6<br />
sustained operations 2-18, 3-3<br />
tactical risk 2-2, 2-4, 2-1 1, 3-1<br />
task organization 2-6<br />
terrain 2-5.<br />
See also key terrain<br />
terrain and weather 2-4<br />
aspects of 2-5<br />
as part of METT-T 2-4<br />
threat capabilities and<br />
vulnerabilities 2-4<br />
time available, as part of METT-T<br />
2-6<br />
tools<br />
to assess identified hazards<br />
2-19<br />
for risk management 2-19<br />
tracking Appendix-1<br />
training 3-1<br />
assessment 3-9<br />
levels of 2-6<br />
plan 3-10<br />
training management cycle 3-9<br />
training and operations,<br />
integration into 3-7-3-9<br />
troops, care of 2-6<br />
uncertainty 1-2, 2-1 1<br />
v<br />
vehicles, maintenance of 2-6<br />
violence, and risk decisions 3-3<br />
wartime environment 2-7<br />
weather hazards, identification of<br />
2-5<br />
work sheet instructions<br />
(Fig A-1) Appendix-1<br />
Index-6
The Tool To Protect The Force, Family and<br />
Friends
“<strong>Risk</strong> management is the Army’s principal<br />
risk-reduction process to protect the force.<br />
Our goal is to make risk management a<br />
routine part of planning and executing<br />
operational missions.”<br />
Chief of Staff, Army<br />
L<br />
Protect the Force
What the Chief Didn’t Say<br />
<strong>Risk</strong> mangement is optional.<br />
<strong>Risk</strong> management is a safety officer<br />
function.<br />
<strong>Risk</strong> management is for leaders only.<br />
3
<strong>Risk</strong> <strong>Management</strong> Terms<br />
<strong>Risk</strong> <strong>Management</strong> - The process of identifling and<br />
controlling hazards to protect the force.<br />
4<br />
Hazard - Any real or potential condition that can cause injury,<br />
illness, . . death,<br />
4 damage<br />
4 ..<br />
to or loss of equipment or property, or<br />
mission degradation.<br />
or<br />
Any adverse condition of a METT-T factor that, if not<br />
controlled, can cause loss of combat power from accidents or<br />
enemy action.<br />
<strong>Risk</strong><br />
-?<br />
Chance of hazard or bad consequences; exposure to<br />
chance of injury or loss. Expressed in terms of hazard<br />
probability and severity.<br />
Protect the Force
f<br />
<strong>Risk</strong> <strong>Management</strong> Terms<br />
<strong>Risk</strong> Assessment - the identification and assessment of<br />
hazards (first two steps of the <strong>Risk</strong> <strong>Management</strong><br />
process).<br />
<strong>Risk</strong> level - expressed in terms of hazard probability<br />
and severity.<br />
Probability - the likelihood an event will occur.<br />
Severity - the expected consequence of an event in terms of<br />
degree of injury, lost resources, or other mission impairing<br />
factors that could occur.<br />
5<br />
Controls - actions taken to eliminate hazards or reduce their<br />
risks.<br />
Protect the Force -
Residual <strong>Risk</strong> - the level of risk remaining after<br />
controls have been identified and selected.<br />
<strong>Risk</strong> Decision - The decision to accept or not<br />
accept the risks associated with an action made by<br />
the commander, leader, or individual responsible<br />
for performing that action.<br />
6<br />
Protect the Force
I<br />
I B<br />
Rules of <strong>Risk</strong> <strong>Management</strong><br />
Integrate into danning;.<br />
U I U<br />
Accept no unnecessary risks.<br />
Make risk decisions at the proper level.<br />
Accept risk if the benefits outweigh the<br />
potential losses.<br />
I<br />
Protect the Force
I<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
8<br />
1<br />
Protect the Force
I<br />
Hazard Identification<br />
<strong>11</strong><br />
Look for things that can keep you from reaching<br />
the objective without all of your combat<br />
power.<br />
II<br />
Hazard factors - Operational, environmental,<br />
situational/scenario .<br />
Consider all aspects of current and future<br />
situations, and known historical problem<br />
areas.<br />
1<br />
Protect the Force<br />
9
Most Likely Hazards<br />
~ d<br />
OBJECTIVE - Identify those hazards most likely to<br />
result in loss of combat power.<br />
CRITERIA- Hazard is not adequately controlled at this<br />
For echelon or next lower echelon.<br />
“Most Likelv<br />
Hazard”<br />
-AND-<br />
Include control(s) for hazard in FRAGO<br />
OPORD, mission instructions or verbal<br />
order.<br />
10<br />
Track hazard via risk management work<br />
sheet.<br />
Protect the Force =
9<br />
ID HAZARDS<br />
Q- Is hazard adequately controlled?<br />
I<br />
Identified<br />
METT-%<br />
hazard<br />
-Support - Is type/amount/capability/condition of suppoi<br />
8% adequate to control hazard?<br />
- Personnel - Equipment/material<br />
- Supplies - Services/facilities<br />
-Standards - Is guidance/procedure adequately clear/<br />
8% mactical/sPecific to control hazard?<br />
- Training - Is training adequately thorough and recent<br />
18% to control hazard?<br />
- Leader - Are leaders ready, willing and able to enforce<br />
18% standards required to control hazard?<br />
Adequate<br />
YES NO<br />
Individual - Is soldier performance and conduct sufficieni<br />
48% self-disciplined to control hazard?<br />
Y<br />
<strong>11</strong><br />
A - If all “yes”, no further action.<br />
- If one or more “no”. risk manage th is hazard.<br />
Protect the Force
Identify hazards during<br />
JReceive The Mission<br />
JIssue The Warning Order<br />
JMake A Tentative Plan<br />
I1<br />
12<br />
Protect the Force
( Hazards )<br />
-3<br />
13<br />
5<br />
Protect the Force
-.---<br />
Assess Hazards<br />
Don’t get wound up in a matrix.<br />
More art than science (use experience).<br />
Tailor to the operation and level involved.<br />
Think of cumulative effects and critical path.<br />
Assess hazards based on probability, severity<br />
and mission impact.<br />
14<br />
Protect the Force =
I<br />
THE ARMY RISK ASSESSMENT MATRIX. ..<br />
<strong>Risk</strong> Level:<br />
E - Extremely High<br />
H - High<br />
M - Moderate<br />
L -Low<br />
S<br />
e<br />
V<br />
e<br />
r<br />
i<br />
t<br />
Y<br />
Catastrophic<br />
Critical<br />
Marginal<br />
Negligible<br />
I<br />
I Frequent<br />
HAZARD PROBABILITY<br />
Likely Occasional Seldom ~<br />
Unlikely<br />
E E H H M<br />
E H H M L<br />
H M M L L<br />
M L L L L<br />
15<br />
..I One<br />
size fits all?<br />
Protect the Force
Unit:<br />
Operation:<br />
<strong>Risk</strong> <strong>Management</strong> Worksheet<br />
16<br />
Protect the Force =
RISK MANAGEMENT<br />
IDENTIFY AND ASSESS MISSION RISKS AND HAZARDS<br />
I MISSION PLANNING<br />
I<br />
TERRAIN<br />
TRAFFICABI LITY<br />
I MISSION I PREPARATORY TIME<br />
DURATION<br />
r m K S<br />
24-48 HOURS<br />
< 24 HOURS<br />
IN DEPTH ADEQUATE MINIMAL<br />
3 4 5<br />
2 3 4<br />
1 2 4<br />
TYPE<br />
MOUNTAIN/<br />
DESERT<br />
HILLS<br />
FLATROLLING<br />
I MISSION CONTROL EQUIPMENT<br />
I<br />
AGE<br />
OLD<br />
AVERAGE<br />
NEW<br />
I<br />
IMPROVED TRAILS CROSS COUNTRJ<br />
3 4 5<br />
2 3 4<br />
1 3 4<br />
EQUIPMENT STATUS<br />
MAINTENANCE STATUS<br />
MLY MISSION<br />
CWABLE<br />
I<br />
I NTmME;IN<br />
3 4 5<br />
2 4 5<br />
1 3 5<br />
I<br />
SOLDIER SELECTION<br />
I WEATHER & ENVIRONMENTAL CONDITIONS<br />
TEMP<br />
DAY LIMITED VISIBILITY/ NIGHTDUSTEOG<br />
CLEMRY HAZYDRIZZLE SNOWiMUDiICERAIN<br />
TASK<br />
HIGHLY<br />
EXPERIENCED MOS QUALIFIED UNTRAINED<br />
80<br />
3 4 5<br />
COMPLEX<br />
32-59<br />
2 3 4<br />
I<br />
ROUTINE<br />
SIMPLE<br />
OPERATING<br />
ENVIRONMENT<br />
NON ACCLIMATED<br />
PARTIALLY<br />
ACCLIMATED<br />
SOLDIER ALERTNESS<br />
OPTIMUM<br />
> 8 HOURS<br />
4<br />
3<br />
ADEQUATE<br />
4-8HOURS<br />
MINIMAL<br />
< 4 HOURS<br />
4 5<br />
3 4<br />
60-79<br />
1 2 4<br />
DEVELOP AND IMPLEMENT RISK REDUCTION ACTIONS.<br />
ALL RISK GREATER THAN 4 REQUIRE IMMEDIATE ACTION.<br />
WHEN TWO OR MORE AREAS ARE ASSIGNED A RISK<br />
FACTOR OF 5, THE OVERALL RATING SCHEME IS EXTREMELY HIGH.<br />
ACCLIMATED<br />
1<br />
2 4<br />
YOU ARE CHALLENGED TO MAKE PRUDENT RISK DECISIONS.<br />
ACCEPT RISKS WHEN THE BENEFITS OUTWEIGH THE COST.<br />
DON’T ACCEPT UNNECESSARY RISKS!
Assess Hazards<br />
Assess hazards during<br />
71 Situation Estimate<br />
J Detailed Mission Analysis<br />
JDeveloping Situation and COA<br />
71 Analyzing COA<br />
19<br />
Protect the Force
1<br />
<strong>Risk</strong> ~ 1<br />
<strong>Management</strong> <strong>Process</strong><br />
( )-( t:.:zs Decisions lMake<br />
><br />
20<br />
Protect the Force
1<br />
I iDevelop Controls and Make <strong>Risk</strong><br />
For Each Hazard<br />
Decision<br />
71 Implement existing controls if adequate<br />
71 If not, adjust to make adequate or develop new<br />
71 Consider realism and resources<br />
71 Minimize chance of accidents, maximize mission<br />
accomplishment<br />
Determine residual risk and appropriate<br />
commander acceptshejects risk<br />
21<br />
Protect the Force
1Develop Controls and Make <strong>Risk</strong><br />
Decision<br />
Do this during<br />
71 Comparing COA<br />
JMaking Decisions<br />
JExpanding selected COA into a tentative plan<br />
22<br />
Protect the Force
I<br />
d<br />
I <strong>Risk</strong> 9<br />
<strong>Management</strong> <strong>Process</strong><br />
Identify<br />
Hazards<br />
Implemen<br />
Controls<br />
I<br />
23<br />
Protect the Force
Implement Controls<br />
Controls are the standard.<br />
Include in OPORDs, FRAGOs, rehearsals.<br />
Link to specific hazards.<br />
Communicate to your soldiers.<br />
SOPS and training to standard are some of the<br />
most common sources of controls.<br />
24<br />
Protect the Force
Implent Controls During<br />
J Initiating Movement<br />
J Reconnoitering<br />
3 Completing The Plan<br />
JIssueing The Order
j<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
><br />
26<br />
Protect the Force
Enforce standards.<br />
Deconflict controls.<br />
Plan!<br />
C<br />
Evaluate controls and adjusthpdate as<br />
nece s sary .<br />
Incorporate lessons learned for fitture<br />
use.<br />
Do this during supervise and refine the<br />
plan.<br />
21 Protect the Force
~ enforcement<br />
-1<br />
Put your greatest emphasis in hazard<br />
identification and development and<br />
of controls.<br />
The higher the risk, the more senior the decision maker.<br />
Continually assess risk and adjust controls.<br />
Be careful “averaging out” risk.<br />
28<br />
Protect the Force
RISK MANAGEMENT WORKSHEET PAGF 1 nf 3<br />
4. PREPAREDBY:<br />
/ /<br />
5. HAZARDS<br />
Inexperienced<br />
untrained soldiers<br />
- Air Loading<br />
- Rail Loading<br />
- Hazardous Cargo<br />
- New Equipment<br />
Continuous operations<br />
during loading<br />
Lack of / improper<br />
ground guiding<br />
H<br />
-<br />
H<br />
9. OVERALL RISK LEVEL AFTER CONTROLS ARE Ik<br />
ID soldiers with<br />
deployment experience<br />
and assigned to load<br />
teams.<br />
Train Airloadmail<br />
teams.<br />
Train drivers on new<br />
equipment<br />
Develop rest plans/<br />
shift schedules<br />
Train driverdground<br />
guides in correct<br />
procedures.(Hand&Arm)<br />
,EMENTED (CIRCLE ONE):<br />
LOW ~DERATI~J HIGH EXTREMELY HIGH<br />
I<br />
10. RI<br />
RSOP/<br />
Training<br />
guidance<br />
RSOP/<br />
TACSOP<br />
OPORD<br />
RSOP/<br />
Training<br />
guidance<br />
ON AUTHORITY:<br />
12. HOWTO<br />
LEAD<br />
spot<br />
check<br />
by BCs<br />
Cont. supv<br />
by Plt Sgt<br />
Cont. supv<br />
spot<br />
check<br />
by 1SGs<br />
Section<br />
Chiefs<br />
COLONEL BATTISTEBDE CDR<br />
RANWLASTNAMEIDUTY POSITION<br />
TSP-29
I FY ~<br />
96 STATS<br />
FA Soldiers killed: 25<br />
FA Soldiers killed off-duty: 23<br />
FA Soldiers killed in POVs: 21<br />
Total Soldiers killed in POVs: 130<br />
FA % of POV deaths: 16%<br />
30<br />
FA % ofArrny: 6%<br />
Protect the Force
The Tool To Protect The Force, Family and<br />
Friends<br />
I 1<br />
Protect the Force -<br />
“<strong>Risk</strong> management is the Army’s principal<br />
risk-reduction process to protect the force.<br />
Our goal is to make risk management a<br />
routine part of planning and executing<br />
operational missions.”<br />
Chief of Staff, Army<br />
It<br />
Protect the Force -
-<br />
1 What the Chief Didn't Say<br />
'<br />
1<br />
<strong>Risk</strong> mangement is optional.<br />
<strong>Risk</strong> management is a safety officer<br />
hnct ion.<br />
<strong>Risk</strong> management is for leaders only.<br />
Protect the Force<br />
i<br />
<strong>Risk</strong> <strong>Management</strong> Terms<br />
<strong>Risk</strong> <strong>Management</strong> - The process of identifying and<br />
controlling hazards to protect the force.<br />
Hazard - Any real or potential condition that can cause injury,<br />
illness, death, damage to or loss of equipment or property, or<br />
mission degradation.<br />
or<br />
Any adverse condition of a METT-T factor that, if not<br />
controlled, can cause loss of combat power from accidents or<br />
enemy action.<br />
<strong>Risk</strong> - Chance of hazard or bad consequences; exposure to<br />
chance of injury or loss. Expressed in terms of hazard<br />
probability and severity.<br />
Protect the Force -
<strong>Risk</strong> <strong>Management</strong> Terms<br />
<strong>Risk</strong> Assessment - the identification and assessment of<br />
hazards (first two steps of the <strong>Risk</strong> <strong>Management</strong><br />
process).<br />
<strong>Risk</strong> level - expressed in terms of hazard probability<br />
and severity.<br />
Probability - the likelihood an event will occur.<br />
Severity - the expected consequence of an event in terms of<br />
degree of injury, lost resources, or other mission impairing<br />
factors that could occur.<br />
Controls - actions taken to eliminate hazards or reduce their<br />
risks.<br />
I . Protect the Force -<br />
I<br />
<strong>Risk</strong> <strong>Management</strong> Terms<br />
Residual <strong>Risk</strong> - the level of risk remaining after<br />
controls have been identified and selected.<br />
<strong>Risk</strong> Decision - The decision to accept or not<br />
accept the risks associated with an action made by<br />
the commander, leader, or individual responsible<br />
for performing that action.<br />
I<br />
Protect the Force
Integrate into planning.<br />
Accept no unnecessary risks.<br />
Make risk decisions at the proper level.<br />
Accept risk if the benefits outweigh the<br />
potential losses.<br />
I<br />
Protect the Force I<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
I Protect the Force -
Hazard Identification<br />
Look for things that can keep you from reaching<br />
the objective without all of your combat<br />
power.<br />
Hazard factors - Operational, environmental,<br />
situational/scenario.<br />
Consider all aspects of current and future<br />
situations, and known historical problem<br />
areas.<br />
Protect the Force -<br />
Most Likely Hazards<br />
OBJECTIVE - IdentifL those hazards most likely to<br />
result in loss of combat power.<br />
CRITERIA- Hazard is not adequately controlled at this<br />
For echelon or next lower echelon.<br />
“Most Likelv<br />
Hazard ”<br />
-AND-<br />
- Include control(s) for hazard in FRAGO<br />
OPORD, mission instructions or verbal<br />
order.<br />
- Track hazard via risk management work<br />
sheet.<br />
10 Protect the Force -
Adeauate<br />
Q- Is hazard adeauatelv controlled? YES NO<br />
Identified<br />
METT-T<br />
hazard<br />
-Support - Is type/amount/capability/condition of support<br />
8% adequate to control hazard?<br />
- Personnel Equipmenvmaterial<br />
- Supplies - Services/facilities<br />
-Standards - Is guidance/procedure adequately clear/<br />
8% practical/specific to control hazard?<br />
- Training - Is training adequately thorough and recent<br />
18% to control hazard?<br />
- Leader - Are leaders ready, willing and able to enforce<br />
18% standards required to control hazard?<br />
Individual - Is soldier performance and conduct sufficien<br />
48% self-disciulined to control hazard?<br />
I I<br />
A - If all “yes”, no further action.<br />
1f-e // no ,> . v d .<br />
.<br />
Protect the Force -<br />
Hazard Identification<br />
IdentifL hazards during<br />
ZReceive The Mission<br />
YIssue The Warning Order<br />
71Make A Tentative Plan<br />
Protect the Force -
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
3<br />
Protect the Force -<br />
j<br />
Assess Hazards<br />
Don’t get wound up in a matrix.<br />
More art than science (use experience).<br />
Tailor to the operation and level involved.<br />
Think of cumulative effects and critical path.<br />
Assess hazards based on probability, severity<br />
and mission impact.<br />
14<br />
Protect the Force -
THE ARMY RISK ASSESSMENT MATRIX. ..<br />
<strong>Risk</strong> Level:<br />
E - Extremely High<br />
H - High<br />
M - Moderate<br />
L - Low<br />
-<br />
S<br />
e<br />
V<br />
e<br />
r<br />
i<br />
t<br />
- Y<br />
Catastrophic<br />
Critical<br />
Marginal<br />
Negligible<br />
HAZARD PROBABILITY<br />
Frequent Likely Occasional Seldom Unlikely<br />
E E H H M<br />
E H H M L<br />
H M M L L<br />
M L L L L<br />
J<br />
... One size fits all?<br />
Protect the Force -<br />
I Unit:<br />
Operation:<br />
<strong>Risk</strong> <strong>Management</strong> Worksheet<br />
16<br />
Protect the Force -
Protect the Force -<br />
MISSION<br />
MISSION PLANNING<br />
PREPARATORY TIME<br />
n PE<br />
TERRAIN<br />
rnCABILrn<br />
I<br />
I<br />
I<br />
1 WEATHER 81 ENVIRONMENTAL CONDITIONS 1<br />
II SOLDIER ALERTNESS I<br />
DLVUaP .AND IMPLEMEVT PJSK REDUXIOK ACTIONS<br />
ALL RISK GREATER THAN4 REWIRE IMMEDIATE ACTION<br />
U~YTWOORhlOREIUIEr~~~,G~~DARlSK<br />
FACTOR OF I. THE OI'ERALL RATING SCHEME IS WREMELY HIGH.<br />
YOU ARE CHALLEhGED TO MAKE PRUDEM RISK DECISIONS.<br />
ACCEPTRISKS U'HENTHEBEUEmSOL~EIGHTHECOST.
i<br />
I<br />
Assess Hazards<br />
Assess hazards during<br />
71 Situation Estimate<br />
71Detailed Mission Analysis<br />
JDeveloping Situation and COA<br />
71Analyzing COA<br />
I<br />
I9 Protect the Force -<br />
in Protect the Force -
Develop Controls and Make <strong>Risk</strong><br />
Decision<br />
For Each Hazard<br />
71 Implement existing controls if adequate<br />
71 If not, adjust to make adequate or develop new<br />
71 Consider realism and resources<br />
71 Minimize chance of accidents, maximize mission<br />
accomplishment<br />
Determine residual risk and appropriate<br />
commander acceptshejects risk<br />
Protect the Force -<br />
I<br />
,Develop Controls and Make <strong>Risk</strong><br />
!<br />
Decision<br />
Do this during<br />
acornparing COA<br />
2Making Decisions<br />
71Expanding selected COA into a tentative plan<br />
Protect the Force -
I<br />
1 <strong>Risk</strong><br />
<strong>Management</strong> <strong>Process</strong><br />
( Assess ) ( Make )<br />
Hazards<br />
Decisions<br />
Protect the Force -<br />
I<br />
Implement Controls<br />
Controls are the standard.<br />
Include in OPORDs, FRAGOs, rehearsals.<br />
Link to specific hazards.<br />
Communicate to your soldiers.<br />
Avoid the big<br />
hand-wave<br />
SOPS and training to standard are some of the<br />
most common sources of controls.<br />
I 24<br />
Protect the Force -
~ Protect<br />
Implement Controls<br />
Implent Controls During<br />
71Initiating Movement<br />
71Reconnoitering<br />
71Completing The Plan<br />
71Issueing The Order<br />
Protect the Force -<br />
I) 3<br />
Hazards<br />
-<br />
Decisions<br />
the Force J
Lead and Evaluate<br />
Enforce standards.<br />
Deconflict controls.<br />
Evaluate controls and adjusthpdate as<br />
necessary.<br />
Incorporate lessons learned for hture<br />
use.<br />
Do this during supervise and refine the<br />
plan.<br />
Protect the Force -<br />
Put your greatest emphasis in hazard<br />
identification and development and<br />
enforcement of controls.<br />
The higher the risk, the more senior the decision maker.<br />
Continually assess risk and adjust controls.<br />
Be careful "averaging out'' risk.<br />
Use the process creatively.<br />
Protect the Force -
RISK MANAGEMENT WORKSHEET DACC I "r 1<br />
I MSNirASK Deploy he 2ND Bnmde Combat Tram 2 MG BEGIN 10FJIB97 3 DATE<br />
END 6MAR97 PRPARED2UNOV96 1<br />
4 PWARU)BY CPT AMERICA ASSISTANT S-3.2ND BCT<br />
RANK2ASTU4UEmVIY WSnlON<br />
L H*Z\RDS<br />
Inexperienced/<br />
untrained soldiers<br />
- Air Loading<br />
- Rail Loading<br />
- Hazardous Cargo<br />
New Equipment<br />
Continuous operations<br />
during loading<br />
Lack of / improper<br />
ground guiding<br />
H ID soldiers with L<br />
deployment experience<br />
and assigned to load<br />
teams.<br />
Train AirloadRail<br />
teams.<br />
Train drivers on new<br />
equipment<br />
H Develop rest plans/<br />
shift schedules<br />
H Train driverslground M<br />
guides in correct<br />
procedures.(Hand&Arm)<br />
IRE hlPLEMENTED(CRCLE0NE) I 10 AlsRbEE<br />
RSOPI<br />
Training<br />
guidance<br />
RSOP/<br />
TACSOP<br />
OPORD<br />
RSOPl<br />
Training<br />
guidance<br />
,I. now TO<br />
LEAD<br />
Spot<br />
check<br />
by BCs<br />
Cont. sup<br />
by Plt Sg<br />
Cont. sup<br />
Spot<br />
check<br />
by lSGs<br />
Section<br />
Chiefs<br />
-<br />
I LOW HIGH EXTREMELY HIGH I BATTIST"BDE CDR<br />
RNWLASTNAMEIDUN wsinoN --<br />
FA Soldiers killed: 25<br />
FA Soldiers killed off-duty: 23<br />
FA Soldiers killed in POVs: 21<br />
Total Soldiers killed in POVs: 130<br />
FA % of POV deaths: 16%<br />
FA % of Army: 6%<br />
Protect the Force -
RISK<br />
<strong>Risk</strong> <strong>Management</strong>, when properly<br />
applied, enables a commander to<br />
maximize oDerational capabilities while<br />
minimizing risk to the force.<br />
Clvll 6 criminal<br />
llabilwles \<br />
Environmental<br />
degradation *<br />
<strong>Risk</strong>s Threaten the Force<br />
and Its Capabilities<br />
Fratricide 4 L<br />
Loss of public 9<br />
trust 6<br />
confldence<br />
Loss &theft of<br />
++- materiel &funds<br />
Accidental destructlon<br />
of materiei/facllitles<br />
Thase risks can h. minimized if they an effectively detected and controlled -<br />
<strong>Risk</strong> Manraement<br />
I<br />
1<br />
I
The Dimensions of <strong>Risk</strong><br />
I The relative Mission Fiscal<br />
Safety<br />
Personal<br />
Legamedia Environmental<br />
1 Changing - - one element often influences<br />
other elements positively or negatively<br />
What Price are we Paying<br />
Wow?<br />
Historically<br />
aoa-threat losses<br />
Desert Shield<br />
Storm<br />
Hostile fire ............ 2.9 (20Y0)<br />
Accidents .......... <strong>11</strong>.14 (75%)!<br />
Fratricide ............. .68 (5%)<br />
27 -Trucks<br />
450 tow of 8mmunilmkI<br />
The non-threat losses<br />
can be cut 50-100%<br />
2<br />
2
I Whoisthe I<br />
REAL<br />
threat?? I<br />
What’s New About <strong>Risk</strong><br />
<strong>Management</strong>?<br />
Hasn’t risk always been managed?<br />
Yes, but:<br />
Not systematically and consistently<br />
Not with tested and proven methods<br />
Not on a totally integrated basis<br />
Not as a tool for expanding capabilities<br />
The procedures for risk management offer<br />
breakthrough improvements in<br />
warfighting effectiveness and force protecfion.<br />
<strong>Risk</strong> <strong>Management</strong> Philosophy<br />
<strong>Risk</strong> management is the best process for the<br />
protecting the force. <strong>Risk</strong> management provides a<br />
systematic and lmical aaaroach to identifvinp and<br />
controlline hazards that endanger our resources.<br />
<strong>Risk</strong> management supports and encourages<br />
initiative allowine flexibilitv. adaatabilitv and<br />
eaeerness to act. ... it applies to all elements of force<br />
protection in all situations and environments.<br />
I<br />
I<br />
3<br />
3
+Hazard - any real or Dotential condition that can<br />
cause iniurv, illness or death of personnel, or damage<br />
to, or loss of equipment or property, or mission<br />
degradation.<br />
+<strong>Risk</strong> - chance of hazard or bad consequences;<br />
exposure to chance of injury or loss.<br />
Key Definitions<br />
+<strong>Risk</strong> level is expressed in terms of hazard<br />
probability and severity.<br />
- Severity - exDected conseauenw of an event in term:<br />
of degree of injury, property damage, or other missior<br />
impairing factors (loss of combat power, adverse<br />
publicity, etc.) that could occur.<br />
- Probability - likelihood that an event will occur.<br />
Key Definitions<br />
+ <strong>Risk</strong> <strong>Management</strong> (RM) - the process of identifying<br />
and controlling hazards to protect the force.<br />
- Its five steps represent a logical thought process from<br />
which users develop toois, techniques, and<br />
procedures for applying risk management in their<br />
areas of responsibility.<br />
- It is a continuous process applicable to any situation<br />
and environment.<br />
+ <strong>Risk</strong> Assessment -the first two steps of the RM<br />
process.<br />
4<br />
4
Key Definitions<br />
+Controls - actions taken to eliminate<br />
hazards or reduce their risk@).<br />
<strong>Risk</strong> Decision - the decision to acceDt or<br />
not acceDt the risks associated with an<br />
action made by the individual responsible<br />
for performing that action.<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ Identify Hazards. Identify hazards to the force. Consider all<br />
aspects of current and future situations, environment, and<br />
known historical problem areas.<br />
5<br />
5
+ Assess Hazards. Assess hazards to determine risks.<br />
Assess the impact of each hazard in terms of potential<br />
loss and cost, based on probability and severity.<br />
control measures that eliminate the hazard or reduce its risk.<br />
As control measures are developed, risks are reevaluated until<br />
all risks are reduced to a level where benefits outweigh<br />
I<br />
+ Implement Controls. Put controls in place that<br />
eliminate the hazards or reduce their risks.<br />
.Examples:<br />
+Plana, OPORDs,<br />
SOPS, Tnlning<br />
Performance<br />
Standards,<br />
Reheanals.<br />
6<br />
6
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ Supervise & Evaluate. Enforce standards and<br />
controls. Evaluate the effectiveness of controls and<br />
adjusthpdate as necessary.<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ A risk assessment matrix can be used to determine<br />
risk levels of an identified hazard. Standard terms<br />
associated with risk assessment:<br />
- Probability -the likelihood that an event will occur.<br />
- Severity -the expected consequence of an event in<br />
terms of degree of injury, property damage, or other<br />
mission impairing factors (loss of combat power,<br />
adverse publicity, etc), that could occur.<br />
<strong>Risk</strong> Assessment Matrix<br />
7<br />
7
<strong>Risk</strong> <strong>Management</strong> Tools<br />
Readiness <strong>Risk</strong> <strong>Management</strong><br />
+Key risk issues for the unit have been<br />
identified. Effective indicators of risk status<br />
exist in these areas.<br />
+Leaders assess soldier risk proneness<br />
factors 8 use leadership skills to reduce<br />
risks.<br />
+Important risk skills 8 knowledge’s have<br />
been identified 8 the unit scores high on<br />
tests of factors.<br />
8<br />
8
~<br />
Readiness Rlsk <strong>Management</strong> Iconl'dl<br />
+All leaders have been trained on RM<br />
responsibilities 8 skills. All can apply RM to<br />
unit operations<br />
+METL-based tasks have been assessed for risk<br />
& effective risk controls are in place.<br />
+Each soldier can name the 5 leading sources of<br />
injury for their MOS &job and the key risk<br />
controls.<br />
+New o<br />
& risk<br />
I<br />
Applications of <strong>Risk</strong> <strong>Management</strong><br />
To perform optimally, unit leaders must be able<br />
to detect and control risks in specific missions<br />
assigned to the unit within operational<br />
resources and time constraints.<br />
Control Option Matrix<br />
Control Option<br />
Engineer<br />
+ Guard<br />
Limit exposure<br />
Pcnonnel sekclioa<br />
Train & educate<br />
Warn<br />
Molivste<br />
Reduceeffects<br />
+ Rehabilitate<br />
ndividual Supervisor<br />
I<br />
'ommander<br />
9<br />
9
Applications of <strong>Risk</strong> <strong>Management</strong><br />
Safety restnctions often stifle audacity in training and actual war<br />
Opportunity-risk concept have a proven capability to detect thse bzers They also<br />
provlde the means to elminate or modify counterproductive safety resmctinns and<br />
override the risk associated wth audacity<br />
><br />
Decisive Victq<br />
&<br />
-Initiative<br />
increased losses<br />
Traditional process vs. RM process<br />
Traditional approach<br />
- "Common Sense".<br />
- Random hazard ID and<br />
assessment.<br />
- More omission.<br />
- Uninformed decision.<br />
- Reactiveldownstream<br />
oriented.<br />
- Compliance based.<br />
<strong>Risk</strong> <strong>Management</strong><br />
- Methodical.<br />
- Less omission.<br />
- Informed decision.<br />
- Upstream process<br />
oriented.<br />
- Involvement and<br />
empowerment.<br />
10<br />
IO
~~<br />
What are the Potentlal<br />
Benefits?<br />
I<br />
Promotes audacity thru prudent rrsh laking<br />
+ Improved abdity . to .. proiect force with minimal .<br />
losser<br />
+ Enhanms decision-making skills<br />
Improved congressional & media confidence in<br />
force<br />
+ Improves soldier confidence in unit capabilities<br />
lN COMBAT<br />
The Bottom Line<br />
Commanders can cut accidental losses in<br />
training and combat by 50-90%. At the same<br />
time, training realism can be substantially<br />
enhanced and operational capabilities<br />
significantly and continuously improved.<br />
The Four Rules of<br />
<strong>Risk</strong> <strong>Management</strong><br />
+ lntearate risk management into operational<br />
planning.<br />
+Accept no unnecessary risks.<br />
+Make risk decisions at the proDer level.<br />
+Accept risks if the benefits outweighs the<br />
cost.<br />
<strong>11</strong><br />
<strong>11</strong>
“Don’t never take a<br />
chance you don’t have<br />
to.”<br />
Standing Orders<br />
Rogers’ Rangers 1759<br />
12<br />
12
RISK<br />
<strong>Risk</strong> <strong>Management</strong>, when properly<br />
applied, enables a commander to<br />
maximize ODerational CaDabilities while<br />
minimizing risk to the force.<br />
Civil 6 criminal<br />
<strong>Risk</strong>s Threaten the Force<br />
and Its Capabilities<br />
'dental deaths 6 Injuries<br />
Environmental<br />
degradation *<br />
Diseases 6 illnesses<br />
Loss 6 theft of<br />
-Fratricide d I 4 k materiel 6 funds<br />
Loss of ubiic<br />
ttusP6<br />
confidence<br />
Accidental destruction<br />
of materiel/facllities<br />
These risks can be minimized if they are effectively detected and controlled -<br />
<strong>Risk</strong> Manapemmnt<br />
1<br />
I
The Dimensions of <strong>Risk</strong><br />
I The relative Mission Fiscal I<br />
significance of<br />
Of<br />
risk varies<br />
from<br />
operation to<br />
operation<br />
Train j<br />
I Changing - - one element often influences<br />
other elements positively or negatively<br />
I<br />
I<br />
I -<br />
Historically<br />
non-threat losses<br />
What Price are We Paying<br />
WOW<br />
Desert Shield<br />
Storm<br />
Hostile tire ............ 2.9 (20%)<br />
I nL<br />
The Doha Catastrophe<br />
450 tom of .amunition<br />
Accidents .......... <strong>11</strong>.14 (%YO)!<br />
Fratricide ............. .68 (5%)<br />
The non-threat losses<br />
can be cut 50-100%<br />
I<br />
I<br />
2<br />
2
Who is the<br />
REAL<br />
threat ??<br />
What’s New About <strong>Risk</strong><br />
<strong>Management</strong>?<br />
Hasn’t risk always been managed?<br />
Yes, but:<br />
Not systematically and consistently<br />
Not with tested and proven methods<br />
- Not on a totally integrated basis<br />
* Not as a tool for expanding capabilities<br />
The procedures for risk management offer<br />
breakthrough improvements in<br />
warfighting effectiveness and force protection.<br />
<strong>Risk</strong> Marauement Philosouhy<br />
<strong>Risk</strong> management is the best process for the<br />
protecting the force. <strong>Risk</strong> management provides a<br />
svstematic and loeical amroach to identifvinp and<br />
controlling hazards that endanger our resources.<br />
<strong>Risk</strong> management supports and encourages<br />
initiative allowing flexihilitv. adaptabilitv and<br />
eaeerness to act. ... it applies to all elements of force<br />
protection in all situations and environments.<br />
3<br />
3
Key Definitions<br />
+Hazard - any real or ootential condition that can<br />
cause iniuru, illness or death of personnel, or damage<br />
to, or loss of equipment or property, or mission<br />
degradation.<br />
+<strong>Risk</strong> - chance of hazard or bad consequences;<br />
exposure to chance of injury or loss.<br />
I<br />
I<br />
Key Definitions<br />
+<strong>Risk</strong> level is expressed in terms of hazard<br />
probabilitv and severity.<br />
- Severity - exDected mnseauence of an event in terms<br />
of degree of injury, property damage, or other mission<br />
impairing factors (loss of combat power, adverse<br />
publicity, etc.) that could occur.<br />
- Probability - likelihood that an event will occur.<br />
+ <strong>Risk</strong> <strong>Management</strong> (RM) -the process of identifying<br />
and controlling hazards to protect the force.<br />
- Its five steps represent a logical thought process from<br />
which users develop tools, techniques, and<br />
procedures for applying risk management in their<br />
areas of responsibility.<br />
- It is a continuous process applicable to any situation<br />
and environment.<br />
+ <strong>Risk</strong> Assessment - the first two steps of the RY<br />
process.<br />
4<br />
4
Key Definitions<br />
+Controls - actions taken to eliminate<br />
hazards or reduce their risk(s).<br />
+ <strong>Risk</strong> Decision - the decision to acceDt or<br />
not acceDt the risks associated with an<br />
action made by the individual responsible<br />
for performing that action.<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
Identify Hazards. Identify hazards to the force. Consider all<br />
aspects of current and future situations, environment, and<br />
known historical problem areas.<br />
5<br />
5
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ Assess Hazards. Assess hazards to determine risks.<br />
Assess the impact of each hazard in terms of potential<br />
loss and cost, based on probability and severity.<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
Develop Controls and Make <strong>Risk</strong> Decisions. Develop<br />
control measures that eliminate the hazard or reduce its risk.<br />
As control measures are developed, risks are reevaluated until<br />
all risks are reduced to a level where benefits outweigh<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
Implement Controls. Put controls in place that<br />
eliminate the hazards or reduce their risks.<br />
.Examples:<br />
*Plans, OPORDs<br />
SOPS, Training<br />
Performance<br />
Standards,<br />
Rehearsals.<br />
6<br />
6
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ Supervise & Evaluate. Enforce standards and<br />
controls. Evaluate the effectiveness of controls and<br />
adjusthpdate as necessary.<br />
<strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
+ A risk assessment matrix can be used to determine<br />
risk levels of an identified hazard. Standard terms<br />
associated with risk assessment:<br />
- Probabllity - the likelihood that an event will occur.<br />
- Severity - the expected consequence of an event in<br />
terms of degree of injury, property damage, or other<br />
mission impairing factors (loss of combat power,<br />
adverse publicity, etc), that could occur.<br />
<strong>Risk</strong> Assessment Matrix<br />
I<br />
7<br />
7
<strong>Risk</strong> <strong>Management</strong> Tools<br />
I<br />
Readiness <strong>Risk</strong> <strong>Management</strong><br />
+Key risk issues for the unit have been<br />
identified. Effective indicators of risk status<br />
exist in these areas.<br />
+Leaders assess soldier risk proneness<br />
factors & use leadership skills to reduce<br />
risks.<br />
+Important risk skills & knowledge’s have<br />
been identified & the unit scores high on<br />
tests of factors.<br />
8<br />
8
Readiness Rlsk <strong>Management</strong> Icomidl<br />
+All leaders have been trained on RM<br />
responsibilities 8 skills. All can apply RM to<br />
unit operations<br />
+METL-based tasks have been assessed for risk<br />
& effective risk controls are in place.<br />
+Each soldier can name the 5 leading sources of<br />
injury for their MOS &job and the key risk<br />
controls.<br />
+New operational capabilities are subjected to RM<br />
Applications of <strong>Risk</strong> <strong>Management</strong><br />
To perform optimally, unit leaders must be able<br />
to detect and control risks in specific missions<br />
assigned to the unit within operational<br />
resources and time constraints.<br />
Control Option Matrix<br />
Control Option<br />
Engineer<br />
Guard<br />
Limit exposure<br />
Personnel selection<br />
Train & educate<br />
Warn<br />
Motivate<br />
Reduceeffects<br />
+ Rehabilitate<br />
ndividual Supervisor :ommander<br />
9<br />
9
Applications of <strong>Risk</strong> <strong>Management</strong><br />
I override<br />
Safety rermctions often stifle audacity in training and actual war<br />
Opportunity-nsk concept have a proven capability to detect these bsen They also<br />
provide the means to eliminate or modify eaunterproducuve safety restrictions and<br />
the risks associated with audacity<br />
><br />
Decisive Victor).<br />
. Synchmnimtior<br />
- Flewbiht)<br />
-Initiative<br />
-Depth<br />
-Audacity<br />
nsks Do more w>t<br />
increased losses<br />
Traditional process vs. RM process<br />
- Random hazard ID and<br />
assessment.<br />
- More omission.<br />
+ <strong>Risk</strong> <strong>Management</strong><br />
- Methodical.<br />
- L~~~ omission.<br />
- Informed decision.<br />
- Upstream process<br />
- Uninformed decision. oriented.<br />
- Reactive/downstream - Involvement and<br />
empowerment.<br />
- Compliance based.<br />
10<br />
IO
What are the Potential<br />
Benefits9<br />
‘)i Non-battle casualties (non-hostile fire) reduced up<br />
to 5Q%<br />
+ Promotes audacity thru prudent risk taking<br />
+ Improved ability to project force wth minimal<br />
losses<br />
Enhances decision-making skills<br />
+ Improved congressional & media confidence tn the<br />
force<br />
+ Improves soldier confidence in unit capabilities<br />
J<br />
4EEE<br />
\<br />
MmA,N,NI<br />
IN COMBAT<br />
A POTENTIALLY DECISIVE EDGE!<br />
Commanders can cut accidental losses in<br />
training and combat by 50-90%. At the same<br />
time, training realism can be substantially<br />
enhanced and operational capabilities<br />
significantly and continuously improved.<br />
The Four Rules of<br />
<strong>Risk</strong> <strong>Management</strong><br />
4 lntearate risk management into operational<br />
4Accept no unnecessarv risks.<br />
4 Make risk decisions at the proDer level.<br />
+Accept risks if the benefits outweighs the<br />
cost.<br />
<strong>11</strong><br />
II
“Don’t never take a<br />
chance you don’t have<br />
