You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
B-4 KEY <strong>SOLUTION</strong><br />
• Intermediate Routing<br />
This feature is needed for interconnection between<br />
segments in the access network, and between the access<br />
network and core network. In order to perform this<br />
function, D-<strong>Link</strong> solution provides support for static route,<br />
RIP I/II, OSPF and RIPng for IPv6 implementation.<br />
• Bandwidth Management<br />
This feature allows the network administrator to allocate<br />
different amounts of bandwidth for each service and<br />
user, which will lead to more efficient bandwidth usage.<br />
• Traffic Policing - ACL<br />
Network traffic passing through the aggregation network<br />
will be filtered against defined access control list to<br />
eliminate unnecessary and malicious traffic.<br />
• High Availability<br />
D-<strong>Link</strong> provides high availability of aggregation network<br />
with redundancy power supply, stacking configuration<br />
and Virtual Router Redundancy Protocol (VRRP).<br />
Core Network<br />
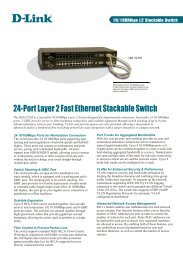
As its name implies, core network is where enterprises<br />
place their critical information technology resources. Core<br />
network makes up the enterprise network backbone.<br />
Network connection from the enterprise network<br />
(access and aggregation network), server farm, Internet<br />
and network management system culminate in core<br />
network. Because of its critical role, enterprise needs<br />
high performance and reliable infrastructure for the<br />
core network. In meeting this challenge, D-<strong>Link</strong> offers<br />
its xStack Layer-3 switches and Layer-3 chassis switches.<br />
D-<strong>Link</strong> core network solution provides high switching<br />
capacity with 10 Gigabit connections to ensure high speed<br />
and excellent core network performance. In addition, to<br />
provide an ideal core network infrastructure, D-<strong>Link</strong> also<br />
enrich this high performance infrastructure with features<br />
such as high availability (stacking configuration, VRRP),<br />
and routing for IPv4, IPv6 and multicast traffic. Besides<br />
providing excellent core network infrastructure, D-<strong>Link</strong> also<br />
provides network management and storage solution for<br />
comprehensive core network solution.<br />
D-<strong>Link</strong> offers two solutions for Centralized Network<br />
Management, namely, the AP Manager II and D-View 6.0.<br />
• Centralized Network Management<br />
For large scale centralized network management, D-<strong>Link</strong><br />
provides D-View 6.0 Simple Network Management<br />
Protocol (SNMP) software. D-View 6.0 is a centralized<br />
management system that covers a wide range of network<br />
devices such as access points, managed switches and<br />
SNMP capable routers. It allows the network administrator<br />
to manage and monitor critical network characteristic<br />
such as device configuration, network performance,<br />
security and fault tolerance.<br />
• Centralized Access Point Management<br />
AP Manager II provides centralized management for<br />
up to recommended 20 fat wireless access points. Features<br />
supported by AP Manager II include mass configuration,<br />
mass firmware upgrade, fault management, real-time<br />
monitoring and real-time reporting. This software<br />
provides network administrators with the means of<br />
verifying and conducting regular maintenance checks<br />
without the need of physical travel.<br />
End-to-End Security (E2ES)<br />
E2ES is a unique security solution from D-<strong>Link</strong> that covers the<br />
entire enterprise network from the access network to core<br />
network. This solution consists of three elements:<br />
• Gateway Security<br />
This carries out the security function for enterprise<br />
network at the gateway, the boundary between<br />
enterprise network and the Internet. It protects<br />
enterprise network from external security threats to<br />
ensure the secure operation of internal network. For<br />
this element of E2ES, D-<strong>Link</strong> present the NetDefend<br />
UTM/IPS firewall. This firewall is equipped with various<br />
advanced security features such as illegal traffic detection,<br />
intrusion detection prevention, anti-spam, anti-virus, web<br />
content filtering, high availability, VPN and more.<br />
• Endpoint Security<br />
This is the first line of defense within enterprise internal<br />
network. It protects enterprise network from security<br />
threats coming from inside the network. D-<strong>Link</strong> provides<br />
this solution by pushing intelligence to its xStack<br />
switch as an evolutionary endpoint security that performs<br />
authentication, authorization, traffic control, node address<br />
control and attack mitigation. Some of the endpoint<br />
security functions supported by the D-<strong>Link</strong> xStack switch<br />
are access control (802.1X, MAC-based, web-based),<br />
dynamic VLAN assignment, loopback detection, IP-MAC-<br />
Port binding, rogue DHCP server detection, Safeguard<br />
Engine, and broadcast storm control.<br />
• Joint Security<br />
Joint Security is a security solution formed with D-<strong>Link</strong><br />
ZoneDefense and Microsoft Network Access Protection<br />
(NAP) to provide user access control and comprehensive<br />
security mechanism for enterprise network. D-<strong>Link</strong><br />
ZoneDefense is a unique security technology that enables<br />
D-<strong>Link</strong> NetDefend firewall to work together with<br />
D-<strong>Link</strong> xStack switch to carry out an advanced defense<br />
mechanism. With this defense mechanism, the firewall<br />
will block any malicious traffic or security threat and<br />
inform the xStack switch within the enterprise network<br />
to block the suspected host. ZoneDefense, in this way,<br />
effectively stops security threats and virus/worm infections<br />
and outbreaks. D-<strong>Link</strong> Joint Security offers two important<br />
functions for user access control in enterprise network:<br />
• User Authentication<br />
Only users with valid access credential allowed<br />
accessing the network.<br />
• Policy Enforcement and Remediation<br />
nAP will check and ensure system compliance of<br />
each user that has passed authentication process<br />
against enterprise security requirements such as<br />
updated anti-virus definition of network host, updated<br />
operating system patch of network host or personal<br />
firewall in active status. Only network hosts that meet<br />
the security requirements specified will be allowed to<br />
access the network.