LOK-IT Technical Overview
LOK-IT Technical Overview
LOK-IT Technical Overview
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
S Y S T E M A T I C D E V E L O P M E N T G R O U P , L L C<br />
well and used to decrypt the content. In addition to the epoxy potting all <strong>LOK</strong>-<strong>IT</strong> models<br />
internal security system are designed to store the encryption key on a separate<br />
electronically protected security controller. Therefore, even if the flash is accessed by<br />
slicing away the epoxy potting, the encryption key remains secure and the data cannot be<br />
decrypted.<br />
PIN<br />
Drive Default Status<br />
To meet the varying requirements of clients, <strong>LOK</strong>-<strong>IT</strong> drives may be configured to be<br />
shipped unlocked (i.e. use of PIN is optional) or disabled (i.e. PIN must be set before initial<br />
use). See <strong>LOK</strong>-<strong>IT</strong> FEATURE COMPARISONS on page 18 for a listing of drive default states.<br />
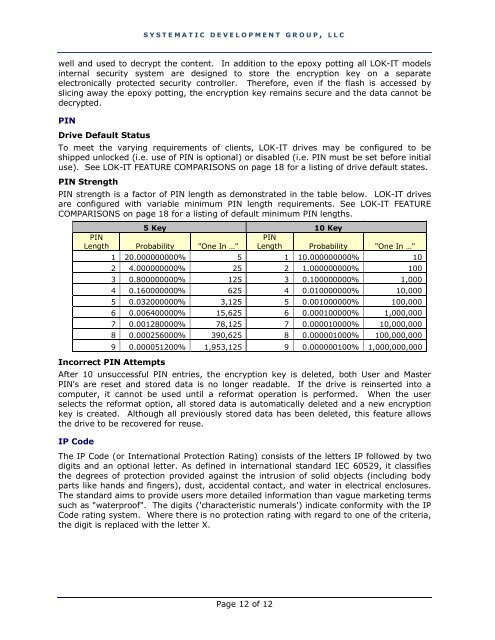
PIN Strength<br />
PIN strength is a factor of PIN length as demonstrated in the table below. <strong>LOK</strong>-<strong>IT</strong> drives<br />
are configured with variable minimum PIN length requirements. See <strong>LOK</strong>-<strong>IT</strong> FEATURE<br />
COMPARISONS on page 18 for a listing of default minimum PIN lengths.<br />
5 Key 10 Key<br />
PIN<br />
Length Probability "One In …"<br />
PIN<br />
Length Probability "One In …"<br />
1 20.000000000% 5 1 10.000000000% 10<br />
2 4.000000000% 25 2 1.000000000% 100<br />
3 0.800000000% 125 3 0.100000000% 1,000<br />
4 0.160000000% 625 4 0.010000000% 10,000<br />
5 0.032000000% 3,125 5 0.001000000% 100,000<br />
6 0.006400000% 15,625 6 0.000100000% 1,000,000<br />
7 0.001280000% 78,125 7 0.000010000% 10,000,000<br />
8 0.000256000% 390,625 8 0.000001000% 100,000,000<br />
9 0.000051200% 1,953,125 9 0.000000100% 1,000,000,000<br />
Incorrect PIN Attempts<br />
After 10 unsuccessful PIN entries, the encryption key is deleted, both User and Master<br />
PIN's are reset and stored data is no longer readable. If the drive is reinserted into a<br />
computer, it cannot be used until a reformat operation is performed. When the user<br />
selects the reformat option, all stored data is automatically deleted and a new encryption<br />
key is created. Although all previously stored data has been deleted, this feature allows<br />
the drive to be recovered for reuse.<br />
IP Code<br />
The IP Code (or International Protection Rating) consists of the letters IP followed by two<br />
digits and an optional letter. As defined in international standard IEC 60529, it classifies<br />
the degrees of protection provided against the intrusion of solid objects (including body<br />
parts like hands and fingers), dust, accidental contact, and water in electrical enclosures.<br />
The standard aims to provide users more detailed information than vague marketing terms<br />
such as "waterproof". The digits ('characteristic numerals') indicate conformity with the IP<br />
Code rating system. Where there is no protection rating with regard to one of the criteria,<br />
the digit is replaced with the letter X.<br />
Page 12 of 12