to.”<br />
Standing Orders<br />
Rogers’ Rangers 1759<br />
12<br />
12
FM 3-100.12<br />
MCRP 5-12.lC<br />
NTTP 5-03.5<br />
AFTTP( I) 3-2.34<br />
FEBRUARY 2001<br />
DISTRIBUTION RESTRICTION:<br />
Approved for public release;<br />
distribution is unrestricted
FOREWORD<br />
This publication has been prepared under our direction for use by our respective<br />
commands and other commands as appropriate.<br />
A<br />
JOHN N. ABRAMS<br />
General, USA<br />
Commander<br />
Training and Doctrine Command<br />
BRUCE B. KNUTSON, JR.<br />
Lieutenant General, USMC<br />
Commanding General<br />
Marine Corps Combat<br />
Development Command<br />
ROBERT G. SPRIGG<br />
Rear Admiral, USN<br />
Commander<br />
Navy Warfare Development Command<br />
LANCE L. SMITH<br />
Major General, USAF<br />
Commander<br />
Headquarters Air Force Doctrine Center<br />
This publication is available on the General<br />
Dennis J. Reimer Training and Doctrine <strong>Digital</strong><br />
Library at www.adtdI .army. mil
1. Scope<br />
This publication describes risk management functions and responsibilities applicable to<br />
the joint task force (JTF) and service staffs. It applies risk management planning<br />
procedures to the military decision making process and employs the Joint Operation<br />
Planning and Execution System (JOPES) for the operation planning team.<br />
2. Purpose<br />
This publication provides a consolidated multiservice reference addressing risk<br />
management background, principles, and application procedures. To facilitate multiservice<br />
interoperability, this publication identifies and explains the risk management process and<br />
its differences and similarities as it is applied by each service.<br />
3. Applicability<br />
The audience for this publication includes combatant command, JTF, and functional<br />
and service component staffs. The target staff level is the JTF headquarters staff. This<br />
publication serves as a source document for developing service and joint manuals,<br />
publications, and curricula, and may be used as a stand-alone document.<br />
4. Implementation Plan<br />
Participating service command offices of primary responsibility will review this<br />
publication, validate the information, and reference and incorporate it in service and<br />
command manuals, regulations, instructions, and curricula as follows:<br />
Army. The Army will incorporate this publication in U.S. Army training and doctrinal<br />
publications as directed by the Commander, U.S. Army Training and Doctrine Command<br />
(TRADOC). Distribution is in accordance with DA Form 12-99-R.<br />
Marine Corps. The Marine Corps will incorporate the procedures in this publication in<br />
U.S. Marine Corps (USMC) training and doctrinal publications as directed by the<br />
Commanding General, U.S. Marine Corps Combat Development Command (MCCDC).<br />
Distribution is in accordance with Marine Corps Publication Distribution System (MCPDS) .<br />
Navy. The Navy will incorporate these procedures in U.S. Navy (USN) training and<br />
doctrinal publications as directed by the Commander, Navy Warfare Development<br />
Command (NWDC). Distribution is in accordance with Military Standard Requisitioning<br />
and Issue Procedures (MILSTRIP) Desk Guide and Navy Standing Operating Procedures<br />
(NAVSOP) Publication 409.<br />
Air Force. The Air Force will validate and incorporate appropriate procedures in<br />
accordance with applicable governing directives. Distribution is in accordance with Air Force<br />
Instruction 33-360, Volume 1.<br />
5. User Information<br />
a. The TRADOC-MCCDC-NWDC-Headquarters (HQ) Air Force Doctrine Center<br />
(AFDC) and Air Land Sea Application (ALSA) Center developed this publication with the<br />
joint participation of the approving service commands. ALSA will review and update this<br />
publication as necessary.<br />
b. This publication reflects current joint and service doctrine, command and control<br />
organizations, facilities, personnel, responsibilities, and procedures. Changes in service<br />
MARINE CORPS: PCN 14400009300<br />
I
protocol, appropriately reflected in joint and service publications, will be incorporated in<br />
revisions of this document.<br />
c. We encourage recommended changes for improving this publication. Key your<br />
comments to the specific page and paragraph and provide a rationale for each<br />
recommendation. Send comments and recommendations directly to-<br />
ii
FM 3-100.12<br />
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTP(I) 3-2.34<br />
FM 3-100.12<br />
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTP(I) 3-2.34<br />
U.S. Army Training and Doctrine Command<br />
Fort Monroe, Virginia<br />
Marine Corps Combat Development Command<br />
Quantico, Virginia<br />
Navy Warfare Development Command<br />
Newport, Rhode Island<br />
Headquarters Air Force Doctrine Center<br />
Maxwell Air Force Base, Alabama<br />
15 February 2001<br />
RISK MANAGEMENT<br />
Multiservice Tactics, Techniques, and Procedures for<br />
<strong>Risk</strong> <strong>Management</strong><br />
TABLE OF CONTENTS<br />
EXECUTIVE SUM MARY.. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .<br />
Chapter I RISK MANAGEMENT FUNDAMENTALS .........................................................<br />
Page<br />
1. Background ................................................................................................... 1-1<br />
2. <strong>Risk</strong> <strong>Management</strong> Goal ................................................................................. 1-1<br />
3. Key Aspects of <strong>Risk</strong> <strong>Management</strong> ................................................................. 1-1<br />
4. Principles of <strong>Risk</strong> <strong>Management</strong> .................................................................... 1-2<br />
5. Levels of <strong>Risk</strong> <strong>Management</strong> .......................................................................... 1-3<br />
6. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Overview ............................................................ 1-3<br />
7. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Application Guidelines. .. . . . . .. . . . .. . . . . . . . . . . . . . . . . . . . ... . . 1-3<br />
8. Relationship of Force Protection to <strong>Risk</strong> <strong>Management</strong>. .. . . . ... . . . .. . . . . .. . . . ... . . . .. . 1-5<br />
Chapter II RISK MANAGEMENT PROCESS AND OPERATIONAL<br />
CONSIDERATIONS .................................................................................................. <strong>11</strong>-1<br />
1. Background .................................................................................................. <strong>11</strong>-1<br />
2. Application of <strong>Risk</strong> <strong>Management</strong> .... ....... .... . ........ ..... ...... . .... . .... .................... <strong>11</strong>-1<br />
3. Integration of <strong>Risk</strong> <strong>Management</strong> ..................... ......................... ..... . ......... .... <strong>11</strong>-7<br />
4. Analysis Models.. ... ..... . .... ....... ..... . ...... .... .......... . .... . ..... .... ...... ......... . .... ..... .... <strong>11</strong>-8<br />
Chapter <strong>11</strong>1 STAFF FUNCTIONS AND RESPONSIBILITIES ............................................. <strong>11</strong>1-1<br />
1. Background ................................................................................................ <strong>11</strong>1-1<br />
2. Responsibilities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . <strong>11</strong>1- 1<br />
V<br />
1-1<br />
iii
3 . Integration into Training and Operations ................................................. <strong>11</strong>1-6<br />
4 . Review of the <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> .................................................. <strong>11</strong>1-6<br />
Appendix A <strong>Risk</strong> <strong>Management</strong> Tools .............................................................................. A-1<br />
Appendix 6 Force Protection Working Group ............................................................... B-1<br />
References ..........................................................................................................<br />
Glossary ..............................................................................................................<br />
References-1<br />
Glossary-1<br />
Index .................................................................................................................... Index- 1<br />
Figures 1.1 . Continuous Application of <strong>Risk</strong> <strong>Management</strong> ............................................ 1-4<br />
<strong>11</strong>- 1 . Identify the Threats .................................................................................. . II-1<br />
<strong>11</strong>.2 . Assess the Threat ....................................................................................... <strong>11</strong>-2<br />
<strong>11</strong>.3 . Develop Controls and Make <strong>Risk</strong> Decisions ............................................. , II-3<br />
<strong>11</strong>.4 . Implement Controls ................................................................................... <strong>11</strong>-5<br />
<strong>11</strong>.5 . Supervise and Review ................................................................................ <strong>11</strong>-6<br />
A.A.1 . Sample Completed <strong>Risk</strong> <strong>Management</strong> Worksheet ..............................<br />
A-A-1<br />
A-B-1<br />
A-D-1<br />
A-B- 1 . Sample Force Protection Priority Matrix ...........................................<br />
A.D.l . <strong>Risk</strong> Assessment Matrix .....................................................................<br />
A-E- 1 . Sample <strong>Risk</strong> Control Options Planning Matrix .................................. A. E.1<br />
B.1 . Potential Sources for the FPWG ................................................................ B-1<br />
B.2 . Example FPWG Meeting Agenda .............................................................. B-2<br />
B.3 . Sample <strong>Risk</strong> Considerations Matrix .......................................................... B-5<br />
Tables <strong>11</strong>.1 . Criteria for Effective Controls ................................................................... <strong>11</strong>-3<br />
<strong>11</strong>.2 . <strong>Risk</strong> <strong>Management</strong> Execution (<strong>Risk</strong> <strong>Management</strong> in Deliberate<br />
Planning) .................................................................................................. . II-7<br />
<strong>11</strong>.3 . <strong>Risk</strong> <strong>Management</strong> Execution (<strong>Risk</strong> <strong>Management</strong> in Crisis Action<br />
Planning) ................................................................................................... <strong>11</strong>.8<br />
<strong>11</strong>.4 . Considerations and Potential Threats Analyzed (Man Element,<br />
5-M Model) ............................................................................................... <strong>11</strong>- <strong>11</strong><br />
<strong>11</strong>.5 . Considerations and Potential Threats Analyzed (Machine Element,<br />
5-M Model) ............................................................................................... <strong>11</strong>- <strong>11</strong><br />
<strong>11</strong>.6 . Considerations and Potential Threats Analyzed (Media Element,<br />
5-M Model) ............................................................................................... <strong>11</strong>- 12<br />
<strong>11</strong>.7 . <strong>Management</strong> Tools and Examples Analyzed (<strong>Management</strong> Element.<br />
5-M Model) ............................................................................................... <strong>11</strong>-12<br />
A-C- 1 . Sample Force Protection Tasks. Conditions. Desired Effects. and<br />
Activities ...............................................................................................<br />
A-D- 1 . <strong>Risk</strong> Severity Categories ....................................................................<br />
A.D.2 . Probability Definitions .......................................................................<br />
A.E.1 . Examples of <strong>Risk</strong> Control Options ......................................................<br />
A-C-1<br />
A-D-2<br />
A-D-3<br />
A-E-2<br />
iv
This publication-<br />
<strong>Risk</strong> <strong>Management</strong><br />
Provides multiservice tactics, techniques, and procedures for tactical level<br />
risk management in the planning and execution of operations in a joint<br />
environment.<br />
Provides a basic risk management process that may be used by all services.<br />
Applies to all elements of a force that assists in planning and conducting<br />
force protection.<br />
0 Provides risk management tools for commanders and staffs to use to<br />
manage risk during planning, preparation, and execution of joint operations.<br />
Chapter I<br />
<strong>Risk</strong> <strong>Management</strong> Fundamentals<br />
Chapter I introduces risk management as a process to assist decision makers in<br />
reducing or offsetting risks. It identifies the goal, key aspects, and principle concepts of the<br />
process; provides general guidelines for applying the process: and gives an overview of the<br />
process:<br />
0<br />
Identifying threats.<br />
Assessing threats to determine risks.<br />
Developing controls and making risk decisions.<br />
0 Implementing controls.<br />
0 Supervising and reviewing.<br />
Chapter II<br />
Operational Considerations and Implementation<br />
Chapter I1 describes the actions involved in applying the risk management process:<br />
identifies pitfalls, types of controls, and feedback requirements; and integrates the risk<br />
management process into the planning process. This chapter describes how common<br />
situation analysis tools support the risk management process.<br />
Chapter <strong>11</strong>1<br />
Staff Functions and Responsibilities<br />
Chapter I<strong>11</strong> ties the risk management process to the chain of command and the staff<br />
directorates, and describes how leader involvement at all levels is necessary for the process<br />
to be effective. This chapter also describes the integration of the risk management process<br />
into all aspects of operations and training and illustrates how constant review of the<br />
process leads to improvement in the process.<br />
V
PROGRAM PARTICIPANTS<br />
The following commands and agencies participated in the development of this<br />
publication:<br />
Army<br />
HQ TRADOC (ATDO-A)& (ATBO-SO), Ingalls Rd Bldg 133 Room 7, Ft. Monroe,<br />
VA 23651-5000<br />
Combined Arms Center (CAC), Combined Arms Doctrine Directorate (CADD),<br />
Ft Leavenworth, KS<br />
OG-D, BCTP, Ft Leavenworth, KS<br />
CDR, XVIII Airborne Corps, Ft Bragg, NC<br />
Army Safety Center, Training Division, Ft Rucker, AL<br />
USAREUR, DCSPER, Unit 29351, APO AE, 09063<br />
Marine Corps<br />
Marine Corps Combat Development Command, Joint Doctrine Branch (C427) 3300 Russell<br />
Rd, 3rd Floor Suite 318A, Quantico, VA 22134-5021<br />
Marine Corps Combat Development Command, MSTP (C54) 2076 South Street,<br />
Quantico, VA 22134-5021<br />
Commandant of the Marine Corps (Code SD), 2 Navy Annex, Room, 33 17,<br />
Washington, DC 20380- 1775<br />
Navy<br />
OPNAV, N09K, 2000 Navy Pentagon 5E8 16, Washington, DC 20305-2000<br />
Commander, Navy Warfare Development Command/N5,686 Cushing Rd,<br />
Newport, RI 02841-1207<br />
Commander, Naval Safety Center, 375 A Street, Norfolk, VA 2351 1-4399<br />
COMPHIBGRU TWO, NAB Little Creek, Norfolk, VA 2352 1<br />
Air Force<br />
HQ Air Force Doctrine Center, 155 N Twining Street, Maxwell Air Force Base, AL 361 12<br />
AFDC Detachment 1, 216 Sweeny Bvld. Ste 109, Langley Air Force Base, VA 23665<br />
HQ USAF/SE, 9700 G Ave SE, Kirkland Air Force Base, NM 871 17-5670<br />
vi
1. Background<br />
Chapter I<br />
RISK MANAGEMENT FUNDAMENTALS<br />
<strong>Risk</strong> management is a process that assists decision makers in reducing or offsetting risk<br />
(by systematically identifying, assessing, and controlling risk arising from operational<br />
factors) and making decisions that weigh risks against mission benefits. <strong>Risk</strong> is an<br />
expression of a possible loss or negative mission impact stated in terms of probability and<br />
severity. The risk management process provides leaders and individuals a method to assist<br />
in identifying the optimum course of action (COA). <strong>Risk</strong> management must be fully<br />
integrated into planning, preparation, and execution. Commanders are responsible for the<br />
application of risk management in all military operations. <strong>Risk</strong> management facilitates the<br />
mitigation of the risks of threats to the force. For the purposes of this document, threat is<br />
defined as a source of danger-any opposing force, condition, source, or circumstance with<br />
the potential to negatively impact mission accomplishment and/or degrade mission<br />
capability.<br />
a. Each of the services uses similar but slightly different processes. This publication<br />
provides a single process to enable warfighters from different services to manage risk from<br />
a common perspective.<br />
b. <strong>Risk</strong> management is useful in developing, deploying, and employing the joint force.<br />
Development concerns force design, manpower allocation, training development, and<br />
combat material developments. Deploying and employing the joint force generates concerns<br />
in force protection and balancing risk against resource constraints.<br />
c. Military operations are inherently complex, dynamic, dangerous and, by nature,<br />
involve the acceptance of risk. Because risk is often related to gain, leaders weigh risk<br />
against the benefits to be gained from an operation. The commander's judgment balances<br />
the requirement for mission success with the inherent risks of military operations. Leaders<br />
have always practiced risk management in military decision making; however, the<br />
approach to risk management and degree of success vary widely depending on the leader's<br />
level of training and experience.<br />
d. Since the Korean conflict, United States forces have suffered more losses from noncombat<br />
causes than from enemy action. Key factors contributing to those losses include-<br />
(1) Rapidly changing operational environment.<br />
(2) Fast-paced, high operations tempo and high personnel tempo.<br />
(3) Equipment failure, support failure, and effects of the physical environment.<br />
(4) Human factors.<br />
2. <strong>Risk</strong> <strong>Management</strong> Goal<br />
The fundamental goal of risk management is to enhance operational capabilities and<br />
mission accomplishment, with minimal acceptable loss.<br />
3. Key Aspects of <strong>Risk</strong> <strong>Management</strong><br />
a. <strong>Risk</strong> management assists the commander or leader by-<br />
(1) Enhancing operational mission accomplishment.<br />
(2) Supporting well-informed decision making to implement a COA.<br />
(3) Providing assessment tools to support operations.<br />
1-1
(4) Enhancing decision-making skills based on a reasoned and repeatable process.<br />
(5) Providing improved confidence in unit capabilities. Adequate risk analysis<br />
provides a clearer picture of unit readiness.<br />
(6) Preserving and protecting personnel, combat weapon systems, and related<br />
support equipment while avoiding unnecessary risk.<br />
(7) Providing an adaptive process for continuous feedback through the planning,<br />
preparation, and execution phases of military operations.<br />
(8) Identifying feasible and effective control measures where specific standards do<br />
not exist.<br />
b. <strong>Risk</strong> <strong>Management</strong> does not-<br />
(1) Replace sound tactical decision making.<br />
(2) Inhibit the commander’s and leader’s flexibility, initiative, or accountability.<br />
(3) Remove risk altogether, or support a zero defect mindset.<br />
(4) Sanction or justify violating the law.<br />
(5) Remove the necessity for rehearsals, tactics, techniques, and procedures.<br />
4. Principles of <strong>Risk</strong> <strong>Management</strong><br />
The basic principles that provide a framework for implementing the risk management<br />
process include-<br />
a. Accept No Unnecessary <strong>Risk</strong>. An unnecessary risk is any risk that, if taken, will<br />
not contribute meaningfully to mission accomplishment or will needlessly endanger lives or<br />
resources. No one intentionally accepts unnecessary risks. The most logical choices for<br />
accomplishing a mission are those that meet all mission requirements while exposing<br />
personnel and resources to the lowest acceptable risk. All military operations and off-duty<br />
activities involve some risk. The risk management process identifies threats that might<br />
otherwise go unidentified and provides tools to reduce or offset risk. The corollary to this<br />
axiom is “accept necessary risk” required to successfully complete the mission or task.<br />
b. Make <strong>Risk</strong> Decisions at the Appropriate Level. Anyone can make a risk<br />
decision: however, the appropriate level for risk decisions is the one that can make<br />
decisions to eliminate or minimize the threat, implement controls to reduce the risk, or<br />
accept the risk. Commanders at all levels must ensure that subordinates know how much<br />
risk they can accept and when to elevate the decision to a higher level. Ensuring that risk<br />
decisions are made at the appropriate level will establish clear accountability. The risk<br />
management process must include those accountable for the mission. After the commander,<br />
leader, or individual responsible for executing the mission or task determines that controls<br />
available to them will not reduce risk to an acceptable level, they must elevate decisions to<br />
the next level in the chain of command.<br />
c. Accept <strong>Risk</strong> When Benefits Outweigh the Cost. The process of weighing risks<br />
against opportunities and benefits helps to maximize mission success. Balancing costs and<br />
benefits is a subjective process and must remain a leader’s decision.<br />
d. Anticipate and Manage <strong>Risk</strong> by Planning. Integrate risk management into<br />
planning at all levels. Commanders must dedicate time and resources to apply risk<br />
management effectively in the planning process, where risks can be more readily assessed<br />
and managed. Integrating risk management into planning as early as possible provides<br />
leaders the greatest opportunity to make well-informed decisions and implement effective<br />
risk controls. During execution phases of operations, the risk management process must be<br />
1-2
applied to address previously unidentified risks while continuing to evaluate the<br />
effectiveness of existing risk control measures and modify them as required.<br />
5. Levels of <strong>Risk</strong> <strong>Management</strong><br />
The risk management process has two levels of application: crisis action and deliberate.<br />
Time is the basic factor that contributes to the selection of the level of application used.<br />
a. Crisis Action. Crisis action risk management is an “on-the-run” mental or verbal<br />
review of the situation using the basic risk management process. The crisis action process<br />
of risk management is employed to consider risk while making decisions in a timecompressed<br />
situation. This level of risk management is used during the execution phase of<br />
training or operations as well as in planning and execution during crisis responses. It is<br />
particularly helpful for choosing the appropriate COA when an unplanned event occurs.<br />
b. Deliberate. Deliberate risk management is the application of the complete process<br />
when time is not critical. It primarily uses experience and brainstorming to identify threats<br />
and develop controls and is, therefore, most effective when done in a group. Examples of<br />
deliberate applications include planning upcoming operations, reviewing standing<br />
operating procedures (SOP), maintenance, training, and developing damage control or<br />
disaster response plans.<br />
6. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Overview<br />
The risk management process involves the following:<br />
0 Identifying threats.<br />
0 Assessing threats to determine risks.<br />
Developing controls and making risk decisions.<br />
0 Implementing controls.<br />
0 Supervising and reviewing.<br />
a. Threat Identification and Threat Assessment. These elements comprise the<br />
risk assessment portion of risk management. In threat identification, individuals identify<br />
the threats that may be encountered in executing a mission. In threat assessment, they<br />
determine the direct impact of each threat on the operation. <strong>Risk</strong> assessment provides<br />
enhanced awareness and understanding of the situation. This awareness builds confidence<br />
and allows timely, efficient, and effective protective measures.<br />
b. Develop Controls, Make Decisions, Implement Controls, Supervise, and<br />
Review. These remaining elements of the risk management process are the essential<br />
follow-through actions of managing risk effectively. Leaders weigh risk against benefits and<br />
take appropriate actions to eliminate unnecessary risk. During planning, preparation, and<br />
execution, the commander should communicate his acceptable risks to subordinates and<br />
continuously assess risks to the overall mission. Finally, leaders and individuals evaluate<br />
the effectiveness of controls and capture lessons learned.<br />
7. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Application Guidelines<br />
This section provides general guidelines for applying the risk management process. To<br />
get maximum benefit from this tool-<br />
a. Apply the <strong>Process</strong> in Sequence. Each element is a building block for the next<br />
one. For example, if threat identification is interrupted to focus control on a particular<br />
threat, other more important threats may be overlooked and the risk management process<br />
may be distorted. Until threat identification is complete, it is not possible to prioritize risk<br />
control efforts properly.<br />
1-3
. Maintain Balance in the <strong>Process</strong>. All parts of the process are important. If only<br />
an hour is available to apply the risk management process, the time must be allocated to<br />
ensure the total process can be completed. Spending fifty minutes of the hour on threat<br />
identification may not leave enough time to apply the other parts of the process effectively.<br />
The result would be suboptimal risk management. Of course, it is simplistic to rigidly insist<br />
that each of the parts is allocated ten minutes. The objective is to assess the time and<br />
resources available for risk management activities and allocate them to the actions in a<br />
manner most likely to produce the best overall result.<br />
c. Apply the <strong>Process</strong> as a Cycle. See Figure 1-1 below. Notice that “supervise and<br />
review” feeds back into the beginning of the process. When “supervise and review” identifies<br />
additional threats or determines that controls are ineffective, the entire risk management<br />
process should be repeated.<br />
Identify the Threats<br />
I Analyze Mission I I ListThreats I I Listcauses I<br />
New<br />
Threats<br />
Supervise and Review<br />
r<br />
I<br />
Assess the Threat<br />
Assess Threat<br />
Severitv<br />
f<br />
--- Make <strong>Risk</strong> Decisions<br />
jiProvide<strong>11</strong><br />
Implementation Accountabilit Support Develop Controls<br />
and Determine<br />
I Implement Controls I I Develop Controls and<br />
<strong>11</strong> : I! Establish<br />
I -<br />
I I I I Residual <strong>Risk</strong> I<br />
13Make <strong>Risk</strong><br />
Decisions<br />
I<br />
I<br />
As controls for threats are identified and selected, the<br />
Assess Threats <strong>Process</strong> is repeated.<br />
Figure 1-1. Continuous Application of <strong>Risk</strong> <strong>Management</strong><br />
1-4
d. Involve People Fully. The only way to ensure the risk management process is<br />
effective is to involve the people actually exposed to the risks. Periodically revalidate risk<br />
management procedures to ensure those procedures support the mission.<br />
8. Relationship of Force Protection to <strong>Risk</strong> <strong>Management</strong><br />
The commander has the dilemma of weighing mission requirements and force protection<br />
measures. One of his primary tools for weighing mission and protection is reconciled by<br />
assessing and balancing risk. This process forms a direct relationship between force<br />
protection and risk management. In the force protection process, we consider three<br />
elements: planning, operations, and sustainment. <strong>Risk</strong> management enables the force<br />
protection process by using risk assessment and controls in each element. The relationship<br />
between force protection and risk management is evident in the following:<br />
a. In planning, we conduct risk assessment and develop controls.<br />
b. In operations, we update risk assessment and implement controls.<br />
c. In sustainment, we continue to update assessments and adjust controls.<br />
1-5
1. Background<br />
Chapter II<br />
RISK MANAGEMENT PROCESS AND OPERATIONAL<br />
CONSIDERATIONS<br />
This chapter discusses the risk management process and how it may be applied in the<br />
planning and execution phases of all operations. This chapter also provides two situational<br />
analysis models. These models are the mission, enemy, terrain and weather, troops and<br />
support available, time (METT-T) model and the man, machine, media, management,<br />
mission (5-M) model.<br />
2. Application of <strong>Risk</strong> <strong>Management</strong><br />
a. Identify Threats. A threat is a source of danger: any opposing force, condition,<br />
source, or circumstance with the potential to impact mission accomplishment negatively<br />
and/or degrade mission capability. Experience, common sense, and risk management tools<br />
help identify real or potential threats. Threat identification is the foundation of the entire<br />
risk management process; if a threat is not identified it cannot be controlled. The effort<br />
expended in identifying threats will have a multiplier effect on the impact of the total risk<br />
management<br />
1<br />
process. Figure<br />
bl<br />
<strong>11</strong>-1 depicts the actions necessary<br />
Fl<br />
to identify threats<br />
1<br />
associated with these three categories: (1) mission degradation, (2) personal injury or death,<br />
and (3) property damage.<br />
ACTION1 ACTION2 ACTION3<br />
ANALYZE MISSION LIST THREATS LIST CAUSES<br />
I 1 I I I I<br />
Figure <strong>11</strong>-1. Identify the Threats<br />
(1) Action 1-Analyze Mission. This is accomplished by-<br />
(a) Reviewing operation plans and orders describing the mission.<br />
(b) Defining requirements and conditions to accomplish the tasks.<br />
(c) Constructing a list or chart depicting the major phases of the operation<br />
normally in time sequence.<br />
(d) Breaking the operation down into “bite-size” chunks.<br />
(2) Action 2-List Threats. Threats (and factors that could generate threats) are<br />
identified based on the mission and associated vulnerabilities. The output of the<br />
identification phase is a list of inherent threats or adverse conditions, which is developed by<br />
listing the threats associated with each phase of the operation. Stay focused on the specific<br />
steps in the operation; limit your list to “big picture” threats. Examine friendly centers of<br />
gravity for any critical vulnerabilities. Threats may be tracked on paper or in a computer<br />
spreadsheeddatabase system to organize ideas and serve as a record of the analysis for<br />
future use.<br />
(3) Action 3-List Causes. Make a list of the causes associated with each threat<br />
identified in Action 2. Although a threat may have multiple causes, it is paramount to<br />
identify the root cause(s). <strong>Risk</strong> controls may be more effective when applied to root causes.<br />
b. Assess Threats. Each threat is assessed for probability and severity of occurrence.<br />
Probabilityis the estimate of the likelihood that a threat will cause an impact on the<br />
<strong>11</strong>-1
mission. Some threats produce losses frequently; others almost never do. Severity is the<br />
expected consequence of an event in terms of degree of injury, property damage, or other<br />
mission-impairing factors (such as loss of combat power). The result of this risk assessment<br />
allows prioritization of threats based on risk. The number one risk is the one with the<br />
greatest potential impact on the mission. However, the least risky issue may still deserve<br />
some attention and, possibly, risk control action. Keep in mind that this priority listing is<br />
intended for use as a guide to the relative priority of the risks involved, not as an absolute<br />
order to be followed. There may be, as an example, something that is not a significant risk<br />
that is extremely simple to control. Figure <strong>11</strong>-2 depicts the necessary actions.<br />
ASSESS THREAT ASSESS THREAT COMPLETE RISK<br />
SEVERITY PROBABILITY ASSESSMENT<br />
I I I I<br />
Figure <strong>11</strong>-2. Assess the Threat<br />
(1) Action 1-Assess Threat Severity. Determine the severity of the threat in<br />
terms of its potential impact on the mission, exposed personnel, and exposed equipment.<br />
Severity categories are defined to provide a qualitative measure of the worst credible<br />
outcome resulting from external influence (such as combat or terrorist action; personnel<br />
error; environmental conditions; design inadequacies; procedural deficiencies; or system,<br />
subsystem, or component failure or malfunction). Severity categories listed in Appendix A,<br />
Annex D, provide guidance for a wide variety of missions and systems.<br />
(2) Action 2-Assess Threat Probability. Determine the probability that the<br />
threat will cause a negative event of the severity assessed in Action 1. Probability may be<br />
determined through experienced-based estimates or derived from research, analysis, and<br />
evaluation of historical data from similar missions and systems. The typical event sequence<br />
is much more complicated than a single line of erect dominos; tipping the first domino<br />
(threat) triggers a clearly predictable reaction. Supporting rationale for assigning a<br />
probability should be documented for future reference. Generally accepted definitions for<br />
probability may be found at Appendix A, Annex D.<br />
(3) Action 3-Complete <strong>Risk</strong> Assessment. Combine severity and probability<br />
estimates to form a risk assessment for each threat. When combining the probability of<br />
occurrence with severity, a matrix may be used to assist in identifying the level of risk. A<br />
sample matrix is in Appendix A, Annex D. Existing databases and/or a panel of personnel<br />
experienced with the mission and threats can also be used to help complete the risk<br />
assessment.<br />
(4) Output of <strong>Risk</strong> Assessment. The outcome of the risk assessment process is a<br />
prioritized list of threats. The highest priority threat is the most serious one to the mission;<br />
the last is the least serious risk of any consequence.<br />
(5) <strong>Risk</strong> Assessment Pitfalls. The following are some pitfalls that should be<br />
avoided during the assessment:<br />
(a) Over optimism: “It can’t happen to us. We’re already doing it.” This pitfall<br />
results from not being totally honest and not looking for root causes of the threats.<br />
(b) Misrepresentation: Individual perspectives may distort data. This can be<br />
deliberate or unconscious.<br />
(c) Alarmism: “The sky is falling” approach, or “worst case” estimates are used<br />
regardless of their possibility.<br />
<strong>11</strong>-2
(d) Indiscrimination: All data is given equal weight.<br />
(e) Prejudice: Subjectivity andor hidden agendas are used instead of facts.<br />
(f)<br />
Inaccuracy: Bad or misunderstood data nullify accurate risk assessment.<br />
(g) Enumeration: It is difficult to assign a numerical value to human behavior.<br />
Numbers may oversimplify real life situations.<br />
It may be difficult to get enough applicable data; this could force<br />
inaccurate estimates.<br />
numbers.<br />
0<br />
Numbers often take the place of reasoned judgment.<br />
<strong>Risk</strong> can be unrealistically traded off against benefit by relying solely on<br />
c. Develop Controls and Make <strong>Risk</strong> Decisions. These actions are listed as<br />
separate and distinct parts of the overall process by the U.S. Air Force (USAF), but will be<br />
dealt with under this overall heading for the purpose of this publication. Figure <strong>11</strong>-3 depicts<br />
the necessary actions.<br />
I<br />
ACTION 1<br />
DEVELOP CONTROLS AND<br />
DETERMINE RESIDUAL<br />
RISK<br />
I<br />
Figure <strong>11</strong>-3. Develop Controls and Make <strong>Risk</strong> Decisions<br />
MAKE RISK<br />
DECISIONS<br />
(1) Action 1-Develop Controls. After assessing each threat, leaders should<br />
develop one or more controls that either eliminate the threat or reduce the risk (probability<br />
and/or severity) of threats. For each threat identified, develop one or more control options<br />
that either avoid the threat or reduce its risk to a level that meets the commander’s risk<br />
guidance. Examples of criteria for establishing effective controls are listed in Table <strong>11</strong>- 1.<br />
<strong>11</strong>-3
(a) Some types of controls are as follows:<br />
Engineering controls. These controls use engineering methods to reduce<br />
risks, such as developing new technologies or design features, selecting better materials,<br />
identifying suitable substitute materials or equipment, or adapting new technologies to<br />
existing systems. Examples of engineering controls that have been employed in the past<br />
include development of aircraft stealth technology, integrating global positioning system<br />
data into cruise missiles, and development of night vision devices.<br />
Administrative controls. These controls involve administrative actions,<br />
such as establishing written policies, programs, instructions, and SOPS, or limiting the<br />
exposure to a threat either by reducing the number of personneVassets or length of time<br />
they are exposed.<br />
0 Educational controls. These controls are based on the knowledge and<br />
skills of the units and individuals. Effective control is implemented through individual and<br />
collective training that ensures performance to standard.<br />
0 Physical controls. These controls may take the form of barriers and<br />
guards or signs to warn individuals and units that a threat exists. Use of personal<br />
protective equipment, fences around high power high frequency antennas, and special<br />
controller or oversight personnel responsible for locating specific threats fall into this<br />
category.<br />
0 Operational controls. These controls involve operational actions such as<br />
pace of operations, battlefield controls (areas of operations and boundaries, direct fire<br />
control measures, fire support coordinating measures), rules of engagement, airspace<br />
control measures, map exercises, and rehearsals.<br />
(b) A control should avoidreduce the risk of a threat by accomplishing one or<br />
more of the following:<br />
0 Avoiding the risk. This often requires canceling or delaying the task,<br />
mission, or operation and is, therefore, an option rarely exercised because of mission<br />
importance. However, it may be possible to avoid specific risks: risks associated with a<br />
night operation may be avoided by planning the operation for daytime; thunderstorm or<br />
surface-to-air-missile risks can be avoided by changing the flight route.<br />
0 Delay a COA. If there is no time deadline or other operational benefit to<br />
speedy accomplishment of a task, it may be possible to reduce the risk by delaying the task.<br />
Over time, the situation may change and the risk may be eliminated, or additional risk<br />
control options may become available (resources become available, new technology becomes<br />
available, etc.) reducing the overall risk. For example, a mission can be postponed until<br />
more favorable weather reduces the risk to the force.<br />
0 Transferring the risk. <strong>Risk</strong> may be reduced by transferring a mission, or<br />
some portion of that mission, to another unit or platform that is better positioned, more<br />
survivable, or more expendable. Transference decreases the probability or severity of the<br />
risk to the total force. For example, the decision to fly an unmanned aerial vehicle into a<br />
high-risk environment instead of risking a manned aircraft is risk transference.<br />
0 Assigning redundant capabilities. To ensure the success of critical<br />
missions to compensate for potential losses assign redundant capabilities. For example,<br />
tasking a unit to deploy two aircraft to attack a single high value target increases the<br />
probability of mission success.<br />
<strong>11</strong>-4
(c) Determine Residual <strong>Risk</strong>. Once the leader develops and accepts<br />
controls, he or she determines the residual risk associated with each threat and the overall<br />
residual risk for the mission. Residual risk is the risk remaining after controls have been<br />
identified, selected, and implemented for the threat. As controls for threats are identified<br />
and selected, the threats are reassessed, and the level of risk is revised. This process is<br />
repeated until the level of residual risk is acceptable to the commander or leader or cannot<br />
be further reduced. Overall residual risk of a mission must be determined when more than<br />
one threat is identified. The residual risk for each of these threats may have a different<br />
level, depending on the assessed probability and severity of the hazardous incident. Overall<br />
residual mission risk should be determined based on the threat having the greatest<br />
residual risk. Determining overall mission risk by averaging the risks of all threats is not<br />
valid. If one threat has high residual risk, the overall residual risk of the mission is high, no<br />
matter how many moderate or low risk threats are present.<br />
(2) Action 2-Make <strong>Risk</strong> Decisions. A key element of the risk decision is<br />
determining if the risk is justified. The leader should compare and balance the risk against<br />
the mission’s potential gain. The leader alone decides if controls are sufficient and<br />
acceptable and whether to accept the resulting residual risk. If the leader determines the<br />
risk level is too high, he or she directs the development of additional or alternate controls,<br />
or modifies, changes, or rejects the COA. Leaders can use the risk assessment matrix or<br />
other tools found in Appendix A, in conjunction with their commanders’ guidance, to<br />
communicate how much risk they are willing to allow subordinate leaders to accept.<br />
d. Implement Controls. Once the risk control decision is made, assets must be made<br />
available to implement the specific controls. Part of implementing controls is informing the<br />
personnel in the system of the risk management process results and subsequent decisions.<br />
Figure <strong>11</strong>-4 depicts the actions necessary to complete this step. Careful documentation of<br />
each step in the risk management process facilitates risk communication and the rational<br />
processes behind risk management decisions.<br />
I<br />
ACTION 1 ACTION 2<br />
MAKE<br />
IMPLEMENTATION<br />
I<br />
ESTABLISH<br />
ACCOUNTABILITY<br />
I CLEAR I I I<br />
I I I I<br />
Figure <strong>11</strong>-4. Implement Controls<br />
ACTION 3<br />
PROVl DE<br />
SUPPORT<br />
(1) Action 1-Make Implementation Clear. To make the implementation<br />
directive clear, consider using examples, providing pictures or charts, including job aids,<br />
etc. Provide a roadmap for implementation, a vision of the end state, and description of<br />
successful implementation. The control should be presented so it will be received positively<br />
by the intended audience. This can best be achieved by designing in user ownership.<br />
(2) Action 2-Establish Accountability. Accountability is important to effective<br />
risk management. The accountable person is the one who makes the decision (approves the<br />
control measures): therefore, the right person (appropriate level) must make the decision.<br />
Clear assignment of responsibility for implementation of the risk control is required.<br />
<strong>11</strong>-5
(3) Action 3-Provide Support. To be successful, the command must support the<br />
risk controls. This support requires-<br />
(a) Providing the personnel and resources necessary to implement the control<br />
measures.<br />
(b) Designing in sustainability from the beginning.<br />
(c) Employing the control with a feedback mechanism that will provide<br />
information on whether the control is achieving the intended purpose.<br />
e. Supervise and Review. Supervise and review involves determining the<br />
effectiveness of risk controls throughout the operation. There are three aspects: monitoring<br />
the effectiveness of risk controls: determining the need for further assessment of either all,<br />
or a portion of, the operation due to an unanticipated change; and capturing lessons<br />
learned, both positive and negative. Figure <strong>11</strong>-5 depicts the necessary actions.<br />
I i<br />
1- I<br />
i<br />
1- I<br />
ACTION 1 ACTION 2 ACTION 3<br />
SUPERVISE REVIEW FEEDBACK<br />
I I I I I<br />
Figure <strong>11</strong>-5. Supervise and Review<br />
(1) Action l-Supervise. Monitor the operation to ensure-<br />
(a) Controls are implemented correctly, effective, and remain in place.<br />
(b) Changes requiring further risk management are identified.<br />
(c) Action is taken to correct ineffective risk controls and reinitiate the risk<br />
management process in response to new threats.<br />
(d) <strong>Risk</strong>s and controls are reevaluated any time the personnel, equipment, or<br />
mission tasks change, or new operations are anticipated in an environment not covered in<br />
the initial risk management analysis.<br />
Successful mission performance is achieved by shifting the cost versus benefit balance<br />
more in favor of benefit through controlling risks. By using risk management whenever<br />
anything changes, we consistently control risks identified before an operation and those<br />
that develop during the operation. Addressing the risks before they get in the way of<br />
mission accomplishment saves resources and enhances mission performance.<br />
(2) Action 2-Review. The risk management process review must be systematic.<br />
After controls are applied, a review must be accomplished to see if the risks and the mission<br />
are in balance. To determine if appropriate risk management controls have been applied,<br />
compare METT-T or the 5-M model from the earlier steps to the present risk management<br />
assessment.<br />
(a) To accomplish an effective review, commanders identify whether the actual<br />
cost is in line with expectations. The commander needs to determine what effect the risk<br />
control had on mission performance. It is difficult to evaluate the risk control by itself;<br />
therefore, the focus should be on the aspect of mission performance the control measure<br />
was designed to improve.<br />
(b) Measurements are necessary to ensure accurate evaluations of how<br />
effectively controls eliminated threats or reduced risks. After Action Reports (AAR) ,<br />
surveys, and in-progress reviews provide great starting places for measurements.<br />
<strong>11</strong>-6
~ Deliberate<br />
(3) Action 3-Feedback. A review by itself is not enough; a mission feedback<br />
system should be established to ensure that the corrective or preventative action taken was<br />
effective and that any newly discovered threats identified during the mission were analyzed<br />
and corrective action taken.<br />
(a) When a decision is made to accept risk, factors (cost versus benefit<br />
information) involved in the decision should be recorded: proper documentation allows for<br />
review of the risk decision process. Then, when a negative consequence occurs, the decision<br />
process can be reviewed to determine where errors in the process may have occurred.<br />
(b) <strong>Risk</strong> analysis will not always be perfect the first time. When errors occur in<br />
an analysis, use feedback (such as briefings, lessons learned, cross-tell reports,<br />
benchmarking, or database reports) to identify and correct those errors. This feedback will<br />
help determine if the previous forecasts were accurate, contained errors, or were<br />
completely incorrect.<br />
3. Integration of <strong>Risk</strong> <strong>Management</strong><br />
Tables <strong>11</strong>-2 and <strong>11</strong>-3 integrate the risk management process into each phase of the<br />
deliberate and crisis action Joint Operation Planning and Execution System (JOPES). The<br />
annotations of the joint task force (JTF) and major subordinate element (MSE) in the<br />
matrix identify the level of command primarily responsible for risk management execution<br />
during each particular phase of planning. The risk management process should be<br />
considered throughout the planning process by each level of command.<br />
Planning<br />
Table <strong>11</strong>-2<br />
<strong>Risk</strong> <strong>Management</strong> Execution<br />
(<strong>Risk</strong> <strong>Management</strong> in Deliberate Planning)<br />
Develop Controls<br />
Identify Assess<br />
Make<br />
Threats Threats <strong>Risk</strong> Decision Controls<br />
Supervise<br />
and Review<br />
PHASE I<br />
Initiation<br />
JTF<br />
I<br />
I<br />
PHASE II<br />
Concept Development<br />
PHASE <strong>11</strong>1<br />
Plan Development<br />
PHASE IV<br />
Plan Review<br />
PHASE V<br />
Supporting Plans<br />
EXECUTION<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
JTF<br />
I I I I I I<br />
JTF<br />
JTF<br />
MSE<br />
MSE<br />
<strong>11</strong>-7
~ PLANNING<br />
~<br />
~ Controls<br />
CRISIS ACTION<br />
1 PHASE I<br />
Situation Development<br />
PHASE II<br />
Crisis Assessment<br />
~~<br />
PHASE <strong>11</strong>1<br />
COA Development<br />
PHASE IV<br />
COA Selection<br />
<strong>Risk</strong> Manage1<br />
(<strong>Risk</strong> Mananement in<br />
I JTF<br />
I JTF<br />
I JTF I JTF<br />
Tab e <strong>11</strong>-3<br />
lent Execution<br />
Xsis Action Planni<br />
Develop Controls<br />
Make <strong>Risk</strong><br />
Decision<br />
JTF<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
Implement<br />
Supervise<br />
and Review<br />
PHASE V<br />
Execution Planning<br />
JTF<br />
MSE<br />
+IMSE<br />
PHASE VI<br />
Execution<br />
I MSE I MSE<br />
MSE<br />
MSE<br />
MSE<br />
4. Analysis Models<br />
a. The METT-T Model. The METT-T model can be used for conducting a situation<br />
analysis by breaking it into five general areas: (1) the mission itself, (2) the enemy, (3)<br />
terraidweather, (4) troops and support available, and (5) time available.<br />
Note. The U.S. Army uses mission, enemy, terrain and weather, troops and support<br />
available, time available, civil considerations (METT-TC), adding civil considerations<br />
as a sixth area of analysis.<br />
(1) Mission. Leaders first analyze the assigned mission. They look at the type of<br />
mission to be accomplished and consider possible subsequent missions. Certain kinds of<br />
operations are inherently more dangerous than others. For example, a deliberate frontal<br />
attack is more likely to expose a unit to losses than would a defense from prepared<br />
positions. Identifying missions that routinely present greater risk is imperative. Leaders<br />
also look for threats associated with complexity of the plan (such as a scheme of maneuver<br />
that is difficult to understand or too complex for accurate communications down to the<br />
lowest level) or the impact of operating under a fragmentary order.<br />
(2) Enemy. Commanders look for enemy capabilities that pose significant threats to<br />
the operation. For example, “What can the enemy do to defeat my operation?”<br />
to-<br />
(a) Common shortfalls that can create threats during operations include failure<br />
0 Assess potential advantages to the enemy provided by the battlefield<br />
environment.<br />
0 Fully assess the enemy’s capabilities.<br />
0 Understand enemy capabilities and friendly vulnerabilities to those<br />
capabilities.<br />
<strong>11</strong>-8
Accurately determine the enemy’s probable COAs.<br />
Plan and coordinate active ground and aerial reconnaissance activities.<br />
Disseminate intelligence about the enemy to lower echelons.<br />
Identify terrorist threats and capabilities.<br />
(b) Intelligence plays a critical part in identifying threats associated with the<br />
presence of an enemy or an adversary. Intelligence preparation of the battlespace is a<br />
dynamic staff process that continually integrates new information and intelligence that<br />
ultimately becomes input to the commander’s risk assessment process. Intelligence assists<br />
in identifying threats during operations by-<br />
Identifying opportunities and constraints the battlefield environment offers<br />
to enemy and friendly forces.<br />
Thoroughly portraying enemy capabilities and vulnerabilities.<br />
0 Collecting information on populations, governments, and infrastructures.<br />
(3) Terrain and Weather. Terrain and weather pose great potential threats to<br />
military operations. The unit must be familiar with both the terrain and its associated<br />
environment for a mission to succeed. Basic issues include availability of reliable weather<br />
forecasts, how long the unit has operated in the environment and climate, and whether the<br />
terrain has been crossed before.<br />
(a) Terrain. The main military aspects of terrain are observation and fields of<br />
fire, cover and concealment, obstacles, key terrain, and avenues of approach; these may be<br />
used to identify and assess threats impacting friendly forces. Terrain analysis includes both<br />
map and visual reconnaissance to identify how well the terrain can accommodate unit<br />
capabilities and mission demands.<br />
0 Observation and fields uffire. Threats associated with observation and fields<br />
of fire usually involve when the enemy will be able to engage a friendly unit and when the<br />
friendly unit’s weapon capabilities allow it to engage the enemy effectively.<br />
Cover and Concealment. Threats associated with cover and concealment are<br />
created either by failure to use cover and concealment or by the enemy’s use of cover and<br />
concealment to protect his assets from observation and fire.<br />
0 Obstacles. Threats associated with obstacles may be caused by natural<br />
conditions (such as rivers or swamps) or man-made conditions (such as minefields or builtup<br />
areas).<br />
0 Key terrain. Threats associated with key terrain result when the enemy<br />
controls that terrain or denies its use to the friendly forces.<br />
0 A venues of approach. Threats associated with avenues of approach include<br />
conditions in which an avenue of approach impedes deployment of friendly combat power or<br />
conditions that support deployment of enemy combat power.<br />
(b) Weather. To identify weather threats, leaders and unit personnel must<br />
assess the impact on operating systems. Threats may arise from-<br />
0 Lack of understanding of reliability and accuracy of weather forecasting.<br />
0 Effects of climate and weather on personnel and equipment operation and<br />
maintenance.<br />
0 Effects of weather on mobility.<br />
<strong>11</strong>-9
(4) Troops and Support Available. Leaders analyze the capabilities of available<br />
friendly troops. Associated threats impact both individual personnel and the unit. Key<br />
considerations are level of training, manning levels, the condition and maintenance of<br />
equipment, morale, availability of supplies and services, and the physical and emotional<br />
health of personnel. All personnel must be vigilant to the fact that threats in these areas<br />
can adversely affect a mission. Even when all tactical considerations point to success,<br />
mission failure can be caused by-<br />
(a) Threats to physical and emotional health. The health threat depends on a<br />
complex set of environmental and operational factors that combine to produce “disease<br />
non-battle injuries” as well as combat injuries. Care of troops requires long-range<br />
projection of logistical and medical needs with close monitoring of mission changes that<br />
could impact troop support.<br />
(b) Threats to task organization or units participating in an operation. Threats<br />
include poor communication, unfamiliarity with higher headquarters SOPS, and<br />
insufficient combat power to accomplish the mission. How long units have worked together<br />
under a particular command relationship should be considered when identifying threats.<br />
(c) Threats associated with long-term missions. Long-term missions include<br />
peacekeeping, or insurgencykounterinsurgency operations. Threats associated with these<br />
missions include the turmoil of personnel turnover, lack of continuity of leadership,<br />
inexperience, and lack of knowledge of the situation and the unit’s operating procedures.<br />
Long-term missions can also lead to complacency; units conditioned to routine ways of<br />
accomplishing the mission fail to see warnings evident in the operational environment. An<br />
especially insidious threat is the atrophy of critical-skills that results from not performing<br />
mission-essential task list related missions.<br />
(5) Time Available. The threat is insufficient time to plan, prepare, and execute<br />
operations. Planning time is always at a premium. Leaders routinely apply the onethirdtwo-thirds<br />
rule (providing two thirds of time available to subordinates for planning) to<br />
ensure their subordinate units are given maximum time to plan. Failure to accomplish a<br />
mission on time can result in shortages of time for subordinate and adjacent units to<br />
accomplish their missions.<br />
b. U.S. Army Situation Analysis. While Joint, Marine Corps, Air Force, and Navy<br />
doctrine use METT-T for situation analysis, the Army uses MEW-TC. The “C” in METT-TC<br />
is civil considerations-how the attitudes and activities of the civilian leaders, populations,<br />
and organizations within an area of operations will influence the conduct of military<br />
operations. Threats associated with civil considerations include, but are not limited to,<br />
collateral damage, changing political and social attitudes, civilian unrest, the influence of<br />
the press on public opinion, conflicting goals and objectives of private voluntary<br />
organizations (PVOs) and nongovernmental organizations (NGOs), and the handling of<br />
refugees, noncombatants, and protesters.<br />
c. 5-M Model. The 5-M model provides an alternative framework for conducting<br />
mission analysis by examining the impacts and inter-relationships between the composite<br />
elements of Man, Machine, Media, <strong>Management</strong>, and Mission. The amount of overlap or<br />
interaction between the individual components is a characteristic of each mission and<br />
evolves as the mission develops.<br />
<strong>11</strong>-10
(1) Man. This is the area of greatest variability and thus possesses the majority of<br />
risks. Some considerations and potential threats are listed in Table <strong>11</strong>-4.<br />
Table <strong>11</strong>-4<br />
Considerations and Potential Threats Analyzed<br />
(Man Element, 5-M Model)<br />
Considerations<br />
Selection<br />
Performance<br />
Personal Factors<br />
Potential Threats<br />
Wrong person psychologicaIly/physicaIly, not proficient in assigned<br />
task, no procedural guidance<br />
Lack of awareness, false perceptions, over-tasking, distraction,<br />
channelized attention, stress, peer pressure, over/lack of<br />
confidence, poor insight, poor adaptive skills, pressure/workload,<br />
fatigue<br />
Expectations, lack of job satisfaction, poor values, families/friends,<br />
commandkontrol, poor discipline (internal and external), perceived<br />
pressure (over tasking) and poor communication skills<br />
(2) Machine. Used as intended, limitations interface with man. Some<br />
considerations and potential threats are listed in Table <strong>11</strong>-5.<br />
Table <strong>11</strong>-5<br />
Considerations and Potential Threats Analyzed<br />
(Machine Element, 5-M Model)<br />
Considerations<br />
Design<br />
Maintenance<br />
Log istics<br />
Technical Data<br />
Potential Threats<br />
Engineering reliability and performance, ergonomics<br />
Availability of time, tools, and parts, ease of access<br />
Supply, upkeep, and repair<br />
Clear, accurate, useable, and available<br />
<strong>11</strong>-1 1
~ ~~ ~____<br />
(3) Media. This includes external, largely environmental forces. Some<br />
considerations and potential threats are listed in Table <strong>11</strong>-6.<br />
Table <strong>11</strong>-6<br />
Considerations and Potential Threats Analyzed<br />
(Media Element, 5-M Model)<br />
I Considerations<br />
I Po fen fial Threa fs<br />
I Climatic<br />
Operational<br />
~ _ _ _ _ ~ ~<br />
I Ceiling, visibility, temperature, humidity, wind, and precipitation<br />
Terrain, wildlife, vegetation, man-made obstructions, daylight,<br />
maritime environment, and darkness<br />
Hygienic<br />
I Trafficability<br />
Ventilationlair quality, noiselvibration, dust, and contaminants<br />
Pavement, gravel, dirt, ice, mud, dust, snow, sand, hills, and<br />
curves<br />
(4) <strong>Management</strong>. Directs the process by defining standards, procedures, and<br />
controls. While management provides procedures and rules to govern interactions, it cannot<br />
completely control the system elements. For example, weather is not under management<br />
control and individual decisions affect off-duty personnel much more than management<br />
policies. Some considerations and examples are listed in Table <strong>11</strong>-7.<br />
Table <strong>11</strong>-7<br />
<strong>Management</strong> Tools and Examples Analyzed<br />
I Considerations<br />
(<strong>Management</strong> Element, 5-M Model)<br />
I Examples<br />
I<br />
Standards<br />
Procedures<br />
Controls<br />
Doctrine statements, applicable criteria, and policy directives<br />
Checklists, SOPS, work cards, and multi-command manuals<br />
Crew rest, altitudelairspeedkpeed limits, restrictions, training<br />
rules/limitations, rules of engagement (ROE), lawful orders<br />
(5) Mission. The desired outcome. Objectives: Big picture understood, well defined,<br />
obtainable. The results of the interactions of the other 4-Ms (Man, Media, Machine, and<br />
<strong>Management</strong>).<br />
<strong>11</strong>-12
1. Background<br />
Chapter <strong>11</strong>1<br />
STAFF FUNCTIONS AND RESPONSIBILITIES<br />
The unit commander, staff, leaders, and individual members integrate risk<br />
management by embedding the risk management process into unit operations, culture,<br />
organization, systems, and individual behaviors.<br />
a. Successful risk management is underwritten by the chain of command. Leaders do<br />
not expect all missions to be accomplished with zero defects. Leaders need to support<br />
subordinates’ decisions to accept risks that are within the leaders’ understanding of the<br />
commander’s intent and guidance. Demanding rigid standards, such as zero defects, leads<br />
to over-supervision and paralysis, producing timid leaders afraid to make tough decisions in<br />
crisis, and unwilling to take risks necessary for successful military operations. A zerodefects<br />
mindset creates conditions that will inevitably lead to failure and higher casualties<br />
in battle.<br />
b. Leaders anticipate things may go wrong, even with the certain knowledge that<br />
subordinates do all within their power to prevent incidents. When incidents occur, leaders<br />
step forward and accept the responsibility along with their subordinates. Furthermore, risk<br />
management does not justify taking actions to facilitate an unethical, immoral, or illegal<br />
action.<br />
2. Responsibilities<br />
a. Commanders. With the assistance of their leaders and staffs, commanders manage<br />
risks. Minimizing risk is the responsibility of everyone in the chain of command, from the<br />
highest commander, through his subordinate leaders, to each individual service member.<br />
Managing risk is critical for all operations, whether for training or operations; commanders<br />
should issue clear risk guidance.<br />
(1) Military plans should make risk management a priority. It is an inherent part of<br />
every mission and a basic responsibility of commanders. Leaders and service members at<br />
all levels are responsible and accountable for managing risks by ensuring that threats and<br />
associated risks are-<br />
(a) Identified during planning, preparation, and execution of operations.<br />
(b) Controlled during preparation and execution of operations. Service members<br />
are responsible for executing risk controls to standards. They continuously assess variable<br />
threats such as fatigue, equipment serviceability, and the environment. They make risk<br />
decisions consistent with the higher commander’s guidance.<br />
(2) Sometimes commanders are not properly advised in situations where the<br />
assumption of risk may affect or imperil their units, the intent of their higher commander,<br />
or the operations of an adjacent unit. This is most often attributed to-<br />
(a) <strong>Risk</strong> denial syndrome-leaders do not want to know of the risk.<br />
(b) Staff members who believe that the risk decision is part of their jobs and<br />
do not want to bother the commander or section leader.<br />
guidance.<br />
(c) Subordinates failure to fully understand the higher commander’s<br />
(d) Complacency-outright failure to recognize a threat or the level of risk<br />
involved, or overconfidence in one’s abilities or the unit’s capabilities to avoid or recover<br />
from a hazardous incident.<br />
<strong>11</strong>1-1
(e) Use of a standardized risk assessment tool, such as a risk assessment<br />
matrix, that is not tailored to the unit’s mission or adapted to the factors of METT-T/S-M<br />
and may put missions in the routine low-risk category.<br />
b. Commanders/Leaders.<br />
(1) The commander directs the organization and sets priorities and the command<br />
climate (values, attitudes, and beliefs). Successful preservation of combat power requires<br />
embedding risk management into unit behavior. This requires commitment, creative<br />
leadership, innovative planning, and careful management. It also requires the chain of<br />
command’s demonstrated support of the risk management process. Commanders establish<br />
a command climate favorable for risk management integration by-<br />
(a) Demonstrating consistent and sustained risk management behavior through<br />
leading by example-habitually doing risk management-and actively participating<br />
throughout the risk management process.<br />
(b) Providing clear guidance where to accept risk or what risk to accept.<br />
(c) Obtaining and providing to subordinates the necessary assets to control risk.<br />
(d) Knowing their own limitations, their leaders’ and service members’<br />
limitations, and their unit’s capabilities.<br />
(e) Preventing a zero-defects mindset from creeping into their commands<br />
culture.<br />
(0 Allowing subordinates to make mistakes and learn from them.<br />
(g) Demonstrating full confidence in subordinates’ mastery of their trade and<br />
their ability to execute a chosen COA.<br />
(h) Keeping subordinates informed and consulting with subordinate leaders<br />
before making a decision, if feasible.<br />
(i) Listening to subordinates.<br />
(i) Establishing clear, feasible risk management policies and goals.<br />
(k) Conducting detailed planning within time constraints; assessing each<br />
mission and task in terms of its risk; continuously reassessing risk as the mission and<br />
conditions change and experience is gained.<br />
(1) Making informed risk decisions; establishing and clearly communicating<br />
risk guidance.<br />
(m) Training on the risk management process. Ensuring subordinates<br />
understand who, what, where, when, how, and why of managing risk, and how the risk<br />
management process applies to their circumstances and assigned responsibilities.<br />
(n) Examining how subordinates manage risk and how service members protect<br />
themselves.<br />
mission.<br />
(0) Supervising and evaluating the unit’s execution of risk controls during the<br />
(p) Advising the chain of command on risks and risk-reduction measures and<br />
providing subordinates with feedback on their performance and ways to improve.<br />
(4) Assessing the effectiveness of their unit’s risk management program.<br />
(r) Capturing and disseminating lessons learned to ensure they are continued<br />
from mission to mission so that others may benefit from the experience.<br />
<strong>11</strong>1-2
(2) Commanders weigh the repercussions of casualties, damage to the environment,<br />
impact on civilians, and loss of equipment. They also consider the public reaction to loss<br />
against national, strategic, operational, or tactical objectives. Commanders are also<br />
responsible for keeping subordinates from becoming complacent. An acceptable risk is the<br />
result of an informed decision. A gamble is an uninformed bet or guess on a hopeful<br />
outcome. Leaders and service members need to clearly understand the difference.<br />
(3) <strong>Risk</strong> decisions are frequently required by, and dependent on, the immediate<br />
situation. Judgment is required; a formula, rule, or checklist, by itself, is not appropriate<br />
under such circumstances. An effective commander’s approach to managing risk is to<br />
empower leaders by pushing risk decisions as far down the chain of command as feasible<br />
within the next higher commander’s guidance. Subordinates consider threats outside their<br />
assigned responsibilities that impact the mission. The result is coordination and<br />
communication-laterally and up and down the chain of command.<br />
(4) <strong>Risk</strong> management is a two-way street. It is important that those involved in<br />
mission preparation and execution are fully aware of the amount of command involvement<br />
and actions necessary to control or remove threats.<br />
(a) The higher commander’s guidance specifies the degree of acceptable damage<br />
or risk to subordinate units during the current operation.<br />
(b) Subordinates ensure they understand and implement their commander’s<br />
intent and guidance.<br />
0 If, during the planning process, residual risk exceeds that which the higher<br />
commander is willing to accept, the subordinate informs his commander. He requests the<br />
resources necessary to mitigate the risk.<br />
If, during mission execution, the subordinate determines the risk is too<br />
great, he directs the development of additional or alternate controls or modifies or changes<br />
the COA; then he notifies the next higher commander of his decision. Requiring<br />
subordinates to report to the higher commander when a risk decision point is reached<br />
during mission execution can result in paralysis.<br />
(5) The objective of managing risk is not to remove all risk, but to eliminate<br />
unnecessary risk. Commanders conduct tough, realistic training, knowing that they may<br />
put lives and property at risk in the course of military operations. If an action will result in<br />
an unacceptable risk, take measures to mitigate it. If the risk cannot be mitigated to an<br />
acceptable level, do not execute the action. Circumstances may occur during mission<br />
execution when a decision to stop and defer execution of the operation should be made to<br />
avoid taking unwarranted risk. Such a situation will generally occur at the tactical level.<br />
For example, circumstances may determine if a trade-off between maintaining the<br />
momentum of the attack and risking fratricide or serious accidents is justified.<br />
c. Staffs.<br />
(1) The chief of staff or executive officer may be assigned responsibility for<br />
supervising integration of risk management across the staff. As a means of assessing and<br />
monitoring threats, commanders may establish a force protection working group (FPWG),<br />
which is covered in detail in Appendix B. He coordinates development of risk controls with<br />
emphasis on deconflicting controls that affect multiple functional areas and adjacent units.<br />
The staff officer helps the commander eliminate unnecessary risks by-<br />
(a) Analyzing his functional area and applying risk management during the<br />
military decision-making process.<br />
guidance.<br />
(b) Identifying both constraints and restraints in the higher commander’s risk<br />
I <strong>11</strong>-3
(c) Including threats and their risks in the mission analysis briefing.<br />
(d) Including a risk assessment for the commander’s estimate.<br />
(e) Considering the risk assessment in the operations estimate.<br />
(f) Including risks and recommending ways to reduce their impact in the staff<br />
estimate.<br />
(g) Implementing risk controls by coordinating and integrating them into the<br />
appropriate paragraphs and graphics of the operation order (OPORD) and into products<br />
such as SOPS and operation plans (OPLANs).<br />
(h) Establishing procedures and standards that are clear and practical.<br />
(i) Determining the effectiveness of risk controls and continuously assessing<br />
their suitability, feasibility, supportability, clarity, and acceptability.<br />
(j) Supervising, evaluating, and assessing the integration of risk management<br />
during an operation.<br />
(k) Continuously identifying threats, assessing initial and residual risks for<br />
each threat, and recommending control measures to reduce the risk.<br />
(1) Identifying and assessing threats associated with complacency, especially<br />
during extended operations, and recommending appropriate actions to the commander.<br />
(2) Staffs focus on threats and their risks across the spectrum of protecting the force.<br />
These staffs-<br />
(a) Identify friendly vulnerabilities during current operations and implement<br />
controls to mitigate risk.<br />
(b) Implement commander’s intent on acceptance of risk in current operations.<br />
(3) The following list identifies some of the risk management responsibilities of the<br />
primary JTF directorates:<br />
(a) J- 1 (Personnel):<br />
0 Estimate time delay risks on personnel deployment flow.<br />
Determine casualty risks for each COA.<br />
0 Estimate casualty and replacement flow risks on future operations.<br />
Ensure controls for personnel-related activities are conducted to diminish<br />
operations security vulnerabilities and support military deception initiatives.<br />
0 Estimate risks of employed local civilian labor in coordination with the 5-4<br />
(logistics), 5-2 (intelligence), and legal officer.<br />
(b) 5-2:<br />
0 Monitor and report threats that counter the effectiveness of friendly combat<br />
identification/counter-fratricide measures.<br />
0 Develop current regional threat assessments.<br />
0 Determine risk of loss of low-density intelligence collection assets.<br />
(c) 5-3 (Operations):<br />
0 Develop risk assessment for the commander’s estimate.<br />
<strong>11</strong>1-4
Perform as staff proponent for combat identificatiodcounter-fratricide<br />
measures. Develop policy, procedures and assign responsibility for combat<br />
identificatiodcounter-fratricide measures.<br />
Report and investigate reports of fratricides.<br />
0 Develop risk assessment of military and political aspects of draft ROE and<br />
supplemental ROE.<br />
Determine criticality and vulnerability of bases in the Joint Rear Area to<br />
prioritize controls and levels of response.<br />
(d) 5-41<br />
Make recommendations to the JTF commander on the combat<br />
identificatiodcounter-fratricide technology acquisition and procurement strategies.<br />
Assess the risk of critical supply levels not meeting required number of days<br />
of supply days.<br />
0 Determine petroleum, oils, and lubricants storage site vulnerabilities and<br />
controls.<br />
Determine munitions storage site vulnerabilities and safety requirements.<br />
(e) 5-5 (Plans):<br />
0 Integrate functional directorate risk management controls and combat<br />
identification/counter-fratricide measures into deliberate planning products.<br />
0 Identify friendly maneuver and firepower vulnerabilities during mission<br />
analysis, wargaming and plan controls to mitigate risk.<br />
(f) J-6 (Communications): Responsible for assessing risk to geospatial<br />
information and services systems and developing controls to counter threats.<br />
(g) Special staff offices: <strong>Risk</strong> management should be addressed in the various<br />
special staff offices, including-<br />
* Surgeon (health and nonbattle injury, return to duty policy, preventative<br />
medicine).<br />
0 Legal officer (Uniform Code of Military Justice, law of armed conflict, and<br />
host nation (HN) law).<br />
0 Public affairs officer (media coverage, public opinion, etc.).<br />
Safety officer.<br />
d. Individuals.<br />
(1) An individual's level of expertise and maturity influences risk management<br />
proficiency. Managing risk is subjective because its basis is individual judgment.<br />
Inexperienced service members are routinely charged with executing risk controls and risk<br />
reduction measures. Their limited experience can significantly increase the level of risk<br />
they are willing to accept. Their sense of indestructibility, motivation (esprit de corps), and<br />
willingness to achieve the mission at any cost can lead to failure to consider risks. Due to<br />
inexperience or complacency, they may become susceptible to-<br />
(a) Overestimating their ability to respond to, or recover from, a hazardous<br />
incident-they become overconfident.<br />
(b) Underestimating the level of risk posed by a threat. It is imperative that<br />
individuals understand and execute controls directed by leaders and staffs.<br />
<strong>11</strong>1-5
(2) Individuals should be aware of, and fully understand, the situation, and<br />
maintain self-discipline when they perform their duties. They should-<br />
(a) Understand and apply risk management.<br />
(b) Execute controls directed by their leaders, that is, perform to standards.<br />
(c) Carry risk management over into all activities-both on and off duty.<br />
(d) Look out for others-anyone has authority to halt something that is<br />
inherently unsafe.<br />
3. Integration into Training and Operations<br />
a. Integrating risk management into training and operations-<br />
(1) Preserves the lives and well-being of everyone.<br />
(2) Conserves equipment, facilities, environmental resources, and combat power.<br />
b. <strong>Risk</strong> management is planned up front, not treated as an afterthought. Leaders and<br />
managers of materiel acquisition, base operations, and industrial operations budget risk<br />
control costs up front at the level of expected payback over the duration of the activity, or<br />
the life cycle of materiel/weapons system.<br />
c. When integrating risk management into sustained operations, leaders consider<br />
increases in turbulence, personnel turnover, critical skill atrophy, and mission<br />
development. Leaders continuously assess-<br />
(1) The complexity of mission development and associated changing<br />
interrelationships with other agencies.<br />
(2) The inclusion of civilian contractors, such as logistics civilian augmentation<br />
programs, as part of the force.<br />
(3) The presence of the media, NGOs, and PVOs. These diverse elements need to be<br />
integrated into the risk management process.<br />
d. A key consideration relevant to managing risk in complex operational environments<br />
is understanding the culture of the indigenous population or society and its way of doing<br />
business. Leaders consider the impact of interference with the indigenous population’s way<br />
of life and local customs. Such interference could risk damage to relationships and increase<br />
the potential for introducing instability into the local society. Leaders do not, however,<br />
intentionally allow these considerations to endanger their force or its mission.<br />
e. Leaders and service members systematically provide observations and assessments<br />
of the unit’s risk management performance for the training management cycle and SOPS.<br />
They should have the skills, knowledge, and attitude to manage risks inherent in all<br />
operations effectively. Effective training helps service members become proficient. It<br />
qualifies them technically and tactically, and as leaders, to accomplish the mission without<br />
unnecessary risk.<br />
f. Unit leaders and their staffs continually assess and evaluate the integration of risk<br />
management into short-, near-, and long-term training plans. They continually review Joint<br />
Mission Essential Task Lists to ensure that training is supported by realistic risk<br />
management objectives. The services consider past experiences to avoid repeating mistakes.<br />
4. Review of the <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
a. Reviewing the risk management process determines a unit’s current level of<br />
proficiency in implementing the process. How well risk is managed affects readiness.<br />
Leaders need to know the current status and effectiveness of their unit’s risk management<br />
<strong>11</strong>1-6
program. Reviewing the unit’s effectiveness in managing risk permits the unit to gain<br />
insight into areas for improvement and obtain feedback on subordinates’ understanding<br />
and application of risk guidance. The objective is to determine how-<br />
(1) Effectively risk management is embedded into planning and preparing for<br />
operations.<br />
(2) Well subordinate leaders and service members understand risk management.<br />
(3) Effectively risk management is used to execute operations. Leaders assess the<br />
effectiveness of their units by reviewing how well threats are identified and risk controls<br />
are-<br />
(a) Specified in oral and written OPORDs, OPLANs, and SOPS.<br />
(b) Communicated to lowest level of chain of command.<br />
(c) Included in short-, near-, and long-term training plans.<br />
(d) Implemented into all activities, on and off duty.<br />
(e) Embedded into force protection programs.<br />
(f) Included in AARs and captured in lessons learned.<br />
b. <strong>Risk</strong> management cannot be seen as a competitive program whereby a unit or leader<br />
is judged or compared in a competitive sense. Focus is strictly on both reduction of risk and<br />
hazardous incidents.<br />
<strong>11</strong>1-7
Appendix A<br />
<strong>Risk</strong> <strong>Management</strong> Tools<br />
Commanders, leaders, and staffs use risk management tools to facilitate the risk<br />
management process-identification of threats and development of controls. The tables and<br />
matrices in this appendix are samples of tools that commanders, leaders and staffs may use<br />
when integrating the risk management process. It is impractical to create detailed<br />
procedures to ensure the “right” tools are used for each activity and every contingency.<br />
However, choosing the best tools is important when planning a potentially hazardous<br />
operation. Most tools in this appendix can be used in a variety of creative ways: the user<br />
selects the appropriate tool, or combination of tools, and the extent of effort to expend on<br />
each. Since there are no right or wrong selections, the user must rely on his knowledge and<br />
experience to make the right choice for each situation.<br />
Annex A: <strong>Risk</strong> <strong>Management</strong> Worksheet<br />
Annex B: Force Protection Priority Matrix<br />
Annex C: Force Protection Tasks, Conditions, Desired Effects and Activities<br />
Annex D: <strong>Risk</strong> Assessment Matrix<br />
Annex E: Sample <strong>Risk</strong> Control Option Planning Matrix<br />
A- 1<br />
-
Annex A<br />
<strong>Risk</strong> <strong>Management</strong> Worksheet<br />
The risk management worksheet provides a starting point to track the process of<br />
threats and risks logically. It can be used to document risk management steps taken during<br />
planning, preparation, and execution.<br />
Mission<br />
Date Worksheet Prepared<br />
Phases<br />
identify Threats<br />
Assess<br />
Threats<br />
Threats Causes Initial RAC Develop Controls<br />
Develop <strong>Risk</strong> Controls and Implement Supervise<br />
Make <strong>Risk</strong> Decisions<br />
Controls<br />
Residual How to How to<br />
RAC Implement Supervise<br />
Personnel<br />
Training<br />
Initial<br />
Religious<br />
First line<br />
Protesters Medium awareness, Low Civil Affairs,<br />
entry<br />
belief<br />
supervisors<br />
cantonment area<br />
perimeter fencing<br />
Initial<br />
Water<br />
Immunize Predeployment Component<br />
Diseases<br />
High<br />
Low<br />
entry<br />
airborne<br />
field sanitation actions, training commanders<br />
Increase security<br />
Lodgment 1 Pilferage 1 Local I High<br />
I Medium I Augment force J-314<br />
expansion<br />
economy<br />
force<br />
Air<br />
Airfield takedown<br />
Lodgment Defense Deny<br />
High Direct action Medium 1st Ranger J-3<br />
expansion Artillery airfield<br />
Battalion<br />
Battery (-)<br />
Accept <strong>Risk</strong>s YesINo<br />
Comm with HigherNes No<br />
Legend: RAC<strong>Risk</strong> Assessment Code<br />
Figure A-A-I. Sample Completed <strong>Risk</strong> <strong>Management</strong> Worksheet<br />
A-A- 1
Annex B<br />
Force Protection Priority Matrix<br />
This matrix prioritizes force protection tasks and operating systems used for protection<br />
in each task. It reverses the normal targeting methodology and focuses the Joint Planing<br />
Group on what it needs to protect for each specific task.<br />
Priority<br />
1<br />
Maneuver<br />
2<br />
Command and Control<br />
3<br />
4<br />
5<br />
6<br />
Key:<br />
PD-Prevent<br />
PN-Prevent<br />
PS-Prevent<br />
Destruction<br />
Neutralization<br />
Suppression<br />
Legend:<br />
CSSA-combat service support area<br />
FOB-forward operating base<br />
JLOTS-joint logistics over the shore<br />
MEB-Marine Expeditionary Brigade<br />
TACC-Tactical Air Command Center<br />
UAV-unmanned aerial vehicle<br />
Figure A-B-I. Sample Force Protection Priority Matrix<br />
A-B-I
~ ~~~ ~ ~<br />
~~~<br />
Annex C<br />
Force Protection Tasks,<br />
Conditions, Desired Effects, and Activities<br />
Troop-to-task analysis may reveal deficiencies that require risk assessment and<br />
subsequent adjustments. The following table is a sample analysis that draws out the logical<br />
consequences of a force protection task. It can also be rendered as a decision tree. During<br />
COA development, each member of the joint planning group needs to be able to justify the<br />
tasking of resources to support force protection tasks.<br />
Table A-C-1.<br />
Sample Force Protection Tasks, Conditions, Desired Effects, and Activities<br />
Force Protection Task<br />
Maintain security of vital areas<br />
Minimize losses<br />
Force Protection Condition<br />
GMF remains fully operational during H-hour to H+24<br />
Rapid evacuation of casualties<br />
Force Protection Desired Effect<br />
GMF site safe from local attack and from effects of weapons of mass destruction<br />
Air MEDEVAC less than 20 minutes<br />
Surface MEDEVAC to regimental aid stations only<br />
Force Protection Activities<br />
Local security in place<br />
TCF prepared to respond to level Ill threat<br />
TBMD coverage includes GMF site<br />
Task MAW to dedicatelconfigure 2 CH-46 for air MEDEVAC during H+10 - H+ 24<br />
Ensure adequacy of Class Vlll prior to H + 10<br />
Legend:<br />
GMF-Ground Mobile Force<br />
MAW-Marine Air Wing<br />
MEDEVAC-medical evacuation<br />
TBMD-theater ballistic missile defense<br />
TCF-Tactical Combat Force<br />
A-C- 1
Annex D<br />
<strong>Risk</strong> Assessment Matrix<br />
The <strong>Risk</strong> Assessment Matrix combines severity and probability estimates to form a risk<br />
assessment for each threat. Use the <strong>Risk</strong> Assessment Matrix to evaluate the acceptability<br />
of a risk, and the level at which the decision on acceptability will be made. The matrix may<br />
also be used to prioritize resources, to resolve risks, or to standardize threat notification or<br />
response actions. Severity, probability, and risk assessment should be recorded to serve as<br />
a record of the analysis for future use.<br />
Figure A-D-1. <strong>Risk</strong> Assessment Matrix<br />
I. <strong>Risk</strong> Definitions<br />
a. E - Extremely High <strong>Risk</strong>: Loss of ability to accomplish the mission if threats occur<br />
during mission. A frequent or likely probability of catastrophic loss (IA or IB) or frequent<br />
probability of critical loss (IIA) exists.<br />
b. H - High <strong>Risk</strong> Significant degradation of mission capabilities in terms of the<br />
required mission standard, inability to accomplish all parts of the mission, or inability to<br />
complete the mission to standard if threats occur during the mission. Occasional to seldom<br />
probability of catastrophic loss (IC or ID) exists. A likely to occasional probability exists of a<br />
critical loss (IIB or IIC) occurring. Frequent probability of marginal losses (IIIA) exists.<br />
c. M - Moderate <strong>Risk</strong>: Expected degraded mission capabilities in terms of the<br />
required mission standard will have a reduced mission capability if threats occur during<br />
mission. An unlikely probability of catastrophic loss (IE) exists. The probability of a critical<br />
loss is seldom (IID) . Marginal losses occur with a likely or occasional probability (IIIB or<br />
IIIC). A frequent probability of negligible (IVA) losses exists.<br />
d. L - Low <strong>Risk</strong> Expected losses have little or no impact on accomplishing the<br />
mission. The probability of critical loss is unlikely (IIE), while that of marginal loss is<br />
seldom (IIID) or unlikely (HIE). The probability of a negligible loss is likely or less (IVB<br />
through (IVE).<br />
A-D-1
~~<br />
2. Severity Categories<br />
The following table outlines severity categories:<br />
Table A-D-I<br />
<strong>Risk</strong> Severity Categories<br />
Category<br />
CATASTROPHIC (I)<br />
CRITICAL (<strong>11</strong>)<br />
MARGINAL (<strong>11</strong>1)<br />
NEGLIGIBLE (IV)<br />
Definition<br />
Loss of ability to accomplish the mission or mission failure. Death or permanent<br />
disability. Loss of major or mission-critical system or equipment. Major property<br />
(facility) damage. Severe environmental damage. Mission-critical security failure.<br />
Unacceptable collateral damage.<br />
Significantly degraded mission capability, unit readiness, or personal disability.<br />
Extensive damage to equipment or systems. Significant damage to property or the<br />
environment. Security failure. Significant collateral damage.<br />
Degraded mission capability or unit readiness. Minor damage to equipment or<br />
systems, property, or the environment. Injury or illness of personnel.<br />
Little or no adverse impact on mission capability. First aid or minor medical<br />
treatment. Slight equipment or system damage, but fully functional and serviceable.<br />
Little or no property or environmental damage.<br />
3. Probability Categories<br />
The following table outlines probability categories for the risk assessment matrix:
~~~ ~<br />
Element Exposed<br />
Table A-D-2<br />
Probability Definitions<br />
Definition<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurs very often in service life. Expected to occur several times over duration<br />
of a specific mission or operation.<br />
Occurs continuously during a specific mission or operation, or over a service<br />
life.<br />
Occurs very often. Expected to occur several times during mission or operation.<br />
Occurs continuously during a specific mission or operation.<br />
Single item<br />
Fleet or inventory of items<br />
Occurs several times in service life. Expected to occur during a specific mission<br />
or operation.<br />
Occurs at a high rate, but experienced intermittently (regular intervals, generally<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
Occurs some time in service life. May occur about as often as not during a<br />
specific mission or operation.<br />
Occurs several times in service life.<br />
Occurs over a period of time. May occur during a specific mission or operation,<br />
but not often.<br />
Occurs sporadically (irregularly, sparsely, or sometimes).<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurs in service life, but only remotely possible. Not expected to occur during<br />
a specific mission or operation.<br />
Occurs as isolated incidents. Possible to occur some time in service life, but<br />
rarely. Usually does not occur.<br />
Occurs as isolated incident. Remotely possible, but not expected to occur<br />
during a specific mission or operation.<br />
Occurs rarely within exposed population as isolated incidents.<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurrence not impossible, but can assume will almost never occur in service<br />
life. Can assume will not occur during a specific mission or operation.<br />
Occurs very rarely (almost never or improbable). Incidents may occur over<br />
service life.<br />
Occurrence not impossible, but may assume will not occur during a specific<br />
mission or operation.<br />
Occurs very rarely, but not impossible.<br />
A-D-3
Annex E<br />
Sample <strong>Risk</strong> Control Options Planning Matrix<br />
This matrix combines risk control options and responsible personnel that appear<br />
suitable and practical with potential options. Many of these options may be applied at more<br />
than one level. For example, the training option may be applied to operators, supervisors,<br />
senior leaders, or staff personnel.<br />
OPTIONS I OPERATOR<br />
ENGINE E R<br />
Limit energy X X X<br />
Substitute safer form<br />
LEADER STAFF COMMANDER<br />
Rechannel/separate in time/space<br />
X<br />
Provide special maintenance of controls X X X<br />
X<br />
Figure A-E-1. Sample <strong>Risk</strong> Control Options Planning Matrix<br />
A-E-1
Option<br />
Limit energy<br />
Substitute safer form<br />
Prevent release<br />
Separate<br />
Provide special maintenance of<br />
controls<br />
Core Tasks (especially critical tasks)<br />
Leader tasks<br />
Emergency contingency tasks<br />
Rehearsals<br />
Briefings<br />
Mental criteria<br />
Emotional criteria<br />
Physical criteria<br />
Experience<br />
Number of people or items<br />
Emergency medical care<br />
Personnel<br />
Facilitieslequipment<br />
Barrier<br />
On human or object<br />
Raise threshold (harden)<br />
Time<br />
Signslcolor coding<br />
Audiolvisual<br />
Sequence of events (flow)<br />
Timing (within tasks, between tasks)<br />
Simplify tasks<br />
Reduce task loads<br />
Backout options<br />
Contingency capabilities<br />
Emergency damage control<br />
procedures<br />
Backupdredundant capabilities<br />
Mission capabilities<br />
Table A-E-I<br />
Examples of <strong>Risk</strong> Control Options<br />
Example<br />
ENGINEER<br />
Small amount of explosives, reduce speeds<br />
Use air power, precision guided munitions<br />
Containment, double/triple containment<br />
Barriers, distance, boundaries<br />
Special procedures, environmental filters<br />
EDUCATIONAL<br />
Define critical minimum abilities, train<br />
Define essential leader tasks and standards, train<br />
Define, assign, train, verify ability<br />
Validate processes, validate skills, verify interfaces<br />
Refresher warnings, demonstrate threats, refresh training<br />
ADMINISTRA TlVE<br />
Essential skills and proficiency<br />
Essential stability and maturity<br />
Essential strength, motor skills, endurance, size<br />
Demonstrated performance abilities<br />
Only expose essential personnel and items<br />
Medical facilities, personnel, medical evacuation<br />
Replace injured personnel, reinforce units, reallocate<br />
Restore key elements to service<br />
PHYSICAL<br />
Between revetments, walls, distance, ammunition storage facility<br />
Personal protective equipment, energy absorbing materials<br />
Acclimatization, reinforcement, physical conditioning<br />
Minimize exposure and number of iterationslrehearsals<br />
Warning signs, instruction signs, traffic signs<br />
Identification of friendly forces, chemical/biological attack warning<br />
OPERA TlONAL<br />
Put tough tasks first before fatigue, do not schedule several tough<br />
tasks in a row<br />
Allow sufficient time to perform, practice, and time between tasks<br />
Provide job aids, reduce steps, provide tools<br />
Set weight limits, spread task among many<br />
Establish points where process reversal is possible when threat is<br />
detected<br />
Combat search and rescue, rescue equipment, helicopter rescue,<br />
tactical combat force<br />
Emergency responses for anticipated contingencies, coordinating<br />
agencies<br />
Alternate ways to continue the mission if primaries are lost<br />
Restore ability to perform the mission<br />
A-E-2
~<br />
I. Purpose<br />
Appendix B<br />
Force Protection Working Group<br />
The purpose of the force protection working group (FPWG) is to review threats, identify<br />
vulnerabilities, recommend counter-measures, determine force protection levels, assess in<br />
place measures, review tasks to components, monitor corrective actions, and direct special<br />
studies (force protection assessment teams). The primary responsibility is to monitor and<br />
assess the risk and threats to forces in the joint operations area and implement risk<br />
controls to maintain the protection of the force. Each command and control node, rear,<br />
intermediate support base, or FOB, should have a FPWG.<br />
2. Group Composition<br />
The composition will vary based on the threats and forces available. Suggested potential<br />
sources to provide representatives to the FPWG are listed in Figure B-1 .<br />
Chief of Staff<br />
Personnel<br />
Intelligence<br />
Operations<br />
Logistics<br />
Plans<br />
Communications<br />
Engineer<br />
Aviation<br />
Senior Enlisted Representative<br />
Public Affairs<br />
Surgeon<br />
Nuclear, Biological, and Chemical<br />
Chaplain<br />
Staff Weather Officer<br />
Safety<br />
Political Advisor<br />
Host Nation Support Representative<br />
BOTTOM LINE: Composition is Mission Dependent<br />
Figure 6-1. Potential Sources for the FPWG<br />
Army Forces<br />
Marine Forces<br />
Air Force Forces<br />
Navy Forces<br />
Special Operations Forces<br />
Security Forces<br />
Judge Advocate General<br />
I<br />
3. Procedures<br />
The group may meet daily, weekly, or on-call in the vicinity of the Joint Operations<br />
Center to use the risk management process.<br />
4. Agenda<br />
The officer in charge of the command and control node or a designated representative<br />
should chair the meetings. The chairperson for the FPWG is not necessarily designated by<br />
duty position, but based on the ability of the person to fulfill the duties of force protection<br />
officer. A recommended agenda for conducting FPWG meetings follows:<br />
a. Start with updates from-<br />
(1) 52 Representative: intelligence update with focus on changes to the situation<br />
that may lead to additional threats for the force.<br />
(2) Counterintelligence (CI) representative: follows the 52, clarifies and provides<br />
details of current risks based on his field reports.<br />
(3) 53 Representative: overview of current operations and force protection measures<br />
currently in place.<br />
B- 1
. Next, update new or evolving threats. This is an open discussion by functional area.<br />
For example, the surgeon would focus on medical health of command, the veterinary on new<br />
or changing food sources, etc. Steady state activities are raised during this phase of the<br />
meeting. All members consider emerging trends and determine if new vulnerabilities<br />
within their area of responsibility require the focus of the task force or if they are just<br />
isolated incidents. Each member comes to the meeting with documented concerns and<br />
recommendations.<br />
c. When new threats are identified, the FPWG will discuss measures to reduce the<br />
threat. For example, Threat identified: current route from billeting area to the Joint<br />
Operations Center is dangerous and not acceptable at night. Control: CI team will contact<br />
the country team, identify alternate routes, and drive and assess the routes. At the next<br />
FPWG meeting a decision will be made to change route.<br />
d. Once controls are decided upon (above example, CI to conduct a reconnaissance of a<br />
new route), that information is captured by the 53 representative and placed, as a directive<br />
for action, in the next fragmentary order.<br />
e. Following identification and development of controls for new threats, the group will<br />
review current measures in effect against known threats and determine the requirement<br />
for any changes or adjustments. Figure B-2 is an example FPWG agenda.<br />
I Event I Input I<br />
I Threat Situation Review I J2 I<br />
Current Force Protection Levels<br />
Current Operations<br />
Results of Previous Meeting<br />
Recommend Force Protection Level<br />
Recommend Taskings<br />
Summary<br />
Confirm Next Meeting<br />
J3<br />
J3<br />
Components, 53<br />
I Threat Identification I FPWG I<br />
I Vulnerability Identification 1 FPWG<br />
I Identify Controls I FPWG<br />
I<br />
I<br />
FPWG<br />
FPWG<br />
J3<br />
J3<br />
5. Assessment Teams<br />
To maintain visibility of threats, the FPWG may designate assessment teams to<br />
monitor the situation continuously. These teams may be tailored to review specific threats<br />
(such as preventive medicine and surgeon for medical, CI and Provost Marshal/Security<br />
OfficerEhief Security Forces for perimeter security). These teams may be assigned and<br />
operate at all operating bases throughout the joint operations area.<br />
a. The assessment teams mission includes-<br />
(1) Identify and assess threats and vulnerabilities.<br />
(2) Recommend controls.<br />
8-2
(3) Report through FPWG to Commander of the JTF.<br />
(4) Gather information.<br />
b. Assessment teams may use the following checklist:<br />
threats?<br />
(1) Threat.<br />
(a) What is the terrorist threatlcapability?<br />
(b) What is the in-country leave and pass policy?<br />
(c) Are there any areas service members should avoid due to criminal or terrorist<br />
(d) What is the pre-disposition of the local populace to Americans (is it safe for<br />
service members to mix with public)?<br />
(e) Could operations be affected by civil disturbances protesting U.S. policy?<br />
(f) What criminal threats are likely to threaten operations (are there any threats<br />
of pilferage affecting sustainment operations)?<br />
(g) What is the relationship of local population with host nation (HN) authorities<br />
(is there any threat of civil unrest that could affect operations)?<br />
(h) Are there other threats such as para-military organizations or hostile<br />
intelligence that may target operations?<br />
(2) Facilities.<br />
(a) What facilities will the task force occupy?<br />
Tent city vs. hard site?<br />
Location-urban or rural?<br />
(b) What is the status of-<br />
* Perimeters?<br />
Barriers?<br />
Lighting?<br />
Motor pool facilities?<br />
(c) Will the node collocate with HN or friendly forces?<br />
(d) Is secure storage available for arms, ammunition, and explosives and<br />
classified, high dollar, and sensitive items?<br />
(e) Are there high-speed avenues of approach?<br />
(0 What checkpoints and barriers are necessary to control compound access?<br />
(3) Where will mission-essential vulnerable areas be established for arms,<br />
ammunition, and explosives storage; sensitive item storage: pilferable high dollar value<br />
item storage: fuel storage etc.?<br />
(a) What is their proximity to the perimeter?<br />
(b) What is their vulnerability to attack or observation?<br />
(4) Will the task force operate any sustainment operations facilities at air, sea, or<br />
rail ports?<br />
(5) Joint Operations.<br />
8-3
(a) If the task force occupies facilities with HN or friendly forces, who has<br />
command and control for force protection?<br />
(b) Who must the task force coordinate with concerning force protection, HN,<br />
friendly forces?<br />
(c) What are capabilities of friendly forces, HN armed forces, HN police forces,<br />
and HN security forces?<br />
(d) How are in-place friendly forces approaching force protection?<br />
(e) What historical problems have in-place friendly forces had concerning<br />
criminal activity (such as pilferage, assaults, terrorist threat, civil disturbance, and hostile<br />
intelligence)?<br />
(f)<br />
What threats do they perceive as possible?<br />
(g) What operations security measures are in effect?<br />
(h) What movement security measures are in effect?<br />
6. FPWG Products<br />
Based on the FPWG meeting, there are three suggested deliverables.<br />
a. First-an update to the Force Protection Matrix. This should be briefed to the JTF<br />
commander and placed on the SECRET Internet Protocol Router Network for the staff and<br />
components. Figure B-3 is an example of the risk considerations matrix.<br />
b. Second-Fragmentary Order directing execution of the new FPWG measures.<br />
c. Third - risk assessment for the current phase of the operation.<br />
d. Force protection assessment-continuous process throughout the conduct of the<br />
operation.<br />
8-4
Operational<br />
Operating<br />
System<br />
Movement/<br />
Maneuver<br />
Event: JTF FOB<br />
Threat<br />
Local faction<br />
stablishment loca; )n /component: FC<br />
Vulnerability<br />
Troop movement<br />
Route to hotel<br />
Countermeasure<br />
Minimize<br />
Standard route/<br />
Alternate routes<br />
!<br />
Action<br />
Adjust battle rhythm<br />
All drivers with<br />
alternate route maps<br />
Aircraft<br />
Crossing flight<br />
lines<br />
Do not cross<br />
Intelligence<br />
Accident<br />
Civil rights<br />
Know embassy<br />
numbers<br />
Accident card<br />
USAF security patrols<br />
post speed limit<br />
Speeding flight line<br />
Pedestrians<br />
Slow speed<br />
(15 mph)<br />
LNOs brief forces<br />
Fires<br />
Loitering<br />
ThefVbad press<br />
Minimum<br />
presence in hotel<br />
Place of duty or room<br />
Sustainment<br />
Fire Threats<br />
Personnel and<br />
equipment<br />
Know route,<br />
exiting and alert<br />
procedure<br />
Fire break around<br />
FARP<br />
No help/assist<br />
Personnel<br />
stranded<br />
Blood chits<br />
Order 500 chits<br />
Command and<br />
Control<br />
Protection<br />
Personnel<br />
accountability/<br />
location<br />
Heat<br />
Unsafe location/<br />
Unknown location<br />
Injury<br />
Frequent<br />
reporting, improve<br />
communication<br />
Water discipline<br />
Command emphasis<br />
Distribute cell phones<br />
Monitor WGBT<br />
Disease-malaria<br />
Health<br />
Buddy check<br />
Field sanitation<br />
Take pills<br />
Clean latrines<br />
Dogs<br />
Injury/health<br />
Caution<br />
Stay clear<br />
Legend:<br />
FARP-forward arming and refueling point<br />
LNO-liaison officer<br />
mph-miles per hour<br />
USAF-US. Air Force<br />
WGBT-wet globe bulb temperature<br />
Notes.<br />
Any changes made by the FPWG are highlighted.<br />
An additional column labeled "Assessment" can show how the countermeasures are working<br />
Figure 8-3. Sample <strong>Risk</strong> Considerations Matrix<br />
B-5
-<br />
REFERENCES<br />
National<br />
Presidential Decision Directive 39, U.S. Policy on Counterterrorism, 2 1 June 1995<br />
Department of Defense<br />
DODI 6055.1, DUD Safety and Occupational Health (SOH) Program, 19 August 1998<br />
Joint<br />
CJCSM 3500.03, Joint Training Manual for the Armed Forces of the United States, 1 June<br />
1996<br />
CJCSM 3500.04, Universal Joint Task List, 1 November 1999<br />
CJCSM 3500.05, Joint Task Force Headquarters Master Training Guide, 15 April 1997<br />
JP 1-02, Department of Defense Dictionary of Military and Associated Terms, 1 <strong>September</strong><br />
2000<br />
JP 3-0, Doctrine for Joint Opemtions, 1 February 1995<br />
JP 3-10, Joint Doctrine for Rear Area Operations, 28 May 1996<br />
JP 3- 1 1, Joint Doctrine for Operations in Nuclear, Biological, and Chemical (NBC)<br />
Environments, <strong>11</strong> July 2000<br />
JP 3- 13.1, Joint Doctrine for Command and Control Warfare (CZW, 7 February 1996<br />
JP 3-54, Joint Doctrine for Operations Security, 24 January 1997<br />
JP 3-58, Joint Doctrine for Military Deception, 31 May 1996<br />
JP 4-0, Doctrine for Logistics Support of Joint Operations, 6 April 2000<br />
JP 5.00.1, Joint Tactics, Techniques, and Procedures for Joint Campaign Planning (Draft)<br />
JP 5-00.2, Joint Task Force (JTF) Planning Guidance and Procedures, 13 January 1999<br />
Air Force<br />
AFDD 2-4.1, Force Protection, 29 October 1999<br />
AFPD 90-9, Operational <strong>Risk</strong> <strong>Management</strong>, 1 April 2000<br />
AFI 90-901, Operational <strong>Risk</strong> <strong>Management</strong>, 1 April 2000<br />
AFPAM 90-902, Operational <strong>Risk</strong> <strong>Management</strong> Guidelines and Tools, 14 December 2000<br />
Army<br />
FM 3-0 (FM 100-5), operations, 14 June 1993<br />
FM 3-07 (FM 100-ZO), Military Operations in Low Intensity Conflicts, 5 December 1990<br />
FM 3-07.3 (FM 100-23), Peace Operations, 30 December 1994<br />
FM 3-58 (FM 90-2), Battlefield Deception, 3 October 1988<br />
FM 6-22 (FM 22-loo), Army Leadership, 31 August 1999<br />
FM 3-21.10 (FM 7-10), TheInfantryRifle Company, 31 October 2000<br />
FM 7-10 (FM 25-101), Battle Focused Training, 30 <strong>September</strong> 1990<br />
References- 1
Coast Guard<br />
COMMANDANT INSTRUCTION 3500.3 Operational <strong>Risk</strong> <strong>Management</strong> (Draft)<br />
Marine Corps<br />
Marine Corps Order 3500.27, Operational <strong>Risk</strong> <strong>Management</strong>, 3 April 1997<br />
ALMAR 210/97, Operational <strong>Risk</strong> <strong>Management</strong>, 15 July 1997<br />
MCDP-1, Warfighting, June 1997<br />
MCDP 1-2, Campaigning, August 1997<br />
MCWP 3-22, Antiair Warfare, 23 June 2000<br />
MCWP 5-1, Marine Corps Planning <strong>Process</strong>, January 2000<br />
Navy<br />
OPNAVINST 3500.38, Universal Naval Task List, 30 <strong>September</strong> 1996<br />
OPNAVINST 3500.39, Operational <strong>Risk</strong> <strong>Management</strong>, 3 April 1997<br />
References-2
Glossary<br />
PART I-ABBREVIATIONS<br />
AND ACRONYMS<br />
5 -M<br />
AAR<br />
AFB<br />
AFDC<br />
AFTTP<br />
AL<br />
ALSA<br />
APO<br />
CAC<br />
CADD<br />
Cdr<br />
CI<br />
COA<br />
CSSA<br />
DC<br />
DCSPER<br />
DSN<br />
etc<br />
FARP<br />
FM<br />
FOB<br />
FPWG<br />
GMF<br />
man, machine, media, management, mission<br />
A<br />
After Action Report<br />
Air Force Base<br />
Air Force Doctrine Center<br />
Air Force Tactics, Techniques, and Procedures<br />
Alabama<br />
Air Land Sea Application<br />
Army Post Overseas<br />
C<br />
Combined Arms Center<br />
Combined Arms Doctrine Development Center<br />
commander<br />
counterintelligence<br />
course of action<br />
combat service support area<br />
D<br />
District of Columbia<br />
Deputy Chief of Staff for Personnel<br />
Defense Switched Network<br />
E<br />
etcetera<br />
F<br />
forward arming and refueling point<br />
field manual<br />
forward operating base<br />
force protection working group<br />
G<br />
ground mobile force<br />
Glossary-I
HN<br />
HQ<br />
J- 1<br />
5-2<br />
5-3<br />
5-4<br />
5-5<br />
J-6<br />
JLOTS<br />
JOPES<br />
JP<br />
JTF<br />
KS<br />
LNO<br />
MAW<br />
MCCDC<br />
MCPDS<br />
MCRP<br />
MEDEVAC<br />
METT-T<br />
METT-TC<br />
MILSTRIP<br />
MSE<br />
MSTP<br />
H<br />
host nation<br />
headquarters<br />
J<br />
.Manpower and Personnel Directorate of a joint staff<br />
Intelligence Directorate of a joint staff<br />
Operations Directorate of a joint staff<br />
Logistics Directorate of a joint staff<br />
Plans Directorate of a joint staff<br />
Command, Control, Communications, and Computer Systems<br />
Directorate of a joint staff<br />
joint logistics over-the-shore<br />
Joint Operation Planning and Execution System<br />
joint publication<br />
joint task force<br />
K<br />
Kansas<br />
L<br />
liaison officer<br />
M<br />
Marine air wing<br />
Marine Corps Combat Development Command<br />
Marine Corps Publication Distribution System<br />
Marine Corps Reference Publication<br />
medical evacuation<br />
mission, enemy, terrain and weather, troops and support available,<br />
time available<br />
mission, enemy, terrain and weather, troops and support available,<br />
time available, civil considerations (Army)<br />
Military Standard Requisitioning and Issue Procedures<br />
major subordinate element<br />
Marine Air Ground Task Force Training Program<br />
Glossary-2
NAVSOP<br />
NC<br />
NWDC<br />
NGO<br />
NM<br />
OPLAN<br />
OPORD<br />
PD<br />
PN<br />
PS<br />
PVO<br />
RAC<br />
RI<br />
ROE<br />
SOP<br />
TACC<br />
TBMD<br />
TCF<br />
TRADOC<br />
UAV<br />
USAF<br />
USAREUR<br />
USMC<br />
USN<br />
N<br />
Navy Standing Operating Procedure<br />
North Carolina<br />
Navy Warfare Development Command<br />
nongovernmental organization<br />
New Mexico<br />
0<br />
operation plan<br />
operation order<br />
P<br />
prevent destruction<br />
prevent neutralization<br />
prevent suppression<br />
private voluntary organization<br />
R<br />
risk assessment code<br />
Rhode Island<br />
rules of engagement<br />
S<br />
standing operating procedure<br />
T<br />
Tactical Air Command Center<br />
theater ballistic missile defense<br />
tactical combat force<br />
United States Army Training and Doctrine Command<br />
U<br />
unmanned aerial vehicle<br />
United States Air Force<br />
United States Army, Europe<br />
United States Marine Corps<br />
United States Navy<br />
Glossary-3
PART II-TERMS<br />
AND DEFINITIONS<br />
acceptable risk. The portion of identified risk that is allowed to persist without further<br />
controls<br />
assessment. 1. Analysis of the security, effectiveness, and potential of an existing or<br />
planned intelligence activity.<br />
2. Judgment of the motives, qualifications, and characteristics of present or<br />
prospective employees or “agents.” (JP 1-02)<br />
controls. Actions taken to eliminate threats or reduce their risk. This term and its<br />
definition are applicable only in the context of this publication and should not be referenced<br />
outside this publication.<br />
exposure. The frequency and length of time subjected to a hazard (FM 3-100.12/100-14).<br />
extremely high risk. <strong>Risk</strong> that could result in loss of ability to accomplish the mission if<br />
threats occur during mission. A frequent or likely probability of catastrophic loss (IA or IB)<br />
or frequent probability of critical loss (IIA) exists. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
high risk. <strong>Risk</strong> that could result in significant degradation of mission capabilities in terms<br />
of the required mission standard, inability to accomplish all parts of the mission, or<br />
inability to complete the mission to standard if threats occur during the mission. Occasional<br />
to seldom probability of catastrophic loss (IC or ID) exits. A likely to occasional probability<br />
exists of a critical loss (IIB or IIC) occurring. Frequent probability of marginal losses (IIIA)<br />
exists. This term and its definition are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
identified risk. A risk determined by applying severity and probability analysis to an<br />
identified threat.<br />
inherently dangerous. An activity or task containing a danger to life or limb that is a<br />
permanent and inseparable element of the activity. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
low risk. <strong>Risk</strong> that could result in expected losses having little or no impact on<br />
accomplishing the mission. The probability of critical loss is unlikely (IIE), while that of<br />
marginal loss is seldom (IIID) or unlikely (IIIE). The probability of a negligible loss is likely<br />
or less (IVB through IVE). This term and its definition are applicable only in the context of<br />
this publication and should not be referenced outside this publication.<br />
moderate risk. <strong>Risk</strong> that could result in degraded mission capabilities in terms of the<br />
required mission standard will have a reduced mission capability if threats occur during<br />
mission. An unlikely probability of catastrophic loss (IE) exists. The probability of a critical<br />
loss is seldom (IID). Marginal losses occur with a likely or occasional probability (IIIB or<br />
IIIC). A frequent probability of negligible (IVA) losses exists. This term and its definition<br />
are applicable only in the context of this publication and should not be referenced outside<br />
this publication.<br />
operational protection. The conservation of the forces’ fighting potential so that it can be<br />
applied at the decisive time and place. This activity includes actions taken to counter the<br />
enemy’s forces by making friendly forces (including operational formations, personnel, etc.) ,<br />
systems, and operational facilities difficult to locate, strike, and destroy. (CJCSM 3500.04)<br />
Glossary-4
probability. The likelihood that a hazardous incident will occur.<br />
frequent (A): Occurs very often, continuously experienced.<br />
likely (B): Occurs several times<br />
occasional (C): Occurs sporadically<br />
seldom (D): Remotely possible; could occur at some time<br />
unlikely (E): Can assume will not occur, but not impossible.<br />
This term and its definitions are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
residual risk. The level of risk remaining after controls have been identified and selected<br />
for threats that may result in loss of combat power. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
risk. 1. Probability and severity of loss linked to threats.<br />
2. See degree of risk. See also risk management. (JP 1-02)<br />
risk assessment. Identification and assessment of threats: an identified threat is assessed<br />
to determine the risk (both the probability of occurrence and resulting severity) of a<br />
hazardous incident due to the presence of the threat. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
risk decision. The decision to accept or not accept the risks associated with an action:<br />
made by the commander, leader, or individual responsible for performing that action. This<br />
term and its definition are applicable only in the context of this publication and should not<br />
be referenced outside this publication.<br />
risk management. A process by which decision makers reduce or offset risk. Also called<br />
RM. (JP 1-02) The systematic process of identifying, assessing, and controlling risks arising<br />
from operational factors and making decisions that weigh risks against mission benefits.<br />
severity. The intensity of the expected consequence of an event in terms of degree of<br />
injury, property damage, or other mission-impairing factors (loss of combat power and so<br />
on) that could occur.<br />
catastrophic (I): Loss of ability to accomplish the mission or mission failure. Death or<br />
permanent total disability. Loss of major or mission critical system or equipment. Major<br />
property (facility) damage. Severe environmental damage. Unacceptable collateral<br />
damage. Mission-critical security damage.<br />
critical (<strong>11</strong>): Significantly degraded mission capability or unit readiness. Permanent<br />
partial disability. Extensive (major) damage to equipment or systems. Significant<br />
damage to property or the environment. Security failure. Significant collateral damage.<br />
marginal (<strong>11</strong>1): Degraded mission capability or unit readiness. Minor damage to<br />
equipment or systems, property, or the environment.<br />
negligible (IV): Little or no adverse impact on mission capability. Slight equipment or<br />
system damage, but fully functional and serviceable. Little or no property or<br />
environmental damage.<br />
This term and its definitions are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
Glossary-5
threat. A source of danger; any opposing force, condition, source, or circumstance with the<br />
potential to negatively impact mission accomplishment and/or degrade mission capability.<br />
This term and its definition are applicable only in the context of this publication and should<br />
not be referenced outside this publication.<br />
total risk. The sum of identified risk and unidentified risk. It is accepted by the<br />
appropriate decision-maker because further efforts at risk control are not justified by the<br />
perceived gain.<br />
unacceptable risk. The risk that cannot be tolerated and must be eliminated or<br />
controlled.<br />
unidentified risk. The risk that has not been identified. It is unknown or immeasurable.<br />
Glossary-6
Index<br />
A<br />
acceptability, <strong>11</strong>-3, <strong>11</strong>1-4, A-D-1<br />
acceptable loss, 1-1<br />
acceptable risk, I-2,I-3,II-3,<strong>11</strong>-5, <strong>11</strong>1-3, A-D-1, Glossary-4<br />
accountability, I-2,II-5, <strong>11</strong>1-1, B-5<br />
administrative controls, <strong>11</strong>-4, A-E- 1, A-E-2<br />
alarmism, <strong>11</strong>-2<br />
application of risk management, i, I-1,I-3, 1-4, <strong>11</strong>-1<br />
assessment, I-1,I-3, 1-5, <strong>11</strong>-2,<strong>11</strong>-3,<strong>11</strong>-5,<strong>11</strong>-6,<strong>11</strong>-8,<strong>11</strong>-9, <strong>11</strong>1-2, <strong>11</strong>1-4, <strong>11</strong>1-5, <strong>11</strong>1-6, A-1, A-A-1, A-<br />
C-1, A-D- 1, A-D-2, B- 1, B-2, B-3, B-4, B-5, Glossary-3, Glossary-4, Glossary-5<br />
complete, <strong>11</strong>-2<br />
matrix, A-D-1<br />
output, <strong>11</strong>-2<br />
pitfalls, v, <strong>11</strong>-2<br />
teams, B-1<br />
assigning redundant capabilities, <strong>11</strong>-5, A-E- 1, A-E-2<br />
avenues of approach, <strong>11</strong>-9, B-3<br />
avoiding the risk, I-2,II-3, <strong>11</strong>-4, <strong>11</strong>1-3<br />
C<br />
catastrophic, A-D-1, A-D-2, Glossary-4, Glossary-5<br />
chain of command, v, 1-2, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3,<strong>11</strong>1-7<br />
civil consideration, <strong>11</strong>-8,II-10,<strong>11</strong>1-3,<strong>11</strong>1-4,<strong>11</strong>1-6, A-A-1, B-3, B-4, B-5, Glossary-2<br />
climate, <strong>11</strong>-9,<strong>11</strong>1-2<br />
commander, i, v, vi, 1-1, 1-2, I-3,1-5, <strong>11</strong>-3,<strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-8,<strong>11</strong>-9, <strong>11</strong>1-1, <strong>11</strong>1-2,<strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5, A-<br />
1, A-A- 1, A-E- 1, B-3, B-4, Glossary-1 , Glossary-5<br />
complacency, II-lO,III-l, <strong>11</strong>1-4, <strong>11</strong>1-5<br />
complete risk assessment, <strong>11</strong>-2<br />
controls, risk, v, I-2,I-3,1-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-3, <strong>11</strong>-4,<strong>11</strong>-5, <strong>11</strong>-6,II-7, <strong>11</strong>-8,<strong>11</strong>-9,<strong>11</strong>-12,<strong>11</strong>1-1, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3,<strong>11</strong>1-4,<strong>11</strong>1-5,<strong>11</strong>1-6, <strong>11</strong>1-7, A-1, A-A-1, A-E-1, A-E-2, B-1, B-2, Glossary-4, Glossary-5<br />
administrative, <strong>11</strong>-4, A-E-1, A-E-2<br />
avoiding risk, 1-2, <strong>11</strong>-3,II-4, <strong>11</strong>1-3<br />
delay COA, <strong>11</strong>-4<br />
develop, v, 1-3, 1-5, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>1-3, <strong>11</strong>1-5, A-1, A-A-1, B-2<br />
educational, <strong>11</strong>-4, A-E- 1, A-E-2<br />
engineering, <strong>11</strong>-4, A-E-l , A-E-2<br />
implement, v, 1-3, I-5,II-3,II-4.<strong>11</strong>-5,II-6,II-7,II-8,<strong>11</strong>1-4, A-A-1, B-1<br />
operational, <strong>11</strong>-4, A-E-1, A-E-2<br />
options, <strong>11</strong>-3,II-4, A-1, A-E-1, A-E-2<br />
physical, <strong>11</strong>-4, A-E-l , A-E-2<br />
planning matrix, A-E-1<br />
Index-1
edundant capabilities, <strong>11</strong>-4, A-E-1, A-E-2<br />
residual risk, <strong>11</strong>-3.<strong>11</strong>-5, <strong>11</strong>1-3, <strong>11</strong>1-4, A-A-1, Glossary-5<br />
support, v, <strong>11</strong>-3,<strong>11</strong>-6, <strong>11</strong>1-2, <strong>11</strong>1-4<br />
transferring risk, <strong>11</strong>-4<br />
course of action (COA), 1-1, I-3,1-4,II-3,II-4, <strong>11</strong>-5,<strong>11</strong>-8,<strong>11</strong>-9,<strong>11</strong>1-2,<strong>11</strong>1-3, <strong>11</strong>1-4, A-C-1,<br />
Glossary- 1<br />
cover and concealment, <strong>11</strong>-9<br />
crisis action, I-3,II-7, <strong>11</strong>-8<br />
critical, 1-3,II-l, <strong>11</strong>-4, <strong>11</strong>-9.<strong>11</strong>-10, <strong>11</strong>1-1.<strong>11</strong>1-5,<strong>11</strong>1-6, A-D-1, A-D-2, A-E-1, A-E-2, Glossary-4,<br />
Glossary-5<br />
D<br />
decisions, i, v, 1-1, 1-2, 1-3, <strong>11</strong>-3, <strong>11</strong>-5.<strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8,II-12, <strong>11</strong>1-1 <strong>11</strong>1-2, <strong>11</strong>1-3, A-A-1, A-C-1, A-<br />
D-1, B-2, Glossary-5, Glossary-6<br />
delay, <strong>11</strong>-4, <strong>11</strong>1-4<br />
deliberate, 1-3, <strong>11</strong>-2, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>1-5<br />
develop controls, v, 1-3, I-5,II-3, <strong>11</strong>-5, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>1-3, <strong>11</strong>1-5, A-1, A-A-1, B-2<br />
E<br />
enemy, 1-1,<strong>11</strong>-1,<strong>11</strong>-8,<strong>11</strong>-9, Glossary-2, Glossary-4<br />
engineering, <strong>11</strong>-4,II- 1 1, A-E- 1, A-E-2, B- 1<br />
exposure, <strong>11</strong>-4, A-E-2<br />
F<br />
feasibility, 1-2, <strong>11</strong>-3, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-4<br />
feedback, v, 1-2, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>1-2,<strong>11</strong>1-7<br />
force protection, v, 1-1, I-5,<strong>11</strong>1-3,<strong>11</strong>1-7, --1, ---B-l, n-C-l, B-l,B-2, B-4, Glossary-1<br />
activities, A-C-1<br />
agenda, B-1, B-2, B-3<br />
assessment team, B-1, B-2<br />
checklist, B-3<br />
composition, B- 1<br />
conditions, A- 1, A-C- 1<br />
effects, A- 1, A-C- 1<br />
facilities, B-3, B-4<br />
priority matrix, A- 1, A-B- 1<br />
procedures, B- 1<br />
products, B-4<br />
tasks, A-1, A-B-1, A-C-1<br />
force protection working group (FPWG), <strong>11</strong>1-3, B-1, B-2, B-3, B-4, B-5, Glossary-1<br />
forward area refueling point (FARP), B-5, Glossary-1<br />
Index-2
H<br />
high risk, <strong>11</strong>-5, A-A- 1, A-D- 1, Glossary-4<br />
host nation (HN), <strong>11</strong>1-5, B-1, B-3, B-4, Glossary-1<br />
hygienic, <strong>11</strong>- 12<br />
I<br />
identify, i, v, 1-1, 1-2, 1-3, 1-4, <strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-10, <strong>11</strong>1-1, <strong>11</strong>1-3,<br />
<strong>11</strong>1-4, <strong>11</strong>1-5,<strong>11</strong>1-7, A-1, A-A-1, A-B-1, A-E-2, B-1, B-2, Glossary-4, Glossary-5, Glossary-6<br />
impact, mission, probability and severity, I-1,I-3, II-l,II-2, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-10,<strong>11</strong>1-3, <strong>11</strong>1-4, III-<br />
6, A-D-2, Glossary-4, Glossary-5<br />
implementation, i, v, 1-1, 1-2, 1-3, 1-5, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8,<strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-6, <strong>11</strong>1-7,<br />
A-A- 1. B- 1<br />
J<br />
Joint Operation Planning and Execution System (JOPES), i, <strong>11</strong>-7, Glossary-2<br />
joint task force (JTF) i, <strong>11</strong>-7,II-8, <strong>11</strong>1-4,<strong>11</strong>1-5, B-3, B-4, B-5, Glossary-2<br />
K<br />
key aspects, v, 1-1, <strong>11</strong>-6, <strong>11</strong>-9, <strong>11</strong>1-5<br />
L<br />
logistics, <strong>11</strong>-10, <strong>11</strong>-1 1, <strong>11</strong>1-4, <strong>11</strong>1-6, A-B-1, B-1, Glossary-2<br />
loss, 1-1,<strong>11</strong>-2,<strong>11</strong>-4, <strong>11</strong>-8, <strong>11</strong>1-3, <strong>11</strong>1-4, A-C-1, A-D-1, A-D-2, Glossary-4, Glossary-5<br />
low risk, 1-2, <strong>11</strong>-5, <strong>11</strong>1-2, A-A-1, A-D-1, Glossary-4<br />
M<br />
machine, <strong>11</strong>-1, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>,II-12, Glossary- 1<br />
maintenance, 1-3, <strong>11</strong>-9, <strong>11</strong>-10.<strong>11</strong>-<strong>11</strong>, A-E-1, A-E-2<br />
major subordinate element (MSE), <strong>11</strong>-7,II-8, Glossary-2<br />
man, machine, media, management, mission (5-M) model, <strong>11</strong>-1, <strong>11</strong>-6, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>-12, <strong>11</strong>1-2,<br />
Glossary- 1<br />
managing, 1-3,<strong>11</strong>1-1,<strong>11</strong>1-2, <strong>11</strong>1-3.<strong>11</strong>1-5,<strong>11</strong>1-6,<strong>11</strong>1-7<br />
marginal, A-D- 1, A-D-2, Glossary-4, Glossary-5<br />
media, <strong>11</strong>-1, <strong>11</strong>-10, <strong>11</strong>-12.<strong>11</strong>1-5, <strong>11</strong>1-6, Glossary-1<br />
METT-T (mission, enemy, terrain and weather, troops and support available, time<br />
available), <strong>11</strong>-1, <strong>11</strong>-6, <strong>11</strong>-8,II-10, <strong>11</strong>1-2, Glossary-2<br />
METT-TC (mission, enemy, terrain and weather, troops and support available, time<br />
available, civil considerations [Army]) <strong>11</strong>-8, <strong>11</strong>-10, Glossary-2<br />
moderate risk, <strong>11</strong>-5, A-D-1, Glossary-4<br />
N<br />
negligible, A-D- 1, A-D-2, Glossary-4, Glossary-5<br />
0<br />
objective, 1-4, <strong>11</strong>-10, <strong>11</strong>-12, <strong>11</strong>1-3, <strong>11</strong>1-6, <strong>11</strong>1-7<br />
Index-3
observation, <strong>11</strong>-9,<strong>11</strong>1-6, B-3<br />
operational, v, 1-1, <strong>11</strong>-1,II-4, <strong>11</strong>-10, <strong>11</strong>-12,<strong>11</strong>1-3, <strong>11</strong>1-6, A-B-1, A-C-1, A-E-1, A-E-2, B-5,<br />
Glossary-4, Glossary-5<br />
operation order (OPORD), <strong>11</strong>1-4,<strong>11</strong>1-7, Glossary-3<br />
operation plan (OPLAN), <strong>11</strong>1-4,<strong>11</strong>1-7, Glossary-3<br />
operations, military, v, 1-1, 1-2, 1-3, 1-5, <strong>11</strong>-1, <strong>11</strong>-4, <strong>11</strong>-6, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-10, <strong>11</strong>1-1, <strong>11</strong>1-3, <strong>11</strong>1-4, III-<br />
6, <strong>11</strong>1-7, A-1, A-D-3, B-1, B-2, B-3, B-4, Glossary-2<br />
P<br />
performance, <strong>11</strong>-4, <strong>11</strong>-6, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>1-2, <strong>11</strong>1-6, A-E-2<br />
personal, <strong>11</strong>-1, <strong>11</strong>-4, <strong>11</strong>-<strong>11</strong>, A-D-2, A-E-2<br />
physical, 1-1, <strong>11</strong>-4, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>, A-E-1, A-E-2<br />
probability, 1-1, II-l,II-2, <strong>11</strong>-3,II-4,II-5, A-D-1, A-D-2, A-D-3, Glossary-4, Glossary-5,<br />
category, A-D-2<br />
definitions, A-D-3<br />
procedures, i, v, 1-2, 1-3, 1-5, <strong>11</strong>-3, <strong>11</strong>-10, <strong>11</strong>-12, <strong>11</strong>1-4, <strong>11</strong>1-5, A-1, A-E-1, A-E-2, B-1, B-5,<br />
Glossary-1 , Glossary-2, Glossary-3<br />
process, i, v, 1-1, 1-2, I-3,I-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-9, <strong>11</strong>-12,III-l, <strong>11</strong>1-2, <strong>11</strong>1-3,<br />
<strong>11</strong>1-6, A-1, A-A-1, A-E-2, B-1, B-4, Glossary-5<br />
R<br />
residual risks, <strong>11</strong>-3, <strong>11</strong>-5,<strong>11</strong>1-3,<strong>11</strong>1-4, A-A-1, Glossary-5,<br />
responsibilities, i, v, <strong>11</strong>-5, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5, B-1, B-2<br />
commander, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3<br />
leaders, <strong>11</strong>1- 1, <strong>11</strong>1-2<br />
individual, <strong>11</strong>1-5<br />
staff, <strong>11</strong>1-3<br />
risk, i, v, I-1,l-2, 1-3, 1-4, 1-5, II-l,II-2, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5,II-6, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-1 1, <strong>11</strong>1-1, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3, <strong>11</strong>1-4,<strong>11</strong>1-5, <strong>11</strong>1-6, <strong>11</strong>1-7, A-1, A-A-1, A-C-1, A-D-1, A-D-2, A-E-1, A-E-2, B-1, B-4, B-5,<br />
Glossary-3, Glossary-4, Glossary-5, Glossary-6<br />
assessment, <strong>11</strong>2,<strong>11</strong>1-4, A-C- 1, A-D- 1, A-D-2<br />
probability categories, A-D-2<br />
probility definitions, A-D-3<br />
severity categories, <strong>11</strong>-2, A-D-2<br />
unacceptable, I<strong>11</strong> - 3, Glossary-6<br />
unnecessary, I-2,I-3, <strong>11</strong>1-3,<strong>11</strong>1-6<br />
risk management, i, v, I-1,I-2, I-3,1-4,1-5,II-l, <strong>11</strong>-5,II-6,II-7, <strong>11</strong>-8, <strong>11</strong>-10, <strong>11</strong>-12, <strong>11</strong>1-1, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3,<strong>11</strong>1-4, <strong>11</strong>1-5,<strong>11</strong>1-6, <strong>11</strong>1-7, A-1, A-A-1, B-1, Glossary-5<br />
application guidelines, 1-3, <strong>11</strong>1-7<br />
application, i, 1-1, Ii3, <strong>11</strong>-1<br />
assessment, 1-1, <strong>11</strong>-6,<strong>11</strong>1-6<br />
crisis action, 1-3, <strong>11</strong>-7, <strong>11</strong>-8<br />
cycle, 1-4<br />
decisions. <strong>11</strong>-5<br />
Index-4
deliberate, 1-3, <strong>11</strong>-7<br />
execution, <strong>11</strong>-7, <strong>11</strong>-8<br />
feedback, v, 1-2, <strong>11</strong>-6,II-7,<strong>11</strong>1-2, <strong>11</strong>1-7<br />
framework for implementing, 1-2<br />
fundamentals, v, I- 1<br />
goal, v, 1-1<br />
implement, I-2,<strong>11</strong>1-6<br />
integration, v, <strong>11</strong>-7, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-6<br />
key aspects, v, 1-1<br />
levels, 1-3<br />
objective, <strong>11</strong>1-3,<strong>11</strong>1-6, <strong>11</strong>1-7<br />
principles, i, v, 1-2<br />
process, i, v, 1-1, I-2,1-3, 1-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-6, A-1, B-1,<br />
Glossary- 5<br />
review, v, I-3,1-4, <strong>11</strong>-1, <strong>11</strong>-6, <strong>11</strong>-7,<strong>11</strong>-8, <strong>11</strong>1-6, <strong>11</strong>1-7<br />
sequence, 1-3<br />
supervise, 1-3, 1-4, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, A-A-1<br />
training, <strong>11</strong>1-2, <strong>11</strong>1-6<br />
use, I- 1,I-3<br />
worksheet, A-1, A-A- 1<br />
risk management fundamentals, v, I- 1<br />
risk management goal, v, 1-1, <strong>11</strong>-10, <strong>11</strong>1-2<br />
S<br />
services, v, 1-1, <strong>11</strong>-10,<strong>11</strong>1-5, <strong>11</strong>1-6<br />
situational analysis, <strong>11</strong>- 1<br />
supervise and review, 1-3, 1-4, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, A-A-1<br />
T<br />
threat, v, 1-1, I-2,I-3,1-4, <strong>11</strong>-1,II-2,II-3,II-4,II-5,II-6, <strong>11</strong>-7,<strong>11</strong>-8,<strong>11</strong>-9, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>,II-12,<strong>11</strong>1-<br />
1, <strong>11</strong>1-3, <strong>11</strong>1-4, III-5,<strong>11</strong>1-7, A-1, A-A-1, A-C-1, A-D-1, A-E-2, B-1, B-2, B-3, B-4, B-5,<br />
Glossary-4, Glossary-5, Glossary-6<br />
assessment, I-3,<strong>11</strong>1-4<br />
causes, II-l,II-2, A-A-1<br />
checklist, B-3<br />
identification, v, 1-2, I-3,1-4, <strong>11</strong>-1, <strong>11</strong>-3, <strong>11</strong>-5, <strong>11</strong>-7, <strong>11</strong>-8,<strong>11</strong>-9, <strong>11</strong>-10, <strong>11</strong>1-4, A-1, A-A-1, B-2,<br />
Glossary-4, Glossary-5<br />
probability, <strong>11</strong>- 1,<strong>11</strong>-2,<strong>11</strong>-3, A-D- 1, Glossary-5<br />
severity, II-1,<strong>11</strong>-2, <strong>11</strong>-3, Glossary-4, Glossary-5<br />
U<br />
unacceptable risk , <strong>11</strong>1-3, Glossary-6<br />
unnecessary risk, 1-2, 1-3, <strong>11</strong>1-3, <strong>11</strong>1-6<br />
Index-5
FM 3-100.12<br />
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTPU) 3-2.34<br />
15 February 2001<br />
By Order of the Secretary of the Army:<br />
Official:<br />
ERIC K. SHINSEKI<br />
General, United States Army<br />
Chief of Staff<br />
JOEL B. HUDSON<br />
Administrative Assistant to the<br />
Secretary of the Army<br />
0106 101<br />
DISTRIBUTION:<br />
Active Army, Army National Guard, and U.S. Army Reserve: To be distribute in<br />
accordance with the initial distribution number <strong>11</strong> 5840 requirements for FM 3-<br />
100.12.<br />
By Order of the Secretary of the Air Force:<br />
LANCE L. SMITH<br />
Major General, USAF<br />
Commander<br />
Headquarters Air Force Doctrine Center<br />
Air Force Distribution: F
MARINE CORPS: PCN 14400009300
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTP(I) 3-2.34<br />
FEBRUARY 2001<br />
DISTRIBUTION RESTRICTION:<br />
Approved for public release;<br />
distribution is unrestricted
FOREWORD<br />
This publication has been prepared under our direction for use by our respective<br />
commands and other commands as appropriate.<br />
h<br />
U<br />
JOHN N. ABRAMS<br />
General, USA<br />
Commander<br />
Training and Doctrine Command<br />
BRUCE B. KNUTSON, JR.<br />
Lieutenant General, USMC<br />
Commanding General<br />
Marine Corps Combat<br />
Development Command<br />
ROBERT G. SPRIGG<br />
Rear Admiral, USN<br />
Commander<br />
Navy Warfare Development Command<br />
LANCE L. SMITH<br />
Major General, USAF<br />
Commander<br />
Headquarters Air Force Doctrine Center<br />
This publication is available on the General<br />
Dennis J. Reimer Training and Doctrine <strong>Digital</strong><br />
Library at www.adtdl .army. mil
1. Scope<br />
This publication describes risk management functions and responsibilities applicable to<br />
the joint task force (JTF) and service staffs. It applies risk management planning<br />
procedures to the military decision making process and employs the Joint Operation<br />
Planning and Execution System (JOPES) for the operation planning team.<br />
2. Purpose<br />
This publication provides a consolidated multiservice reference addressing risk<br />
management background, principles, and application procedures. To facilitate multiservice<br />
interoperability, this publication identifies and explains the risk management process and<br />
its differences and similarities as it is applied by each service.<br />
3. Applicability<br />
The audience for this publication includes combatant command, JTF, and functional<br />
and service component staffs. The target staff level is the JTF headquarters staff. This<br />
publication serves as a source document for developing service and joint manuals,<br />
publications, and curricula, and may be used as a stand-alone document.<br />
4. Implementation Plan<br />
Participating service command offices of primary responsibility will review this<br />
publication, validate the information, and reference and incorporate it in service and<br />
command manuals, regulations, instructions, and curricula as follows:<br />
Army. The Army will incorporate this publication in U.S. Army training and doctrinal<br />
publications as directed by the Commander, U.S. Army Training and Doctrine Command<br />
(TRADOC). Distribution is in accordance with DA Form 12-99-R.<br />
Marine Corps. The Marine Corps will incorporate the procedures in this publication in<br />
U.S. Marine Corps (USMC) training and doctrinal publications as directed by the<br />
Commanding General, U.S. Marine Corps Combat Development Command (MCCDC).<br />
Distribution is in accordance with Marine Corps Publication Distribution System (MCPDS).<br />
Navy. The Navy will incorporate these procedures in U.S. Navy (USN) training and<br />
doctrinal publications as directed by the Commander, Navy Warfare Development<br />
Command (NWDC). Distribution is in accordance with Military Standard Requisitioning<br />
and Issue Procedures (MILSTRIP) Desk Guide and Navy Standing Operating Procedures<br />
(NAVSOP) Publication 409.<br />
Air Force. The Air Force will validate and incorporate appropriate procedures in<br />
accordance with applicable governing directives. Distribution is in accordance with Air Force<br />
Instruction 33-360, Volume 1.<br />
5. User Information<br />
a. The TRADOC-MCCDC-NWDC-Headquarters (HQ Air Force Doctrine Center<br />
(AFDC) and Air Land Sea Application (ALSA) Center developed this publication with the<br />
joint participation of the approving service commands. ALSA will review and update this<br />
publication as necessary.<br />
b. This publication reflects current joint and service doctrine, command and control<br />
organizations, facilities, personnel, responsibilities, and procedures. Changes in service<br />
MARINE CORPS: PCN 14400009300<br />
i
protocol, appropriately reflected in joint and service publications, will be incorporated in<br />
revisions of this document.<br />
c. We encourage recommended changes for improving this publication. Key your<br />
comments to the specific page and paragraph and provide a rationale for each<br />
recommendation. Send comments and recommendations directly to-
FM 3-100.12<br />
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTP(1) 3-2.34<br />
FM 3-100.12<br />
MCRP 5-12.lC<br />
NTTP 5-03.5<br />
AFTTP(1) 3-2.34<br />
U.S. Army Training and Doctrine Command<br />
Fort Monroe, Virginia<br />
Marine Corps Combat Development Command<br />
Quantico, Virginia<br />
Navy Warfare Development Command<br />
Newport, Rhode Island<br />
Headquarters Air Force Doctrine Center<br />
Maxwell Air Force Base, Alabama<br />
15 February 2001<br />
RISK MANAGEMENT<br />
Multiservice Tactics, Techniques, and Procedures for<br />
<strong>Risk</strong> <strong>Management</strong><br />
TABLE OF CONTENTS<br />
EXECUTIVE SUMMARY ............................................................ ........................................<br />
Chapter I RISK MANAGEMENT FUNDAMENTALS .........................................................<br />
Page<br />
1. Background ............................................................................ ......,................ 1-1<br />
2. <strong>Risk</strong> <strong>Management</strong> Goal ................................................................................. 1-1<br />
3. Key Aspects of <strong>Risk</strong> <strong>Management</strong> ................................................................. 1-1<br />
4. Principles of <strong>Risk</strong> <strong>Management</strong> .................................................................... 1-2<br />
5. Levels of <strong>Risk</strong> <strong>Management</strong> .......................................................................... 1-3<br />
6. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Overview ............................................................ 1-3<br />
7. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Application Guidelines.. . . ....... ..... ........... ...... 1-3<br />
8. Relationship of Force Protection to <strong>Risk</strong> <strong>Management</strong> ................................ 1-5<br />
Chapter II RISK MANAGEMENT PROCESS AND OPERATIONAL<br />
CONSIDERATIONS ............................................................... ,.... .......... . ..... .............. <strong>11</strong>-1<br />
1. Background .... . ... . . . .. . . . ... . . . . . , . . . .. . , . .. , , . .. . . , .. . . . . , , . .. . , . .. , . . .. . . . .. . . . ... . . , , .. , . . . .. . , . .. .. . .. . <strong>11</strong>- 1<br />
2. Application of <strong>Risk</strong> <strong>Management</strong> .... . . . .. .. . . .. . . ... . . . . . . . . .. .. . .. . . . .... . . .... . ..... . .... ..... .II-l<br />
3. Integration of <strong>Risk</strong> <strong>Management</strong> ...... ........ ...,. .... .... .... .... ...... .... ..... .....II-7<br />
4. Analysis Models .......................................................................... .....+...........<br />
<strong>11</strong>-8<br />
Chapter <strong>11</strong>1 STAFF FUNCTIONS AND RESPONSIBILITIES .............................................. <strong>11</strong>1-1<br />
1. Background ................................................................................................ <strong>11</strong>1-1<br />
2. Responsibilities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . <strong>11</strong>1- 1<br />
V<br />
1-1<br />
iii
3 .<br />
4 .<br />
Integration into Training and Operations ................................................. <strong>11</strong>1-6<br />
Review ofthe <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> .................................................. <strong>11</strong>1-6<br />
Appendix A <strong>Risk</strong> <strong>Management</strong> Tools ..............................................................................<br />
Appendix B Force Protection Working Group ...............................................................<br />
References .......................................................................................................... References-1<br />
Glossary .............................................................................................................. Glossary-1<br />
Index .................................................................................................................... Index- 1<br />
Figures 1.1 . Continuous Application of <strong>Risk</strong> <strong>Management</strong> ............................................ 1-4<br />
<strong>11</strong>- 1 . Identify the Threats ................................................................................... <strong>11</strong>.1<br />
<strong>11</strong>.2 . Assess the Threat ....................................................................................... <strong>11</strong>-2<br />
<strong>11</strong>.3 . Develop Controls and Make <strong>Risk</strong> Decisions ............................................. . II-3<br />
<strong>11</strong>.4 . Implement Controls ................................................................................... <strong>11</strong>-5<br />
<strong>11</strong>.5 . Supervise and Review ...............................................................................<br />
1-6<br />
A-A-1 . Sample Completed <strong>Risk</strong> <strong>Management</strong> Worksheet .............................. A-A-1<br />
A-B- 1 . Sample Force Protection Priority Matrix ........................................... A-B-1<br />
A.D-1 . <strong>Risk</strong> Assessment Matrix ..................................................................... A-D-1<br />
A-E-1 . Sample <strong>Risk</strong> Control Options Planning Matrix .................................. A-E-1<br />
B- 1 . Potential Sources for the FPWG ................................................................ B-1<br />
B-2 . Example FPWG Meeting Agenda .............................................................. B-2<br />
B-3 . Sample <strong>Risk</strong> Considerations Matrix .......................................................... B-5<br />
Tables <strong>11</strong>.1 . Criteria for Effective Controls ................................................................... <strong>11</strong>-3<br />
<strong>11</strong>.2 . <strong>Risk</strong> <strong>Management</strong> Execution (<strong>Risk</strong> <strong>Management</strong> in Deliberate<br />
Planning) ................................................................................................... I 1.7<br />
<strong>11</strong>.3 . <strong>Risk</strong> <strong>Management</strong> Execution (<strong>Risk</strong> <strong>Management</strong> in Crisis Action<br />
<strong>11</strong>.4 . Considerations and Potential Threats Analyzed (Man Element.<br />
<strong>11</strong>.5 . Considerations and Potential Threats Analyzed (Machine Element.<br />
<strong>11</strong>.6 . Considerations and Potential Threats Analyzed (Media Element.<br />
1.7 . <strong>Management</strong> Tools and Examples Analyzed (<strong>Management</strong> Element.<br />
A-C- 1 . Sample Force Protection Tasks, Conditions, Desired Effects, and<br />
Activities ............................................................................................... A-C- 1<br />
A.D.l . <strong>Risk</strong> Severity Categories .................................................................... A-D-2<br />
A.D.2 . Probability Definitions ....................................................................... A-D-3<br />
A-E- 1 . Examples of <strong>Risk</strong> Control Options ...................................................... A. E.2<br />
A-1<br />
B-1<br />
Planning) .................................................................................................. . II-8<br />
5-M Model) ............................................................................................... <strong>11</strong>- 1 1<br />
5-M Model) ............................................................................................... <strong>11</strong>-1 1<br />
5-M Model) ............................................................................................... <strong>11</strong>-12<br />
5-M Model) ............................................................................................... <strong>11</strong>- 12<br />
iv
This publicatioe<br />
EXECUTIVE SUMMARY<br />
<strong>Risk</strong> <strong>Management</strong><br />
0 Provides multiservice tactics, techniques, and procedures for tactical level<br />
risk management in the planning and execution of operations in a joint<br />
environment.<br />
0<br />
Provides a basic risk management process that may be used by all services.<br />
0 Applies to all elements of a force that assists in planning and conducting<br />
force protection.<br />
0 Provides risk management tools for commanders and staffs to use to<br />
manage risk during planning, preparation, and execution of joint operations.<br />
Chapter I<br />
<strong>Risk</strong> <strong>Management</strong> Fundamentals<br />
Chapter I introduces risk management as a process to assist decision makers in<br />
reducing or offsetting risks. It identifies the goal, key aspects, and principle concepts of the<br />
process; provides general guidelines for applying the process: and gives an overview of the<br />
process:<br />
0<br />
0<br />
Identifying threats.<br />
Assessing threats to determine risks.<br />
Developing controls and making risk decisions.<br />
Implementing controls.<br />
Supervising and reviewing.<br />
Chapter II<br />
Operational Considerations and Implementation<br />
Chapter I1 describes the actions involved in applying the risk management process;<br />
identifies pitfalls, types of controls, and feedback requirements; and integrates the risk<br />
management process into the planning process. This chapter describes how common<br />
situation analysis tools support the risk management process.<br />
Chapter <strong>11</strong>1<br />
Staff Functions and Responsibilities<br />
Chapter I<strong>11</strong> ties the risk management process to the chain of command and the staff<br />
directorates, and describes how leader involvement at all levels is necessary for the process<br />
to be effective. This chapter also describes the integration of the risk management process<br />
into all aspects of operations and training and illustrates how constant review of the<br />
process leads to improvement in the process.
The following commands and agencies participated in the development of this<br />
publication:<br />
Army<br />
HQ TRADOC (ATDO-A) & (ATBO-SO), Ingalls Rd Bldg 133 Room 7, Ft. Monroe,<br />
VA 23651-5000<br />
Combined Arms Center (CAC), Combined Arms Doctrine Directorate (CADD),<br />
Ft Leavenworth, KS<br />
OG-D, BCTP, Ft Leavenworth, KS<br />
CDR, XVIII Airborne Corps, Ft Bragg, NC<br />
Army Safety Center, Training Division, Ft Rucker, AL<br />
USAREUR, DCSPER, Unit 29351, APO AE, 09063<br />
Marine Corps<br />
Marine Corps Combat Development Command, Joint Doctrine Branch (C427) 3300 Russell<br />
Rd, 3rd Floor Suite 318A, Quantico, VA 22134-5021<br />
Marine Corps Combat Development Command, MSTP (C54) 2076 South Street,<br />
Quantico, VA 22134-5021<br />
Commandant of the Marine Corps (Code SD), 2 Navy Annex, Room, 3317,<br />
Washington, DC 20380- 1775<br />
Navy<br />
OPNAV, N09K, 2000 Navy Pentagon 5E816, Washington, DC 20305-2000<br />
Commander, Navy Warfare Development CommandN5, 686 Cushing Rd,<br />
Newport, RI 02841-1207<br />
Commander, Naval Safety Center, 375 A Street, Norfolk, VA 2351 1-4399<br />
COMPHIBGRU TWO, NAB Little Creek, Norfolk, VA 2352 1<br />
Air Force<br />
HQ Air Force Doctrine Center, 155 N Twining Street, Maxwell Air Force Base, AL 361 12<br />
AFDC Detachment 1, 2 16 Sweeny Bvld. Ste 109, Langley Air Force Base, VA 23665<br />
HQ USAFISE, 9700 G Ave SE, Kirkland Air Force Base, NM 871 17-5670<br />
vi
1. Background<br />
Chapter I<br />
RISK MANAGEMENT FUNDAMENTALS<br />
<strong>Risk</strong> management is a process that assists decision makers in reducing or offsetting risk<br />
(by systematically identifying, assessing, and controlling risk arising from operational<br />
factors) and making decisions that weigh risks against mission benefits. <strong>Risk</strong> is an<br />
expression of a possible loss or negative mission impact stated in terms of probability and<br />
severity. The risk management process provides leaders and individuals a method to assist<br />
in identifying the optimum course of action (COA). <strong>Risk</strong> management must be fully<br />
integrated into planning, preparation, and execution. Commanders are responsible for the<br />
application of risk management in all military operations. <strong>Risk</strong> management facilitates the<br />
mitigation of the risks of threats to the force. For the purposes of this document, threat is<br />
defined as a source of danger-any opposing force, condition, source, or circumstance with<br />
the potential to negatively impact mission accomplishment and/or degrade mission<br />
capability.<br />
a. Each of the services uses similar but slightly different processes. This publication<br />
provides a single process to enable warfighters from different services to manage risk from<br />
a common perspective.<br />
b. <strong>Risk</strong> management is useful in developing, deploying, and employing the joint force.<br />
Development concerns force design, manpower allocation, training development, and<br />
combat material developments. Deploying and employing the joint force generates concerns<br />
in force protection and balancing risk against resource constraints.<br />
c. Military operations are inherently complex, dynamic, dangerous and, by nature,<br />
involve the acceptance of risk. Because risk is often related to gain, leaders weigh risk<br />
against the benefits to be gained from an operation. The commander’s judgment balances<br />
the requirement for mission success with the inherent risks of military operations. Leaders<br />
have always practiced risk management in military decision making; however, the<br />
approach to risk management and degree of success vary widely depending on the leader’s<br />
level of training and experience.<br />
d. Since the Korean conflict, United States forces have suffered more losses from noncombat<br />
causes than from enemy action. Key factors contributing to those losses include-<br />
(1) Rapidly changing operational environment.<br />
(2) Fast-paced, high operations tempo and high personnel tempo.<br />
(3) Equipment failure, support failure, and effects of the physical environment.<br />
(4) Human factors.<br />
2. <strong>Risk</strong> <strong>Management</strong> Goal<br />
The fundamental goal of risk management is to enhance operational capabilities and<br />
mission accomplishment, with minimal acceptable loss.<br />
3. Key Aspects of <strong>Risk</strong> <strong>Management</strong><br />
a. <strong>Risk</strong> management assists the commander or leader by-<br />
(1) Enhancing operational mission accomplishment.<br />
(2) Supporting well-informed decision making to implement a COA.<br />
(3) Providing assessment tools to support operations.
(4) Enhancing decision-making skills based on a reasoned and repeatable process.<br />
(5) Providing improved confidence in unit capabilities. Adequate risk analysis<br />
provides a clearer picture of unit readiness.<br />
(6) Preserving and protecting personnel, combat weapon systems, and related<br />
support equipment while avoiding unnecessary risk.<br />
(7) Providing an adaptive process for continuous feedback through the planning,<br />
preparation, and execution phases of military operations.<br />
(8) Identifying feasible and effective control measures where specific standards do<br />
not exist.<br />
’<br />
b. <strong>Risk</strong> <strong>Management</strong> does not-<br />
(1) Replace sound tactical decision making.<br />
(2) Inhibit the commander’s and leader’s flexibility, initiative, or accountability.<br />
(3) Remove risk altogether, or support a zero defect mindset.<br />
(4) Sanction or justify violating the law.<br />
(5) Remove the necessity for rehearsals, tactics, techniques, and procedures.<br />
4. Principles of <strong>Risk</strong> <strong>Management</strong><br />
The basic principles that provide a framework for implementing the risk management<br />
process include-<br />
a.’ Accept No Unnecessary <strong>Risk</strong>. An unnecessary risk is any risk that, if taken, will<br />
not contribute meaningfully to mission accomplishment or will needlessly endanger lives or<br />
resources. No one intentionally accepts unnecessary risks. The most logical choices for<br />
accomplishing a mission are those that meet all mission requirements while exposing<br />
personnel and resources to the lowest acceptable risk. All military operations and off-duty<br />
activities involve some risk. The risk management process identifies threats that might<br />
otherwise go unidentified and provides tools to reduce or offset risk. The corollary to this<br />
axiom is “accept necessary risk” required to successfully complete the mission or task.<br />
b. Make <strong>Risk</strong> Decisions at the Appropriate Level. Anyone can make a risk<br />
decision; however, the appropriate level for risk decisions is the one that can make<br />
decisions to eliminate or minimize the threat, implement controls to reduce the risk, or<br />
accept the risk. Commanders at all levels must ensure that subordinates know how much<br />
risk they can accept and when to elevate the decision to a higher level. Ensuring that risk<br />
decisions are made at the appropriate level will establish clear accountability. The risk<br />
management process must include those accountable for the mission. After the commander,<br />
leader, or individual responsible for executing the mission or task determines that controls<br />
available to them will not reduce risk to an acceptable level, they must elevate decisions to<br />
the next level in the chain of command.<br />
c. Accept <strong>Risk</strong> When Benefits Outweigh the Cost. The process of weighing risks<br />
against opportunities and benefits helps to maximize mission success. Balancing costs and<br />
benefits is a subjective process and must remain a leader’s decision.<br />
d. Anticipate and Manage <strong>Risk</strong> by Planning. Integrate risk management into<br />
planning at all levels. Commanders must dedicate time and resources to apply risk<br />
management effectively in the planning process, where risks can be more readily assessed<br />
and managed. Integrating risk management into planning as early as possible provides<br />
leaders the greatest opportunity to make well-informed decisions and implement effective<br />
risk controls. During execution phases of operations, the risk management process must be<br />
1-2
applied to address previously unidentified risks while continuing to evaluate the<br />
effectiveness of existing risk control measures and modify them as required.<br />
5. Levels of <strong>Risk</strong> <strong>Management</strong><br />
The risk management process has two levels of application: crisis action and deliberate.<br />
Time is the basic factor that contributes to the selection of the level of application used.<br />
a. Crisis Action. Crisis action risk management is an “on-the-run” mental or verbal<br />
review of the situation using the basic risk management process. The crisis action process<br />
of risk management is employed to consider risk while making decisions in a timecompressed<br />
situation. This level of risk management is used during the execution phase of<br />
training or operations as well as in planning and execution during crisis responses. It is<br />
particularly helpful for choosing the appropriate COA when an unplanned event occurs.<br />
b. Deliberate. Deliberate risk management is the application of the complete process<br />
when time is not critical. It primarily uses experience and brainstorming to identify threats<br />
and develop controls and is, therefore, most effective when done in a group. Examples of<br />
deliberate applications include planning upcoming operations, reviewing standing<br />
operating procedures (SOP), maintenance, training, and developing damage control or<br />
disaster response plans.<br />
6. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Overview<br />
The risk management process involves the following:<br />
Identifying threats.<br />
Assessing threats to determine risks.<br />
Developing controls and making risk decisions.<br />
Implementing controls.<br />
Supervising and reviewing.<br />
a. Threat Identification and Threat Assessment. These elements comprise the<br />
risk assessment portion of risk management. In threat identification, individuals identify<br />
the threats that may be encountered in executing a mission. In threat assessment, they<br />
determine the direct impact of each threat on the operation. <strong>Risk</strong> assessment provides<br />
enhanced awareness and understanding of the situation. This awareness builds confidence<br />
and allows timely, efficient, and effective protective measures.<br />
b. Develop Controls, Make Decisions, Implement Controls, Supervise, and<br />
Review. These remaining elements of the risk management process are the essential<br />
follow-through actions of managing risk effectively. Leaders weigh risk against benefits and<br />
take appropriate actions to eliminate unnecessary risk. During planning, preparation, and<br />
execution, the commander should communicate his acceptable risks to subordinates and<br />
continuously assess risks to the overall mission. Finally, leaders and individuals evaluate<br />
the effectiveness of controls and capture lessons learned.<br />
7. <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong> Application Guidelines<br />
This section provides general guidelines for applying the risk management process. To<br />
get maximum benefit from this tool-<br />
a. Apply the <strong>Process</strong> in Sequence. Each element is a building block for the next<br />
one. For example, if threat identification is interrupted to focus control on a particular<br />
threat, other more important threats may be overlooked and the risk management process<br />
may be distorted. Until threat identification is complete, it is not possible to prioritize risk<br />
control efforts properly.<br />
1-3
. Maintain Balance in the <strong>Process</strong>. All parts of the process are important. If only<br />
an hour is available to apply the risk management process, the time must be allocated to<br />
ensure the total process can be completed. Spending fifty minutes of the hour on threat<br />
identification may not leave enough time to apply the other parts of the process effectively.<br />
The result would be suboptimal risk management. Of course, it is simplistic to rigidly insist<br />
that each of the parts is allocated ten minutes. The objective is to assess the time and<br />
resources available for risk management activities and allocate them to the actions in a<br />
manner most likely to produce the best overall result.<br />
c. Apply the <strong>Process</strong> as a Cycle. See Figure 1-1 below. Notice that “supervise and<br />
review” feeds back into the beginning of the process. When “supervise and review” identifies<br />
additional threats or determines that controls are ineffective, the entire risk management<br />
process should be repeated.<br />
I<br />
Identify the Threats<br />
Lessons<br />
Learned<br />
fl<br />
Supervise and Review<br />
Feedback<br />
m a<br />
Assess the Threat<br />
Assess Threat<br />
I<br />
x<br />
Severitv<br />
Assess Threat<br />
I Probabilitv I<br />
I Determine risk level for<br />
each threat and overall<br />
I<br />
Implement Controls<br />
Develop Controls and<br />
Make <strong>Risk</strong> Decisions<br />
As controls for threats are identified and selected, the<br />
Assess Threats <strong>Process</strong> is repeated.<br />
Figure 1-1. Continuous Application of <strong>Risk</strong> <strong>Management</strong><br />
1-4
d. Involve People Fully. The only way to ensure the risk management process is<br />
effective is to involve the people actually exposed to the risks. Periodically revalidate risk<br />
management procedures to ensure those procedures support the mission.<br />
8. Relationship of Force Protection to <strong>Risk</strong> <strong>Management</strong><br />
The commander has the dilemma of weighing mission requirements and force protection<br />
measures. One of his primary tools for weighing mission and protection is reconciled by<br />
assessing and balancing risk. This process forms a direct relationship between force<br />
protection and risk management. In the force protection process, we consider three<br />
elements: planning, operations, and sustainment. <strong>Risk</strong> management enables the force<br />
protection process by using risk assessment and controls in each element. The relationship<br />
between force protection and risk management is evident in the following:<br />
a. In planning, we conduct risk assessment and develop controls.<br />
b. In operations, we update risk assessment and implement controls.<br />
c. In sustainment, we continue to update assessments and adjust controls.<br />
1-5
1. Background<br />
Chapter II<br />
RISK MANAGEMENT PROCESS AND OPERATIONAL<br />
CONSIDERATIONS<br />
This chapter discusses the risk management process and how it may be applied in the<br />
planning and execution phases of all operations. This chapter also provides two situational<br />
analysis models. These models are the mission, enemy, terrain and weather, troops and<br />
support available, time (METT-T) model and the man, machine, media, management,<br />
mission (5-M) model.<br />
2. Application of <strong>Risk</strong> <strong>Management</strong><br />
a. Identify Threats. A threat is a source of danger: any opposing force, condition,<br />
source, or circumstance with the potential to impact mission accomplishment negatively<br />
and/or degrade mission capability. Experience, common sense, and risk management tools<br />
help identify real or potential threats. Threat identification is the foundation of the entire<br />
risk management process; if a threat is not identified it cannot be controlled. The effort<br />
expended in identifying threats will have a multiplier effect on the impact of the total risk<br />
management process. Figure <strong>11</strong>- 1 depicts the actions necessary to identify threats<br />
associated with these three categories: (1) mission degradation, (2) personal injury or death,<br />
and (3) property damage.<br />
k<br />
LIST<br />
I 1 I I I<br />
ACTION 1<br />
ANALYZE MISSION<br />
ACTION 2<br />
THREATS<br />
Figure <strong>11</strong>-1. Identify the Threats<br />
(1) Action 1-Analyze Mission, This is accomplished by-<br />
(a) Reviewing operation plans and orders describing the mission.<br />
(b) Defining requirements and conditions to accomplish the tasks.<br />
ACTION 3<br />
LIST CAUSES<br />
(c) Constructing a list or chart depicting the major phases of the operation<br />
normally in time sequence.<br />
(d) Breaking the operation down into “bite-size’’ chunks.<br />
(2) Action 2-List Threats. Threats (and factors that could generate threats) are<br />
identified based on the mission and associated vulnerabilities. The output of the<br />
identification phase is a list of inherent threats or adverse conditions, which is developed by<br />
listing the threats associated with each phase of the operation. Stay focused on the specific<br />
steps in the operation; limit your list to “big picture” threats. Examine friendly centers of<br />
gravity for any critical vulnerabilities. Threats may be tracked on paper or in a computer<br />
spreadsheeddatabase system to organize ideas and serve as a record of the analysis for<br />
future use.<br />
(3) Action 3-List Causes. Make a list of the causes associated with each threat<br />
identified in Action 2. Although a threat may have multiple causes, it is paramount to<br />
identify the root cause(s). <strong>Risk</strong> controls may be more effective when applied to root causes.<br />
b. Assess Threats. Each threat is assessed for probability and severity of occurrence.<br />
Probabilityis the estimate of the likelihood that a threat will cause an impact on the<br />
<strong>11</strong>-1
mission. Some threats produce losses frequently; others almost never do. Severity is the<br />
expected consequence of an event in terms of degree of injury, property damage, or other<br />
mission-impairing factors (such as loss of combat power). The result of this risk assessment<br />
allows prioritization of threats based on risk. The number one risk is the one with the<br />
greatest potential impact on the mission. However, the least risky issue may still deserve<br />
some attention and, possibly, risk control action. Keep in mind that this priority listing is<br />
intended for use as a guide to the relative priority of the risks involved, not as an absolute<br />
order to be followed. There may be, as an example, something that is not a significant risk<br />
that is extremely simple to control. Figure <strong>11</strong>-2 depicts the necessary actions.<br />
r r<br />
ACTION 1 ACTION 2 I ACTION 3<br />
ASSESS THREAT<br />
ASSESS THREAT<br />
COMPLETE RISK<br />
SEVERITY<br />
PROBABILITY<br />
ASSESSMENT<br />
I I I I I<br />
Figure <strong>11</strong>-2. Assess the Threat<br />
(1) Action 1-Assess Threat Severity. Determine the severity of the threat in<br />
terms of its potential impact on the mission, exposed personnel, and exposed equipment.<br />
Severity categories are defined to provide a qualitative measure of the worst credible<br />
outcome resulting from external influence (such as combat or terrorist action; personnel<br />
error; environmental conditions; design inadequacies; procedural deficiencies; or system,<br />
subsystem, or component failure or malfunction). Severity categories listed in Appendix A,<br />
Annex D, provide guidance for a wide variety of missions and systems.<br />
(2) Action 2-Assess Threat Probability. Determine the probability that the<br />
threat will cause a negative event of the severity assessed in Action 1. Probability may be<br />
determined through experienced-based estimates or derived from research, analysis, and<br />
evaluation of historical data from similar missions and systems. The typical event sequence<br />
is much more complicated than a single line of erect dominos; tipping the first domino<br />
(threat) triggers a clearly predictable reaction. Supporting rationale for assigning a<br />
probability should be documented for future reference. Generally accepted definitions for<br />
probability may be found at Appendix A, Annex D.<br />
(3) Action 3-Complete <strong>Risk</strong> Assessment. Combine severity and probability<br />
estimates to form a risk assessment for each threat. When combining the probability of<br />
occurrence with severity, a matrix may be used to assist in identifying the level of risk. A<br />
sample matrix is in Appendix A, Annex D. Existing databases and/or a panel of personnel<br />
experienced with the mission and threats can also be used to help complete the risk<br />
assessment.<br />
(4) Output of <strong>Risk</strong> Assessment. The outcome of the risk assessment process is a<br />
prioritized list of threats. The highest priority threat is the most serious one to the mission;<br />
the last is the least serious risk of any consequence.<br />
(5) <strong>Risk</strong> Assessment Pitfalls. The following are some pitfalls that should be<br />
avoided during the assessment:<br />
(a) Over optimism: “It can’t happen to us. We’re already doing it.” This pitfall<br />
results from not being totally honest and not looking for root causes of the threats.<br />
(b) Misrepresentation: Individual perspectives may distort data. This can be<br />
deliberate or unconscious.<br />
(c) Alarmism: “The sky is falling” approach, or “worst case” estimates are used<br />
regardless of their possibility.<br />
<strong>11</strong>-2
(d) Indiscrimination: All data is given equal weight.<br />
(e) Prejudice: Subjectivity and/or hidden agendas are used instead of facts.<br />
(f)<br />
Inaccuracy: Bad or misunderstood data nullify accurate risk assessment.<br />
(g) Enumeration: It is difficult to assign a numerical value to human behavior.<br />
Numbers may oversimplify real life situations.<br />
It may be difficult to get enough applicable data: this could force<br />
inaccurate estimates.<br />
numbers.<br />
0<br />
Numbers often take the place of reasoned judgment.<br />
<strong>Risk</strong> can be unrealistically traded off against benefit by relying solely on<br />
c. Develop Controls and Make <strong>Risk</strong> Decisions. These actions are listed as<br />
separate and distinct parts of the overall process by the U.S. Air Force (USAF), but will be<br />
dealt with under this overall heading for the purpose of this publication. Figure <strong>11</strong>-3 depicts<br />
the necessary actions.<br />
ACTION 1 I ACTION2 I<br />
DEVELOP CONTROLS AND<br />
DETERMINE RESIDUAL<br />
RISK<br />
MAKE RISK<br />
DECISIONS<br />
Figure <strong>11</strong>-3. Develop Controls and Make <strong>Risk</strong> Decisions<br />
(1) Action 1-Develop Controls. After assessing each threat, leaders should<br />
develop one or more controls that either eliminate the threat or reduce the risk (probability<br />
and/or severity) of threats. For each threat identified, develop one or more control options<br />
that either avoid the threat or reduce its risk to a level that meets the commander’s risk<br />
guidance. Examples of criteria for establishing effective controls are listed in Table <strong>11</strong>- 1.<br />
REMARKS<br />
Standards<br />
<strong>11</strong>-3
(a) Some types of controls are as follows:<br />
0 Engineering controls. These controls use engineering methods to reduce<br />
risks, such as developing new technologies or design features, selecting better materials,<br />
identifying suitable substitute materials or equipment, or adapting new technologies to<br />
existing systems. Examples of engineering controls that have been employed in the past<br />
include development of aircraft stealth technology, integrating global positioning system<br />
data into cruise missiles, and development of night vision devices.<br />
0 Administrative controls. These controls involve administrative actions,<br />
such as establishing written policies, programs, instructions, and SOPS, or limiting the<br />
exposure to a threat either by reducing the number of personnellassets or length of time<br />
they are exposed.<br />
0 Educational controls. These controls are based on the knowledge and<br />
skills of the units and individuals. Effective control is implemented through individual and<br />
collective training that ensures performance to standard.<br />
0 Physical controls. These controls may take the form of barriers and<br />
guards or signs to warn individuals and units that a threat exists. Use of personal<br />
protective equipment, fences around high power high frequency antennas, and special<br />
controller or oversight personnel responsible for locating specific threats fall into this<br />
category.<br />
0 Operational controls. These controls involve operational actions such as<br />
pace of operations, battlefield controls (areas of operations and boundaries, direct fire<br />
control measures, fire support coordinating measures), rules of engagement, airspace<br />
control measures, map exercises, and rehearsals.<br />
(b) A control should avoid/reduce the risk of a threat by accomplishing one or<br />
more of the following:<br />
0 Avoiding the risk. This often requires canceling or delaying the task,<br />
mission, or operation and is, therefore, an option rarely exercised because of mission<br />
importance. However, it may be possible to avoid specific risks: risks associated with a<br />
night operation may be avoided by planning the operation for daytime; thunderstorm or<br />
surface-to-air-missile risks can be avoided by changing the flight route.<br />
0 Delay a COA. If there is no time deadline or other operational benefit to<br />
speedy accomplishment of a task, it may be possible to reduce the risk by delaying the task.<br />
Over time, the situation may change and the risk may be eliminated, or additional risk<br />
control options may become available (resources become available, new technology becomes<br />
available, etc.) reducing the overall risk. For example, a mission can be postponed until<br />
more favorable weather reduces the risk to the force.<br />
0 Transferring the risk. <strong>Risk</strong> may be reduced by transferring a mission, or<br />
some portion of that mission, to another unit or platform that is better positioned, more<br />
survivable, or more expendable. Transference decreases the probability or severity of the<br />
risk to the total force. For example, the decision to fly an unmanned aerial vehicle into a<br />
high-risk environment instead of risking a manned aircraft is risk transference.<br />
0 Assigning redundant capabilities. To ensure the success of critical<br />
missions to compensate for potential losses assign redundant capabilities. For example,<br />
tasking a unit to deploy two aircraft to attack a single high value target increases the<br />
probability of mission success.<br />
<strong>11</strong>-4
(c) Determine Residual <strong>Risk</strong>. Once the leader develops and accepts<br />
controls, he or she determines the residual risk associated with each threat and the overall<br />
residual risk for the mission. Residual risk is the risk remaining after controls have been<br />
identified, selected, and implemented for the threat. As controls for threats are identified<br />
and selected, the threats are reassessed, and the level of risk is revised. This process is<br />
repeated until the level of residual risk is acceptable to the commander or leader or cannot<br />
be further reduced. Overall residual risk of a mission must be determined when more than<br />
one threat is identified. The residual risk for each of these threats may have a different<br />
level, depending on the assessed probability and severity of the hazardous incident. Overall<br />
residual mission risk should be determined based on the threat having the greatest<br />
residual risk. Determining overall mission risk by averaging the risks of all threats is not<br />
valid. If one threat has high residual risk, the overall residual risk of the mission is high, no<br />
matter how many moderate or low risk threats are present.<br />
(2) Action 2-Make <strong>Risk</strong> Decisions. A key element of the risk decision is<br />
determining if the risk is justified. The leader should compare and balance the risk against<br />
the mission’s potential gain. The leader alone decides if controls are sufficient and<br />
acceptable and whether to accept the resulting residual risk. If the leader determines the<br />
risk level is too high, he or she directs the development of additional or alternate controls,<br />
or modifies, changes, or rejects the COA. Leaders can use the risk assessment matrix or<br />
other tools found in Appendix A, in conjunction with their commanders’ guidance, to<br />
communicate how much risk they are willing to allow subordinate leaders to accept.<br />
d. Implement Controls. Once the risk control decision is made, assets must be made<br />
available to implement the specific controls. Part of implementing controls is informing the<br />
personnel in the system of the risk management process results and subsequent decisions.<br />
Figure <strong>11</strong>-4 depicts the actions necessary to complete this step. Careful documentation of<br />
each step in the risk management process facilitates risk communication and the rational<br />
processes behind risk management decisions.<br />
I<br />
ESTABLISH<br />
IMPLEMENTATION ACCOUNTABILITY SUPPORT<br />
CLEAR<br />
I<br />
Figure <strong>11</strong>-4. Implement Controls<br />
(1) Action 1-Make Implementation Clear. To make the implementation<br />
directive clear, consider using examples, providing pictures or charts, including job aids,<br />
etc. Provide a roadmap for implementation, a vision of the end state, and description of<br />
successful implementation. The control should be presented so it will be received positively<br />
by the intended audience. This can best be achieved by designing in user ownership.<br />
(2) Action 2-Establish Accountability. Accountability is important to effective<br />
risk management. The accountable person is the one who makes the decision (approves the<br />
control measures); therefore, the right person (appropriate level) must make the decision.<br />
Clear assignment of responsibility for implementation of the risk control is required.<br />
<strong>11</strong>-5
(3) Action 3-Provide Support. To be successful, the command must support the<br />
risk controls. This support requires-<br />
(a) Providing the personnel and resources necessary to implement the control<br />
measures.<br />
(b) Designing in sustainability from the beginning.<br />
(c) Employing the control with a feedback mechanism that will provide<br />
information on whether the control is achieving the intended purpose.<br />
e. Supervise and Review. Supervise and review involves determining the<br />
effectiveness of risk controls throughout the operation. There are three aspects: monitoring<br />
the effectiveness of risk controls; determining the need for further assessment of either all,<br />
or a portion of, the operation due to an unanticipated change; and capturing lessons<br />
learned, both positive and negative. Figure <strong>11</strong>-5 depicts the necessary actions.<br />
ACTION 1<br />
SUPERVISE<br />
FEEDBACK<br />
Figure <strong>11</strong>-5. Supervise and Review<br />
(1) Action 1-Supervise. Monitor the operation to ensure-<br />
(a) Controls are implemented correctly, effective, and remain in place.<br />
(b) Changes requiring further risk management are identified.<br />
(c) Action is taken to correct ineffective risk controls and reinitiate the risk<br />
management process in response to new threats.<br />
(d) <strong>Risk</strong>s and controls are reevaluated any time the personnel, equipment, or<br />
mission tasks change, or new operations are anticipated in an environment not covered in<br />
the initial risk management analysis.<br />
Successful mission performance is achieved by shifting the cost versus benefit balance<br />
more in favor of benefit through controlling risks. By using risk management whenever<br />
anything changes, we consistently control risks identified before an operation and those<br />
that develop during the operation. Addressing the risks before they get in the way of<br />
mission accomplishment saves resources and enhances mission performance.<br />
(2) Action 2-Review. The risk management process review must be systematic.<br />
After controls are applied, a review must be accomplished to see if the risks and the mission<br />
are in balance. To determine if appropriate risk management controls have been applied,<br />
compare METT-T or the 5-M model from the earlier steps to the present risk management<br />
assessment.<br />
(a) To accomplish an effective review, commanders identify whether the actual<br />
cost is in line with expectations. The commander needs to determine what effect the risk<br />
control had on mission performance. It is difficult to evaluate the risk control by itself;<br />
therefore, the focus should be on the aspect of mission performance the control measure<br />
was designed to improve.<br />
(b) Measurements are necessary to ensure accurate evaluations of how<br />
effectively controls eliminated threats or reduced risks. After Action Reports (AAR) ,<br />
surveys, and in-progress reviews provide great starting places for measurements.<br />
<strong>11</strong>-6
(3) Action 3-Feedback. A review by itself is not enough; a mission feedback<br />
system should be established to ensure that the corrective or preventative action taken was<br />
effective and that any newly discovered threats identified during the mission were analyzed<br />
and corrective action taken.<br />
(a) When a decision is made to accept risk, factors (cost versus benefit<br />
information) involved in the decision should be recorded: proper documentation allows for<br />
review of the risk decision process. Then, when a negative consequence occurs, the decision<br />
process can be reviewed to determine where errors in the process may have occurred.<br />
(b) <strong>Risk</strong> analysis will not always be perfect the first time. When errors occur in<br />
an analysis, use feedback (such as briefings, lessons learned, cross-tell reports,<br />
benchmarking, or database reports) to identify and correct those errors. This feedback will<br />
help determine if the previous forecasts were accurate, contained errors, or were<br />
completely incorrect.<br />
3. Integration of <strong>Risk</strong> <strong>Management</strong><br />
Tables <strong>11</strong>-2 and <strong>11</strong>-3 integrate the risk management process into each phase of the<br />
deliberate and crisis action Joint Operation Planning and Execution System (JOPES). The<br />
annotations of the joint task force (JTF) and major subordinate element (MSE) in the<br />
matrix identify the level of command primarily responsible for risk management execution<br />
during each particular phase of planning. The risk management process should be<br />
considered throughout the planning process by each level of command.<br />
Deliberate Planning<br />
PHASE I<br />
Initiation<br />
Table <strong>11</strong>-2<br />
<strong>Risk</strong> <strong>Management</strong> Execution<br />
(<strong>Risk</strong> <strong>Management</strong> in Deliberate Planning)<br />
Develop Controls<br />
Identi@ Assess<br />
Make<br />
Threats<br />
Controls<br />
Threats <strong>Risk</strong> Decision<br />
JTF<br />
Supervise<br />
and Review<br />
PHASE II<br />
Concept Development<br />
JTF<br />
JTF<br />
PHASE <strong>11</strong>1<br />
Plan Development<br />
MSE<br />
MSE<br />
JTF<br />
MSE<br />
PHASE IV<br />
Plan Review<br />
JTF<br />
PHASE V<br />
Supporting Plans<br />
MSE<br />
MSE<br />
MSE<br />
JTF<br />
MSE<br />
EXECUTION<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
<strong>11</strong>-7
Table <strong>11</strong>-3<br />
<strong>Risk</strong> <strong>Management</strong> Execution<br />
(<strong>Risk</strong> <strong>Management</strong> in Crisis Action Planni<br />
CRISIS ACTION Identify Assess<br />
Develop Controls<br />
Make <strong>Risk</strong><br />
PLANNING<br />
Threats Threats<br />
PHASE I<br />
Situation Development<br />
PHASE II<br />
Crisis Assessment<br />
I I I Decision<br />
I JTF I JTF I<br />
I JTF I JTF I JTF<br />
ii<br />
Controls<br />
Supervise<br />
and Review<br />
PHASE <strong>11</strong>1<br />
COA Development<br />
JTF JTF JTF<br />
MSE MSE MSE<br />
PHASE IV<br />
COA Selection<br />
JTF<br />
MSE<br />
JTF<br />
PHASE V<br />
Execution Planning<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
PHASE VI<br />
Execution<br />
I MSE I MSE I MSE<br />
JTF<br />
MSE<br />
JTF<br />
MSE<br />
I<br />
4. Analysis Models<br />
a. The METT-T Model. The METT-T model can be used for conducting a situation<br />
analysis by breaking it into five general areas: (1) the mission itself, (2) the enemy, (3)<br />
terraidweather, (4) troops and support available, and (5) time available.<br />
Note. The U.S. Army uses mission, enemy, terrain and weather, troops and support<br />
available, time available, civil considerations (METT-TC), adding civil considerations<br />
as a sixth area of analysis.<br />
(1) Mission. Leaders first analyze the assigned mission. They look at the type of<br />
mission to be accomplished and consider possible subsequent missions. Certain kinds of<br />
operations are inherently more dangerous than others. For example, a deliberate frontal<br />
attack is more likely to expose a unit to losses than would a defense from prepared<br />
positions. Identifying missions that routinely present greater risk is imperative. Leaders<br />
also look for threats associated with complexity of the plan (such as a scheme of maneuver<br />
that is difficult to understand or too complex for accurate communications down to the<br />
lowest level) or the impact of operating under a fragmentary order.<br />
(2) Enemy. Commanders look for enemy capabilities that pose significant threats to<br />
the operation. For example, “What can the enemy do to defeat my operation?”<br />
(a) Common shortfalls that can create threats during operations include failure<br />
to-<br />
* Assess potential advantages to the enemy provided by the battlefield<br />
environment.<br />
Fully assess the enemy’s capabilities.<br />
Understand enemy capabilities and friendly vulnerabilities to those<br />
capabilities.<br />
<strong>11</strong>-8
Accurately determine the enemy’s probable COAs.<br />
Plan and coordinate active ground and aerial reconnaissance activities.<br />
Disseminate intelligence about the enemy to lower echelons.<br />
Identify terrorist threats and capabilities.<br />
(b) Intelligence plays a critical part in identifying threats associated with the<br />
presence of an enemy or an adversary. Intelligence preparation of the battlespace is a<br />
dynamic staff process that continually integrates new information and intelligence that<br />
ultimately becomes input to the commander’s risk assessment process. Intelligence assists<br />
in identifying threats during operations by-<br />
0 Identifying opportunities and constraints the battlefield environment offers<br />
to enemy and friendly forces.<br />
Thoroughly portraying enemy capabilities and vulnerabilities.<br />
0 Collecting information on populations, governments, and infrastructures.<br />
(3) Terrain and Weather. Terrain and weather pose great potential threats to<br />
military operations. The unit must be familiar with both the terrain and its associated<br />
environment for a mission to succeed. Basic issues include availability of reliable weather<br />
forecasts, how long the unit has operated in the environment and climate, and whether the<br />
terrain has been crossed before.<br />
(a) Terrain. The main military aspects of terrain are observation and fields of<br />
fire, cover and concealment, obstacles, key terrain, and avenues of approach; these may be<br />
used to identify and assess threats impacting friendly forces. Terrain analysis includes both<br />
map and visual reconnaissance to identify how well the terrain can accommodate unit<br />
capabilities and mission demands.<br />
0 Observation and fields offire. Threats associated with observation and fields<br />
of fire usually involve when the enemy will be able to engage a friendly unit and when the<br />
friendly unit’s weapon capabilities allow it to engage the enemy effectively.<br />
0 Cover and concealment. Threats associated with cover and concealment are<br />
created either by failure to use cover and concealment or by the enemy’s use of cover and<br />
concealment to protect his assets from observation and fire.<br />
0 Obstacles. Threats associated with obstacles may be caused by natural<br />
conditions (such as rivers or swamps) or man-made conditions (such as minefields or builtup<br />
areas).<br />
0 Key terrain. Threats associated with key terrain result when the enemy<br />
controls that terrain or denies its use to the friendly forces.<br />
0 Avenues of approach. Threats associated with avenues of approach include<br />
conditions in which an avenue of approach impedes deployment of friendly combat power or<br />
conditions that support deployment of enemy combat power.<br />
(b) Weather. To identify weather threats, leaders and unit personnel must<br />
assess the impact on operating systems. Threats may arise from-<br />
0 Lack of understanding of reliability and accuracy of weather forecasting.<br />
0 Effects of climate and weather on personnel and equipment operation and<br />
maintenance.<br />
0 Effects of weather on mobility.<br />
<strong>11</strong>-9
(4) Troops and Support Available. Leaders analyze the capabilities of available<br />
friendly troops. Associated threats impact both individual personnel and the unit. Key<br />
considerations are level of training, manning levels, the condition and maintenance of<br />
equipment, morale, availability of supplies and services, and the physical and emotional<br />
health of personnel. All personnel must be vigilant to the fact that threats in these areas<br />
can adversely affect a mission. Even when all tactical considerations point to success,<br />
mission failure can be caused by-<br />
(a) Threats to physical and emotional health. The health threat depends on a<br />
complex set of environmental and operational factors that combine to produce “disease<br />
non-battle injuries” as well as combat injuries. Care of troops requires long-range<br />
projection of logistical and medical needs with close monitoring of mission changes that<br />
could impact troop support.<br />
(b) Threats to task organization or units participating in an operation. Threats<br />
include poor communication, unfamiliarity with higher headquarters SOPS, and<br />
insufficient combat power to accomplish the mission. How long units have worked together<br />
under a particular command relationship should be considered when identifying threats.<br />
(c) Threats associated with long-term missions. Long-term missions include<br />
peacekeeping, or insurgencykounterinsurgency operations. Threats associated with these<br />
missions include the turmoil of personnel turnover, lack of continuity of leadership,<br />
inexperience, and lack of knowledge of the situation and the unit’s operating procedures.<br />
Long-term missions can also lead to complacency; units conditioned to routine ways of<br />
accomplishing the mission fail to see warnings evident in the operational environment. An<br />
especially insidious threat is the atrophy of critical-skills that results from not performing<br />
mission-essential task list related missions.<br />
(5) Time Available. The threat is insufficient time to plan, prepare, and execute<br />
operations. Planning time is always at a premium. Leaders routinely apply the onethirdkwo-thirds<br />
rule (providing two thirds of time available to subordinates for planning) to<br />
ensure their subordinate units are given maximum time to plan. Failure to accomplish a<br />
mission on time can result in shortages of time for subordinate and adjacent units to<br />
accomplish their missions.<br />
b. U.S. Army Situation Analysis. While Joint, Marine Corps, Air Force, and Navy<br />
doctrine use METT-T for situation analysis, the Army uses METT-TC. The “C” in METT-TC<br />
is civil considerations-how the attitudes and activities of the civilian leaders, populations,<br />
and organizations within an area of operations will influence the conduct of military<br />
operations. Threats associated with civil considerations include, but are not limited to,<br />
collateral damage, changing political and social attitudes, civilian unrest, the influence of<br />
the press on public opinion, conflicting goals and objectives of private voluntary<br />
organizations (PVOs) and nongovernmental organizations (NGOs), and the handling of<br />
refugees, noncombatants, and protesters.<br />
c. 5-M Model. The 5-M model provides an alternative framework for conducting<br />
mission analysis by examining the impacts and inter-relationships between the composite<br />
elements of Man, Machine, Media, <strong>Management</strong>, and Mission. The amount of overlap or<br />
interaction between the individual components is a characteristic of each mission and<br />
evolves as the mission develops.<br />
<strong>11</strong>-10
(1) Man. This is the area of greatest variability and thus possesses the majority of<br />
risks. Some considerations and potential threats are listed in Table <strong>11</strong>-4.<br />
Table <strong>11</strong>-4<br />
Considerations and Potential Threats Analyzed<br />
(Man Element, 5-M Model)<br />
Considera tions<br />
Selection<br />
Performance<br />
Personal Factors<br />
Potential Threats<br />
Wrong person psychologically/physically, not proficient in assigned<br />
task, no procedural guidance<br />
Lack of awareness, false perceptions, over-tasking, distraction,<br />
channelized attention, stress, peer pressure, over/lack of<br />
confidence, poor insight, poor adaptive skills, pressure/workload,<br />
fatigue<br />
Expectations, lack of job satisfaction, poor values, familiedfriends,<br />
command/control, poor discipline (internal and external), perceived<br />
pressure (over tasking) and poor communication skills<br />
(2) Machine. Used as intended, limitations interface with man. Some<br />
considerations and potential threats are listed in Table <strong>11</strong>-5.<br />
Table <strong>11</strong>-5<br />
Considerations and Potential Threats Analyzed<br />
(Machine Element, 5-M Model)<br />
Considera tions<br />
Design<br />
Maintenance<br />
Logistics<br />
Technical Data<br />
I Potential Threats<br />
I<br />
Engineering reliability and performance, ergonomics<br />
Availability of time, tools, and parts, ease of access<br />
Supply, upkeep, and repair<br />
Clear, accurate, useable, and available<br />
<strong>11</strong>-1 1
(3) Media. This includes external, largely environmental forces. Some<br />
considerations and potential threats are listed in Table <strong>11</strong>-6.<br />
Table <strong>11</strong>-6<br />
Considerations and Potential Threats Analyzed<br />
(Media Element, 5-M Model)<br />
Considerations<br />
Climatic<br />
Operational<br />
Potential Threats<br />
Ceiling, visibility, temperature, humidity, wind, and precipitation<br />
Terrain, wildlife, vegetation, man-made obstructions, daylight,<br />
maritime environment, and darkness<br />
Hygienic<br />
I Trafficability<br />
Ventilatiodair quality, noiselvibration, dust, and contaminants<br />
Pavement, gravel, dirt, ice, mud, dust, snow, sand, hills, and<br />
curves<br />
(4) <strong>Management</strong>. Directs the process by defining standards, procedures, and<br />
controls. While management provides procedures and rules to govern interactions, it cannot<br />
completely control the system elements. For example, weather is not under management<br />
control and individual decisions affect off-duty personnel much more than management<br />
policies. Some considerations and examples are listed in Table <strong>11</strong>-7.<br />
Table <strong>11</strong>-7<br />
<strong>Management</strong> Tools and Examples Analyzed<br />
(<strong>Management</strong> Element, 5-M Model)<br />
Considerations<br />
Standards<br />
Procedures<br />
Controls<br />
Examples<br />
Doctrine statements, applicable criteria, and policy directives<br />
Checklists, SOPS, work cards, and multi-command manuals<br />
Crew rest, altitude/airspeed/speed limits, restrictions, training<br />
rulesllimitations, rules of engagement (ROE), lawful orders<br />
(5) Mission. The desired outcome. Objectives: Big picture understood, well defined,<br />
obtainable. The results of the interactions of the other 4-Ms (Man, Media, Machine, and<br />
<strong>Management</strong>).<br />
<strong>11</strong>-12
1. Background<br />
Chapter <strong>11</strong>1<br />
STAFF FUNCTIONS AND RESPONSIBILITIES<br />
The unit commander, staff, leaders, and individual members integrate risk<br />
management by embedding the risk management process into unit operations, culture,<br />
organization, systems, and individual behaviors.<br />
a. Successful risk management is underwritten by the chain of command. Leaders do<br />
not expect all missions to be accomplished with zero defects. Leaders need to support<br />
subordinates’ decisions to accept risks that are within the leaders’ understanding of the<br />
commander’s intent and guidance. Demanding rigid standards, such as zero defects, leads<br />
to over-supervision and paralysis, producing timid leaders afraid to make tough decisions in<br />
crisis, and unwilling to take risks necessary for successful military operations. A zerodefects<br />
mindset creates conditions that will inevitably lead to failure and higher casualties<br />
in battle.<br />
b. Leaders anticipate things may go wrong, even with the certain knowledge that<br />
subordinates do all within their power to prevent incidents. When incidents occur, leaders<br />
step forward and accept the responsibility along with their subordinates. Furthermore, risk<br />
management does not justify taking actions to facilitate an unethical, immoral, or illegal<br />
action.<br />
2. Responsibilities<br />
a. Commanders. With the assistance of their leaders and staffs, commanders manage<br />
risks. Minimizing risk is the responsibility of everyone in the chain of command, from the<br />
highest commander, through his subordinate leaders, to each individual service member.<br />
Managing risk is critical for all operations, whether for training or operations; commanders<br />
should issue clear risk guidance.<br />
(1) Military plans should make risk management a priority. It is an inherent part of<br />
every mission and a basic responsibility of commanders. Leaders and service members at<br />
all levels are responsible and accountable for managing risks by ensuring that threats and<br />
associated risks are-<br />
(a) Identified during planning, preparation, and execution of operations.<br />
(b) Controlled during preparation and execution of operations. Service members<br />
are responsible for executing risk controls to standards. They continuously assess variable<br />
threats such as fatigue, equipment serviceability, and the environment. They make risk<br />
decisions consistent with the higher commander’s guidance.<br />
(2) Sometimes commanders are not properly advised in situations where the<br />
assumption of risk may affect or imperil their units, the intent of their higher commander,<br />
or the operations of an adjacent unit. This is most often attributed to-<br />
(a) <strong>Risk</strong> denial syndrome-leaders do not want to know of the risk.<br />
(b) Staff members who believe that the risk decision is part of their jobs and<br />
do not want to bother the commander or section leader.<br />
guidance.<br />
(c) Subordinates failure to fully understand the higher commander’s<br />
(d) Complacency-outright failure to recognize a threat or the level of risk<br />
involved, or overconfidence in one’s abilities or the unit’s capabilities to avoid or recover<br />
from a hazardous incident.<br />
<strong>11</strong>1-1
(e) Use of a standardized risk assessment tool, such as a risk assessment<br />
matrix, that is not tailored to the unit’s mission or adapted to the factors of METT-T/5-M<br />
and may put missions in the routine low-risk category.<br />
b. CommandersLeaders.<br />
(1) The commander directs the organization and sets priorities and the command<br />
climate (values, attitudes, and beliefs). Successful preservation of combat power requires<br />
embedding risk management into unit behavior. This requires commitment, creative<br />
leadership, innovative planning, and careful management. It also requires the chain of<br />
command’s demonstrated support of the risk management process. Commanders establish<br />
a command climate favorable for risk management integration by-<br />
(a) Demonstrating consistent and sustained risk management behavior through<br />
leading by example-habitually doing risk management-and actively participating<br />
throughout the risk management process.<br />
(b) Providing clear guidance where to accept risk or what risk to accept.<br />
(c) Obtaining and providing to subordinates the necessary assets to control risk.<br />
(d) Knowing their own limitations, their leaders’ and service members’<br />
limitations, and their unit’s capabilities.<br />
culture.<br />
(e) Preventing a zero-defects mindset from creeping into their commands<br />
(0 Allowing subordinates to make mistakes and learn from them.<br />
(g) Demonstrating full confidence in subordinates’ mastery of their trade and<br />
their ability to execute a chosen COA.<br />
(h) Keeping subordinates informed and consulting with subordinate leaders<br />
before making a decision, if feasible.<br />
(i) Listening to subordinates.<br />
(i) Establishing clear, feasible risk management policies and goals.<br />
(k) Conducting detailed planning within time constraints; assessing each<br />
mission and task in terms of its risk; continuously reassessing risk as the mission and<br />
conditions change and experience is gained.<br />
(1) Making informed risk decisions; establishing and clearly communicating<br />
risk guidance.<br />
(m) Training on the risk management process. Ensuring subordinates<br />
understand who, what, where, when, how, and why of managing risk, and how the risk<br />
management process applies to their circumstances and assigned responsibilities.<br />
(n) Examining how subordinates manage risk and how service members protect<br />
themselves.<br />
(0) Supervising and evaluating the unit’s execution of risk controls during the<br />
mission.<br />
(p) Advising the chain of command on risks and risk-reduction measures and<br />
providing subordinates with feedback on their performance and ways to improve.<br />
(9) Assessing the effectiveness of their unit’s risk management program.<br />
(r) Capturing and disseminating lessons learned to ensure they are continued<br />
from mission to mission so that others may benefit from the experience.<br />
<strong>11</strong>1-2
(2) Commanders weigh the repercussions of casualties, damage to the environment,<br />
impact on civilians, and loss of equipment. They also consider the public reaction to loss<br />
against national, strategic, operational, or tactical objectives. Commanders are also<br />
responsible for keeping subordinates from becoming complacent. An acceptable risk is the<br />
result of an informed decision. A gamble is an uninformed bet or guess on a hopeful<br />
outcome. Leaders and service members need to clearly understand the difference.<br />
(3) <strong>Risk</strong> decisions are frequently required by, and dependent on, the immediate<br />
situation. Judgment is required: a formula, rule, or checklist, by itself, is not appropriate<br />
under such circumstances. An effective commander’s approach to managing risk is to<br />
empower leaders by pushing risk decisions as far down the chain of command as feasible<br />
within the next higher commander’s guidance. Subordinates consider threats outside their<br />
assigned responsibilities that impact the mission. The result is coordination and<br />
communication-laterally and up and down the chain of command.<br />
(4) <strong>Risk</strong> management is a two-way street. It is important that those involved in<br />
mission preparation and execution are fully aware of the amount of command involvement<br />
and actions necessary to control or remove threats.<br />
(a) The higher commander’s guidance specifies the degree of acceptable damage<br />
or risk to subordinate units during the current operation.<br />
(b) Subordinates ensure they understand and implement their commander’s<br />
intent and guidance.<br />
If, during the planning process, residual risk exceeds that which the higher<br />
commander is willing to accept, the subordinate informs his commander. He requests the<br />
resources necessary to mitigate the risk.<br />
If, during mission execution, the subordinate determines the risk is too<br />
great, he directs the development of additional or alternate controls or modifies or changes<br />
the COA; then he notifies the next higher commander of his decision. Requiring<br />
subordinates to report to the higher commander when a risk decision point is reached<br />
during mission execution can result in paralysis.<br />
(5) The objective of managing risk is not to remove all risk, but to eliminate<br />
unnecessary risk. Commanders conduct tough, realistic training, knowing that they may<br />
put lives and property at risk in the course of military operations. If an action will result in<br />
an unacceptable risk, take measures to mitigate it. If the risk cannot be mitigated to an<br />
acceptable level, do not execute the action. Circumstances may occur during mission<br />
execution when a decision to stop and defer execution of the operation should be made to<br />
avoid taking unwarranted risk. Such a situation will generally occur at the tactical level.<br />
For example, circumstances may determine if a trade-off between maintaining the<br />
momentum of the attack and risking fratricide or serious accidents is justified.<br />
c. Staffs.<br />
(1) The chief of staff or executive officer may be assigned responsibility for<br />
supervising integration of risk management across the staff. As a means of assessing and<br />
monitoring threats, commanders may establish a force protection working group (FPWG),<br />
which is covered in detail in Appendix B. He coordinates development of risk controls with<br />
emphasis on deconflicting controls that affect multiple functional areas and adjacent units.<br />
The staff officer helps the commander eliminate unnecessary risks by-<br />
(a) Analyzing his functional area and applying risk management during the<br />
military decision-making process.<br />
guidance.<br />
(b) Identifying both constraints and restraints in the higher commander’s risk<br />
<strong>11</strong>1-3
estimate.<br />
(c) Including threats and their risks in the mission analysis briefing.<br />
(d) Including a risk assessment for the commander’s estimate.<br />
(e) Considering the risk assessment in the operations estimate.<br />
(0 Including risks and recommending ways to reduce their impact in the staff<br />
(g) Implementing risk controls by coordinating and integrating them into the<br />
appropriate paragraphs and graphics of the operation order (OPORD) and into products<br />
such as SOPS and operation plans (OPLANs).<br />
(h) Establishing procedures and standards that are clear and practical.<br />
(i) Determining the effectiveness of risk controls and continuously assessing<br />
their suitability, feasibility, supportability, clarity, and acceptability.<br />
(i) Supervising, evaluating, and assessing the integration of risk management<br />
during an operation.<br />
(k) Continuously identifying threats, assessing initial and residual risks for<br />
each threat, and recommending control measures to reduce the risk.<br />
(1) Identifying and assessing threats associated with complacency, especially<br />
during extended operations, and recommending appropriate actions to the commander.<br />
(2) Staffs focus on threats and their risks across the spectrum of protecting the force.<br />
These staffs-<br />
(a) Identify friendly vulnerabilities during current operations and implement<br />
controls to mitigate risk.<br />
(b) Implement commander’s intent on acceptance of risk in current operations.<br />
(3) The following list identifies some of the risk management responsibilities of the<br />
primary JTF directorates:<br />
(a) J- 1 (Personnel):<br />
0 Estimate time delay risks on personnel deployment flow.<br />
0 Determine casualty risks for each COA.<br />
0 Estimate casualty and replacement flow risks on future operations.<br />
0 Ensure controls for personnel-related activities are conducted to diminish<br />
operations security vulnerabilities and support military deception initiatives.<br />
0 Estimate risks of employed local civilian labor in coordination with the 5-4<br />
(logistics), 5-2 (intelligence), and legal officer.<br />
(b) J-2:<br />
0 Monitor and report threats that counter the effectiveness of friendly combat<br />
identificationkounter-fratricide measures.<br />
0 Develop current regional threat assessments.<br />
0 Determine risk of loss of low-density intelligence collection assets.<br />
(c) 5-3 (Operations):<br />
0 Develop risk assessment for the commander’s estimate.<br />
<strong>11</strong>1-4
Perform as staff proponent for combat identificatiodcounter-fratricide<br />
measures. Develop policy, procedures and assign responsibility for combat<br />
identification/counter-fratricide measures.<br />
Report and investigate reports of fratricides.<br />
Develop risk assessment of military and political aspects of draft ROE and<br />
supplemental ROE.<br />
0 Determine criticality and vulnerability of bases in the Joint Rear Area to<br />
prioritize controls and levels of response.<br />
(d) 5-4:<br />
0 Make recommendations to the JTF commander on the combat<br />
identificatiodcounter-fratricide technology acquisition and procurement strategies.<br />
Assess the risk of critical supply levels not meeting required number of days<br />
of supply days.<br />
controls.<br />
0 Determine petroleum, oils, and lubricants storage site vulnerabilities and<br />
0 Determine munitions storage site vulnerabilities and safety requirements.<br />
(e) 5-5 (Plans):<br />
Integrate functional directorate risk management controls and combat<br />
identificatiodcounter-fratricide measures into deliberate planning products.<br />
0 Identify friendly maneuver and firepower vulnerabilities during mission<br />
analysis, wargaming and plan controls to mitigate risk.<br />
(f) J-6 (Communications): Responsible for assessing risk to geospatial<br />
information and services systems and developing controls to counter threats.<br />
(g) Special staff offices: <strong>Risk</strong> management should be addressed in the various<br />
special staff offices, including-<br />
0 Surgeon (health and nonbattle injury, return to duty policy, preventative<br />
medicine).<br />
0 Legal officer (Uniform Code of Military Justice, law of armed conflict, and<br />
host nation (HN) law).<br />
d. Individuals.<br />
Public affairs officer (media coverage, public opinion, etc.).<br />
0 Safety officer.<br />
(1) An individual's level of expertise and maturity influences risk management<br />
proficiency. Managing risk is subjective because its basis is individual judgment.<br />
Inexperienced service members are routinely charged with executing risk controls and risk<br />
reduction measures. Their limited experience can significantly increase the level of risk<br />
they are willing to accept. Their sense of indestructibility, motivation (esprit de corps), and<br />
willingness to achieve the mission at any cost can lead to failure to consider risks. Due to<br />
inexperience or complacency, they may become susceptible to-<br />
(a) Overestimating their ability to respond to, or recover from, a hazardous<br />
incident-they become overconfident.<br />
(b) Underestimating the level of risk posed by a threat. It is imperative that<br />
individuals understand and execute controls directed by leaders and staffs.<br />
<strong>11</strong>1-5
(2) Individuals should be aware of, and fully understand, the situation, and<br />
maintain self-discipline when they perform their duties. They should-<br />
(a) Understand and apply risk management.<br />
(b) Execute controls directed by their leaders, that is, perform to standards.<br />
(c) Carry risk management over into all activities-both on and off duty.<br />
(d) Look out for others-anyone<br />
inherently unsafe.<br />
3. Integration into Training and Operations<br />
has authority to halt something that is<br />
a. Integrating risk management into training and operations-<br />
(1) Preserves the lives and well-being of everyone.<br />
(2) Conserves equipment, facilities, environmental resources, and combat power.<br />
b. <strong>Risk</strong> management is planned up front, not treated as an afterthought. Leaders and<br />
managers of materiel acquisition, base operations, and industrial operations budget risk<br />
control costs up front at the level of expected payback over the duration of the activity, or<br />
the life cycle of materiel/weapons system.<br />
c. When integrating risk management into sustained operations, leaders consider<br />
increases in turbulence, personnel turnover, critical skill atrophy, and mission<br />
development. Leaders continuously assess-<br />
(1) The complexity of mission development and associated changing<br />
interrelationships with other agencies.<br />
(2) The inclusion of civilian contractors, such as logistics civilian augmentation<br />
programs, as part of the force.<br />
(3) The presence of the media, NGOs, and PVOs. These diverse elements need to be<br />
integrated into the risk management process.<br />
d. A key consideration relevant to managing risk in complex operational environments<br />
is understanding the culture of the indigenous population or society and its way of doing<br />
business. Leaders consider the impact of interference with the indigenous population’s way<br />
of life and local customs. Such interference could risk damage to relationships and increase<br />
the potential for introducing instability into the local society. Leaders do not, however,<br />
intentionally allow these considerations to endanger their force or its mission.<br />
e. Leaders and service members systematically provide observations and assessments<br />
of the unit’s risk management performance for the training management cycle and SOPS.<br />
They should have the skills, knowledge, and attitude to manage risks inherent in all<br />
operations effectively. Effective training helps service members become proficient. It<br />
qualifies them technically and tactically, and as leaders, to accomplish the mission without<br />
unnecessary risk.<br />
f. Unit leaders and their staffs continually assess and evaluate the integration of risk<br />
management into short-, near-, and long-term training plans. They continually review Joint<br />
Mission Essential Task Lists to ensure that training is supported by realistic risk<br />
management objectives. The services consider past experiences to avoid repeating mistakes.<br />
4. Review of the <strong>Risk</strong> <strong>Management</strong> <strong>Process</strong><br />
a. Reviewing the risk management process determines a unit’s current level of<br />
proficiency in implementing the process. How well risk is managed affects readiness.<br />
Leaders need to know the current status and effectiveness of their unit’s risk management<br />
<strong>11</strong>1-6
program. Reviewing the unit’s effectiveness in managing risk permits the unit to gain<br />
insight into areas for improvement and obtain feedback on subordinates’ understanding<br />
and application of risk guidance. The objective is to determine how-<br />
(1) Effectively risk management is embedded into planning and preparing for<br />
operations.<br />
(2) Well subordinate leaders and service members understand risk management.<br />
(3) Effectively risk management is used to execute operations. Leaders assess the<br />
effectiveness of their units by reviewing how well threats are identified and risk controls<br />
are-<br />
(a) Specified in oral and written OPORDs, OPLANs, and SOPS.<br />
(b) Communicated to lowest level of chain of command.<br />
(c) Included in short-, near-, and long-term training plans.<br />
(d) Implemented into all activities, on and off duty.<br />
(e) Embedded into force protection programs.<br />
(0 Included in AARs and captured in lessons learned.<br />
b. <strong>Risk</strong> management cannot be seen as a competitive program whereby a unit or leader<br />
is judged or compared in a competitive sense. Focus is strictly on both reduction of risk and<br />
hazardous incidents.<br />
<strong>11</strong>1-7
Appendix A<br />
<strong>Risk</strong> <strong>Management</strong> Tools<br />
Commanders, leaders, and staffs use risk management tools to facilitate the risk<br />
management process-identification of threats and development of controls. The tables and<br />
matrices in this appendix are samples of tools that commanders, leaders and staffs may use<br />
when integrating the risk management process. It is impractical to create detailed<br />
procedures to ensure the “right” tools are used for each activity and every contingency.<br />
However, choosing the best tools is important when planning a potentially hazardous<br />
operation. Most tools in this appendix can be used in a variety of creative ways; the user<br />
selects the appropriate tool, or combination of tools, and the extent of effort to expend on<br />
each. Since there are no right or wrong selections, the user must rely on his knowledge and<br />
experience to make the right choice for each situation.<br />
Annex A: <strong>Risk</strong> <strong>Management</strong> Worksheet<br />
Annex B: Force Protection Priority Matrix<br />
Annex C: Force Protection Tasks, Conditions, Desired Effects and Activities<br />
Annex D: <strong>Risk</strong> Assessment Matrix<br />
Annex E: Sample <strong>Risk</strong> Control Option Planning Matrix<br />
A- 1
Annex A<br />
<strong>Risk</strong> <strong>Management</strong> Worksheet<br />
The risk management worksheet provides a starting point to track the process of<br />
threats and risks logically. It can be used to document risk management steps taken during<br />
planning, preparation, and execution.<br />
Identify Threats<br />
Mission<br />
Phases I Threats 1 Causes<br />
1 1<br />
Initial<br />
Religious<br />
Protesters<br />
entry belief<br />
Initial<br />
I<br />
Diseases<br />
1<br />
entrv<br />
Lodgment Local<br />
Pilferage<br />
expansion<br />
economy<br />
Assess<br />
Threats<br />
Medium<br />
I<br />
Develop <strong>Risk</strong> Controls and<br />
Make <strong>Risk</strong> Decisions<br />
Residual<br />
Initial RAC I Develop Controls I RAc<br />
High<br />
High<br />
I<br />
Personnel<br />
awareness,<br />
cantonment area<br />
Immunize<br />
field sanitation<br />
Increase security<br />
force<br />
Date Worksheet Prepared<br />
I<br />
Low<br />
Low<br />
Medium<br />
Implement<br />
Controls<br />
How to<br />
Training<br />
Civil Affairs,<br />
Predeployment<br />
actions, training<br />
Augment force<br />
Supervise<br />
How to<br />
First line<br />
supervisors<br />
Component<br />
commanders<br />
J-314<br />
High Direct action Medium<br />
Airfield takedown<br />
1st Ranger<br />
Battalion<br />
J-3<br />
Legend:<br />
RAC<strong>Risk</strong> Assessment Code<br />
Comm with HigherNes No<br />
Figure A-A-I. Sample Completed <strong>Risk</strong> <strong>Management</strong> Worksheet<br />
A-A- 1
Annex B<br />
Force Protection Priority Matrix<br />
This matrix prioritizes force protection tasks and operating systems used for protection<br />
in each task. It reverses the normal targeting methodology and focuses the Joint Planing<br />
Group on what it needs to protect for each specific task.<br />
Force Protection Task I:<br />
Maintain flank security<br />
Priority<br />
Operational<br />
Operating System<br />
Protected Capability<br />
3d Marine Division (PD)<br />
1 Maneuver 10lst Airborne Division<br />
(Air Assault) (PD)<br />
2 Logistics<br />
I<br />
I<br />
3 1 Fires<br />
I<br />
4 Intelligence UAV FOB<br />
Command and<br />
Control<br />
6 I Force Protection I<br />
Key:<br />
PD-Prevent<br />
PN-Prevent<br />
PS-Prevent<br />
Destruction<br />
Neutralization<br />
Suppression<br />
Legend:<br />
CSSA-combat service support area<br />
FOB-forward operating base<br />
JLOTS-joint logistics over the shore<br />
MEB-Marine Expeditionary Brigade<br />
TACC-Tactical Air Command Center<br />
UAV-unmanned aerial vehicle<br />
Operational Operating<br />
System<br />
Log istics<br />
Command and Control<br />
Fires<br />
Intelligence<br />
Maneuver<br />
Force Protection<br />
Protected Capability<br />
CSSA (PN)<br />
JLOTS Site (PN)<br />
MEB Command Post (PN)<br />
TACC (PN)<br />
Ground Mobile Force Site<br />
(PS)<br />
Airbase A (PN)<br />
Airbase B (PN)<br />
Tactical Combat Force (PD)<br />
Figure A-B-I. Sample Force Protection Priority Matrix<br />
A-B-1
Annex C<br />
Force Protection Tasks,<br />
Conditions, Desired Effects, and Activities<br />
Troop-to-task analysis may reveal deficiencies that require risk assessment and<br />
subsequent adjustments. The following table is a sample analysis that draws out the logical<br />
consequences of a force protection task. It can also be rendered as a decision tree. During<br />
COA development, each member of the joint planning group needs to be able to justify the<br />
tasking of resources to support force protection tasks.<br />
Table A-GI.<br />
Sample Force Protection Tasks, Conditions, Desired Effects, and Activities<br />
Force Protection Task<br />
Maintain security of vital areas<br />
Minimize losses<br />
Force Protection Condition<br />
GMF remains fully operational during H-hour to H+24<br />
Rapid evacuation of casualties<br />
Force Protection Desired Effect<br />
GMF site safe from local attack and from effects of weapons of mass destruction<br />
Air MEDEVAC less than 20 minutes<br />
Surface MEDEVAC to regimental aid stations only<br />
Force Protection Activities<br />
Local security in place<br />
TCF prepared to respond to level Ill threat<br />
TBMD coverage includes GMF site<br />
Task MAW to dedicatehnfigure 2 CH-46 for air MEDEVAC during H+10 - H+ 24<br />
Ensure adequacy of Class Vlll prior to H + 10<br />
Legend:<br />
GMF-Ground Mobile Force<br />
MAW-Marine Air Wing<br />
MEDEVAC-medical evacuation<br />
TBMD-theater ballistic missile defense<br />
TCF-Tactical Combat Force<br />
A-C-1
Annex D<br />
<strong>Risk</strong> Assessment Matrix<br />
The <strong>Risk</strong> Assessment Matrix combines severity and probability estimates to form a risk<br />
assessment for each threat. Use the <strong>Risk</strong> Assessment Matrix to evaluate the acceptability<br />
of a risk, and the level at which the decision on acceptability will be made. The matrix may<br />
also be used to prioritize resources, to resolve risks, or to standardize threat notification or<br />
response actions. Severity, probability, and risk assessment should be recorded to serve as<br />
a record of the analysis for future use.<br />
I <strong>Risk</strong> Assessment Matrix I<br />
I I<br />
I Severity<br />
!<br />
Probability<br />
I<br />
Frequent I Likely I 0cca;ional I Seldom 1 Unlply I<br />
B<br />
D<br />
1. <strong>Risk</strong> Definitions<br />
Figure A-D-1. <strong>Risk</strong> Assessment Matrix<br />
a. E - Extremely High <strong>Risk</strong> Loss of ability to accomplish the mission if threats occur<br />
during mission. A frequent or likely probability of catastrophic loss (IA or IB) or frequent<br />
probability of critical loss (IIA) exists.<br />
b. H - High <strong>Risk</strong>: Significant degradation of mission capabilities in terms of the<br />
required mission standard, inability to accomplish all parts of the mission, or inability to<br />
complete the mission to standard if threats occur during the mission. Occasional to seldom<br />
probability of catastrophic loss (IC or ID) exists. A likely to occasional probability exists of a<br />
critical loss (IIB or IIC) occurring. Frequent probability of marginal losses (IIIA) exists.<br />
c. M - Moderate <strong>Risk</strong> Expected degraded mission capabilities in terms of the<br />
required mission standard will have a reduced mission capability if threats occur during<br />
mission. An unlikely probability of catastrophic loss (IE) exists. The probability of a critical<br />
loss is seldom (IID). Marginal losses occur with a likely or occasional probability (IIIB or<br />
IIIC) . A frequent probability of negligible (IVA) losses exists.<br />
d. L - Low <strong>Risk</strong>: Expected losses have little or no impact on accomplishing the<br />
mission. The probability of critical loss is unlikely (IIE), while that of marginal loss is<br />
seldom (IIID) or unlikely (IIIE). The probability of a negligible loss is likely or less (IVB<br />
through (IVE).<br />
A-D-1
2. Severity Categories<br />
The following table outlines severity categories:<br />
Table A-D-1<br />
<strong>Risk</strong> Severity Categories<br />
Category<br />
CATASTROPHIC (I)<br />
CRITICAL (<strong>11</strong>)<br />
MARGINAL (<strong>11</strong>1)<br />
NEGLIGIBLE (IV)<br />
Definition<br />
Loss of ability to accomplish the mission or mission failure. Death or permanent<br />
disability. Loss of major or mission-critical system or equipment. Major property<br />
(facility) damage. Severe environmental damage. Mission-critical security failure.<br />
Unacceptable collateral damage.<br />
Significantly degraded mission capability, unit readiness, or personal disability.<br />
Extensive damage to equipment or systems. Significant damage to property or the<br />
environment. Security failure. Significant collateral damage.<br />
Degraded mission capability or unit readiness. Minor damage to equipment or<br />
systems, property, or the environment. Injury or illness of personnel.<br />
Little or no adverse impact on mission capability. First aid or minor medical<br />
treatment. Slight equipment or system damage, but fully functional and serviceable.<br />
Little or no property or environmental damage.<br />
3. Probability Categories<br />
The following table outlines probability categories for the risk assessment matrix:<br />
A-D-2
Table A-D-2<br />
Probability Definitions<br />
Element Exposed<br />
Definition<br />
FREQUENT (A) Occurs very often, continuously experienced<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurs very often in service life. Expected to occur several times over duration<br />
of a specific mission or operation.<br />
Occurs continuously during a specific mission or operation, or over a service<br />
life.<br />
Occurs very often. Expected to occur several times during mission or operation.<br />
LIKELY (6) Occurs several times<br />
Single item<br />
Fleet or inventory of items<br />
Occurs several times in service life. Expected to occur during a specific mission<br />
or operation.<br />
Occurs at a high rate, but experienced intermittently (regular intervals, generally<br />
OCCASIONAL (C) Occurs sporadically<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurs some time in service life. May occur about as often as not during a<br />
specific mission or operation.<br />
Occurs several times in service life.<br />
Occurs over a period of time. May occur during a specific mission or operation,<br />
but not often.<br />
SELDOM (0) Remotely possible; could occur at some time<br />
Single item<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
Occurs in service life, but only remotely possible. Not expected to occur during<br />
a specific mission or operation.<br />
Occurs as isolated incidents. Possible to occur some time in service life, but<br />
rarely. Usually does not occur.<br />
Occurs as isolated incident. Remotely possible, but not expected to occur<br />
during a specific mission or operation.<br />
Occurs rarely within exposed population as isolated incidents.<br />
UNLIKELY (E) Can assume will not occur, but not impossible<br />
Fleet or inventory of items<br />
Individual<br />
All personnel exposed<br />
life. Can assume will not occur during a specific mission or operation.<br />
Occurs very rarely (almost never or improbable). Incidents may occur over<br />
service life.<br />
Occurrence not impossible, but may assume will not occur during a specific<br />
mission or operation.<br />
Occurs very rarely, but not impossible.<br />
A-D-3
Annex E<br />
Sample <strong>Risk</strong> Control Options Planning Matrix<br />
This matrix combines risk control options and responsible personnel that appear<br />
suitable and practical with potential options. Many of these options may be applied at more<br />
than one level. For example, the training option may be applied to operators, supervisors,<br />
senior leaders, or staff personnel.<br />
Figure A-E-I. Sample <strong>Risk</strong> Control Options Planning Matrix<br />
A-E-I
Option<br />
Limit energy<br />
Substitute safer form<br />
Prevent release<br />
Separate<br />
Provide special maintenance of<br />
controls<br />
Core Tasks (especially critical tasks)<br />
Leader tasks<br />
Emergency contingency tasks<br />
Rehearsals<br />
Briefings<br />
Mental criteria<br />
Emotional criteria<br />
Physical criteria<br />
Experience<br />
Number of people or items<br />
Emergency medical care<br />
Personnel<br />
Facilitieslequipment<br />
Barrier<br />
On human or object<br />
Raise threshold (harden)<br />
Time<br />
Signslcolor coding<br />
Audiolvisual<br />
Sequence of events (flow)<br />
Timing (within tasks, between tasks)<br />
Simplify tasks<br />
Reduce task loads<br />
Backout options<br />
Contingency capabilities<br />
Emergency damage control<br />
procedures<br />
Backupslredundant capabilities<br />
Mission capabilities<br />
Table A-E-1<br />
Examples of <strong>Risk</strong> Control Options<br />
Example<br />
ENGINEER<br />
Small amount of explosives, reduce speeds<br />
Use air power, precision guided munitions<br />
Containment, doubleltriple containment<br />
Barriers, distance, boundaries<br />
Special procedures, environmental filters<br />
EDUCA TlONAL<br />
Define critical minimum abilities, train<br />
Define essential leader tasks and standards, train<br />
Define, assign, train, verify ability<br />
Validate processes, validate skills, verify interfaces<br />
Refresher warnings, demonstrate threats, refresh training<br />
ADMINISTRA TlVE<br />
Essential skills and proficiency<br />
Essential stability and maturity<br />
Essential strength, motor skills, endurance, size<br />
Demonstrated performance abilities<br />
Only expose essential personnel and items<br />
Medical facilities, personnel, medical evacuation<br />
Replace injured personnel, reinforce units, reallocate<br />
Restore key elements to service<br />
PHYSICAL<br />
Between revetments, walls, distance, ammunition storage facility<br />
Personal protective equipment, energy absorbing materials<br />
Acclimatization, reinforcement, physical conditioning<br />
Minimize exposure and number of iterationslrehearsals<br />
Warning signs, instruction signs, traffic signs<br />
Identification of friendly forces, chemicallbiological attack warning<br />
OPERATIONAL<br />
Put tough tasks first before fatigue, do not schedule several tough<br />
tasks in a row<br />
Allow sufficient time to perform, practice, and time between tasks<br />
Provide job aids, reduce steps, provide tools<br />
Set weight limits, spread task among many<br />
Establish points where process reversal is possible when threat is<br />
detected<br />
Combat search and rescue, rescue equipment, helicopter rescue,<br />
tactical combat force<br />
Emergency responses for anticipated contingencies, coordinating<br />
agencies<br />
Alternate ways to continue the mission if primaries are lost<br />
Restore ability to perform the mission<br />
A-E-2
1. Purpose<br />
Appendix B<br />
Force Protection Working Group<br />
The purpose of the force protection working group (FPWG) is to review threats, identify<br />
vulnerabilities, recommend counter-measures, determine force protection levels, assess in<br />
place measures, review tasks to components, monitor corrective actions, and direct special<br />
studies (force protection assessment teams). The primary responsibility is to monitor and<br />
assess the risk and threats to forces in the joint operations area and implement risk<br />
controls to maintain the protection of the force. Each command and control node, rear,<br />
intermediate support base, or FOB, should have a FPWG.<br />
2. Group Composition<br />
The composition will vary based on the threats and forces available. Suggested potential<br />
sources to provide representatives to the FPWG are listed in Figure B-1.<br />
Chief of Staff<br />
Personnel<br />
Intelligence<br />
Operations<br />
Log is tics<br />
Plans<br />
Communications<br />
Engineer<br />
Aviation<br />
Senior Enlisted Representative<br />
Public Affairs<br />
Surgeon<br />
Nuclear, Biological, and Chemical<br />
Chaplain<br />
Staff Weather Officer<br />
Safety<br />
Political Advisor<br />
Host Nation Support Representative<br />
BOTTOM LINE: Composition is Mission Dependent<br />
~ ~ ~~~<br />
Army Forces<br />
Marine Forces<br />
Air Force Forces<br />
Navy Forces<br />
Special Operations Forces<br />
Security Forces<br />
Judge Advocate General<br />
Figure B-1. Potential Sources for the FPWG<br />
3. Procedures<br />
The group may meet daily, weekly, or on-call in the vicinity of the Joint Operations<br />
Center to use the risk management process.<br />
4. Agenda<br />
The officer in charge of the command and control node or a designated representative<br />
should chair the meetings. The chairperson for the FPWG is not necessarily designated by<br />
duty position, but based on the ability of the person to fulfill the duties of force protection<br />
officer. A recommended agenda for conducting FPWG meetings follows:<br />
a. Start with updates from-<br />
(1) 52 Representative: intelligence update with focus on changes to the situation<br />
that may lead to additional threats for the force.<br />
(2) Counterintelligence (CI) representative: follows the JZ, clarifies and provides<br />
details of current risks based on his field reports.<br />
(3) 53 Representative: overview of current operations and force protection measures<br />
currently in place.<br />
B- 1
. Next, update new or evolving threats. This is an open discussion by functional area.<br />
For example, the surgeon would focus on medical health of command, the veterinary on new<br />
or changing food sources, etc. Steady state activities are raised during this phase of the<br />
meeting. All members consider emerging trends and determine if new vulnerabilities<br />
within their area of responsibility require the focus of the task force or if they are just<br />
isolated incidents. Each member comes to the meeting with documented concerns and<br />
recommendations.<br />
c. When new threats are identified, the FPWG will discuss measures to reduce the<br />
threat. For example, Threat identified: current route from billeting area to the Joint<br />
Operations Center is dangerous and not acceptable at night. Control: CI team will contact<br />
the country team, identify alternate routes, and drive and assess the routes. At the next<br />
FPWG meeting a decision will be made to change route.<br />
d. Once controls are decided upon (above example, CI to conduct a reconnaissance of a<br />
new route), that information is captured by the 53 representative and placed, as a directive<br />
for action, in the next fragmentary order.<br />
e. Following identification and development of controls for new threats, the group will<br />
review current measures in effect against known threats and determine the requirement<br />
for any changes or adjustments. Figure B-2 is an example FPWG agenda.<br />
I Event I lnput I<br />
Threat Situation Review<br />
Current Force Protection Levels<br />
Current Operations<br />
Results of Previous Meeting<br />
Threat Identification<br />
Vulnerability Identification<br />
Identify Controls<br />
Recommend Force Protection Level<br />
Recommend Taskings<br />
Summary<br />
Confirm Next Meeting<br />
J2<br />
J3<br />
J3<br />
Components, J3<br />
FPWG<br />
FPWG<br />
FPWG<br />
FPWG<br />
FPWG<br />
Figure 8-2. Example FPWG Meeting Agenda<br />
5. Assessment Teams<br />
To maintain visibility of threats, the FPWG may designate assessment teams to<br />
monitor the situation continuously. These teams may be tailored to review specific threats<br />
(such as preventive medicine and surgeon for medical, CI and Provost Marshal/Security<br />
Officer/Chief Security Forces for perimeter security). These teams may be assigned and<br />
operate at all operating bases throughout the joint operations area.<br />
a. The assessment teams mission includes-<br />
(1) Identify and assess threats and vulnerabilities.<br />
(2) Recommend controls.<br />
J3<br />
J3<br />
6-2
(3) Report through FPWG to Commander of the JTF.<br />
(4) Gather information.<br />
b. Assessment teams may use the following checklist:<br />
threats?<br />
(1) Threat.<br />
(a) What is the terrorist threatkapability?<br />
(b) What is the in-country leave and pass policy?<br />
(c) Are there any areas service members should avoid due to criminal or terrorist<br />
(d) What is the pre-disposition of the local populace to Americans (is it safe for<br />
service members to mix with public)?<br />
(e) Could operations be affected by civil disturbances protesting U.S. policy?<br />
(0 What criminal threats are likely to threaten operations (are there any threats<br />
of pilferage affecting sustainment operations)?<br />
(g) What is the relationship of local population with host nation (HN) authorities<br />
(is there any threat of civil unrest that could affect operations)?<br />
(h) Are there other threats such as para-military organizations or hostile<br />
intelligence that may target operations?<br />
(2) Facilities.<br />
(a) What facilities will the task force occupy?<br />
Tent city vs. hard site?<br />
Location-urban or rural?<br />
(b) What is the status of-<br />
* Perimeters?<br />
Barriers?<br />
Lighting?<br />
Motor pool facilities?<br />
(c) Will the node collocate with HN or friendly forces?<br />
(d) Is secure storage available for arms, ammunition, and explosives and<br />
classified, high dollar, and sensitive items?<br />
(e) Are there high-speed avenues of approach?<br />
(f)<br />
What checkpoints and barriers are necessary to control compound access?<br />
(3) Where will mission-essential vulnerable areas be established for arms,<br />
ammunition, and explosives storage: sensitive item storage; pilferable high dollar value<br />
item storage; fuel storage etc.?<br />
(a) What is their proximity to the perimeter?<br />
(b) What is their vulnerability to attack or observation?<br />
(4) Will the task force operate any sustainment operations facilities at air, sea, or<br />
rail ports?<br />
(5) Joint Operations.<br />
B-3
(a) If the task force occupies facilities with HN or friendly forces, who has<br />
command and control for force protection?<br />
(b) Who must the task force coordinate with concerning force protection, HN,<br />
friendly forces?<br />
(c) What are capabilities of friendly forces, HN armed forces, HN police forces,<br />
and HN security forces?<br />
(d) How are in-place friendly forces approaching force protection?<br />
(e) What historical problems have in-place friendly forces had concerning<br />
criminal activity (such as pilferage, assaults, terrorist threat, civil disturbance, and hostile<br />
intelligence)?<br />
(0 What threats do they perceive as possible?<br />
(g) What operations security measures are in effect?<br />
(h) What movement security measures are in effect?<br />
6. FPWG Products<br />
Based on the FPWG meeting, there are three suggested deliverables.<br />
a. First-an update to the Force Protection Matrix. This should be briefed to the JTF<br />
commander and placed on the SECRET Internet Protocol Router Network for the staff and<br />
components. Figure B-3 is an example of the risk considerations matrix.<br />
b. Second-Fragmentary Order directing execution of the new FPWG measures.<br />
c. Third - risk assessment for the current phase of the operation.<br />
d. Force protection assessment-continuous process throughout the conduct of the<br />
operation.
~<br />
I<br />
Operational<br />
Operating<br />
System<br />
Movement/<br />
Maneuver<br />
Event: JTF FOB stablishment loca m lcomponent: FC<br />
Threat Vulnerability Countermeasure Action<br />
Local faction<br />
Troop movement<br />
Route to hotel<br />
Minimize<br />
Standard route/<br />
Alternate routes<br />
Adjust battle rhythm<br />
All drivers with<br />
alternate route maps<br />
Aircraft<br />
Crossing flight<br />
lines<br />
Do not cross<br />
Intelligence<br />
Accident<br />
Civil rights<br />
Know embassy<br />
numbers<br />
Accident card<br />
USAF security patrols<br />
post speed limit<br />
Speeding flight line<br />
Pedestrians<br />
Slow speed<br />
(15 mph)<br />
LNOs brief forces<br />
Fires<br />
Loitering Thembad press Minimum<br />
presence in hotel<br />
Place of duty or room<br />
Sustainment<br />
Fire Threats<br />
~~<br />
Personnel and<br />
equipment<br />
~~<br />
Know route,<br />
exiting and alert<br />
procedure<br />
Fire break-aroid<br />
FARP<br />
No helplassist<br />
Personnel<br />
stranded<br />
Blood chits<br />
Order 500 chits<br />
Command and<br />
Control<br />
Protection<br />
Personnel<br />
accountability/<br />
location<br />
Heat<br />
Unsafe location/<br />
Unknown location<br />
Injury<br />
Frequent<br />
reporting, improve<br />
communication<br />
Water discipline<br />
Command emphasis<br />
Distribute cell phones<br />
Monitor WGBT<br />
Disease-malaria<br />
Health<br />
Buddy check<br />
Field sanitation<br />
Take pills<br />
Clean latrines<br />
Dogs<br />
Injury/health<br />
Caution<br />
Stay clear<br />
Legend:<br />
FARP-forward arming and refueling point<br />
LNO-liaison officer<br />
mph-miles per hour<br />
USAF-U .S. Air Force<br />
WGBT-wet globe bulb temperature<br />
Notes.<br />
Any changes made by the FPWG are highlighted.<br />
An additional column labeled "Assessment" can show how the countermeasures are working<br />
Figure 8-3. Sample <strong>Risk</strong> Considerations Matrix<br />
8-5
REFERENCES<br />
National<br />
Presidential Decision Directive 39, US. Policy on Counterterrorism, 2 1 June 1995<br />
Department of Defense<br />
DODI 6055.1, DOD Safety and Occupational Health (SOH) Program, 19 August 1998<br />
Joint<br />
CJCSM 3500.03, Joint Training Manual for the Armed Forces of the United States, 1 June<br />
1996<br />
CJCSM 3500.04, Universal Joint Task List, 1 November 1999<br />
CJCSM 3500.05, Joint Task Force Headquarters Master Training Guide, 15 April 1997<br />
JP 1-02. Department of Defense Dictionary of Military and Associated Terms, 1 <strong>September</strong><br />
2000<br />
JP 3-0, Doctrine for Joint Operations, 1 February 1995<br />
JP 3- 10, Joint Doctrine for Rear Area Operations, 28 May 1996<br />
JP 3- 1 1, Joint Doctrine for Operations in Nuclear, Biological, and Chemical (NBC)<br />
Environments, <strong>11</strong> July 2000<br />
JP 3- 13.1, Joint Doctrine for Command and Control Warfare (CZ W), 7 February 1996<br />
JP 3-54, Joint Doctrine for Operations Security, 24 January 1997<br />
JP 3-58, Joint Doctrine for Military Deception, 31 May 1996<br />
JP 4-0, Doctrine for Logistics Support of Joint Operations, 6 April 2000<br />
JP 5.00.1, Joint Tactics, Techniques, and Procedures for Joint Campaign Planning (Draft)<br />
JP 5-00.2, Joint Task Force (JTF) Planning Guidance and Procedures, 13 January 1999<br />
Air Force<br />
AFDD 2-4.1, Force Protection, 29 October 1999<br />
AFPD 90-9, Operational <strong>Risk</strong> <strong>Management</strong>, 1 April 2000<br />
AFI 90-901, Operational <strong>Risk</strong> <strong>Management</strong>, 1 April 2000<br />
AFPAM 90-902, Operational <strong>Risk</strong> <strong>Management</strong> Guidelines and Tools, 14 December 2000<br />
Army<br />
FM 3-0 (FM 100-5), Operations, 14 June 1993<br />
FM 3-07 (FM 100-20), Military Operations in Low Intensity Conflicts, 5 December 1990<br />
FM 3-07.3 (FM 100-23), Peace Operations, 30 December 1994<br />
FM 3-58 (FM 90-2), Battlefield Deception, 3 October 1988<br />
FM 6-22 (FM 22-loo), Army Leadership, 31 August 1999<br />
FM 3-21.10 (FM 7-10), The Infantry Rifle Company, 31 October 2000<br />
FM 7-10 (FM 25-101), Battle Focused Training, 30 <strong>September</strong> 1990<br />
References-I
Coast Guard<br />
COMMANDANT INSTRUCTION 3500.3 Operational <strong>Risk</strong> <strong>Management</strong> (Draft)<br />
Marine Corps<br />
Marine Corps Order 3500.27, Operational <strong>Risk</strong> <strong>Management</strong>, 3 April 1997<br />
ALMAR 210/97, Operational <strong>Risk</strong> <strong>Management</strong>, 15 July 1997<br />
MCDP-1, Warfighting, June 1997<br />
MCDP 1-2, Campaigning, August 1997<br />
MCWP 3-22, Antiair Warfare, 23 June 2000<br />
MCWP 5- 1, Marine Corps Planning <strong>Process</strong>, January 2000<br />
Navy<br />
OPNAVINST 3500.38, Universal Naval Task List, 30 <strong>September</strong> 1996<br />
OPNAVINST 3500.39, Operational <strong>Risk</strong> <strong>Management</strong>, 3 April 1997<br />
References-2
Glossary<br />
PART I-ABBREVIATIONS<br />
AND ACRONYMS<br />
5-M<br />
AAR<br />
AFB<br />
AFDC<br />
AFTTP<br />
AL<br />
ALSA<br />
APO<br />
CAC<br />
CADD<br />
Cdr<br />
CI<br />
COA<br />
CSSA<br />
DC<br />
DCSPER<br />
DSN<br />
etc<br />
FARP<br />
FM<br />
FOB<br />
FPWG<br />
GMF<br />
man, machine, media, management, mission<br />
A<br />
After Action Report<br />
Air Force Base<br />
Air Force Doctrine Center<br />
Air Force Tactics, Techniques, and Procedures<br />
Alabama<br />
Air Land Sea Application<br />
Army Post Overseas<br />
C<br />
Combined Arms Center<br />
Combined Arms Doctrine Development Center<br />
commander<br />
counterintelligence<br />
course of action<br />
combat service support area<br />
D<br />
District of Columbia<br />
Deputy Chief of Staff for Personnel<br />
Defense Switched Network<br />
E<br />
etcetera<br />
F<br />
forward arming and refueling point<br />
field manual<br />
forward operating base<br />
force protection working group<br />
G<br />
ground mobile force<br />
Glossary-I
HN<br />
HQ<br />
J- 1<br />
5-2<br />
5-3<br />
5-4<br />
J-5<br />
J-6<br />
JLOTS<br />
JOPES<br />
JP<br />
JTF<br />
KS<br />
LNO<br />
MAW<br />
MCCDC<br />
MCPDS<br />
MCRP<br />
MEDEVAC<br />
METT-T<br />
METT-TC<br />
MILSTRIP<br />
MSE<br />
MSTP<br />
H<br />
host nation<br />
headquarters<br />
J<br />
Manpower and Personnel Directorate of a joint staff<br />
Intelligence Directorate of a joint staff<br />
Operations Directorate of a joint staff<br />
Logistics Directorate of a joint staff<br />
Plans Directorate of a joint staff<br />
Command, Control, Communications, and Computer Systems<br />
Directorate of a joint staff<br />
joint logis tics over- the-shore<br />
Joint Operation Planning and Execution System<br />
joint publication<br />
joint task force<br />
K<br />
Kansas<br />
L<br />
liaison officer<br />
M<br />
Marine air wing<br />
Marine Corps Combat Development Command<br />
Marine Corps Publication Distribution System<br />
Marine Corps Reference Publication<br />
medical evacuation<br />
mission, enemy, terrain and weather, troops and support available,<br />
time available<br />
mission, enemy, terrain and weather, troops and support available,<br />
time available, civil considerations (Army)<br />
Military Standard Requisitioning and Issue Procedures<br />
major subordinate element<br />
Marine Air Ground Task Force Training Program<br />
Glossary-2
NAVSOP<br />
NC<br />
NWDC<br />
NGO<br />
NM<br />
OPLAN<br />
OPORD<br />
PD<br />
PN<br />
PS<br />
PVO<br />
RAC<br />
RI<br />
ROE<br />
SOP<br />
TACC<br />
TBMD<br />
TCF<br />
TRADOC<br />
UAV<br />
USAF<br />
USAREUR<br />
USMC<br />
USN<br />
N<br />
Navy Standing Operating Procedure<br />
North Carolina<br />
Navy Warfare Development Command<br />
nongovernmental organization<br />
New Mexico<br />
0<br />
operation plan<br />
operation order<br />
P<br />
prevent destruction<br />
prevent neutralization<br />
prevent suppression<br />
private voluntary organization<br />
R<br />
risk assessment code<br />
Rhode Island<br />
rules of engagement<br />
S<br />
standing operating procedure<br />
T<br />
Tactical Air Command Center<br />
theater ballistic missile defense<br />
tactical combat force<br />
United States Army Training and Doctrine Command<br />
U<br />
unmanned aerial vehicle<br />
United States Air Force<br />
United States Army, Europe<br />
United States Marine Corps<br />
United States Navy<br />
Glossary-3
PART II-TERMS<br />
AND DEFINITIONS<br />
acceptable risk. The portion of identified risk that is allowed to persist without further<br />
controls<br />
assessment. 1. Analysis of the security, effectiveness, and potential of an existing or<br />
planned intelligence activity.<br />
2. Judgment of the motives, qualifications, and characteristics of present or<br />
prospective employees or “agents.” (JP 1-02)<br />
controls. Actions taken to eliminate threats or reduce their risk. This term and its<br />
definition are applicable only in the context of this publication and should not be referenced<br />
outside this publication.<br />
exposure. The frequency and length of time subjected to a hazard (FM 3-100.12/100-14).<br />
extremely high risk. <strong>Risk</strong> that could result in loss of ability to accomplish the mission if<br />
threats occur during mission. A frequent or likely probability of catastrophic loss (IA or IB)<br />
or frequent probability of critical loss (IIA) exists. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
high risk. <strong>Risk</strong> that could result in significant degradation of mission capabilities in terms<br />
of the required mission standard, inability to accomplish all parts of the mission, or<br />
inability to complete the mission to standard if threats occur during the mission. Occasional<br />
to seldom probability of catastrophic loss (IC or ID) exits. A likely to occasional probability<br />
exists of a critical loss (IIB or IIC) occurring. Frequent probability of marginal losses (IIIA)<br />
exists. This term and its definition are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
identified risk. A risk determined by applying severity and probability analysis to an<br />
identified threat.<br />
inherently dangerous. An activity or task containing a danger to life or limb that is a<br />
permanent and inseparable element of the activity. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
low risk. <strong>Risk</strong> that could result in expected losses having little or no impact on<br />
accomplishing the mission. The probability of critical loss is unlikely (IIE), while that of<br />
marginal loss is seldom (IIID) or unlikely (IIIE). The probability of a negligible loss is likely<br />
or less (IVB through IVE). This term and its definition are applicable only in the context of<br />
this publication and should not be referenced outside this publication.<br />
moderate risk. <strong>Risk</strong> that could result in degraded mission capabilities in terms of the<br />
required mission standard will have a reduced mission capability if threats occur during<br />
mission. An unlikely probability of catastrophic loss (IE) exists. The probability of a critical<br />
loss is seldom (IID). Marginal losses occur with a likely or occasional probability (IIIB or<br />
IIIC). A frequent probability of negligible (IVA) losses exists. This term and its definition<br />
are applicable only in the context of this publication and should not be referenced outside<br />
this publication.<br />
operational protection. The conservation of the forces’ fighting potential so that it can be<br />
applied at the decisive time and place. This activity includes actions taken to counter the<br />
enemy’s forces by making friendly forces (including operational formations, personnel, etc.) ,<br />
systems, and operational facilities difficult to locate, strike, and destroy. (CJCSM 3500.04)<br />
Glossary-4
probability. The likelihood that a hazardous incident will occur.<br />
frequent (A): Occurs very often, continuously experienced.<br />
likely (B): Occurs several times<br />
occasional (C): Occurs sporadically<br />
seldom (D): Remotely possible; could occur at some time<br />
unlikely (E): Can assume will not occur, but not impossible.<br />
This term and its definitions are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
residual risk. The level of risk remaining after controls have been identified and selected<br />
for threats that may result in loss of combat power. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
risk. 1. Probability and severity of loss linked to threats.<br />
2. See degree of risk. See also risk management. (JP 1-02)<br />
risk assessment. Identification and assessment of threats; an identified threat is assessed<br />
to determine the risk (both the probability of occurrence and resulting severity) of a<br />
hazardous incident due to the presence of the threat. This term and its definition are<br />
applicable only in the context of this publication and should not be referenced outside this<br />
publication.<br />
risk decision. The decision to accept or not accept the risks associated with an action;<br />
made by the commander, leader, or individual responsible for performing that action. This<br />
term and its definition are applicable only in the context of this publication and should not<br />
be referenced outside this publication.<br />
risk management. A process by which decision makers reduce or offset risk. Also called<br />
RM. (JP 1-02) The systematic process of identifying, assessing, and controlling risks arising<br />
from operational factors and making decisions that weigh risks against mission benefits.<br />
severity. The intensity of the expected consequence of an event in terms of degree of<br />
injury, property damage, or other mission-impairing factors (loss of combat power and so<br />
on) that could occur.<br />
catastrophic (I): Loss of ability to accomplish the mission or mission failure. Death or<br />
permanent total disability. Loss of major or mission critical system or equipment. Major<br />
property (facility) damage. Severe environmental damage. Unacceptable collateral<br />
damage. Mission-critical security damage.<br />
critical (<strong>11</strong>): Significantly degraded mission capability or unit readiness. Permanent<br />
partial disability. Extensive (major) damage to equipment or systems. Significant<br />
damage to property or the environment. Security failure. Significant collateral damage.<br />
marginal (<strong>11</strong>1): Degraded mission capability or unit readiness. Minor damage to<br />
equipment or systems, property, or the environment.<br />
negligible (IV): Little or no adverse impact on mission capability. Slight equipment or<br />
system damage, but fully functional and serviceable. Little or no property or<br />
environmental damage.<br />
This term and its definitions are applicable only in the context of this publication and<br />
should not be referenced outside this publication.<br />
Glossary-5
threat. A source of danger: any opposing force, condition, source, or circumstance with the<br />
potential to negatively impact mission accomplishment andor degrade mission capability.<br />
This term and its definition are applicable only in the context of this publication and should<br />
not be referenced outside this publication.<br />
total risk. The sum of identified risk and unidentified risk. It is accepted by the<br />
appropriate decision-maker because further efforts at risk control are not justified by the<br />
perceived gain.<br />
unacceptable risk. The risk that cannot be tolerated and must be eliminated or<br />
controlled.<br />
unidentified risk. The risk that has not been identified. It is unknown or immeasurable.<br />
Glossary-6
Index<br />
A<br />
acceptability, <strong>11</strong>-3, <strong>11</strong>1-4, A-D-1<br />
acceptable loss, 1-1<br />
acceptable risk, 1-2, I-3,II-3,II-5, <strong>11</strong>1-3, A-D-1, Glossary-4<br />
accountability, 1-2,<strong>11</strong>-5,<strong>11</strong>1-1, B-5<br />
administrative controls, <strong>11</strong>-4, A-E-l , A-E-2<br />
alarmism, <strong>11</strong>-2<br />
application of risk management, i, I- 1, I-3,1-4, <strong>11</strong>-1<br />
assessment, I-l,I-3, 1-5, <strong>11</strong>-2, <strong>11</strong>-3,II-5, <strong>11</strong>-6, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>1-2,<strong>11</strong>1-4, <strong>11</strong>1-5, <strong>11</strong>1-6, A-1, A-A-1, A-<br />
C-1, A-D-1, A-D-2, B-1, B-2, B-3, B-4, B-5, Glossary-3, Glossary-4, Glossary-5<br />
complete, <strong>11</strong>-2<br />
matrix, A-D-1<br />
output, <strong>11</strong>-2<br />
pitfalls, v, <strong>11</strong>-2<br />
teams, B-1<br />
assigning redundant capabilities, <strong>11</strong>-5, A-E- 1, A-E-2<br />
avenues of approach, <strong>11</strong>-9, B-3<br />
avoiding the risk, I-2,II-3, <strong>11</strong>-4, <strong>11</strong>1-3<br />
C<br />
catastrophic, A-D- 1, A-D-2, Glossary-4, Glossary-5<br />
chain of command, v, 1-2, <strong>11</strong>1-1,<strong>11</strong>1-2,<strong>11</strong>1-3, <strong>11</strong>1-7<br />
civil consideration, <strong>11</strong>-8, <strong>11</strong>-10, <strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-6, A-A-1, B-3, B-4, B-5, Glossary-2<br />
climate, <strong>11</strong>-9,<strong>11</strong>1-2<br />
commander, i, v, vi, I-1,142, 1-3, 1-5, <strong>11</strong>-3, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5, A-<br />
1, A-A-1, A-E-1, B-3, B-4, Glossary-1, Glossary-5<br />
complacency, <strong>11</strong>-10,<strong>11</strong>1-1, <strong>11</strong>1-4, <strong>11</strong>1-5<br />
complete risk assessment, <strong>11</strong>-2<br />
controls, risk, v, 1-2, 1-3, 1-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-12,III-l, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5,<strong>11</strong>1-6,<strong>11</strong>1-7, A-1, A-A-1, A-E-1, A-E-2, B-1, B-2, Glossary-4, Glossary-5<br />
administrative, <strong>11</strong>-4, A-E- 1, A-E-2<br />
avoiding risk, I-2,II-3,II-4, <strong>11</strong>1-3<br />
delay COA, <strong>11</strong>-4<br />
develop, v, 1-3, 1-5, <strong>11</strong>-3,II-4, <strong>11</strong>-5, <strong>11</strong>-7, <strong>11</strong>-8,<strong>11</strong>1-3,<strong>11</strong>1-5, A-1, A-A-1, B-2<br />
educational, <strong>11</strong>-4, A-E-1, A-E-2<br />
engineering, <strong>11</strong>-4, A-E-1, A-E-2<br />
implement, v, I-3,1-5, <strong>11</strong>-3, <strong>11</strong>-4,<strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>1-4, A-A-1, B-1<br />
operational, <strong>11</strong>-4, A-E-1, A-E-2<br />
options, <strong>11</strong>-3,II-4, A-1, A-E-1, A-E-2<br />
physical, <strong>11</strong>-4, A-E-1, A-E-2<br />
planning matrix, A-E-1<br />
index-1
edundant capabilities, <strong>11</strong>-4, A-E-1, A-E-2<br />
residual risk, <strong>11</strong>-3, <strong>11</strong>-5,<strong>11</strong>1-3,<strong>11</strong>1-4, A-A-1, Glossary-5<br />
support, v, <strong>11</strong>-3,<strong>11</strong>-6,<strong>11</strong>1-2, <strong>11</strong>1-4<br />
transferring risk, <strong>11</strong>-4<br />
course of action (COA), 1-1, 1-3, I-4,II-3,II-4, <strong>11</strong>-5,<strong>11</strong>-8,<strong>11</strong>-9,<strong>11</strong>1-2,<strong>11</strong>1-3, <strong>11</strong>1-4, A-C-1,<br />
Glossary- 1<br />
cover and concealment, <strong>11</strong>-9<br />
crisis action, 1-3, <strong>11</strong>-7, <strong>11</strong>-8<br />
critical, 1-3, <strong>11</strong>-1,II-4,<strong>11</strong>-9,<strong>11</strong>-10, <strong>11</strong>1-1, <strong>11</strong>1-5,<strong>11</strong>1-6, A-D-1, A-D-2, A-E-1, A-E-2, Glossary-4,<br />
Glossary-5<br />
D<br />
decisions, i, v, I-l,I-2,1-3, <strong>11</strong>-3,<strong>11</strong>4.<strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8,<strong>11</strong>-12,<strong>11</strong>1-1 <strong>11</strong>1-2,<strong>11</strong>1-3, A-A-1, A-C-1, A-<br />
D-1, B-2, Glossary-5, Glossary-6<br />
delay, <strong>11</strong>-4, <strong>11</strong>1-4<br />
deliberate, 1-3, <strong>11</strong>-2, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>1-5<br />
develop controls, v, 1-3, 1-5, <strong>11</strong>-3, <strong>11</strong>-5,II-7, <strong>11</strong>-8, <strong>11</strong>1-3, <strong>11</strong>1-5, A-1, A-A-1, B-2<br />
E<br />
enemy, 1-1, II- 1,II-8,II-9, Glossary-2, Glossary-4<br />
engineering, <strong>11</strong>-4, <strong>11</strong>- 1 1, A-E- 1, A-E-2, B- 1<br />
exposure, <strong>11</strong>-4, A-E-2<br />
F<br />
feasibility, 1-2, <strong>11</strong>-3,III-2, <strong>11</strong>1-3, <strong>11</strong>1-4<br />
feedback, v, 1-2, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>1-2, <strong>11</strong>1-7<br />
force protection, v, I-1,I-5,<strong>11</strong>1-3,<strong>11</strong>1-7, A-1, A-B-1, A-C-1, B-l,B-2, B-4, Glossary-1<br />
activities, A-C-1<br />
agenda, B-1, B-2, B-3<br />
assessment team, B-1 , B-2<br />
checklist, B-3<br />
composition, B- 1<br />
conditions, A-1, A-C-1<br />
effects, A- 1, A-C- 1<br />
facilities, B-3, B-4<br />
priority matrix, A- 1, A-B- 1<br />
procedures, B-1<br />
products, B-4<br />
tasks, A- 1, A-B- 1, A-C- I<br />
force protection working group (FPWG), <strong>11</strong>1-3, B-1, B-2, B-3, B-4, B-5, Glossary-1<br />
forward area refueling point (FARP), B-5, Glossary-1<br />
Index-2
H<br />
high risk, <strong>11</strong>-5, A-A-1, A-D-1, Glossary-4<br />
host nation (HN), <strong>11</strong>1-5, B-1, B-3, B-4, Glossary-1<br />
hygienic, <strong>11</strong>- 12<br />
I<br />
identify, i, v, 1-1, I-2,I-3, 1-4,<strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3,II-4,II-5, <strong>11</strong>-6,II-7, <strong>11</strong>-8,<strong>11</strong>-9,<strong>11</strong>-10,<strong>11</strong>1-1, <strong>11</strong>1-3,<br />
<strong>11</strong>1-4,<strong>11</strong>1-5,<strong>11</strong>1-7, A-1, A-A-1, A-B-1, A-E-2, B-1, B-2, Glossary-4, Glossary-5, Glossary-6<br />
impact, mission, probability and severity, 1-1,1-3,<strong>11</strong>-1,<strong>11</strong>-2, <strong>11</strong>-8,II-9,II-10,<strong>11</strong>1-3,<strong>11</strong>1-4, III-<br />
6, A-D-2, Glossary-4, Glossary-5<br />
implementation, i, v, I-1,142, 1-3,1-5,<strong>11</strong>-3,<strong>11</strong>-4,<strong>11</strong>-5,<strong>11</strong>-6,<strong>11</strong>-7,<strong>11</strong>-8,<strong>11</strong>1-3,<strong>11</strong>1-4,<strong>11</strong>1-6,<strong>11</strong>1-7,<br />
A-A-1. B-1<br />
J<br />
Joint Operation Planning and Execution System (JOPES), i, <strong>11</strong>-7, Glossary-2<br />
joint task force (JTF) i, <strong>11</strong>-7,II-8,<strong>11</strong>1-4,<strong>11</strong>1-5, B-3, B-4, B-5, Glossary-2<br />
K<br />
key aspects, v, I-1,II-6, <strong>11</strong>-9, <strong>11</strong>1-5<br />
L<br />
logistics, <strong>11</strong>-10, <strong>11</strong>-1 1,<strong>11</strong>1-4, <strong>11</strong>1-6, A-B-1, B-1, Glossary-2<br />
loss, 1-1 ,II-2,<strong>11</strong>-4,<strong>11</strong>-8, <strong>11</strong>1-3,<strong>11</strong>1-4, A-C-1, A-D-1, A-D-2, Glossary-4, Glossary-5<br />
low risk, 1-2, <strong>11</strong>-5, <strong>11</strong>1-2, A-A-1, A-D-1, Glossary-4<br />
M<br />
machine, <strong>11</strong>-1, II-lO,II-<strong>11</strong>,<strong>11</strong>-12, Glossary- 1<br />
maintenance, I-3,<strong>11</strong>-9,<strong>11</strong>- 10, <strong>11</strong>-<strong>11</strong>, A-E-1, A-E-2<br />
major subordinate element (MSE), <strong>11</strong>-7,II-8, Glossary-2<br />
man, machine, media, management, mission (5-M) model, <strong>11</strong>-1, <strong>11</strong>-6, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>-12, <strong>11</strong>1-2,<br />
Glossary-1<br />
managing, 1-3, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-5, <strong>11</strong>1-6, <strong>11</strong>1-7<br />
marginal, A-D-1, A-D-2, Glossary-4, Glossary-5<br />
media, <strong>11</strong>-1, <strong>11</strong>-10, <strong>11</strong>-12,<strong>11</strong>1-5, <strong>11</strong>1-6, Glossary-1<br />
METT-T (mission, enemy, terrain and weather, troops and support available, time<br />
available), <strong>11</strong>-1,II-6, <strong>11</strong>-8, <strong>11</strong>-10, <strong>11</strong>1-2, Glossary-2<br />
METT-TC (mission, enemy, terrain and weather, troops and support available, time<br />
available, civil considerations [Army]) <strong>11</strong>-8, <strong>11</strong>- 10, Glossary-2<br />
moderate risk, <strong>11</strong>-5, A-D- 1, Glossary-4<br />
N<br />
negligible, A-D- 1, A-D-2, Glossary-4, Glossary-5<br />
0<br />
objective, 1-4, <strong>11</strong>-10, <strong>11</strong>-12, <strong>11</strong>1-3, <strong>11</strong>1-6, <strong>11</strong>1-7<br />
Index-3
observation, <strong>11</strong>-9,<strong>11</strong>1-6, B-3<br />
operational, v, 1-1, <strong>11</strong>-1,II-4,II-10, <strong>11</strong>-12, <strong>11</strong>1-3,<strong>11</strong>1-6, A-B-1, A-C-1, A-E-1, A-E-2, B-5,<br />
Glossary-4, Glossary-5<br />
operation order (OPORD), <strong>11</strong>1-4, <strong>11</strong>1-7, Glossary-3<br />
operation plan (OPLAN), <strong>11</strong>1-4,<strong>11</strong>1-7, Glossary-3<br />
operations, military, v, I-1,I-2, 1-3, 1-5, <strong>11</strong>-1,II-4, <strong>11</strong>-6,<strong>11</strong>-8,<strong>11</strong>-9,<strong>11</strong>-10, <strong>11</strong>1-1,<strong>11</strong>1-3,<strong>11</strong>1-4, III-<br />
6, <strong>11</strong>1-7, A-1, A-D-3, B-1, B-2, B-3, B-4, Glossary-2<br />
P<br />
performance, <strong>11</strong>-4,II-6, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>1-2,<strong>11</strong>1-6, A-E-2<br />
personal, <strong>11</strong>-1, <strong>11</strong>-4.<strong>11</strong>-<strong>11</strong>, A-D-2, A-E-2<br />
physical, 1-1, <strong>11</strong>-4, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>, A-E-1, A-E-2<br />
probability, I-l,II-l,II-2, <strong>11</strong>-3.<strong>11</strong>-4,II-5, A-D-1, A-D-2, A-D-3, Glossary-4, Glossary-5,<br />
category, A-D-2<br />
definitions, A-D-3<br />
procedures, i, v, 1-2, 1-3, 1-5, <strong>11</strong>-3,II-10, <strong>11</strong>-12,<strong>11</strong>1-4, <strong>11</strong>1-5, A-1, A-E-1, A-E-2, B-1, B-5,<br />
Glossary-1 , Glossary-2, Glossary-3<br />
process, i, v, 1-1, 1-2, 1-3, 1-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-9, <strong>11</strong>-12, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3,<br />
<strong>11</strong>1-6, A-1, A-A-1, A-E-2, B-1, B-4, Glossary-5<br />
R<br />
residual risks, <strong>11</strong>-3, <strong>11</strong>-5, <strong>11</strong>1-3,<strong>11</strong>1-4, A-A-1, Glossary-5,<br />
responsibilities, i, v, <strong>11</strong>-5, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3, <strong>11</strong>1-4,<strong>11</strong>1-5, B-1, B-2<br />
commander, <strong>11</strong>1-1, <strong>11</strong>1-2, <strong>11</strong>1-3<br />
leaders, <strong>11</strong>1- 1, <strong>11</strong>1-2<br />
individual, <strong>11</strong>1-5<br />
staff, <strong>11</strong>1-3<br />
risk, i, v, I-1,l-2, 1-3, 1-4, 1-5, <strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-6,II-7, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>1-1, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5, <strong>11</strong>1-6, <strong>11</strong>1-7, A-1, A-A-1, A-C-1, A-D-1, A-D-2, A-E-1, A-E-2, B-1, B-4, B-5,<br />
Glossary-3, Glossary-4, Glossary-5, Glossary-6<br />
assessment, <strong>11</strong>-2, <strong>11</strong>1-4, A-C- 1, A-D-l , A-D-2<br />
probability categories, A-D-2<br />
probility definitions, A-D-3<br />
severity categories, <strong>11</strong>-2, A-D-2<br />
unacceptable, <strong>11</strong>1-3, Glossary-6<br />
unnecessary, 1-2, I-3,<strong>11</strong>1-3, <strong>11</strong>1-6<br />
risk management, i, v, 1-1, 1-2, 1-3, 1-4, I-5,<strong>11</strong>-1, <strong>11</strong>-5,II-6,II-7,II-8,II-10,II-12, <strong>11</strong>1-1, <strong>11</strong>1-2,<br />
<strong>11</strong>1-3, <strong>11</strong>1-4, <strong>11</strong>1-5,<strong>11</strong>1-6, <strong>11</strong>1-7, A-1, A-A-1, B-1, Glossary-5<br />
application guidelines, 1-3, <strong>11</strong>1-7<br />
application, i, 1-1, 1-3, <strong>11</strong>-1<br />
assessment, I-1,II-6,<strong>11</strong>1-6<br />
crisis action, 1-3, <strong>11</strong>-7, <strong>11</strong>-8<br />
cycle, 1-4<br />
decisions, <strong>11</strong>-5<br />
Index-4
deliberate, 1-3, <strong>11</strong>-7<br />
execution, <strong>11</strong>-7,II-8<br />
feedback, v, 1-2, <strong>11</strong>-6, <strong>11</strong>-7,III-2, <strong>11</strong>1-7<br />
framework for implementing, 1-2<br />
fundamentals, v, 1-1<br />
goal, v, 1-1<br />
implement, I-2,<strong>11</strong>1-6<br />
integration, v, <strong>11</strong>-7, III-2,<strong>11</strong>1-3, <strong>11</strong>1-4,<strong>11</strong>1-6<br />
key aspects, v, 1-1<br />
levels, 1-3<br />
objective, <strong>11</strong>1-3, <strong>11</strong>1-6, <strong>11</strong>1-7<br />
principles, i, v, 1-2<br />
process, i, v, I-l,I-2,1-3,1-4, 1-5,<strong>11</strong>-1,<strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7,<strong>11</strong>1-1,<strong>11</strong>1-2, <strong>11</strong>1-6, A-1, B-1,<br />
Glossary-5<br />
review, v, 1-3, 1-4,II-1, <strong>11</strong>-6, <strong>11</strong>-7,II-8, <strong>11</strong>1-6,<strong>11</strong>1-7<br />
sequence, 1-3<br />
supervise, 1-3,I-4,II-6,II-7, <strong>11</strong>-8, A-A-1<br />
training, <strong>11</strong>1-2, <strong>11</strong>1-6<br />
use, 1-1, 1-3<br />
worksheet, A- 1, A-A- 1<br />
risk management fundamentals, v, 1-1<br />
risk management goal, v, I- 1, II- 10, <strong>11</strong>1-2<br />
S<br />
services, v, 1-1, <strong>11</strong>-10, <strong>11</strong>1-5, <strong>11</strong>1-6<br />
situational analysis, <strong>11</strong>-1<br />
supervise and review, 1-3, 1-4, <strong>11</strong>-6, <strong>11</strong>-7,II-8, A-A-1<br />
T<br />
threat, v, 1-1, 1-2, 1-3, 1-4, <strong>11</strong>-1, <strong>11</strong>-2, <strong>11</strong>-3, <strong>11</strong>-4, <strong>11</strong>-5, <strong>11</strong>-6, <strong>11</strong>-7, <strong>11</strong>-8, <strong>11</strong>-9, <strong>11</strong>-10, <strong>11</strong>-<strong>11</strong>, <strong>11</strong>-12, III-<br />
1, <strong>11</strong>1-3,<strong>11</strong>1-4,<strong>11</strong>1-5, <strong>11</strong>1-7, A-1, A-A-1, A-C-1, A-D-1, A-E-2, B-1, B-2, B-3, B-4, B-5,<br />
Glossary-4, Glossary-5, Glossary-6<br />
assessment, 1-3, <strong>11</strong>1-4<br />
causes, <strong>11</strong>-1,II-2, A-A-1<br />
checklist, B-3<br />
identification, v, I-2,I-3, 1-4, <strong>11</strong>-1, <strong>11</strong>-3, <strong>11</strong>-5,<strong>11</strong>-7, <strong>11</strong>-8, II-9,II-10,<strong>11</strong>1-4, A-1, A-A-1, B-2,<br />
Glossary-4, Glossary-5<br />
probability, II-l,II-2, <strong>11</strong>-3, A-D-1, Glossary-5<br />
severity, II- 1, <strong>11</strong>-2, <strong>11</strong>-3, Glossary-4, Glossary-5<br />
U<br />
unacceptable risk ,<strong>11</strong>1-3, Glossary-6<br />
unnecessary risk, 1-2, 1-3, <strong>11</strong>1-3, <strong>11</strong>1-6<br />
Index-5
FM 3-100.12<br />
MCRP 5-12.1C<br />
NTTP 5-03.5<br />
AFTTPG) 3-2.34<br />
15 February 2001<br />
By Order of the Secretary of the Army:<br />
Official:<br />
ERIC K. SHINSEKI<br />
General, United States Army<br />
Chief of Staff<br />
JOEL B. HUDSON<br />
Administrative Assistant to the<br />
Secretary of the Army<br />
01 06 101<br />
DISTRIBUTION:<br />
Active Army, Army National Guard, and US. Army Reserve: To be distribute in<br />
accordance with the initial distribution number <strong>11</strong>5840 requirements for FM 3-<br />
100.12.<br />
By Order of the Secretary of the Air Force:<br />
LANCE L. SMITH<br />
Major General, USAF<br />
Commander<br />
Headquarters Air Force Doctrine Center<br />
Air Force Distribution: F
MARINE CORPS: PCN 14400009300